How secure is your customers’ data? In March 2023, one of the largest healthcare breaches of the year (so far) was reported, impacting more than 4.2 million customers. Don’t be the next statistic. Learn what transport layer security can do to secure your data in transfer. Because your customers’ data care starts with you.
In Q3 2022, 14% of the devices analyzed by Akamai showed at least one domain name system (DNS) malicious transaction (e.g., malware, phishing, ransomware command, and control domains). The consequences? A survey run by IDC and EfficientIP in 2022 gave us a few examples: 70% of organizations victims of a DNS attack experienced application downtime and 24% incurred a loss of data.
Using DNS over TLS (DoT) can help prevent your DNS request data from being tampered with by a cybercriminal, protecting your organization from most DNS attacks. How? By adding transport layer security (TLS) encryption on top of the user datagram protocol (UDP) utilized for DNS queries. But that isn’t all TLS can do; it can also help protect your customers’ sensitive data in transit.
So, what is TLS, exactly? How does it work? And what else can TLS do to improve the security of your organization’s website and data? This is exactly what we’re going to explore in this article.
What Is Transport Layer Security (TLS)?
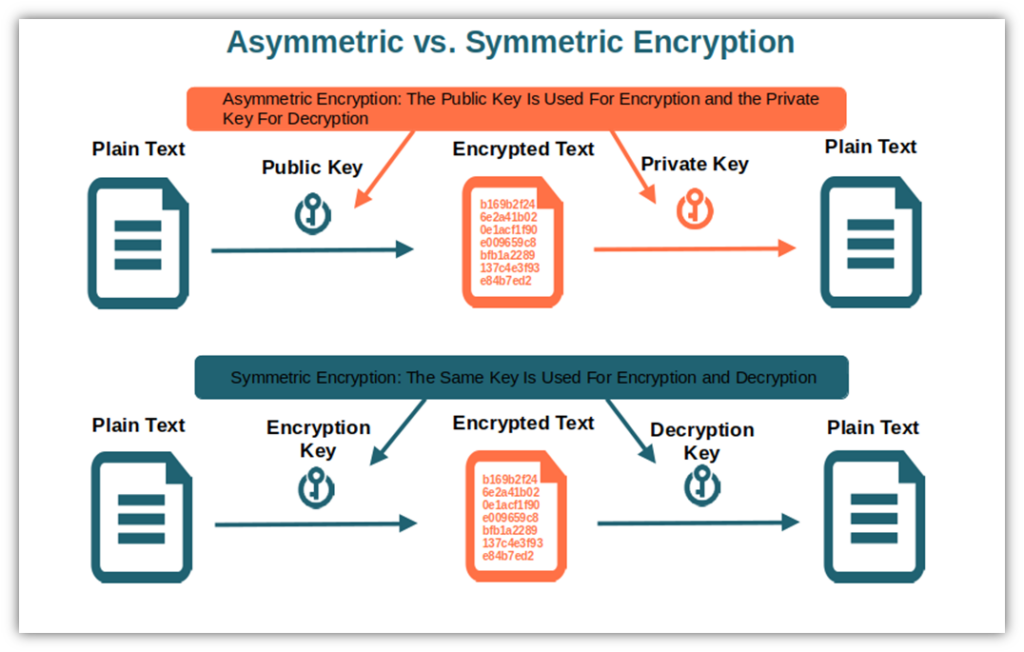
Transport layer security, commonly called TLS, is a cryptographic protocol that helps you keep your internet communications confidential and unmodified by creating an authenticated channel between a client and a web server. This protocol supports public and private key cryptography, meaning encryption methods that use either a key pair or a single key to encrypt and decrypt data.
It uses asymmetric encryption (i.e., a public key to encrypt data and a private key to decrypt it) at the start of a connection between the client and the server, and switches to symmetric encryption (i.e., the same key is used for encryption and decryption) after having exchanged session keys data.
Let’s say you want to ask your boss for a pay raise. You set up a private meeting in his office so that you can discuss your request directly with him, without anybody eavesdropping on your conversation. But how can you do that over the internet via a chat app or email, for example? It’s possible that someone could be listening in if you’re not using a secure connection.
Knowing this, how can you make sure that:
- You’re really talking to your boss and not to a cheeky colleague playing a prank on you?
- The conversation is kept private? And,
- That the stellar raise offered in the document he sent hasn’t been modified by the same cheeky colleague?
Transport layer security can do all of that for you.
TLS is the modern (and more secure) version of Netscape’s old secure sockets layer (SSL) protocol. It’s implemented on top of the hypertext transfer protocol (HTTP) to create a more secure protocol (called HTTPS) that can guarantee data authenticity and integrity by leveraging the power of cryptography.
And do you know what the best part is? Even though its primary use is to encrypt data transmissions between web applications and servers, TLS security can also be utilized in other cases. For instance, you can employ TLS to protect your communications via voice over IP (VoIP), instant messaging, and email servers, as shown in the example we’ve just made.
Before we dig deeper into its characteristics and features, there’s something fundamental that anyone who has to do with TLS should be aware of. Do you know the difference between TLS, SSL, and HTTPS? You don’t? “Nae bother” (“no worries”), as my Scottish friend would say. We’re here to help.
Why Are TLS and SSL Different From HTTPS?
I remember that when I started working in cyber security, I was overwhelmed by the number of acronyms, terms, and definitions used in the industry. No matter how hard I studied, there were always new terms or definitions coming up that I needed to research.
Nevertheless, it’s also one of the things that continues to fascinate me about cyber security: Regardless of how long you’ve been in the business, your learning journey never ends. And with 85% of organizations hit by at least one ransomware attack in 2022, if you want to keep your data secure, knowing the meaning of at least the most common terms is paramount.
This time, to make things easier and ensure that everyone reading this article doesn’t feel like going through a hieroglyphic text, we’ll be your Rosetta stone. Do you prefer to stick to the bare minimum? We’ve summarized the differences between TLS, SSL, and HTTPS in the table below.
| Secure Socket Layer (SSL) | Transport Layer Security (TLS) | Hypertext Transfer Protocol Secure (HTTPS) | |
| History | Developed by Netscape in the 1990s. Its first version was never published. | Created by the Internet Engineering Task Force (IETF). The first version was released in 1999. | Firstly conceived by Tim Berners-Lee at CERN in 1999; later the responsibility moved to the IETF and the World Wide Web Consortium (W3C). |
| Function | A (now deprecated) protocol that’s employed on top of HTTPS to encrypt the transmitted data. | The protocol that’s used on top of HTTPS to encrypt the transmitted data. | HTTPS over TLS (formerly HTTPS over SSL). It’s a secure version of HTTP that uses cryptographic functions to securely transmit data between a client and web server. |
| How Many Versions of the Protocol Exist? | Three versions: SSL 1.0 (never released), SSL 2.0, and SSL 3.0. | Four versions: TLS 1.0, TLS 1.1, TLS 1.2, and TLS 1.3. | One |
| Status | All versions are deprecated. | Versions 1.0 and 1.1 are deprecated; TLS 1.2 and 1.3 are the current secure versions. | It’s the secure version of the HTTP protocol and is the default protocol for 82.9% of websites, according to W3Techs. |
What Makes Hypertext Transfer Protocol Secure (HTTPS) Different?
Have you ever noticed the first letters you see on your browser bar whenever you visit a website? They usually read https://, or, in case of an insecure website, http://. HTTPS is the protocol used to securely transmit data between a client and a web server.
Hang on. Isn’t TLS doing the same thing? Not quite. While they all work to help you keep your internet connections secure, TLS (and previously SSL) is the protocol used to encrypt the HTTP-transmitted data. You can easily recognize a website using TLS by the tiny padlock displayed on your browser’s address bar, just before the URL.
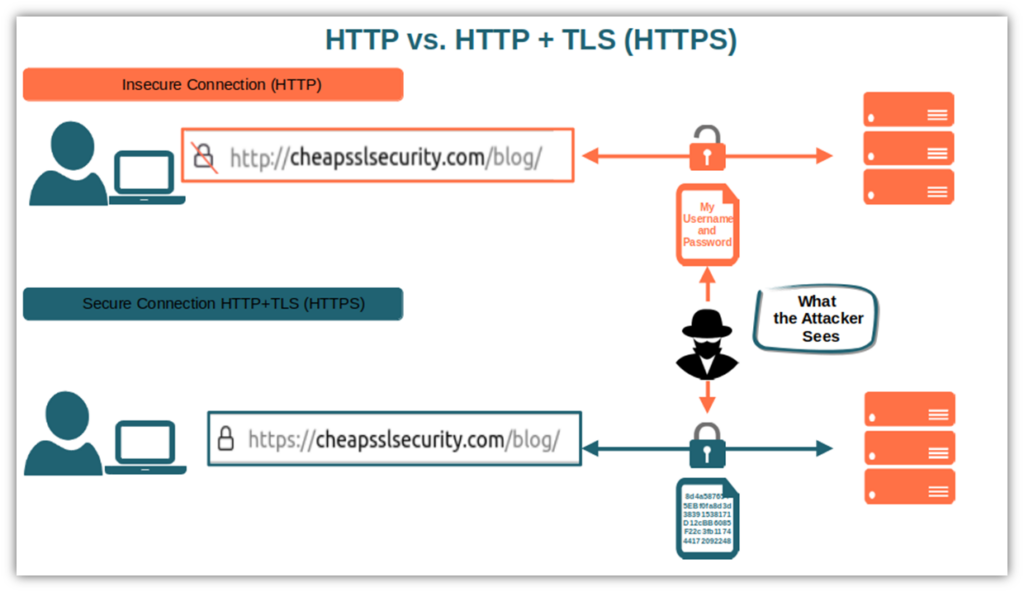
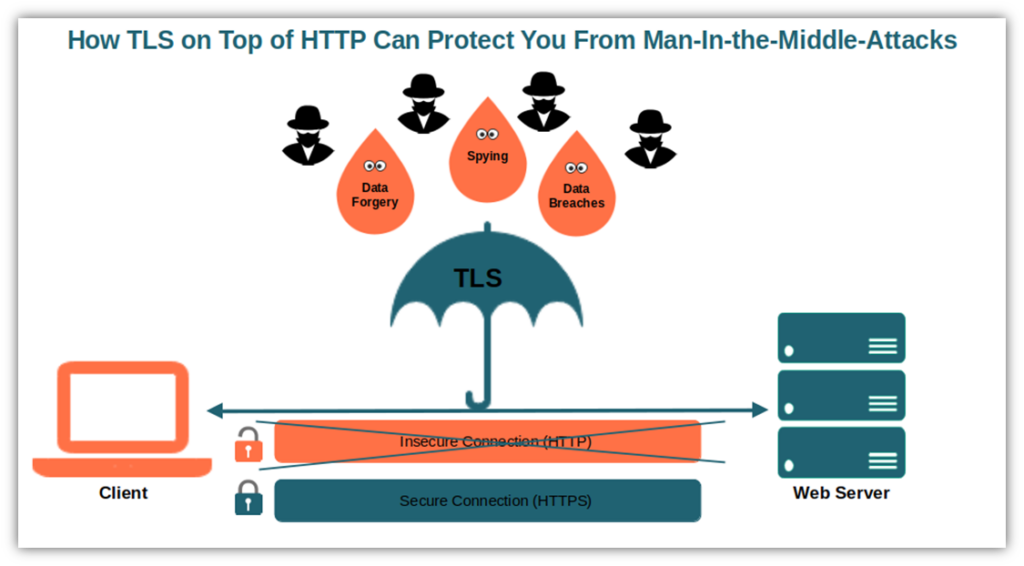
HTTPS defines what type of data can be transmitted, in which format, and how the web server should respond. (Basically, it’s what allows you to view information on the internet.) However, it needs TLS to encrypt information and to guarantee the secure exchange of data between the client and web server. Otherwise, if you use an HTTP (insecure) connection, you’ll send this data in plain text, which can be intercepted or modified in transit.
To say it in plain English, TLS is the “s” of security in HTTPS, enabling you to take the security of your website to the next level.
Nowadays, most websites have at least one TLS version enabled out of the four available. TLS 1.2 is the most popular as, at the time of writing, it’s supported by 99.9% of HTTPS-enabled sites surveyed by Qualys (as of March 2023). Let’s have a quick look at these versions.
Are you interested in knowing more about the differences between the three protocols? Check out DNSimple’s funny short comic strip.
The Four Versions of the Transport Layer Security
Four versions with the same goal: to achieve a secure internet connection. These four digital musketeers support different cryptographic functions, including encryption algorithms (more on that in a moment), and provide different levels of security.
Transport Layer Security 1.0 and 1.1
The first two versions of the protocol, TLS 1.0 and TLS 1.1, have already been declared officially obsolete by the U.S. National Security Agency (NSA) in 2021. Based on old and insecure algorithms like MD5 and SHA-1, they’re still supported by 32-35% of sites.
They’re both vulnerable to several attacks. Among them:
- POODLE. This vulnerability affects TLS versions 1.0 and 1.1. It’s an attack wherein the attacker downgrades the connection to the more vulnerable SSL 3.0 protocol.
- BEAST. This vulnerability affects TLS version 1.0. Similar to man-in-the-middle attacks, this enables attackers to exploit vulnerabilities in block cipher suites (i.e., they encrypt a fixed length block of information at the time), and
- Man-in-the-middle. Thanks to the weak cryptographic algorithms used during authentication, attackers can easily pose as the server communicating with the client.
Want a suggestion? Stay away from them; there’s a reason they’re deprecated, and the NSA removed them from its standards.
Transport Layer Security 1.2
… Then came TLS 1.2. This is the most widely supported TLS protocol and is considered the minimum version you should use to secure your website and other connections.
Among all the improvements characterizing the third version, TLS 1.2:
- Supports more secure algorithms like SHA-256,
- Let the server select the ciphers among those supported by both parties, and
- Can be used with advanced cipher suites supporting elliptic curve cryptography. It’s a more modern alternative to the Rivest-Shamir-Adleman (RSA) algorithm that guarantees the same level of security while utilizing a smaller key size.
Released in 2008, TLS 1.2 was a significant improvement over its predecessors, particularly with regard to the level of security it offers. As the most commonly supported protocol, it secures organizations by minimizing the risks of attacks like:
- Man-in-the-middle attacks. The process used during the handshake to generate random values is more secure. Thus, it limits the chances for attackers to guess the correct values and launch man-in-the-middle attacks, and
- RC4 attacks. With the introduction of more secure cipher suites (i.e., AES-GCM), websites owners can avoid the usage of the vulnerable and deprecated algorithms (including RC4), protecting the websites from RC4-based attacks.
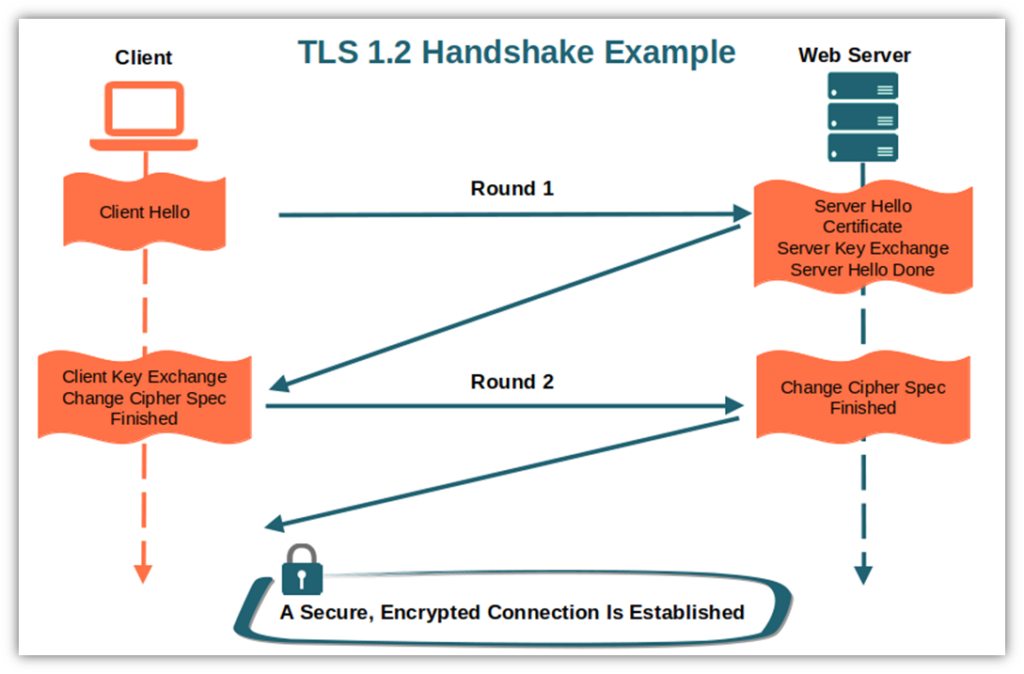
However, good things never last forever. Even if TLS 1.2 supports more secure ciphers, web servers and clients can still opt for using deprecated ones like MD5 and SHA-1. On top of that, TLS 1.2 has a relatively complex and slow handshake (we’ll get to that in a minute). Not good. The solution came in 2018 when the newest TLS 1.3 was published.
Transport Layer Security 1.3
Qualys SSL Labs reports that one-third (66%) of websites it analyzes support TLS 1.3. Data security is the greatest benefit of the secure protocol, according to 85% of surveyed organizations that have already implemented it. This latest version:
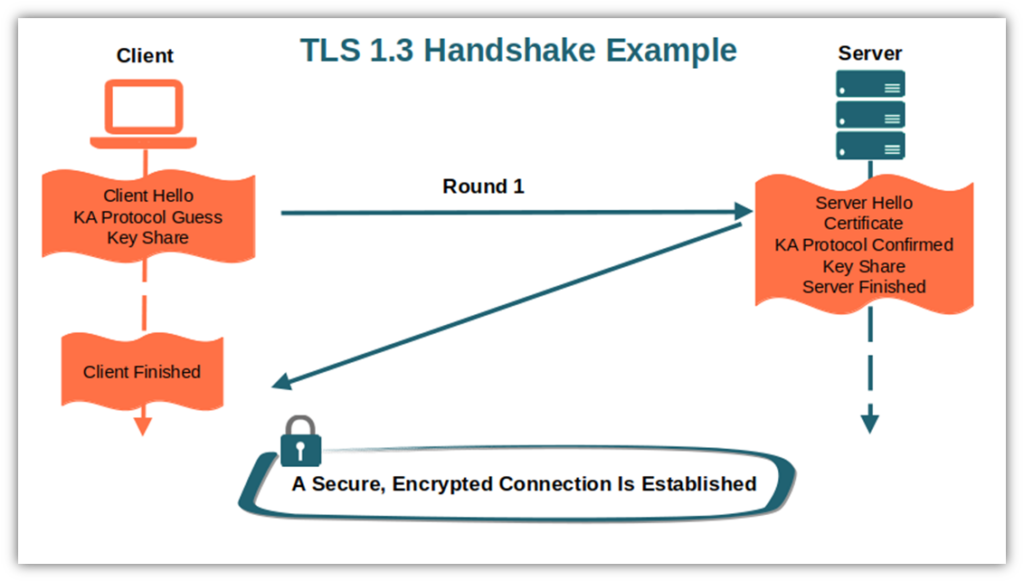
- Improves handshake performance and efficiency. Reducing the steps needed to establish an encrypted connection to a single round guarantees a faster handshake process at scale.
- Removes the obsolete and insecure algorithms still in use in TLS 1.2. No more SHA-1, MD5, or RC4. This means the connection won’t be vulnerable to attacks like LUCKY 13 (similar to the POODLE attack mentioned earlier) or ROBOT (exploiting an RSA vulnerability in encryption).
- Offers more robust security. How? By mandating the usage of the perfect forward secrecy using the Diffie-Hellman ephemeral (DHE) algorithm. The primary difference? This algorithm generates a unique, one-time symmetric key for each session that’s discarded at the end of the session. This makes it impossible for an attacker to break the encryption of previous sessions even if they manage to get hold of the web server’s private key later.
Still wondering if it’s worth making the leap and implementing TLS 1.3 and finally saying goodbye to the deprecated versions?
- Check out our ultimate deep-dive into the four transport layer security versions, and
- Read on to uncover why transport layer security is so valued by cyber security professionals.
Why Is TLS Important in Cyber Security?
In March 2023, ChatGPT suffered its first data breach. Due to a flaw in an open-source library, some users’ payment details and personal information were exposed. In the same month, the telecom giant AT&T informed 9 million customers that unauthorized malicious party accessed their customer property network information (CPNI).
Sadly, these are just two recent examples showing the level of danger every one of us is exposed to in the digital world. Organizations, private users, customers, you name it — we’re all in the same shaky boat.
Cyber security aims to protect data, networks, and devices against unauthorized access. It’s an arms race against all types of cyber security threats, guarding your assets against cybercriminals. Essentially, it’s about ensuring confidentiality, integrity, and availability of your sensitive data and systems.
Transport layer security is one of the fundamental tools that can help organizations reach those goals as, once implemented it can:
- Protect data in transit from eavesdropping attacks. By establishing an encrypted communication channel, sensitive data (e.g., credit card information and login credentials) exchanged between the client and the server remains private and is protected from theft.
- Guarantee data integrity. TLS protocol signs each transmitted message with a MAC. This enables the recipient to use hash functions to check the integrity of the message by computing and verifying the MAC value. No more tampering or message forgery!
- Safeguard from data breaches. Thanks to authentication that occurs during the handshake, the communicating parties can ensure that they’re who they claim to be, avoiding sensitive information ending up in the wrong hands.
While TLS helps shield organizations from myriads of security incidents, it’s particularly effective in preventing man-in-the-middle attacks. How? Thanks to encryption. When the cybercriminal intercepts a conversation or data transfer between two parties, even if he manages to get hold of the encrypted data, he won’t be able to decrypt it without the recipient’s private key.
TLS is a safety net in the stormy sea of our digital world that, sometimes, can be the difference between the life and death of a business. This is why transport layer security is of primary importance to cyber security.
Now that you know what transport layer security is and why it’s one of the main ingredients of a safe data transfer experience, it’s time to discover the magic behind it and learn how it works.
How Does Transport Layer Security Work?
Let’s go back to the physical world for a moment. Often when you meet someone for the first time, you start with ‘Hello!’ and a handshake. TLS does much the same in the digital world. It begins with a “handshake” to ensure the authenticity of the parties and establish a secure, encrypted connection.
Before it does that, though, the website or email server’s owner must have purchased, installed, and enabled an SSL/TLS certificate issued by a trusted certificate authority (CA). To obtain it, they’ll have to go through a specific validation process that varies depending on the type of certificate chosen:
- Domain validation (DV) certificate. Can be obtained by anyone, including malicious actors, due to its basic validation process. (It only requires you to prove you control the domain.)
- Organization validation (OV) certificate. This is considered business validation because it requires additional checks to verify the authenticity of the requesting organization’s digital identity. Nevertheless, its vetting process is simpler than the one required to obtain an EV certificate. It’s often used for blogs and online forms; it should be the minimum level of validation used for websites that collect sensitive information.
- Extended validation (EV) certificate. It’s the most expensive but guarantees the highest levels of identity validation. The best option for checkout pages and websites dealing with sensitive customers’ information (i.e., banking and financial sites, e-commerce).
So, what does an SSL/TLS certificate do? Essentially, it enables its owner to use encryption through the public key infrastructure and authenticates its identity. It does this by tying the organization’s verified digital identity to the certificate. Can you use an SSL certificate to implement TLS? Of course. TLS/SSL certificates are often also called SSL certificates because, essentially, they do the same thing. They just use the more secure TLS protocols to do it!
Now, let’s go into the nitty-gritty of the process and find out how a TLS handshake works. For this demonstration, we’ll take you through each handshake stage of the most recent and secure version of TLS (version 1.3).
By the way, did you know that the moment you opened this article, your client and web server initiated the connection using exactly the TLS handshake process we’re going to explore? Check your browser’s address bar. Can you spot the padlock icon we mentioned earlier, followed by HTTPS?

As soon as you clicked on this article’s link:
- Your client sent a “Client Hello” message to CheapSSLsecurity.com’s web server. At the same time, it:
- Sent the list of supported cipher suites (i.e., a set of algorithms used to secure communications),
- Guessed the key agreement protocol the server may pick, and
- Shared its public key related to the guessed protocol.
- Our web server replied with its “Server Hello,” which included:
- The chosen key agreement protocol and key share information,
- Its SSL/TLS certificate (i.e., a data file confirming that CheapSSLsecurity.com’s is really authentic and includes its public key), and last but not least,
- A “Server Finished” message.
- As a last step, your client:
- Checked our web server’s certificate (i.e., it authenticated our web server),
- Created the symmetric keys based upon the chosen key agreement protocol and values, and
- Sent to our server the “Client Finished” message.
Since the encrypted connection has been established:
- Both the client and the server use secure HTTPS (i.e., SSL/TLS on top of HTTP).
- Messages have been encrypted and decrypted using the session key that only your client and our web server have (i.e., symmetric encryption).
- A message authentication code (which uses a one-way hash function) has been created and embedded in each message to guarantee data integrity.
Have you ever thought that all this could have happened in the background, in a fraction of a second? Isn’t it brilliant?
Curious to know which TLS versions our blog is supporting? Check it out in four simple steps.
Are your websites still unprotected or are you still using a deprecated version of TLS? Time to batten down the hatches. As Kahlil Gibran once said, “If you reveal your secrets to the wind, you should not blame the wind for revealing them to the trees.”
Final Thoughts on What Transport Layer Security Is in Cyber Security
TLS is a widely used security protocol that helps you:
- Ensure the parties communicating over the internet are who they say they are,
- Protect the transmitted data from prying eyes, and
- Guarantee that the same data hasn’t been altered.
The implementation of the transport layer security protocol will not only protect your customers from redirection to malicious websites. It’ll also shield your organization from DNS-based attacks that could badly damage your brand and reputation.
Your client’s trust is one of your most valuable assets. Don’t leave them in the wrong hands. Because if you don’t take care of your customers, someone else will. Still not convinced? In our next article, we’ll give you a plethora of reasons why you should implement TLS security on your website.