How well are small businesses implementing basic security precautions on their websites? I crawled 60,140 websites…here’s what I found.
If you follow the daily chatter in the website security and encryption space, you’re probably used to hearing positive numbers such as: over 90% of web traffic is now secure. That’s true, and it’s a great statistic, but it’s a number that tends to be skewed by a few very big websites. Most internet traffic is to a handful of large websites—Google alone gets billions of website visits per day…more than most of the websites on the internet combined.
So, What About Smaller Websites?
We all know that the big players like Google and Wikipedia have implemented web security best practices such as HTTPS. But what about small business websites? How well are they doing at implementing website security best practices?
That’s what I wanted to find out, so I built a web crawler and checked 60,140 websites to find out the answers to two simple security best practices:
- Are sites use HTTPS by default?
- Are sites using an up-to-date CMS?
Those are the main two questions I wanted to answer, but I also found some other interesting facts along the way.
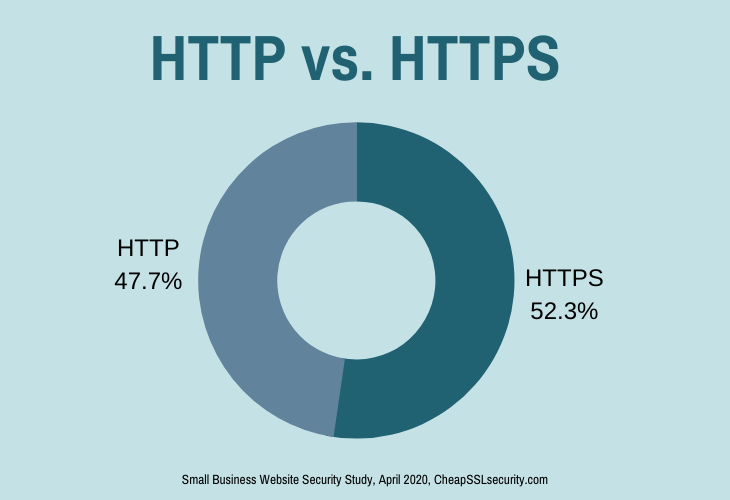
Half of Small Websites Still Haven’t Switched To HTTPS
The big players on the internet may have all made the switch to HTTPS, but many smaller sites haven’t. My crawl found that only 52% of small websites have made the switch to HTTPS, leaving nearly half of websites still using HTTP by default:
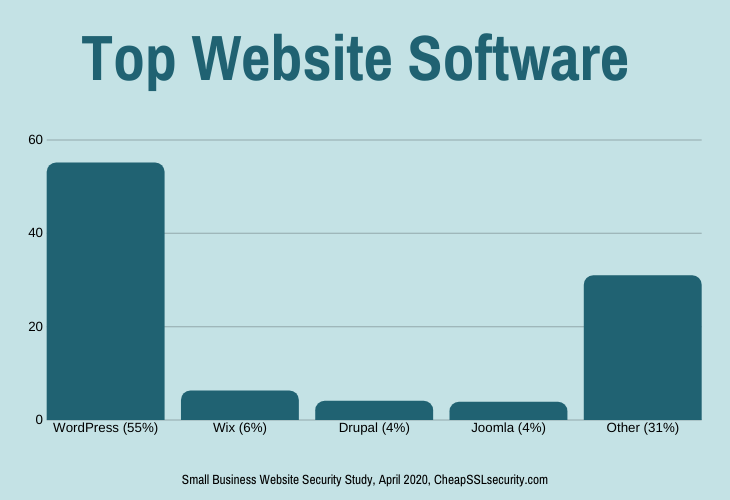
WordPress Is the Leader: 55% Of Websites Run WordPress
I’ve heard people joke that the world wide web runs on WordPress. That’s not too far from the truth, at least for small business websites. WordPress is by far the market leader, although Wix, Joomla, and Drupal also have noticeable market share.
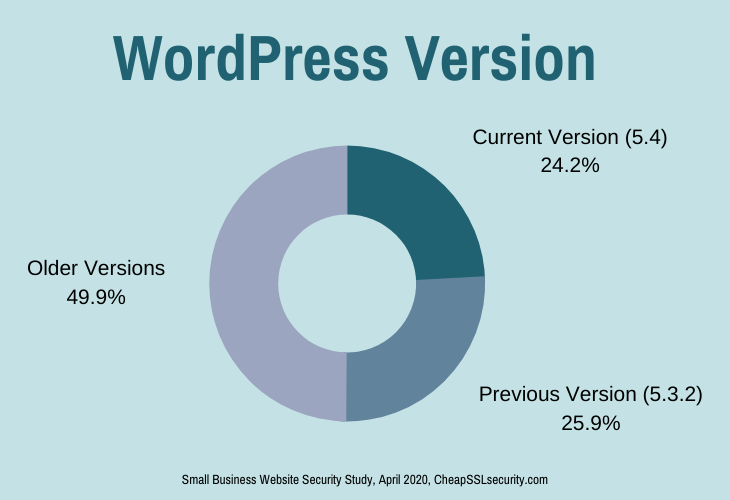
76% Of WordPress Sites Are Running Older Versions of the Software
I ran this web crawl 15 days after the current version of WordPress (5.4) was released, so there was plenty of time for sites to have already updated to the latest version. Still, fewer than 1 in 4 websites were running the current version, and approximately half of them were 2 or more versions behind.
Thanks to WordPress’s update policy, not all of the older versions have security vulnerabilities, but some of them definitely do.
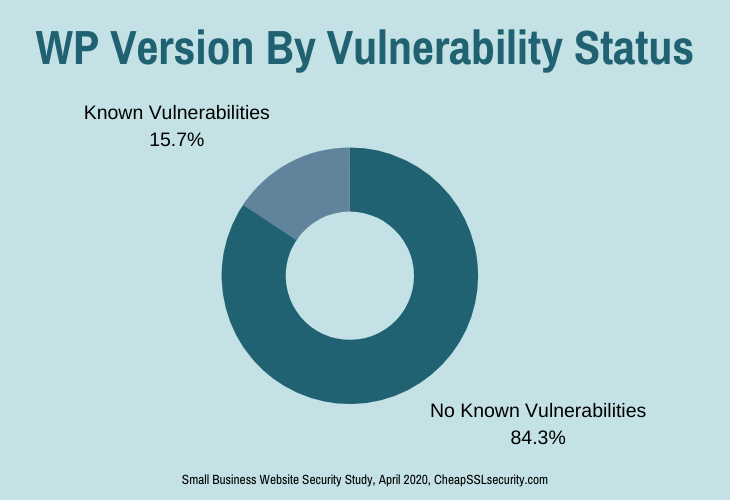
Many Sites Are Running WordPress Versions with Multiple Known Vulnerabilities
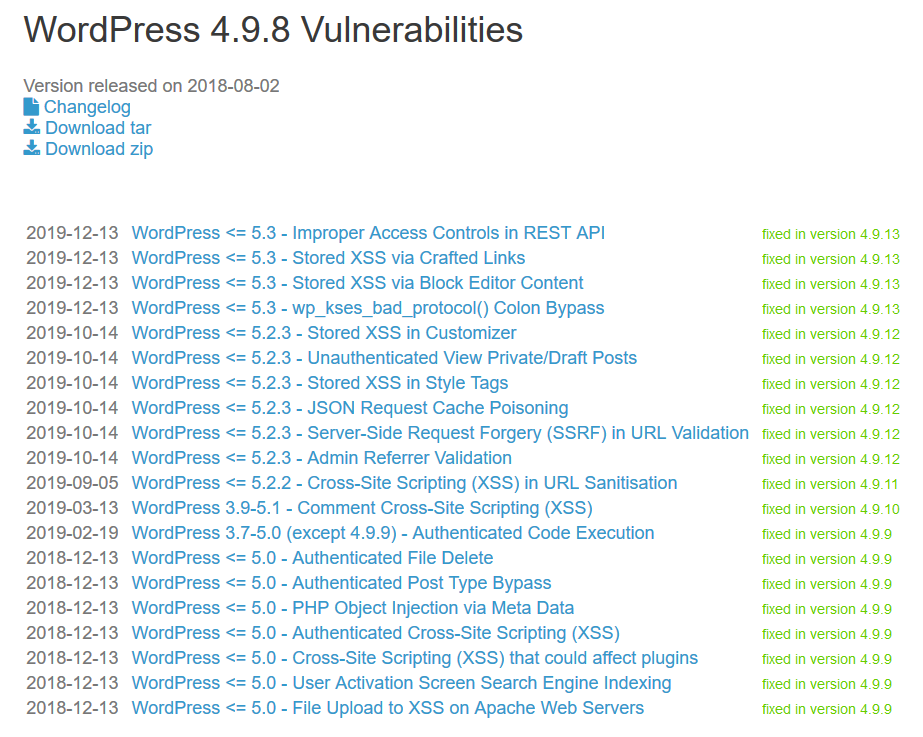
To find out how many of these sites have significant security issues related to their software version, I used wpvulndb.com to identify which WordPress versions have known vulnerabilities in the core WordPress software. Nearly 1 in 6 sites has a known vulnerability in their core WordPress software.
Important note: This is only looking at known vulnerabilities in the WordPress core software. That’s not looking at vulnerabilities in WordPress themes or plugins, implementation errors, or server software. Running a full vulnerability scan or penetration test would undoubtedly uncover many more vulnerabilities.
Here’s a screenshot showing known vulnerabilities for the WordPress version used by a couple hundred sites found in this study:
If a hacker used one of these to compromise the site, they could send spam emails, do shady SEO, mine cryptocurrency, distribute malware, or any number of nefarious things.
Some Sites Are Running WordPress Software That’s 14 Years Out of Date!
I knew a lot of sites were lagging behind when it comes to CMS updates, but I was actually a bit surprised to see how far out of date some websites actually are. Here’s a highlight of the worst offenders:
| WP Release Year | Number of Sites | Percentage of WP Sites |
| 2018 | 406 | 4.2% |
| 2017 | 175 | 1.8% |
| 2016 | 85 | 0.9% |
| 2010-2015 | 210 | 2.2% |
| <2010 | 37 | 0.4% |
In total, 11.3% of the WordPress sites were running versions of the software that were more than a year old.
The worst offender was a site running WordPress 1.5, which was released February 17, 2005:
Conclusion: Most Small Websites Aren’t Implementing Basic Security
This data leads me to the unfortunate conclusion that half or more small websites aren’t implementing even the most basic security precautions—timely updates and Always On SSL.
However, there are signs of hope, too—although many sites are using older versions of the software, most of them don’t have known vulnerabilities. This appears to be due to WordPress’s update policy-releasing security fixes for old versions and enabling auto-updates for minor releases.
More About How I Collected the Data
With studies like this, the devil’s often in the details. The methodology used can influence the outcome in a variety of ways. If you’re curious about how I did it (and how that might impact the results), here are the basics of how I collected and analyzed data for this study:
- I used the Open Page Rank Project to get a list of the top 1 million websites on the internet.
- I selected 80,000 domains from around rank 900,000 on the list. This ensured that I was focused on smaller websites, not the big players of the web. At the same time, we’re still talking about websites that get some amount of attention and traffic.
- I used a custom crawler to check each website’s homepage to identify whether it uses HTTPs by default (Always On SSL) and to attempt to identify the CMS and version in use.
- Websites that returned any type of error were removed.
- The collected data was then cleaned and analyzed in Microsoft Excel and PowerBI.