The never-ending debate of FBI vs Apple is getting tiresome. Here’s why the FBI just cannot crack an iPhone on its own.
We might be about to witness another high-profile clash between two mighty forces – the FBI and Apple. Addressing a news conference on Tuesday, Chris Combs, FBI special agent in charge admitted that the FBI is not able to access the Texas church gunman’s phone.
“I’m not going to describe what phone it is because I don’t want to tell every bad guy out there what phone to buy, to harass our efforts on trying to find justice here,” said Combs.
However, the latest report by the Washington Post confirmed that the phone IS an iPhone.
Welcome to FBI vs Apple 2.0!
We could talk all day about whether the FBI should be granted access to Apple’s products or not. At least a million blogs/articles must have been written about it, and another one will just be a drop in the motionless ocean. That’s why we don’t like to indulge ourselves in such debates and focus on what’s more important – the technology.
Focusing on the technical part, let’s get under the hood of the encryption technology that makes it almost impossible for the FBI to hack into Apple products.
The Six-Digit Password
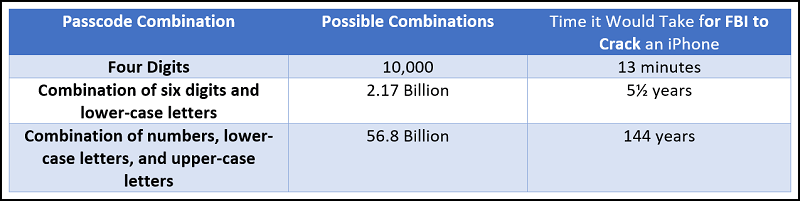
The most obvious way one could think of hacking into an iPhone is by guessing the passcode. In technical terms, this is called a ‘brute-force attack.’ However, it isn’t as easy as it sounds. Apple has taken leaps regarding security in the past few years. In the iPhones preceding 5S, the default passcode one could set was four digits. It means that there were only ten thousand possibilities and the FBI could crack it in just 13 minutes. All this changed with the launch of iOS 9.
With the launch of iOS 9, Apple’s products ask for a six-digit passcode by default. Therefore, it could have a million possibilities. If a passcode comprising of numbers and lower-case letters is set, it could be arranged in 2.17 billion ways. According to Apple’s White Paper, it would take more than 5½ years to try all combinations. If you combine the magic of capital letters with lower-case letters, the number of possible combinations would be 56.8 billion. How long will it take to crack it? 144 years!!!
It’s amazing how numbers work, isn’t it?
The Secure Enclave: Apple’s (almost) Unconquerable Encryption Technology
It’s no secret that iOS devices are much more secure compared to their counterparts. A big part of it goes to the Secure Enclave, Apple’s revolutionary encryption technology.
Launched in 2013 along with the Touch ID technology, the Secure Enclave is a hardware chip or coprocessor responsible for the encryption operations. As it’s a separate entity from the processor, a hacker cannot get into it even if he/she somehow manages to hack the iOS kernel. It has also got its own operating system (OS) and can be updated independently of the main OS.
The manner in which the Secure Enclave works is fascinating, at least on paper! This is how it works:
- As outlined above, the Secure Enclave has its own microkernel. This enables it to have a separate boot process from the main processor. When the device boots, the Secure Kernel produces a temporary key, an ‘ephemeral key’ in technical terms. This combination of ephemeral key and UID encrypts and authenticates the memory stored within the Secure Enclave. Keep in mind that the UID cannot be retrieved by the main CPU or Apple or anyone else.
- Once the booting is done, any data saved to the file system is encrypted using the combination of the entangled ephemeral key and an anti-replay counter. This anti-reply counter protects the data with IP packet-level security. In layman’s terms, this anti-reply counter makes it impossible (almost) for the hackers to intercept the information being transferred.
- So, when a user unlocks the device using his/her fingerprint, the Secure Enclave processes and encrypts the fingerprint data using its own processing power. The main processor facilitates the communication between the biometric sensors to the Secure Enclave. However, it cannot read the data as it doesn’t have the UID.
- The Secure Enclave verifies the information sent (fingerprint) to the data stored within itself. If the data (fingerprint) matches, the main CPU unlocks the phone or make a purchase using the Touch ID.
The entire process is based on keeping the ephemeral key and the UID discreet. As no one including the Phone’s CPU or Apple can read/intercept them, it’s extremely difficult for any 3rd party entity to crack any of the latest Apple products.
Apple’s latest addition, iPhone X, which encompasses Face ID also works the same way. Instead of the numerical data of a fingerprint, it encrypts the mathematical data of the face. Everything else works the same way.
So, next time you see your friends arguing about the FBI vs Apple debate, bring out the techie in you and blow them away.