Verizon’s data shows that 22% of reported data breaches in 2020 involved phishing. But do you know what to look out for to avoid falling for phishing scams? Here are some examples of common phishing emails.
Avast reports that six-in-10 Americans (61%) are at risk of falling victim to phishing scams. Of the 24% of users who admitted to being phishing victims, 59% say they fell for phishing emails in particular. But what makes some phishing emails so successful? This article will show you some of the common phishing email examples so that you can defend yourself when you are being targeted.
For example, in a spear-phishing attack, attackers make phishing emails more believable and seemingly authentic by researching you and your organization ahead of time. The threat of spear-phishing is ever-present for enterprises. In this scenario, the only way in which your enterprise can defend itself is to raise the awareness of phishing emails among your employees.
Benjamin Franklin once said, “an ounce of prevention is worth a pound of cure.” And cyber awareness training is the perfect way to increase awareness of common phishing tactics. A great way to approach this educational lesson is to use real phishing email examples for your employees to learn from. The time and money you spend on training your employees will pay for itself in the long run.
So, what are some common phishing email examples? Let’s take a look.
10 Phishing Email Examples to Learn From
We’ve put together a list of 10 real examples of phishing emails that we’ve received over the past few years. Some of them are very convincing while others are not so much. However, all it takes is one moment of unawareness for cybercriminals to snare your employees in their email phishing traps.
A Phishing Email Example Where the Sender’s Email Address Is Fishy
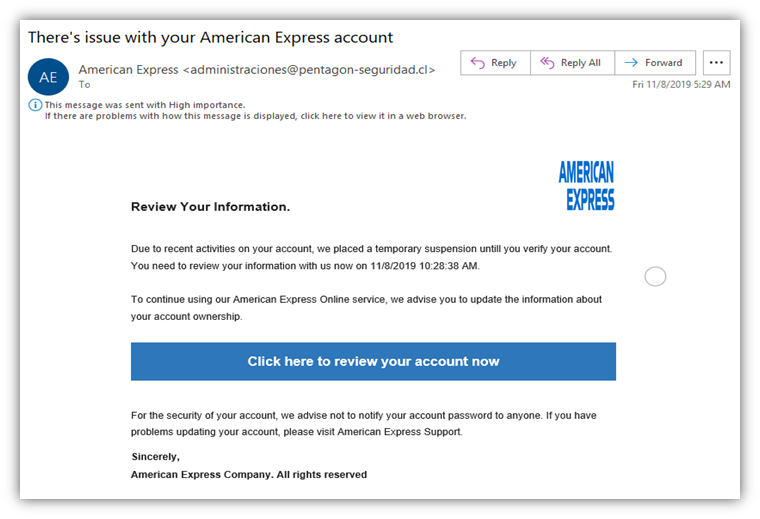
If you glance at the above email quickly, you’ll likely find nothing wrong with it. This might drive most people to take and action and click on the given link because they think it’s a safe and legitimate email. However, if you look closely, you’ll notice that there several things wrong with this email:
- The name and email address don’t match. The first discrepancy you’ll see relates to the name of the sender and the email address. Their display name and the body of the email claim that the email is from American Express. However, the email address is something different that’s unrelated to the credit card company: [email protected]. Considering that the domain name of American Express is americanexpress.com, this means that a legitimate email would come from an address at that domain and not “pentagon-seguridad.cl.”

- “American Express Company” isn’t the name of the legitimate organization. Secondly, the email claims to have come from “American Express Company” in the last line. If you pay attention to the details, the name of the company is “American Express.” They do not add “company” at the end of their name. This is a big red flag.
- Design of the logo is different. Although hackers have used the company’s blue brand color when writing the email, their fake logo’s design gives away their malicious intentions.
- There is a sense of urgency in the tone of the subject line in the email. This is a clear indication that the email is for phishing. The attacker does not want you to ponder much over the email — they want you to react without considering the repercussions. If they give you time to think, the chances are you will figure out their scam and they will fail in their attempt.
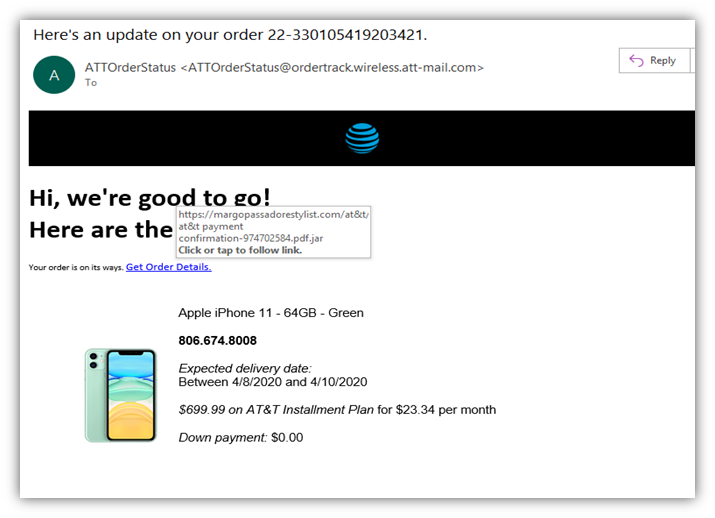
- The “Get Order Details” link takes you to a different site. If you were to press the “click here to view your account now” button, you’ll notice that the link won’t take you to the legitimate American Express website. In another email example below that appears to come from AT&T, you’ll see another example of that:
A Phishing Email Example Where the Scammer Promises Financial Rewards
Sometimes the scammer will promise you an unexpected gain through a phishing email. This common tactic aims to get you to click on a link or reveal your bank or other personal information.
There are many indications that such an email has malicious intent (which we’ll speak to momentarily). Check out the screenshot below that shows an email that will tempt you to reveal your bank details:
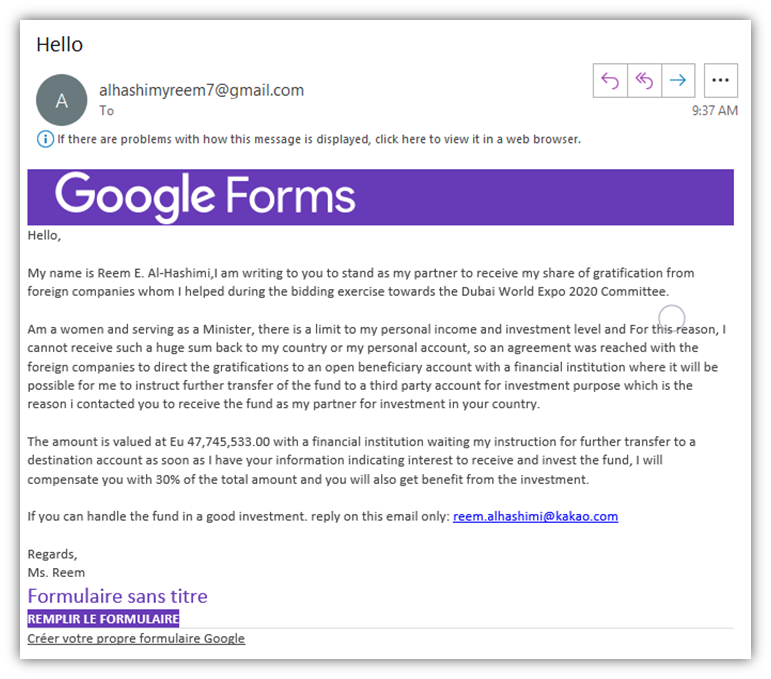
The email above is totally unbelievable. However, some people might fall into the scammer’s trap and lose their savings if they aren’t paying attention or are unaware of common phishing tactics. You can know the email is fake due to the following reasons:
- The language used in the email is not fluent. There are tons of grammatical errors. The meaning of the email is also not clear. Red flag.
- The email leads you to expect a lucrative deal. The email indicates the gain of thousands of Euros if you are willing to give your personal information. If you think logically, why would somebody offer you a deal that is too good to be true? Nobody will contact you to give you thousands of Euros and expect nothing in return. Red flag.
- The email asks you to reply via a different email address. The sender’s email address and the email address they offer for replying to the email are different. This is a huge red flag.
All these signs point in one direction only: the email is sent to you for the purpose of phishing. Be sure to check out one of our other blog posts for more information on how to tell if an email is fake or real.
Phishing Email Example Where You Are Asked to Verify Your Account Details
There may be many services you’ll be subscribed to. You might be approached by an email asking you to verify the details of your account. Look at the first screenshot in our list of phishing email examples:
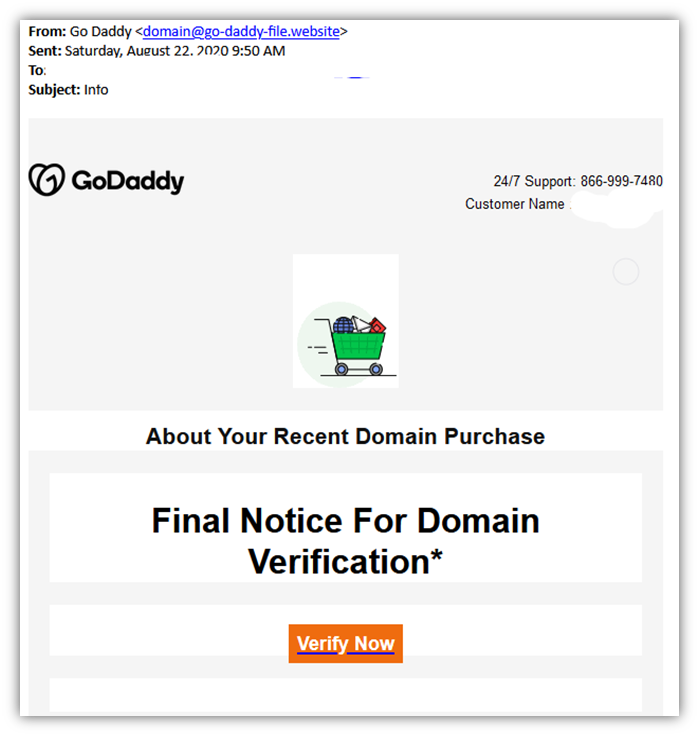
The phishing email example above shows the sender’s email address has the domain name “go-daddy-file.website.” This alone should be enough to raise suspicion because it’s not from a godaddy.com email account. Another indicator can also be the website address of the link you’re asked to follow — it will not match the name of the sender.
You can see a similar phishing email “supposedly” from Netflix. When you look at the link, you’ll notice a similar scenario.
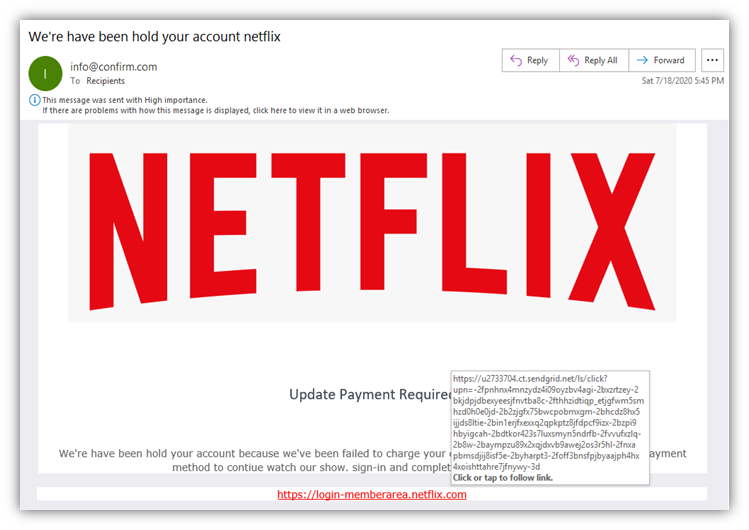
Did you notice the subject line of the above email? “We’re have been hold your account Netflix.” What the heck does that mean? This is not even a real sentence! If the email was from Netflix, do you think they wouldn’t use correct grammar or spelling? Beware!
The signs of scams are right there for you to see in both of these phishing email examples.
A Phishing Email Example That Includes Fake Financial Documents
What will you do if you have an email sitting in your inbox screaming “REMINDER: Export Documents” or “REMINDER: Invoice” and the email directs you to download the attachment? Maybe you will click on the attachment to realize all hell has broken loose and now your organization has to go into emergency response mode.
Check out the phishing email example below and you’ll quickly realize the mistakes:
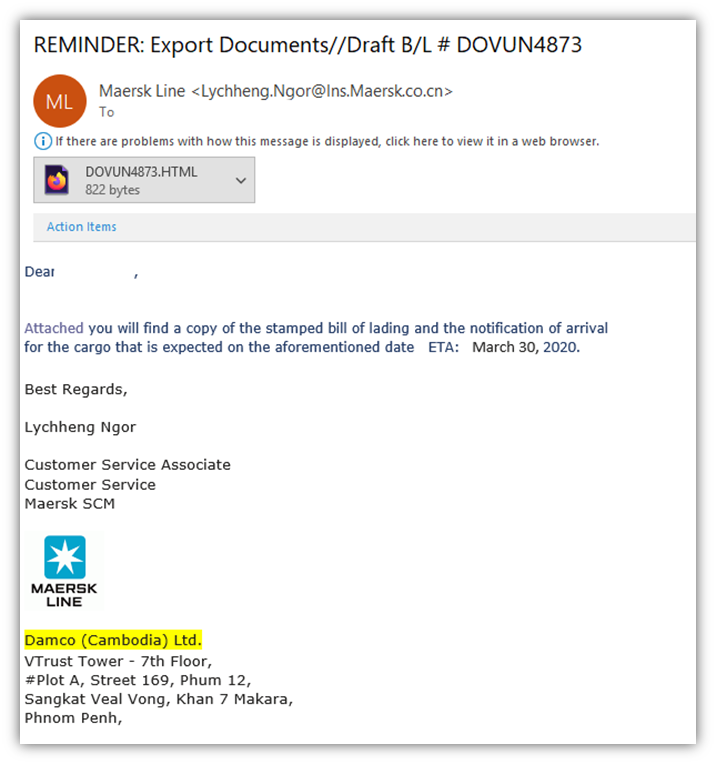
How many mistakes did you notice? Let me list them out and you can check how many did you get right:
- The email address of the sender: the domain registration is done in China (.cn) but the physical mailing address is in Cambodia.
- The headquarters of the said company is in Denmark with the domain name maersk.com.
- The link given is an extremely dodgy HTML file.
- Ask yourself: What company is “Damco (Cambodia) Ltd.” And why is it send an email in the name of Maersk Line?
- Why is a customer service associate sending an email related to export documents?
- Why are they using different colors in terms of text and highlights?
- If the mail was actually from Maersk Line, would it contain so many grammatical and punctuation errors?
- A bill of lading typically doesn’t come in an HTML format. Then, why is it so here?
Did you manage to get all that right and notice their mistakes? Kudos!
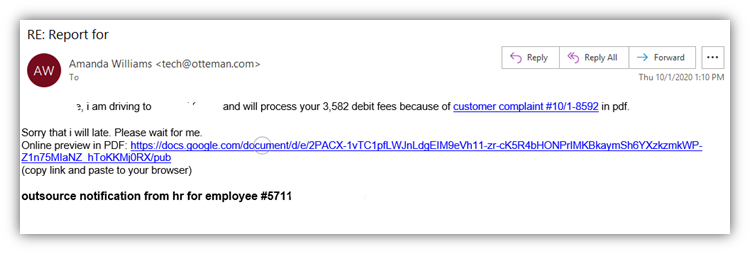
A Phishing Email That Claims to From Someone Within Your Organization
Have you ever received an email claiming to be from your colleague or a debtor or your service provider? This is a very common tactic used in phishing scams. The following email is an obvious scam. The “online preview in PDF” can be viewed on the scammer’s Google docs. The incorrect grammar usage, the request to open the document, the tone of the email, and just about everything you see in the email are fishy (or, I should say, “phishy”).
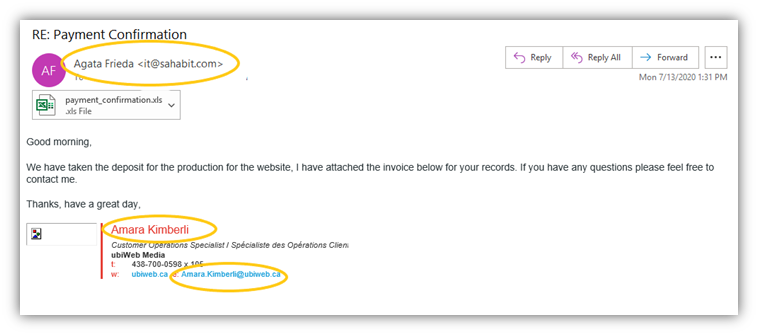
An Example of Phishing Email That Asks For a Payment Confirmation
This next example is a real doozy. The sender seems really confused about their identity! Have a look at the screenshot of this phishing email and how many names and email addresses the attacker used!
An F-Secure report about the most dangerous email attachment types says that there are 85% chances that the malicious emails will have .DOC, .XLS, .PDF, .ZIP, or .7Z attachment. These are the files that users often open without any hesitation because they’re so commonly used in businesses — hackers know this and use it to their advantage.
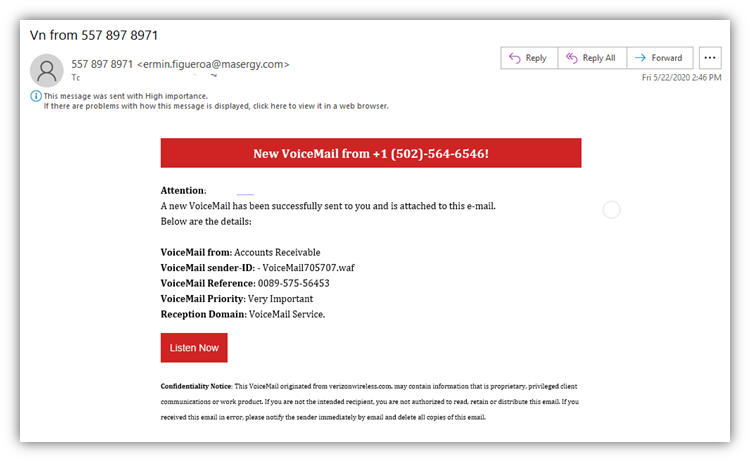
Phishing Email Examples of Voicemail Scams — Why Not?
Scammers are continually upgrading their techniques to coax users into divulging personal information or allowing them to take a peep into their systems. (They like to put new lipstick on the pig every once in a while, so to speak.) This allows them to put new twists on old scam techniques.
Sending fake voice messages is one way they do it. Have a peek at the phishing email example below and see if it is tempting enough to trick you into clicking on a suspicious link:
Or will you trust a voicemail from a person calling himself a “trusted source” and giving you a time limit within which you can listen to the voicemail?
Screenshot of phishing email calling himself a “trusted source.”
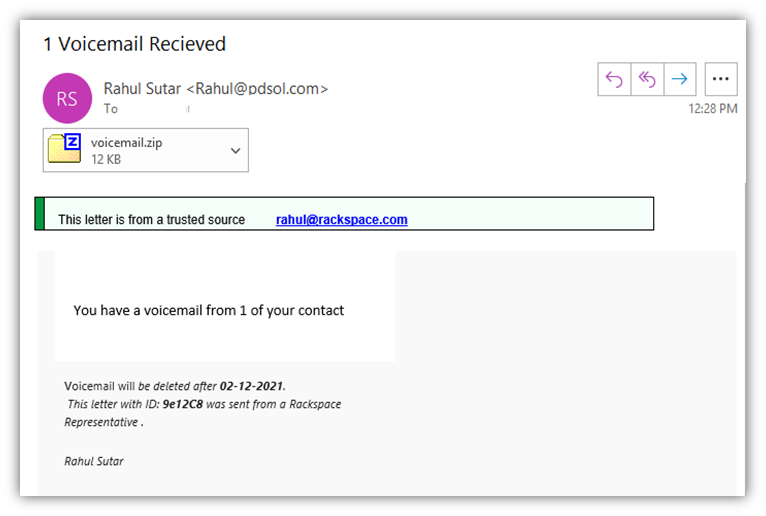
Hopefully, the answer to the above question is “no.”
To Sum Up This Article on Phishing Email Examples
Phishing emails will continue to invade our inboxes as long as the attackers find them lucrative. The best way to defend yourself and your assets is to train your employees, children, or anybody who has access to your email accounts.
Train yourself to stay observant and alert — always be on the defensive when checking emails for potential threats. This list of phishing email examples is in no way exhaustive, but it will help you to learn how to recognize messages with malicious intent. This is the first step to helping your company avoid becoming a victim of phishing email attacks.