We’ll quickly explore one of cybercriminals’ favorite pastimes and why it’s a threat to organizations and consumers alike
The dastardly art of scamming people is one that’s been around in one form or another since, well, pretty much the beginning of recorded history. It’s just that in our modern, digital world, this criminal method has taken on new forms and methods, which we now refer to as phishing.
Verizon reports in its 2021 Data Breach Investigations Report (DBIR) that more than one-in-three data breaches involve the use of phishing. This cyber crime statistic is particularly worrisome because credential theft is one of the primary goals of phishing attacks, and Proofpoint reports in their 2022 report that credential theft has an average cost of nearly $805,000 per incident.
But what is phishing and why is it such a problem for the people (and organizations) that cybercriminals are trying to hook? We’ll answer these questions and check out a few phishing examples as well.
What Is Phishing? A Phishing Definition
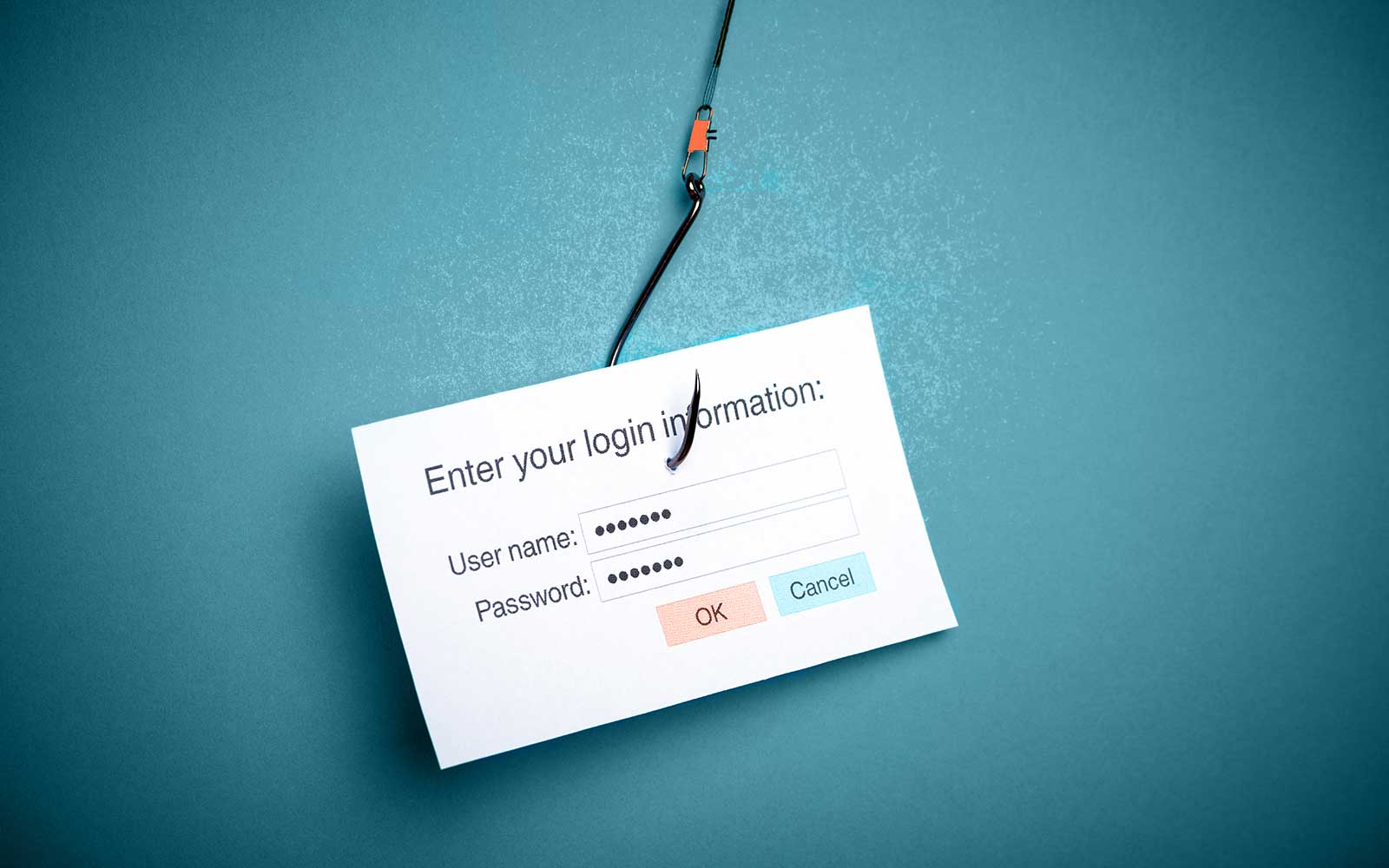
Phishing is a term that plays off the word fishing — it’s about trying to trick or manipulate someone into doing something they typically wouldn’t. It’s like setting your bait and waiting for a fish to bite — only in this case, the attacker is holding the phishing rod and you’re looking like dinner.
The goal of a phishing attack is to get an organization’s employees or private individuals to:
- Share personally identifying information,
- Provide sensitive account information,
- Send them other types of sensitive documents or data, and/or
- Make wire transfers or other fraudulent payments to the soliciting cybercriminals.
The attacker then can use this information to commit crimes, sell it to other cybercriminals, or publish it online to cause additional harm to the affected individual or organization.
How Phishing Ruins Your Day
No one likes being duped — least of all when it results in costly consequences. A successful phishing attack can result in any or all of the following depending on who or what is being targeted and how far the phisher decides to take things:
- Businesses and organizations — A phishing incident can result in non-compliance issues, fines and penalties, lost business and sales opportunities, reputational harm, damaged relationships with customers, etc.
- Consumers — A phishing incident can result in identity theft, financial losses, fraudulent charges, reputational harm (e.g., negative credit score changes or someone doing illegal activities in your name), etc.
How Cybercriminals Set Their Hooks
Phishing comes in multiple forms and techniques depending on how bad guys want to use it. They can target entire companies, individual employees, random people, or specific private individuals. Phishing can be generic in nature, targeting random people with emails, text messages, or phone calls. It also can be specific, targeting particular individuals based on their roles within organizations or their personal statuses.
Understanding the difference between generic and targeted phishing attacks is akin to knowing the difference between using a shotgun and rifles: the former is about spraying far and wide to hit any random target; the latter is about targeting one or more specific individuals.
Phishing also varies depending on the attacker’s platform or method of communication. For example, phishing attacks can be carried out in all of the following channels:
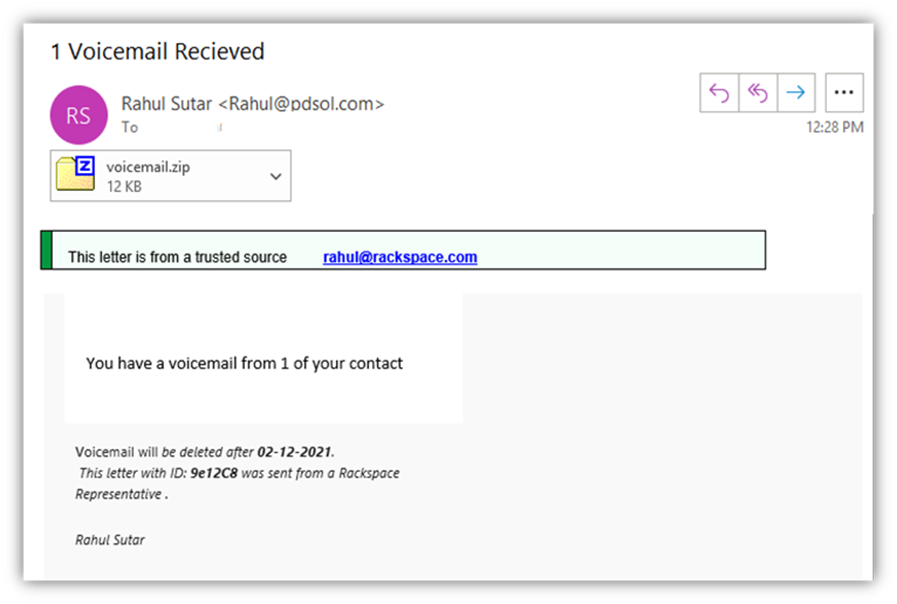
- Emails (phishing, spear phishing, BEC scams, EAC scams, etc.) — Typically, this involves an attacker sending an email to one or more individuals to get them to click on a link or open a malicious attachment
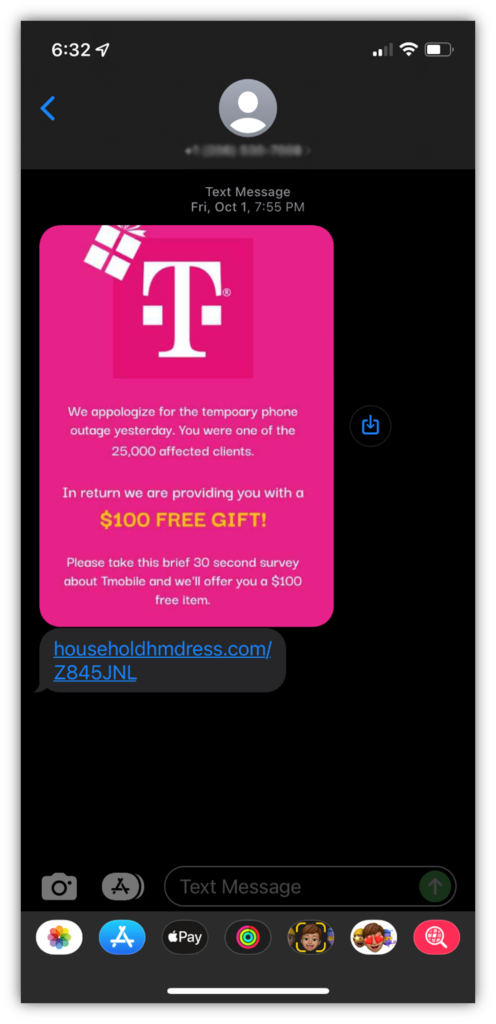
- Text messages (SMS phishing, or “smishing”) — Smishing attacks typically involve an attacker sending an enticing text message with a link to get the target to visit a phishing or malicious website.
- Phone calls (voice phishing, or “vishing”) — This approach involves either calling targets directly or sending an email or text message to trick the target into calling the attacker. Once on the phone, the attacker can then try to get the target to share sensitive information or provide payment information.
- Websites (phishing websites, watering hole attacks) — The goal here is to get an attacker to visit a phony website that’s designed to look authentic. For example, an attacker can create a fake Amazon.com website to trick users into sharing their login credentials or making fraudulent purchases.
- Fake networks (evil twin attacks) — This process typically entails an attacker creating a fake network (such as at a library or a café) to trick people into connecting to it, believing it to be the facility’s legitimate secure network. Once connected, the attacker can steal the victim’s sensitive data (such as login credentials or payment information) in transit.
A Quick Look at What Phishing Attacks Look Like
As mentioned a few moments ago, phishing comes in multiple forms and communication channels. So, here’s a quick look at a few examples of phishing.
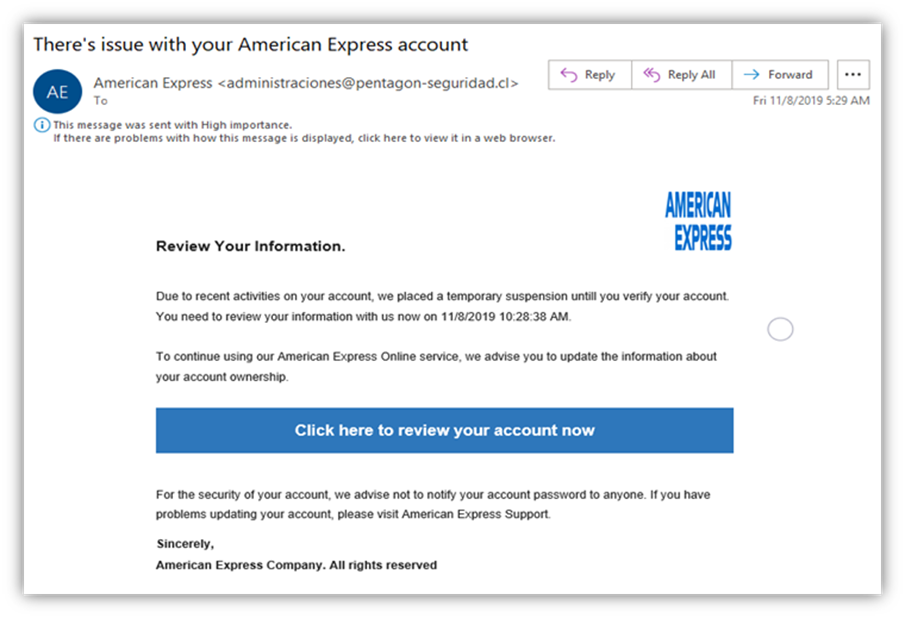
For more examples, check out our article on 10 Phishing Email Examples You Need to See.
Final Thoughts on Phishing Attacks
Phishing attacks are one of the go-to weapons in virtually every cybercriminal’s arsenal. These attacks aren’t going to stop. This is why it’s imperative that businesses and consumers alike know how to recognize these scams and how to protect themselves against them.
To learn more about how to protect yourself and your organization, check out our article on How to Prevent Phishing Emails & Attacks From Being Successful.