In the U.S., the costs of fraud for ecommerce and retail companies have shot up, reaching $3.75 for each $1 of fraud including credit card data. It’s one example of why businesses need to abide by Payment Card Industry Data Security Standards — and here’s an overview of the PCI DSS requirements you need to meet to do so…
With 90% of organizations interviewed by O’Reilly in 2021 using cloud computing and the fast-evolving security threats in the digital world, the now four years old Payment Card Industry Data Security Standards (PCI DSS) v3.2.1 needed a revamp. The new version (PCI DSS v4.0), which was published in March 2022, includes massive changes for all organizations handling card payment data in some way. (What we mean by that is that they store, process, or transmit the data.)
No panic! You have until March 31, 2024, to implement the required changes. But as the early bird catches the worm, we’ll give you a jump start. To make your life easier we’ve put together a high-level, 6-minute overview of the most important new PCI DSS requirements.
It’ll enable you to:
- Understand what the changes mean to your organization.
- Give you a rough idea of the time you need to complete the transition from v3.2.1 to v4.0.
C’mon, grab a coffee and start to familiarize yourself with the new policies now.
Cybercriminals and their attacks are evolving, but they aren’t the only ones. The Payment Card Industry Data Security Standards (PCI DSS) are, too! Find out what’s new in the latest PCI DSS requirements for version 4.0. Discover the latest key changes in PCI DSS v4.0 that’ll help you better secure your customers’ sensitive financial data and thwart cybercriminals’ efforts.
What Are the Key New PCI DSS Requirements For v.4.0?
The Payment Card Industry Security Standards Council (PCI SSC) introduced 64 changes and clarifications in the new DSS v4.0 document. These changes are intended to:
- Address the ever-evolving risks and threats to payment information,
- Promote security as a continuous process, and
- Make it easier for organizations to comply by allowing them to choose among different security technologies that better adapt to their business processes.
We’ve picked the most significant ones you’ll need to know to ensure a smooth transition. But before we dive in, why don’t you familiarize yourself with the “history” of the PCI DSS with this entertaining short video?
| PCI DSS Requirements V.3.2.1 | PCI DSS Requirements V.4.0 | Example of What’s Changed |
| 1. Install and maintain a firewall configuration to protect cardholder data. | 1. Install and maintain network security controls. | The term “firewall” has been replaced by the broader “network security controls” (NSCs), to include any technology used to control network traffic. |
| 2. Do not use vendor-supplied defaults for system passwords and other security parameters. | 2. Apply secure configurations to all system components. | The focus has switched from securing vendor default accounts and passwords to implementing secure configurations everywhere. |
| 3. Protect stored cardholder data. | 3. Protect stored account data. | Data protection and encryption must be extended to all account data. |
| 4. Encrypt transmission of cardholder data across open, public networks. | 4. Protect cardholder data with strong cryptography during transmission over open, public networks. | Strong cryptography and data encryption become the protagonists of this requirement. |
| 5. Protect all systems against malware and regularly update anti-virus software or programs. | 5. Protect all systems and networks from malicious software. | Malware protection is now extended to the organization’s networks covering anything that might involve the cardholder data environment (CDE). |
| 6. Develop and maintain secure systems and applications. | 6. Develop and maintain secure systems and software | To reach compliance organizations will have to secure not only applications used to process or transmit payment data but all software included within the CDE. |
| 7. Restrict access to cardholder data by business need to know. | 7. Restrict access to system components and cardholder data by business need to know. | The key phrase here is access control. And it must cover every single system component. |
| 8. Identify and authenticate access to system components. | 8. Identify users and authenticate access to system components. | PCI DSS is introducing the idea that nobody is trusted (zero trust). |
| 9. Restrict physical access to cardholder data. | 9. Restrict physical access to cardholder data. | As in the previous PCI DSS version, physical access protection is important. |
| 10. Track and monitor all access to network resources and cardholder data. | 10. Log and monitor all access to system components and cardholder data. | Log, monitor, and analyze accesses, but with the support of automation. |
| 11. Regularly test security systems and processes. | 11. Test the security of systems and networks regularly. | Define and document who does what regarding testing systems and networks. |
| 12. Maintain a policy that addresses information security for all personnel. | 12. Support information security with organizational policies and programs. | Everyone becomes responsible for the security of the organization’s payment data ecosystem. |
1. Install and Maintain Network Security Controls
As organizations increasingly rely on containers and cloud services, firewalls aren’t the only tools used to control and restrict network traffic. Therefore, the term “firewall” has been replaced by the broader “network security controls” (NSCs), which include:
- Access control solutions (NAC),
- Anti-virus, anti-malware, and spyware,
- Authentication and authorization policies,
- Virtualization/containers.
2. Apply Secure Configurations to All System Components
Until now, were you only removing default usernames and passwords? That isn’t enough anymore. The focus has now switched from securing vendor default accounts and passwords to implementing secure configurations everywhere. With the new PCI DSS requirements, for example, you’ll need to take things a few steps further:
- Delete unused software, features, and accounts.
- Remove or disable unnecessary services.
- Document secure configurations and have a configuration management process in place.
3. Protect Stored Account Data
One of the most notable changes applies to the data itself. Data protection and encryption must be now extended to include all account data, not only cardholder data. This will include things like:
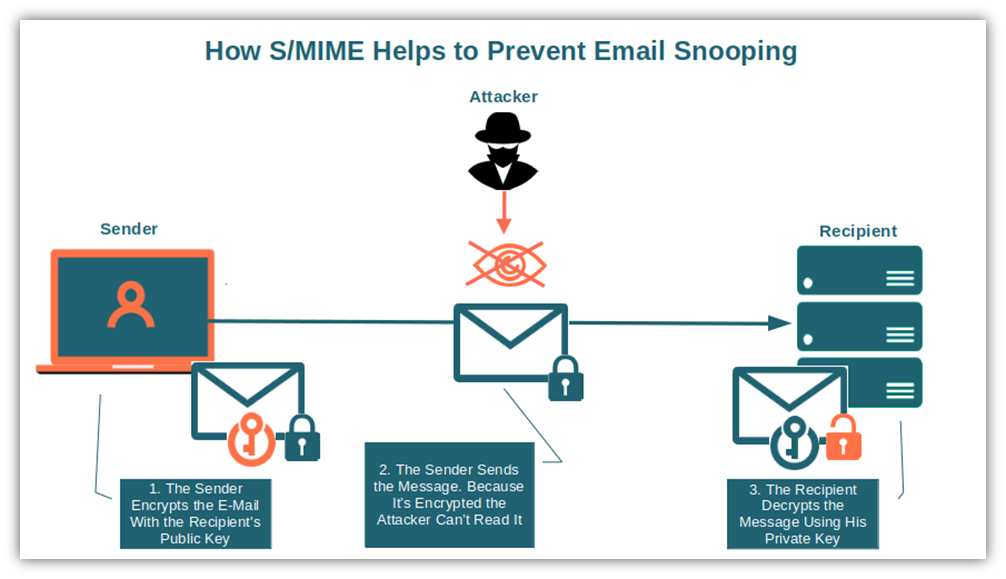
- Email encryption using S/MIME certificates (i.e., email signing certificates).
- Encryption and immediate removal of sensitive authentication data (SAD) – e.g., the card security code and PIN — after the transaction has been completed.
- All primary account numbers (PAN) will have to be entirely encrypted by a keyed cryptographic hashed algorithm (i.e., based on a secret key) to ensure data authenticity and integrity.
4. Protect Cardholder Data With Strong Cryptography During Transmission Over Open, Public Networks
With the cost of data breaches skyrocketing, strong cryptography and data encryption have become the protagonists of this requirement. Join that 55% of technology and software companies that were already using encryption in 2021. But why is encryption necessary for securing data over the internet? Because it’s an insecure public network that otherwise leaves your information vulnerable to interception and theft. That’s why the adoption of encryption has been steadily increasing with 55% of technology and software companies already using it in 2020.
- Authenticate your server using an SSL/TLS certificate to encrypt and secure your data transmissions. Now you can say goodbye to man-in-the-middle attacks. Want to know how it works? Check out the video below:
- Ensure that the digital certificates you use to transmit cardholder data over the network aren’t expired or revoked. If they are, then you might as well hand your customers’ account data to bad guys on a silver platter for all the good that using an expired or revoked certificate will do for you…
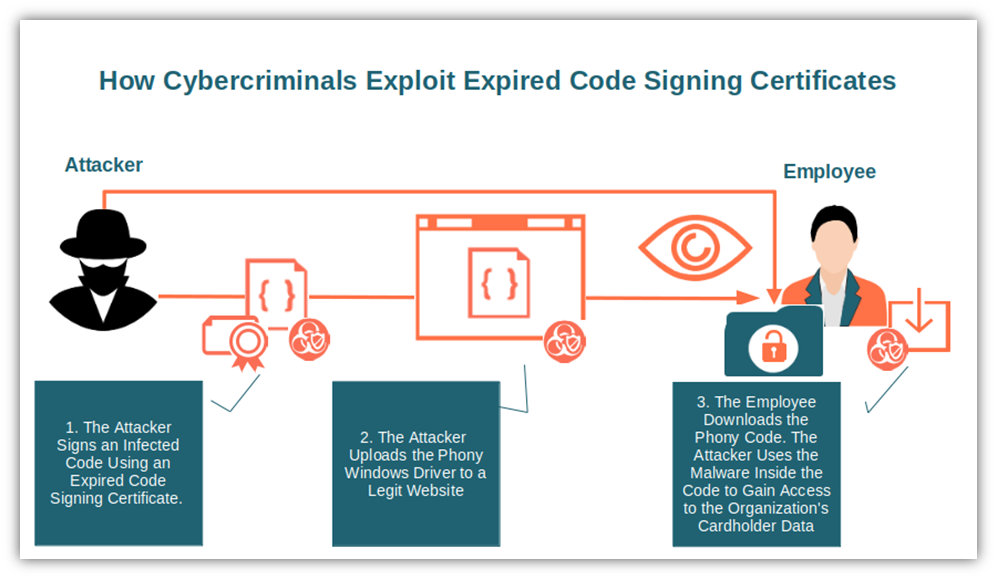
- Implement a certificate and key management process. It’ll help you avoid being part of 80% of organizations that faced multiple outages due to expired certificates in 2021.
5. Protect All Systems and Networks From Malicious Software
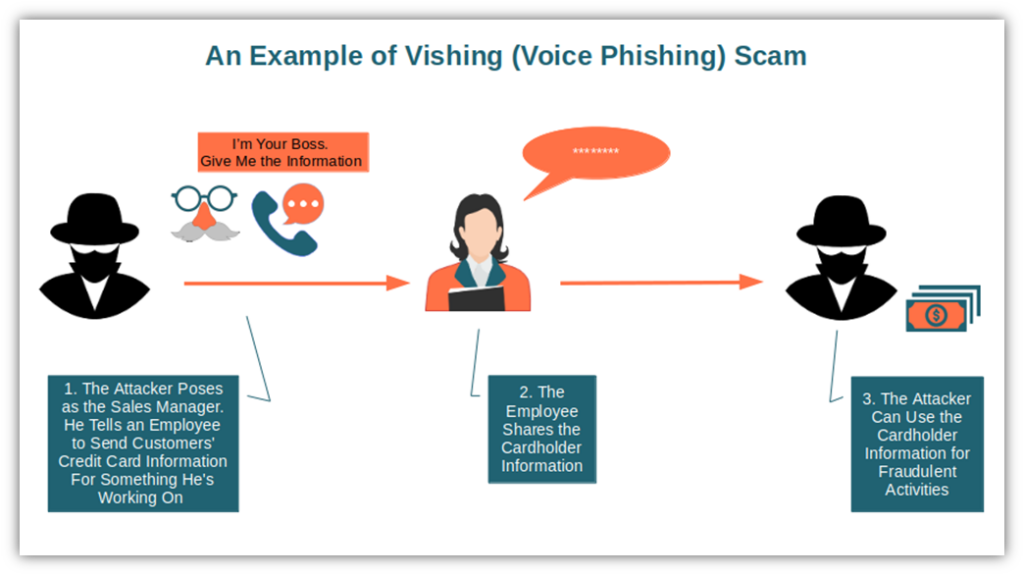
The number of detected phishing attacks jumped to 225 million in the last six months of 2022. That’s a marked increase of 61% increase compared to 2021. This may be part of the reason why PCI DSS v4.0 extended malware protection to the organization’s networks, covering anything that might involve the cardholder data environment (CDE). But what does this mean for you?
- Always redirect your website traffic to use the more secure port 443 (i.e., enable the secure HTTPS protocol).
- Train your users to detect and recognize phishing and vishing attacks.
- Regularly perform malware scans with anti-malware and network security software.
6. Develop and Maintain Secure Systems and Software
To reach compliance, organizations will have to secure not only applications used to process or transmit payment data but also all software included within the CDE. Does it mean that an organization’s website and its entire authentication system will also have to be secure? Yup! That’s exactly the idea.
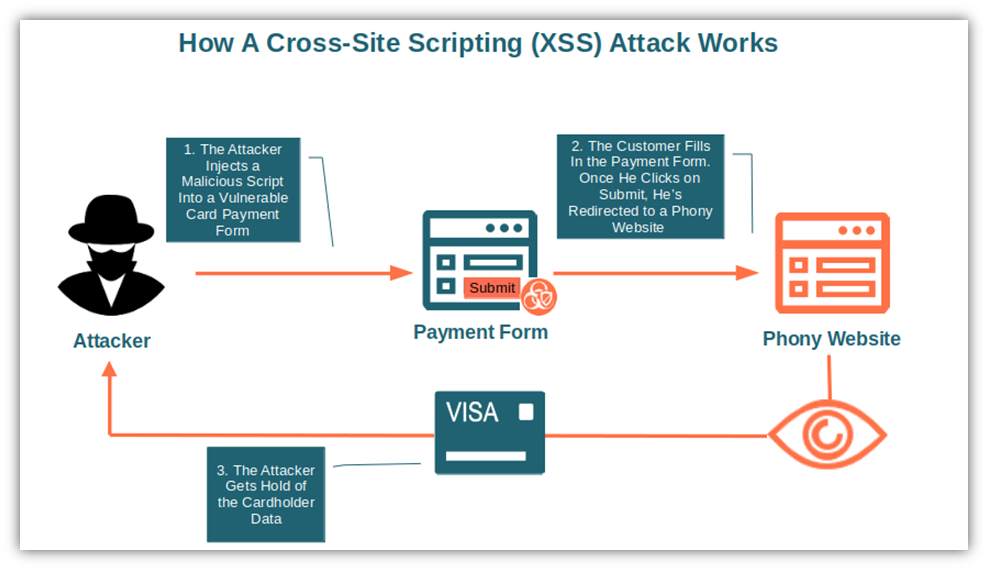
- Implement a web application firewall (WAF) to protect all customer-facing applications from attacks like cross-site scripting (XSS), SQL injection and DDoS attacks.
- Critical and high-security patches must be installed no later than one month after their releases.
- List all your custom-developed and third-party software. Make a list of all their “ingredients” (i.e., all components, libraries and modules used to build each piece of software) using a software bill of materials (SBOM).
7. Restrict Access to System Components and Cardholder Data by Business Need to Know
The key phrase here is access control. And it must cover every system component. What are some of the new requirements?
- Systematically review user accounts and access permissions.
- Roles and responsibilities must be documented and understood by every user (e.g., who can access what). Did I mention that this new point has been added to all 12 requirements?
8. Identify Users and Authenticate Access to System Components
By looking at the newly added requirements, it seems that PCI DSS is introducing the idea that nobody is trusted (zero trust). Are you still allowing eight or seven-character-length passwords? Beware! Their time is gone. There’s also a deeper focus on the National Institute of Standards and Technology NIST password guidance and multi-factor authentication (MFA). Below are a few examples:
- Don’t allow passwords with less than seven alphanumeric characters. Important: this will remain a best practice only till March 2025. After that, it’ll be a minimum of 12 characters.
- Lock accounts with more than 10 failed login attempts.
- Implement MFA for all users and admins, including remote access.
9. Restrict Physical Access to Cardholder Data
Why should you go through all this hassle to digitally protect your cardholder data when everybody in the company has free access to your data center? As in the previous PCI DSS version, physical access protection is important.
- Media containing cardholder data must be securely locked up when not in use.
- Systematically perform a targeted risk analysis to ensure that no point of interaction (POI) device (the payment device [e.g., POS]) has been tampered with.
- Define the frequency of inspection based on the risk analysis results.
10. Log and Monitor All Access to System Components and Cardholder Data
Log, monitor, and analyze accesses, but with the support of automation. On top of that for example you’ll have to:
- Perform automated audit logs review. Can’t afford to spend too much money on it? Some open-source alternatives can help you.
- Run a risk analysis to define how often logs will have to be reviewed.
- Implement a control and alert system for critical components by end of March 2025. Log parsing tools like Kibana or Grafana offer these kinds of features and more.
11. Test the Security of Systems and Networks Regularly
Define and document who does what regarding testing systems and networks. Good news: all other new requirements under this point will be considered best practices only until the end of March 2025.
- Internal vulnerability scans will have to be performed as a logged-in user (i.e., authenticated scanning). This means that black box (unauthenticated) pentestings won’t be enough anymore.
- Implement detection and alert mechanisms to identify unauthorized modifications of HTTPS headers or customer payment forms. Do you remember Magecart attack? As this kind of malware is still alive and kicking, adding some extra protection won’t hurt.
12. Support Information Security With Organizational Policies and Programs
With the advent of PCI DSS v.4.0, everybody in the organization is invited to the information security party. Yup! Everyone becomes responsible for the security of the organization’s payment data ecosystem. And there’s more:
- Assess all hardware and software used within the organization at least once a year.
- To keep up with changes encryption algorithms used must be reviewed every 12 months. Are you still using the deprecated SHA-1 algorithm? Replace it with the more secure SHA-256.
- All employees should attend a reviewed awareness security training at least once a year.
That’s it! This is our quick overview of the key changes brought by version 4.0 to the PCI DSS requirements. As you can see there’s something for every single employee of companies handling cardholder data. Want to know more? Don’t miss the PCI DSS comparative document showing the changes between v3.2.1 and v.4.0 in more detail.
Final Thoughts About A 6-Minute Overview of the PCI DSS Requirements
It’s important to note that these are just a few of the changes from the previous PCI DSS requirements. There are others, but we won’t go into all of them individually in this article. We know it can look overwhelming at first, but implementing PCI DSS v4.0 will enable you to:
- Successfully address new threats to payment card data,
- Manage security as a continuous process, and
- Give you that much-needed flexibility (e.g., the possibility to choose between different approaches and how often to perform certain activities) to achieve data security and compliance.
Now that you know what’s changing, filling the gaps is going to be much easier. Start the new year with a bang and put your organization ahead of the pack with a transition plan. Get ready for the switch!

![A 6-Minute Overview of the PCI DSS Requirements [For PCI DSS v.4.0]](https://cheapsslsecurity.com/blog/wp-content/uploads/2022/12/pci-dss-requirements-v4.jpg)