Ring, Ring! Hello? It’s vishing calling. In the first six months of 2022, mobile users received an astonishing 100 billion scam calls that resulted in financial losses of $40 billion. Discover how vishing works and learn to protect yourself and your organization from it
In August 2020, the Cybersecurity and Infrastructure Agency (CISA) and the Federal Bureau of Investigation (FBI) issued a warning that vishing attacks were targeting remote workers. Fast forward to mid-2022: vishing attacks have reached an all-time high, increasing by almost 550% in the last 12 months.
The same research shows that vishing attacks have now overtaken business email compromise (BEC) in the threat landscape, becoming the second most reported threat. BEC scams are a subset of phishing, a category of scams and cyber attacks that bad guys use to get their hands on sensitive information. Virtually all types of phishing scams involve social engineering tactics in one form or another.
You’re probably familiar with phishing, which is an overarching category of cyber attacks and a specific type of attack. Now, it’s time to get to know its evil brother: vishing. In this article, you’ll learn everything you need to know about voice phishing scams:
- What is it (voice phishing meaning),
- How to recognize it (signs of voice phishing scams), and
- How you can protect yourself and your business.
Are you ready? Let’s go vishing!
Vishing Definition: What Is Vishing and Why Is It a Concern?
Let’s put this in the simplest terms possible: Voice + phishing = vishing.
Basically, vishing is a form of phishing. In this case, the cybercriminal uses a voice call to try to trick the victim into revealing private or sensitive information. This maneuver aims to get sensitive information they can sell or use to commit further crimes.
While phishing exploits email communications to entice the victim to click on a malicious or phony link, and smishing utilizes text messages for the same purpose, with vishing the attacker uses a much older (and common) tool: phone calls. That’s why this type of attack is also called voice phishing scam.
OK. So, based on the above vishing definition, we now know that this attack type is basically a subcategory of phishing.
Some Attackers Pair Vishing With Other Phishing Attack Approaches
In some cases, cybercriminals may even use a combination of attack methods. How?
- Step one: phishing. They could start the attack by sending an urgent phishing email stating that service for your favorite app has been automatically renewed. The email continues, saying that you’ll have to call a specific phone number to get the payment refunded.
- Step two: vishing. Once you call the number, they’ll use all sorts of social engineering tactics to get you to make a payment to a bogus bank account or even download remote desktop software onto your device to give them access to it. These social engineering tactics include coercion and/or intimidation to get you to do what they say.
See? It started with phishing and escalated into a vishing scam. A real-life example was the BazaCall attack. The victims were pushed to unknowingly download malware after receiving emails prompting them to contact a phony call center run by the attackers.
But how does vishing work exactly? What are the latest techniques used by cybercriminals that make vishing three times more effective than traditional phishing (as reported by the latest IBM’s X-Force Threat Intelligence report)? Let’s find it out.
How Does Vishing Work?
The attacker gathers enough information about the victim and/or their organization by checking it on social media channels like YouTube and LinkedIn, two of the top open-source intelligence (OSINT) sources. Once done, the attacker calls the victim, posing as a trusted person (e.g., a bank or a government agent — more on this later in this article).
To push the target into revealing sensitive information or doing something they normally wouldn’t, the criminal then uses social engineering techniques to exploit typical human instincts and traits like
- Fear,
- Desire to help,
- Curiosity,
- Trust and/or other emotions
Last but not least, the attacker also takes advantage of the fact that a person on a phone call is more likely to do something without stopping to think about it first. If successful, like in more than 323,000 cases reported to the FBI in 2021 (which registered total financial losses of over $44 million), the attacker will then be able to access the victim’s bank account, credit cards, or the whole organization’s internal network.
This is just one example of vishing, though. An attacker could also use:
- Automatic calls. In this case, they’d exploit voice-over IP (VoIP) technology asking the victim to confirm personal information by simply pushing specific telephone keys.
- Hybrid vishing. Also called callback phishing, an attacker sends an email to the victim that includes a phony telephone number to contact urgently.
- Artificial intelligence-based vishing (i.e., “deepfakes”). Where scammers utilize commercially available AI software to create the voice of a CEO or the person they’re pretending to be. The first known case of this type of vishing attack reportedly cost a U.K. energy firm $243,000.
Got it? To better understand voice phishing meaning, why don’t you check out this entertaining two-minute video of a real-life vishing call? Don’t miss it! I bet you won’t believe how easy it is for a cybercriminal to scam you.
My Real-World Experience of a Vishing Attempt
One day, when I was working as a mail application security engineer, the phone rang in my office. It was the switchboard operator asking me to take a call from someone who apparently knew me (or so she said).
Due to the nature of my job, I was pretty reluctant. The operator couldn’t give me a name or a phone number to call back. However, as she put the person through before I could further argue, I had to deal with it.
The caller on the phone didn’t introduce herself (first alarm bell). She immediately started talking about how interested she was in getting statistics and insights on our email application cybersecurity attacks identification, and protection techniques (second alarm bell). I asked her why. Her answer was that she was working on a report that would have been published on a well-known IT news website that very same week (third alarm bell).
When she finally told me her name, I asked her how she got my telephone number and why she didn’t contact our press department first. She said she tried to contact a colleague of mine she knew (the person she mentioned was indeed one of my colleagues), but the call went directly to the switchboard. This sounded all too odd.
I told her to stay on the line so that I could put her through my colleague as he was at his desk. At that point, she blubbered something and told me she’ll have to call me back. Did she ever? Of course not. And, as suspected, it turns out that my colleague didn’t know her.
How did I know that something was smelling vishy? It’s elementary, my dear Watson, as Sherlock would say. I noted some of the following four signs of vishing attempts that cybercriminals commonly use.
Four Tell-Tale Signs of a Vishing Attack
In most vishing attempts, the caller will:
- Pose as (impersonate) an authority. Although this didn’t occur in the situation I described, it’s still important to mention that you should always be wary if the caller claims to be an authority (e.g., IRS, Medicare, law enforcement) or another trusted figure and asks you for personal information or money. Authorities don’t do that; they send you official letters if needed.
- Create a sense of urgency. Like in my example, the lady said she wanted to get the report ready that very same week. The attacker might also prey on other emotions like fear or curiosity to entice or motivate you to do something you normally wouldn’t.
- Use an unknown number. This one speaks for itself. Why should someone acting in good faith hide their phone number? By the way, cybercriminals often use apps and other technologies to spoof trusted phone numbers to appear more credible. Therefore, never lower your guard.
- Try to get you to send money or to share sensitive info. Remember: it doesn’t matter the reason the criminal will come up with, do not give in to their demands. They’ll probably try to use the information gathered during their investigation to make you crack. Don’t. In the situation I described, the lady tried to find out about our organization’s security mechanisms by claiming she knew my colleague (she didn’t) to establish a rapport.
Voice Phishing: Five Common Examples
Did you know that 75% of cybersecurity professionals interviewed by CS Hub consider social engineering and phishing attacks (including vishing) the top cybersecurity threat? Let’s have a look at a few examples of the most common voice phishing scams and their resulting costs:
| Vishing Example | Consequences for Vishing Targets |
| 1. Tech Support Voice Phishing Scam | More than $347 million in losses in 2021 (source: FBI Internet Crime Report). |
| 2. Bank/Credit Card Vishing Scam | More than $282 million in losses (U.K. authorized pushed payment fraud). |
| 3. Internal Revenue Service (IRS) Tax Voice Phishing Scam | Stolen tax ID numbers and refunds. |
| 4. Health Sector/Social Security Vishing Scam | Stolen protected health information (PHI) and refunds. |
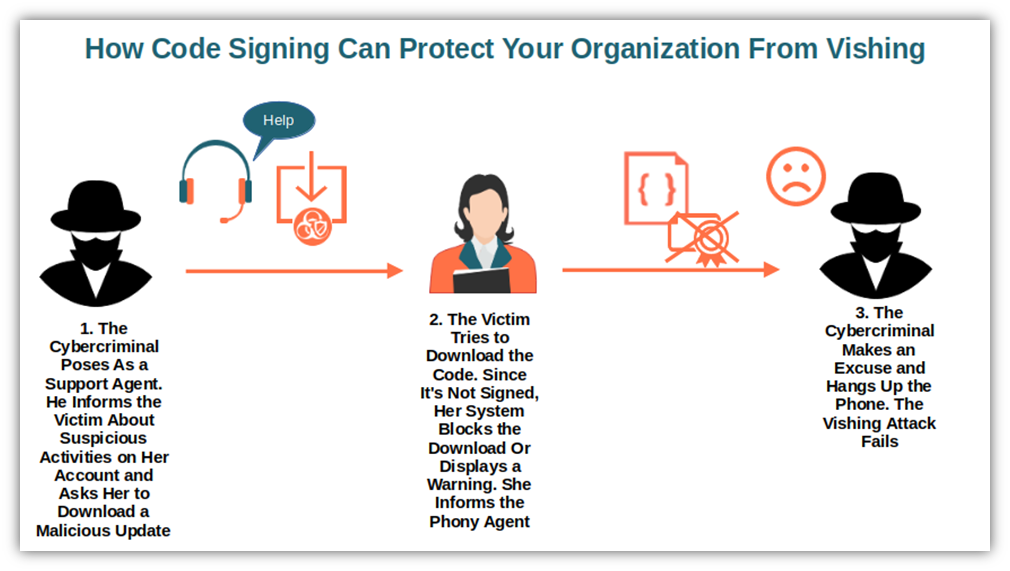
1. Tech Support Voice Phishing Scams
An attacker poses as a tech support agent from a well-known IT company like Microsoft or Apple and reports suspicious activity on your online account or software. If you fall for it, they may ask you to install a malicious software update that will compromise your machine and open it to a multitude of consequences.
Does it happen often? Judge it by yourself: The latest FBI Internet Crime Report (which we linked to at the beginning of this article) shows that in 2021, tech support vishing accounted for more than $347 million in losses. That’s 137% more than in 2020. That’s bad, but it could have been much worse if the FBI’s Recovery Asset Team (RAT) hadn’t been involved after complaints were raised with the Internet Claim Complaint Center (IC3). In October 2021, for example, the RAT halted an unauthorized wire transfer of $53,000 that resulted from a tech support vishing scam.

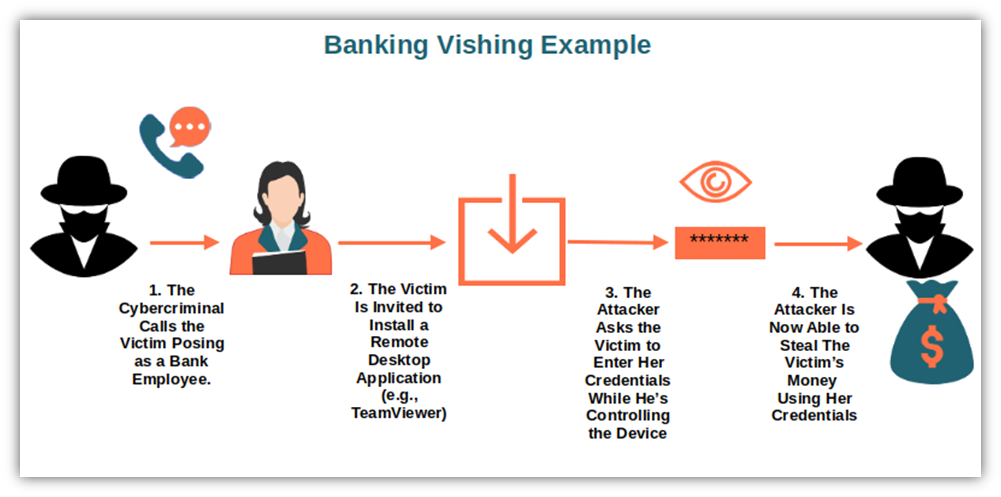
2. Bank/Credit Card Vishing Scams
In this scenario, the cybercriminal will present themself as a bank/credit card company employee or another financial institution’s representative. In some cases, the attackers may use pre-recorded messages to trick you into providing your account details, credentials, or PIN numbers. They can then use the information to validate a fraudulent transaction.
The latest U.K. Finance’s report shows that more than 95,000 successful authorized push payment (APP) scams were identified within the first six months of 2022. The victims of this bank/credit card vishing scam were tricked into approving payments that would go directly to the cybercriminal’s bank account. The total loss? More than £249 million — that’s more than 282 million in U.S. dollars.
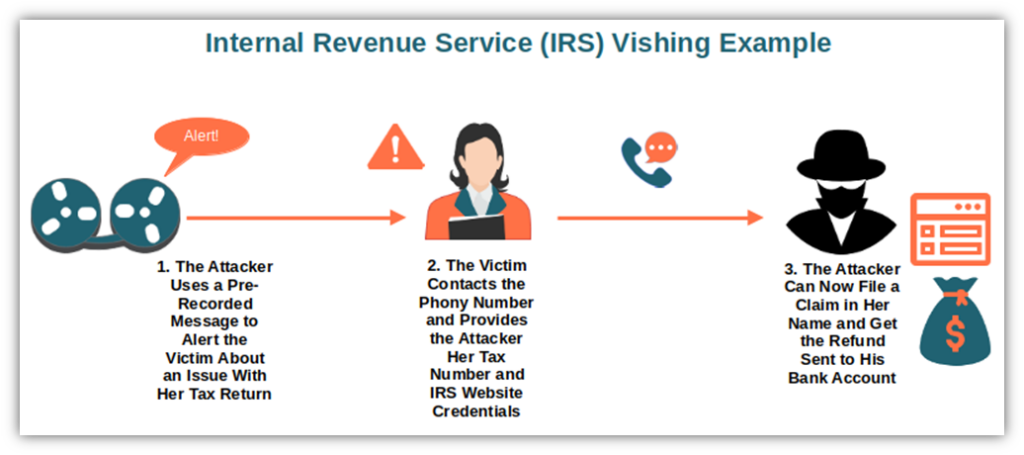
3. Internal Revenue Service (IRS) Tax Voice Phishing Scams
In this scenario, the attacker contacts the victim using a recorded message. The message explains that due to an issue with the target’s tax return, they should contact the bogus number provided immediately to rectify some type of situation. (Of course, it’s just so the attacker can get the victim on the phone to scam them out of money or personal information.) The message usually includes a threatening warning (e.g., a warrant for arrest will be issued, steep fines or penalties, etc.) to add more drama and fear to the situation to instigate an immediate response by the target.
Interested in some real-life samples? The Canadian Revenue Agency collected a few transcript samples. While the U.S. IRS put together an info page with tips and suggestions to help you spot IRS-related vishing.
Even if “tax season is prime time for phone scams,” as written on the IRS’ Tax scams/consumers alert page, IRS tax vishing scams happen any time of the year. This type of voice phishing is so dangerous and common that:
- It’s included in the IRS “dirty dozen list” — a list of the worst tax scams the IRS compiles every year.
- It’s been in the top five U.S. government impostor scams since 2014.
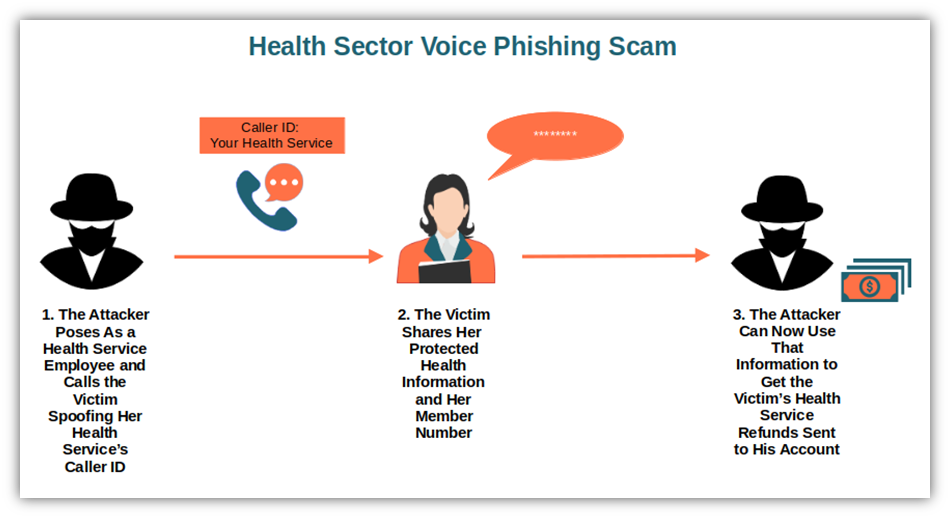
4. Health Sector/Social Security Vishing Scams
In September 2020, attackers called Spectrum Health’s patients posing as employees of the Michigan health system to steal their protected health information (PHI). For the call to appear legitimate, the attackers spoofed Spectrum Health’s caller ID. Once the victim was hooked, they requested PHI and the member’s number. This is a typical example of health sector vishing.
Based on the Health Sector Cybersecurity Coordination Center (HC3)’s analysis note, vishing attacks are on the rise. Scammers just love your PHI and social security information. They love these types of data so much that four positions out of the top five vishing calls identified by First Orion are all related to the health and social security sector.
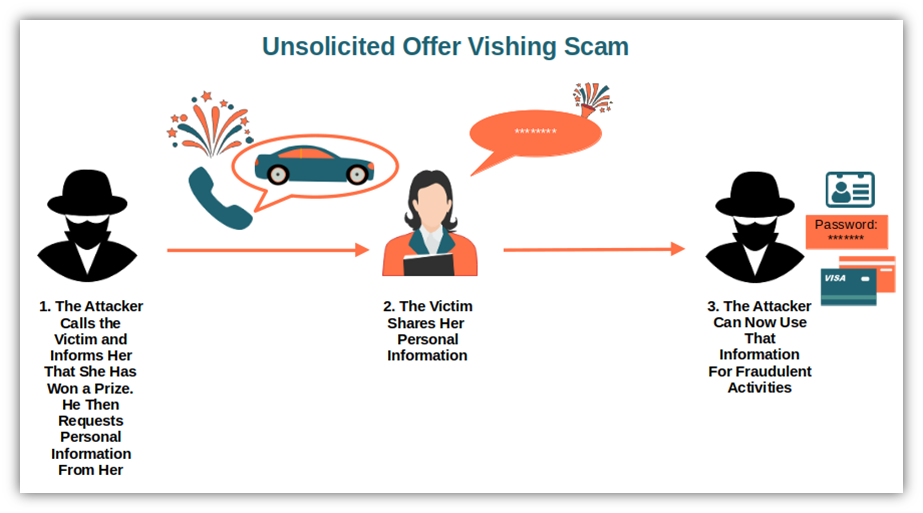
5. Unsolicited Offers Voice Phishing Scams
“Hey, you’re the one-millionth subscriber! Congratulations! You won a new Tesla! To claim your prize, you just have to provide us some personal information…”
OK, sorry to disappoint you, but there’s no competition and you didn’t win anything. It was just a trick to get you to cooperate and provide info. This is an example of a vishing call you may receive in which an attacker tries to lure you into providing sensitive information in exchange for a supposed prize.
Telemarketing fraud, where the attacker tries to steal personal information or money by luring the victim with phony lottery prizes or advantageous offers, is also part of this category. The Office of the Attorney General reports that Americans lose an average of $40 billion a year as a result of falling victim to such telemarketing vishing scams.
OK, I guess you got the picture by now. Vishing isn’t as fun as going fishing. It can also result in devastating effects for your organization and customers. How can you protect yourself and your organization from voice phishing attacks? This is what we’re going to see next. Do you want to get suggestions from North Carolinian victims of telemarketing scams? Check out this heartbreaking but informative video from the North Carolina Attorney General’s Office (NCAGO) YouTube page:
9 Ways to Protect Your Business From Vishing
Know your enemy and half of the battle is won. What about the other half? How can you really prevent voice phishing scams? Follow our simple but effective tips:
- Avoid robocalls. Did you answer a phone call and realize that you aren’t speaking to a human being, so you hung up? No worries, you won’t sound rude. Robots don’t have feelings, so don’t worry about hurting them. Just hang up and go about your business.
- Don’t respond to voice automated prompts. Please press one, please press three, and say “yes” to speak with an operator — I hate those automated prompts. Even when they’re played by legit entities, I find them confusing; it’s too easy to press the wrong button. Now, imagine what would happen with a vishing call. An attacker could record your voice responses so they can use them for fraudulent activities (including pretending to be you for authentication purposes on your legitimate accounts).
- Verify the caller’s identity. How? The simple method is to use the official channels. When I was working as a mail application security engineer, I got regular phone calls from law enforcement officials who requested I disclose sensitive information about cybercriminal cases. How could I tell whether the person calling was really a police officer? I couldn’t. Therefore, I always preferred to call them back by dialing the official police department phone number we had on record. You can do the same: ask for the caller’s name and call him back using the phone number available on the caller’s company website. Never call back using a number the suspicious person provides.
- Never share sensitive information over the phone. Did you get a call from someone claiming to be an IRS agent? Did he ask you for your tax number or any other personal information? Don’t forget that government agencies, banks, or credit card companies will never ask for your personal information over the phone. So, if something smells fishy — I mean, vishy — then trust your gut and hang up the phone.
But that’s not all. There are things that you can do to protect your business even before you receive a vishing call:
- Train your employees (and your family members, too). Do you want to protect your organization from the consequences of voice phishing scams? Teach your employees how to recognize them. Sharing this article with them could be the first step. Ensure you have policies in place indicating the process to follow to verify caller identities and what information can be revealed (and to whom).
- Use strong authentication methods. If a voice phishing scam succeeds, using strong authentication methods will add another layer of security to help you prevent or minimize the damage. There are several options you can go for. Among them are two- or multi-factor authentication (MFA) or passwordless authentication, the latter of which relies on the same principle of publicly trusted digital certificates.
- Digitally sign your emails. Digitally signing your emails enables you to attach a verifiable digital signature to your messages. This helps you prove that the email is legitimate (sent by you) and authentic (unaltered). This way, if one of your employees receives an unsigned message, they’ll probably think twice before calling the dodgy phone number in it.

- Don’t allow unsigned software downloads. Do you remember the tech support vishing scam example? The victim was asked to download a software update infected with malware. Often, attackers don’t bother to add a code signing certificate to their malicious software (which would show users and their operating systems that an application is authentic and hasn’t been altered since it was signed). Why? Because it costs money and requires undergoing validation by a publicly trusted CA that adheres to strict standards. Instead, consider restricting the type of allowed downloads employees can do by:
- Using a device management software (i.e., Microsoft Endpoint Manager)
- Setting specific policies on your firewall (if applicable).
9. Join the National Do Not Call Registry. It’s free and it tells telemarketers that you don’t want to receive their calls. OK, cybercriminals can always call you illegally, but it’ll help to reduce the number of potential vishing. You’re not based in the U.S.? No problem; there are similar programs in other countries, too, like the Telephone Preference Service in the U.K. or Canada’s National Do Not Call List.
Last but not least, many governments and law enforcement agencies provide flyers and quick guides on vishing attack prevention. Don’t miss them; they can be useful reminders to stick on your desk or near your phone:
- Europol’s vishing advice for corporate employees.
- Europol and European Banking Federation’s vishing infographic.
- Europol Federal Trade Commission’s caller ID spoofing and robocalls infographics.
The big takeaway here is if you receive an unexpected or unsolicited phone call or email prompting you to call, don’t take the bait! All that awaits you is heartache, financial losses, and many sleepless nights.
Final Thoughts on What Is Voice Phishing? A Vishing Definition and Meaning
Phishing, smishing, vishing. Criminals are trying everything to get what they want and will use virtually any means to do it. Vishing attacks are the most difficult to dodge among those three types of cyber attacge. Why? Because they’re not only tapping into emotions like fear and panic but also leveraging the fact that once on the phone, you don’t have enough time to reflect.
You’ve now learned some preventive measures (and a few key red flags) that, from now onward, should ring alarm bells to your ears and help protect you from such attacks:
- The caller’s number is unknown.
- The caller asks you for sensitive or personal information.
- The caller claims to be from a government agency or another position of authority.
Next time you receive a call, pause and think twice before picking up the phone. That few seconds’ pause might save you from being the next vishing victim.



![A 6-Minute Overview of the PCI DSS Requirements [For PCI DSS v.4.0]](https://cheapsslsecurity.com/blog/wp-content/uploads/2022/12/pci-dss-requirements-v4-370x245.jpg)