Websites owners worldwide are moving from HTTP to the more secure HTTPS protocol. 95% of internet traffic across Google is now encrypted, going through port 443. But what is exactly HTTPS port 443? And why is it so important for website owners and, above all for e-commerce businesses to use the HTTPS standard port?
In February 2022, IT Governance identified 83 major data breaches worldwide, accounting for 5.1 million breached records. According to IBM’s predictions for 2022, this is just the beginning.
Eavesdroppers, man-in-the-middle attacks, spoofing attacks — you name it, there’s danger lurking around every corner. With so many threats, protecting users online has become a priority for businesses and other organizations that are trying to use everything they have available to stop cybercrimes.
Leveraging the power of HTTPS port 443 can be a simple but effective way to make your website more secure. Using this port to transmit data protects your customer’s sensitive information with modern encryption technology. This article will explore the ins and out of the HTTPS standard port 443. You’ll discover what HTTPS port 443 is, how it works, and how it can help your business reduce the risk of data breaches by creating a secure communication channel between the client and the server.
What Are Networking Ports and What Are They Used For?
Before going into the nitty-gritty of HTTPS port 443, it’s important to understand the definition of network ports in general. A port is a communication endpoint from which data transmissions are sent or received. Devices have many different ports, each of them identified by a different number, like houses’ main doors:
- Port 80 for HTTP web traffic,
- Port 443 default for HTTPS web traffic,
- Port 21 and 22 for file transfer protocol (FTP), and
- Port 25 for outgoing simple mail transfer protocol (SMTP) for example.
When you visit a website, your system connects to the webserver using a dedicated network port (Port 80 or the more secure Port 443, depending on the connection). The web server then sends back the website information to your system through the same port.
Ports can be opened or closed through your firewall or another security mechanism. Unused ports should be kept closed at all times to reduce the risks of hackers using them to gain access to your device or network. Ports work like your main house door: if you leave it open, it can be risky as anyone can get into your home.
What Is HTTPS Port 443? Everything You Need to Know
Now that you have a better idea about how ports work and what they’re used for, we can get down to business and start exploring the world of HTTPS port 443.
Did you notice the padlock icon near the URL in your browser’s address bar when you opened this page? If you look closer, you’ll also see that the web address starts with “HTTPS.” This means that you’re connected to CheapSSLsecurity.com over the HTTPS standard port 443 and that the website is using a website security certificate.
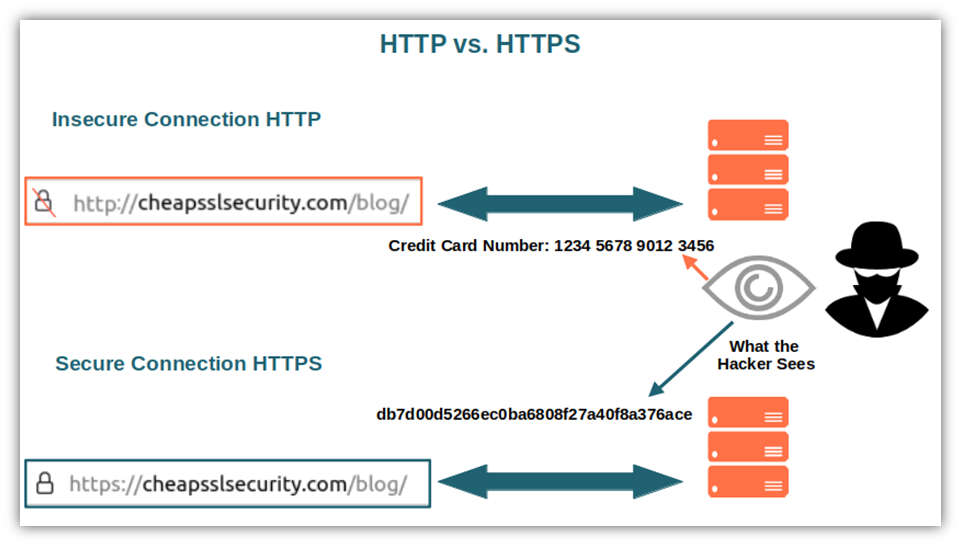
Every time you visit a website, even when you do a web search, you use an HTTP or HTTPS port to access the site. HTTP is an insecure protocol, whereas HTTPS is a secure protocol. With port 443, the connection is much more secure as the information is encrypted through SSL/TLS (secure sockets layer/transport layer security). With port 80, all information is transferred in plaintext and available to anyone to see.
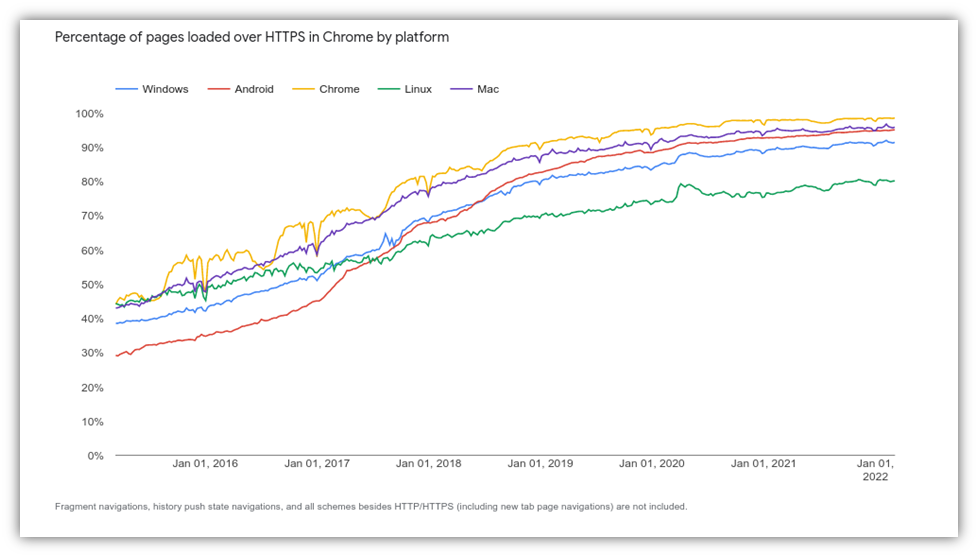
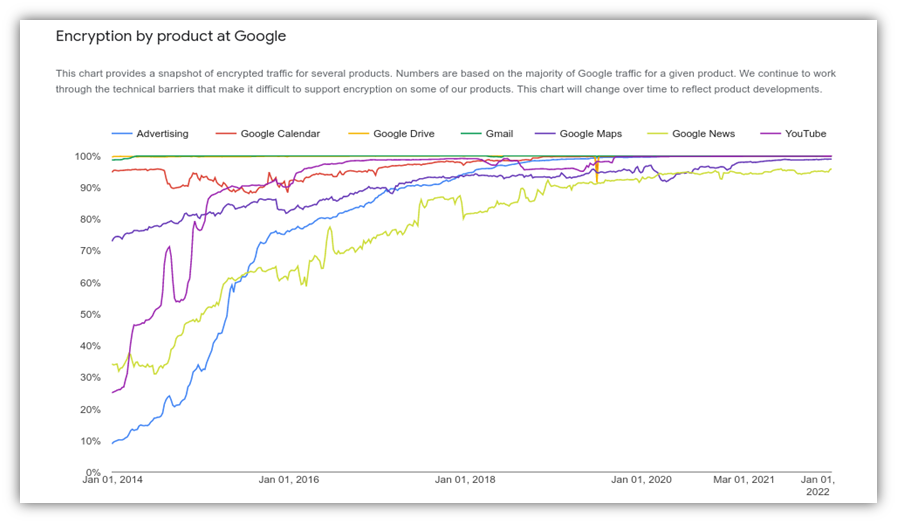
Port 443 is the global standard port for HTTPS traffic. All U.S. federal public domains and subdomains accessible to the public are now transitioning to HTTPS. At the end of January 2022, 95% of Google products were already working on encrypted traffic, and 99% of pages in Chrome are loading over HTTPS connections is constantly growing.
If port 443 is unavailable, the connection may switch over to port 80 automatically, but only if the website configuration allows this type of insecure connection. Otherwise, you’ll likely receive a warning message.
Let’s move on now and discover why this HTTPS standard port can be so crucial to the success of online businesses.
Why HTTPS Port 443 Matters
We all know by now how beneficial an encrypted connection can be, above all when we’re dealing with sensitive information like login details, bank account numbers, passwords just to name a few. But why is it so essential to all organizations owning a website, and particularly to e-commerce businesses?
- It keeps payments secure thanks to the SSL certificate and an encrypted connection. If you have an online business and want to allow your users to pay for your services or goods via debit and/or credit cards, you must have an SSL certificate and encrypt your data. Why? Because it’s a requirement of the Payment Card Industry Data Security Standards (PCI DSS). Would you feel confident in entering credit card information on a site knowing that it will be transmitted as plaintext? I bet you wouldn’t, so why should you expect your customers to feel comfortable doing it?
- It reassures your customers that their data are protected, making them more likely to buy again from you. People are more likely to shop at websites where they feel their data is secure, as demonstrated by Axway Global Consumer Survey. When asked, 75% of the respondents said that they would stop doing business with companies that have experienced data breaches.
- It keeps data secure in transit and helps mitigate man-in-the-middle attacks. HTTPS mitigates man-in-the-middle-attacks by encrypting and authenticating the data as it’s transmitted. This prevents data decryption and traffic interception. On the customer’s side, it’s important to bear in mind that the padlock on the browser address bar and the HTTPS can’t guarantee at 100% the authenticity of the website. Someone could always use a free legitimate SSL/TLS certificate on a fake page to trick users and pass it off as authentic. However, HTTPS remains much safer than a similar HTTP-only web page.
- It increases visibility on Google getting your website placed at a higher rank on its search engine results. In 2014, Google updated its ranking algorithm. The top-ranked search engine added HTTPS as a new metric for search results. Since then, websites encrypted with HTTPS get better placement in Google search and ads compared to those using HTTP. Therefore, with HTTPS, your online business will have more chances to stand out among the highly competitive and crowded online market resulting in higher sales.
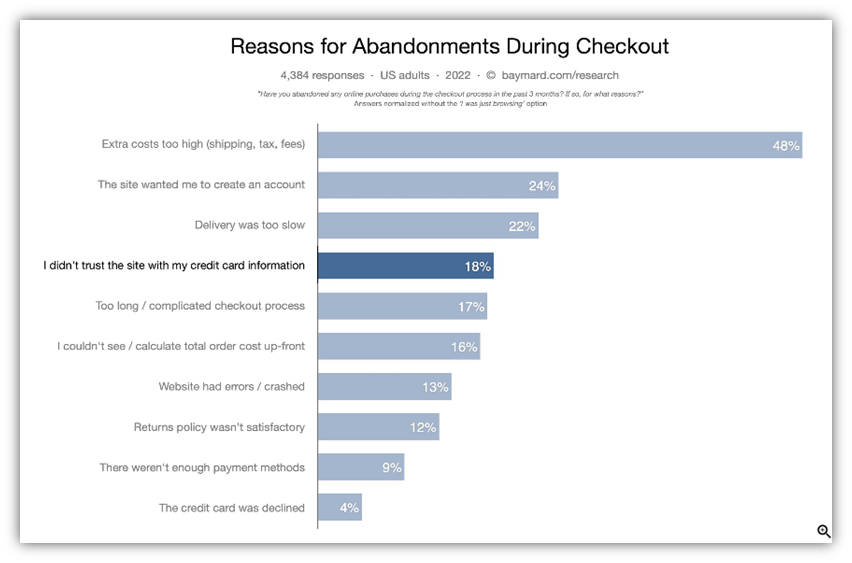
- It can help increase your conversion rate by boosting customer trust. Think about it: if you’d have to buy an expensive smartphone online which website would you choose between:
- Website 1, which uses the insecure HTTP protocol and all transactions go over Port 80
- Website 2, which has a URL that starts with HTTPS (a secure protocol) and all transactions go over Port 443
I guess I already know the answer. Baymard’s recent Ecommerce Checkout Usability study confirms this, showing that 18% of customers don’t complete their purchase when they don’t trust a site. Why? Because in online purchasing, security and trust do have a major impact on choices and the amount spent.
- It helps you get rid of the “not secure” warning displayed by browsers, thus avoiding losing customers due to a lack of trust. Since a few years Chrome, used by more than 60% of all internet users worldwide, flags HTTP-only websites and online forms as not secure. Google is also flagging websites without SSL certificates as dangerous. Imagine how a customer would feel when, before entering his credit card details, its browser would display a warning stating that the site is not secure. Not good, right?
There are many other benefits that come with HTTPS port 443, but seeing as how nothing is perfect, even port 443 has its limitations. Just to give you an example, it won’t be able to guarantee you 100% protection from any form of cyber attack: in the real world, this is simply impossible.
As Benjamin Franklin once said, “An ounce of prevention is worth a pound of cure.” Therefore, it’s worth the extra effort of moving your website to the HTTPS standard port.
But how does HTTPS port 443 work? Let’s get a bit more technical and find it out.
How the HTTPS Standard Port 443 Works
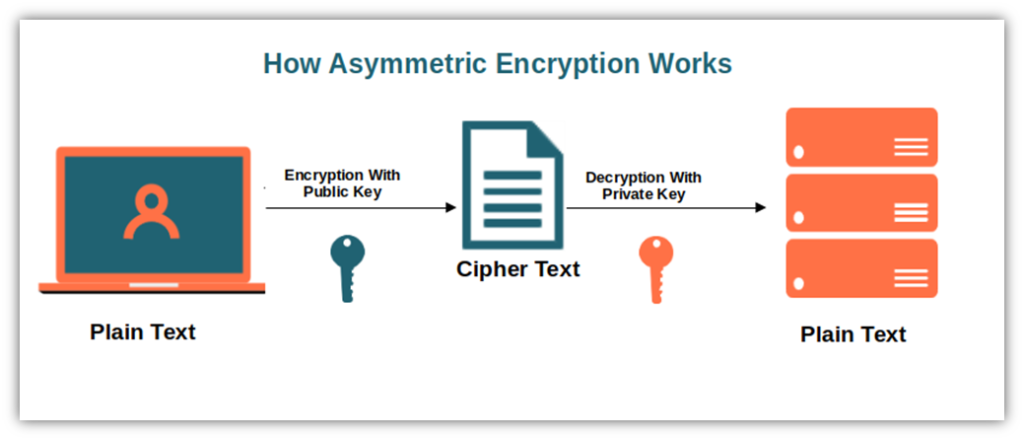
We’ve said that when you go to a website via port 433, the whole data transmission is encrypted. How? Through the use of asymmetric encryption to securely exchange information. Once done, the two parties switch over to the faster and less resource-intensive symmetric encryption. In short, an algorithm in combination with a cryptographic key transforms the original data into an unreadable output of random numbers, special characters, and letters that only the key holder can decipher.
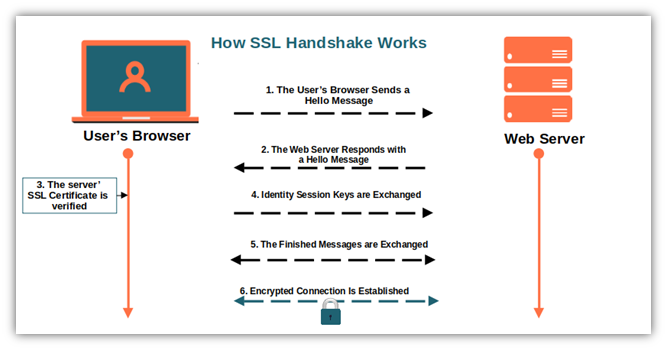
To be able to establish an encrypted connection, though, the browser and the server must first negotiate the secure exchange of information. This is done through the SSL/TLS handshake process.
Time to Negotiate: A Step-by-Step Look at the SSL/TLS Handshake
During this process, the SSL/TLS client and server agree on the version of the protocol to use, which cipher suite (set of algorithms) will be used to encrypt communication, authenticate the server, and exchange secret keys. Depending on the supported cipher suite, the TLS version used, and on the key algorithm chosen, the exact steps may vary. Let’s look at a basic version of the TLS 1.2 handshake as an example of how this process works:
The Browser Starts Sending a Hello Message to the Server
The message will include the SSL/TLS versions supported by the browser, the supported cipher suite, and a random byte string called “client random” that will be used for computation.
The Server Responds with a Hello Message
Along with this first response, the server also sends messages that contain its SSL certificate, the chosen cipher suite, and a string of random bytes (server random). If the browser and server don’t have any shared secure communication capabilities, the server will end the connection then and there.
The Browser Verifies the Server’s Identity Using the SSL Certificate
Using the certificate’s digital signature and other information (including its public key), the browser verifies with the certification authority (CA) that issued the SSL certificate that the server is authentic and that it’s the actual domain owner.
The Browser and the Server Generate Session Keys
The browser sends a random string of bytes (premaster secret) encrypted with the server’s public key included in the SSL certificate. The server decrypts it, and both parties generate the session keys.
The Finished Message Is Exchanged and the Process Is Complete
Both the browser and the server send a finished message encrypted respectively with the private key and the session key indicating that the handshake process is completed. The server sends back a message to tell the browser that it’s now using changing over to the secure communication channel.
Secure Encryption Has Been Achieved
The secure symmetric encryption has been set up successfully. From now onward:
- All information exchanged between the browser and the server will be encrypted and protected by prying eyes.
- Every exchange of information will be done using the authorized algorithm and keys.
- A small padlock will appear on the URL bar confirming the user that the website he’s visiting is using a secure connection.
Note: The more recent TLS 1.3 handshake process is similar to the TLS 1.2 but it’s faster as it involves one round trip instead than three. Learn more about it in our article “TLS 1.3: Everything You Need to Know.”
Houston, We Have a Problem
What happens if something goes wrong? In case of issues with the certificate (e.g., the certificate has expired, it’s incorrect or improperly configured), the user will get an error message about the handshake failing and the secure connection will fail.
The most common reasons for SSL handshake failure and suggested solutions are:
| The Causes of the SSL/TLS Handshake Failure | What to Do to Fix These Issues |
| The certificate is invalid. | The website owner should verify your SSL certificate’s details and ensure that it’s still valid. |
| The browser is set on the wrong date or time. | The user should correct his browser’s date or time. |
| The browser and the server don’t support the same SSL version. | The user should update his browser’s SSL version. |
| The browser and the server use different cipher suites. | The user and the website owner should check what kind of cipher suites they support. |
| The connection is being intercepted by a third party on the browser’ side. | Here we must be very careful as it could be a case of a man-in-the-middle attack we mentioned earlier. If this is not the case: The user could create an exception and allowlist (whitelist) the website, but only if he’s 100% sure that this interception is not malicious (e.g., wrong firewall configuration). The website owner will have to check his server configuration. |
| The browser has a configuration causing the handshake failure. | The user should add the website to its allow list or, try another browser. |
What HTTPS Port 443 Doesn’t Do
When dealing with sensitive data online, basic precautions are never enough. Therefore, it’s important to keep in mind what HTTPS cannot protect:
- It doesn’t protect users against fingerprinting attacks.
- Some less sensitive information can still be read (and misused) by the bad guys:
- What websites you’re visiting,
- Your IP address and location,
- How frequently you visit websites,
- Message size.
- It cannot guarantee you that the website is controlled by a scammer.
Last but not least, using HTTPS Port 443 won’t make your browsing private.
Final Thoughts on Your Guide to HTTPS Port 443
As you can see, setting up an HTTPS connection over Port 443 will do more than only add an extra layer of security to your online business. Your website’s visibility will improve and so will your credibility and customers’ trust.
Online shopping will continue to grow. With most customers thinking twice before buying products or services from insecure websites due to the ever-growing number of data breaches, providing a bulletproof, secure transaction has become critical to every online retailer’s success.
Say no to those red warning messages “this website is not secure”! Offer a hassle-free, safe shopping experience to your customers with HTTPS Port 443.





