“Warning: Potential security risk ahead.” Learn everything about the costly consequences of a simple oversight that could take your company into a breach of disaster. Discover how to keep your data safe and never miss a PKI certificate expiration date again
81%. This is the percentage of organizations that experienced multiple outages due to ‘security certificate expired’ issues from 2020 to 2022, according to recent research from the Ponemon Institute.
Every day, millions of security certificates expire. The majority are renewed on time, so, typically, no one notices it. However, from time to time, one certificate slips through the cracks and that’s when the problems start. One recent example was the 11-hour outage of Megaphone in June 2022 that was caused by Spotify forgetting to renew its SSL/TLS certificate. Other examples of similar incidents involving expired certificates include LinkedIn, Microsoft Exchange Admin portal, and Teams.
Do you want to be one of those businesses that manage their security certificates like pros? Discover what an expired certificate can mean for you, your users, and your customers. Get ahead of the problem — know the risks and learn how to prevent them in the first place.
What Does ‘Security Certificate Expired’ Mean?
Security certificates are a bit like butterflies: they’re great, but they have relatively short lifespans. This is because every digital certificate is assigned an expiration date. Depending on the certificate, the validity period can vary:
- Anywhere from three months to just over a year in the case of the secure socket layer/transport layer security (SSL/TLS) website security certificates, depending on the CA you use.
- Up to three years for code signing certificates.
- Up to three years for legacy email signing certificates and just over two years for those issued on or after Apr. 1, 2022, according to the CA/B Forum’s S/MIME Pre-Ballot Discussion in May 2022.
Once their validity period gets to an end and you forget to renew them, that’s when you and your customers will see the ‘security certificate expired’ message. Because, unlike your Netflix subscription, security certificates don’t auto-renew themselves.
But why are certificates issued with expiration dates? Why can’t we have certificates with a longer life span or that last forever? That would be great, right? Not really. Sure, not having to worry about expiring certificates would be convenient, but your security will pay the price. Why?
- Each certificate’s validity period is based on the recommendations made by the CA/Browser Forum (the industry’s governing body) to protect users’ and customers’ information.
- Secondly, while strong encryption (certificates are based on that) can last for a long time without being breached, other key parts of the certificate might not have such a long life.
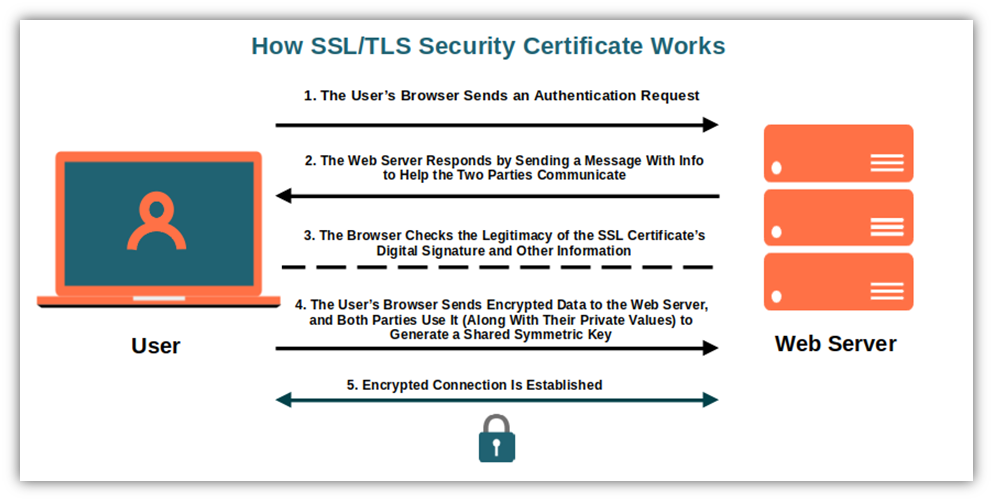
Let’s consider the SSL/TLS certificate as an example. This type of digital certificate enables every customer or user going to your website to verify the identity of the organization behind it, thus confirming that the website is legit and safe. How? By viewing some specific details included in the certificate like the information about the certificate authority (CA) who issued it, and about your organization that it was issued to.
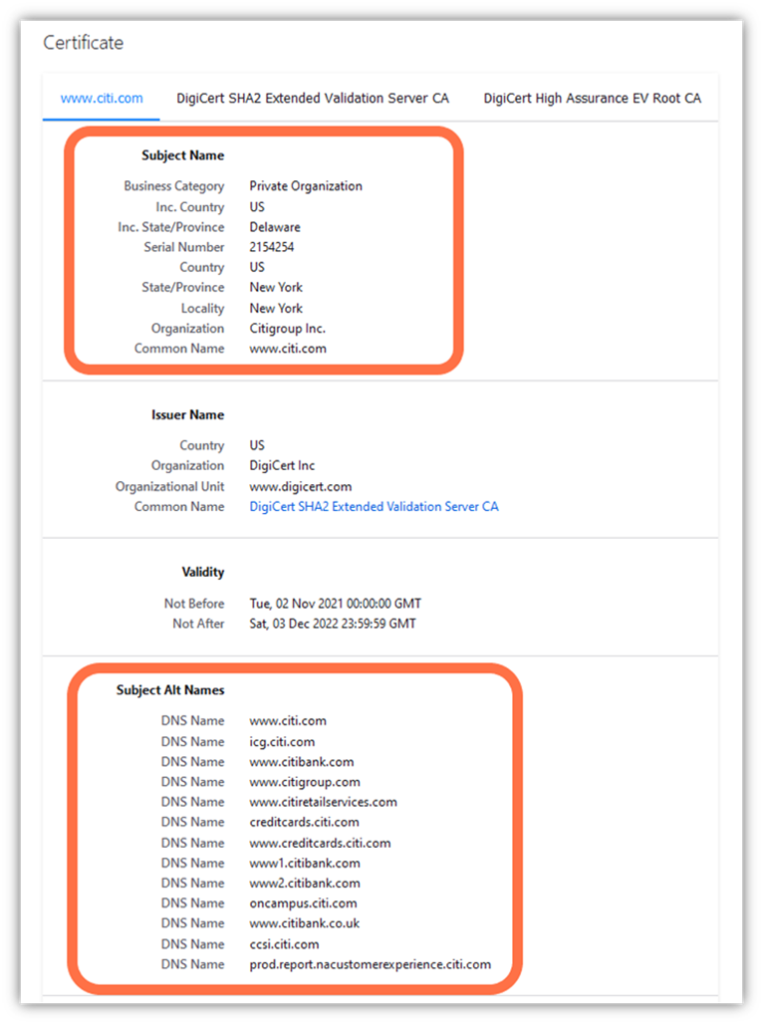
But what if, after a few years, something important changed due to an acquisition (the name, owner, business type, etc.)? What if your business is so successful that from a sole proprietorship it’s changed into a corporation? If the certificate wouldn’t expire, it’d validate outdated information, giving attackers an easy way to exploit the certificate containing the incorrect information. This is just one example of why carefully tracking and managing certificate expirations, despite being annoying and difficult to manage, is important.
It’s a bit like your passport. To make sure that the information on it is still accurate, you have to renew it from time to time. Can you imagine checking in for a flight when you’re 40 years old using a passport with a picture taken when you were sixteen? No matter how young you actually look (which I’m sure you do), I bet the official at Transport Security Administration (TSA) will have a bit of a hard time recognizing you there.
Of course, managing your keys and certificates is also important because you have to ensure that the keys remain secure. If they fall into the wrong hands, it’s game over for your certificate and open season on your organization for cybercriminals.
What Happens When a Security Certificate Expires?
If you renew it before its expiration date, nothing. Your website is still secure, and your customers and users have access to it without issues. Business as usual, basically. But if you forget to renew your certificate and allow it to expire, that’s another matter entirely. You can end up with a few users being unable to access a website or a service or, in the worst-case scenario, it can cause a service disruption impacting millions of users.
You don’t believe it? Twitter has several examples with the hashtag #ExpiredCertificate. Here’s one such example:

So, what are the consequences when an SLL/TLS certificate, a code signing certificate, or an email certificate expires? It depends. Let’s check them out one by one.
| Certificate Type | Consequences of an Expired Certificate For the Certificate Owner | Consequences of an Expired Certificate For Your Customers and Other Users |
| SSL/TLS Certificate | Loss of customer trust. Loss of revenue and sales. Brand and reputation damage. Higher risks of attacks. | Warning error messages. Sensitive data can be stolen or modified in transit. Inability to use a service or a website. |
| Code Signing Certificate | Malware being signed in your name. Reputational harm that can result in reduced numbers of downloads. Your application no longer being trusted. | Risk of malware infection. Scary warning messages. Credential or sensitive information theft. |
| Email Signing Certificate | Emails will be sent unencrypted and unsigned. Your organization won’t be compliant with privacy regulations. Cybercriminals can pretend to be you. | Warning message. Phishing attacks. Leak of sensitive information. |
SSL/TLS Certificates: What Does the ‘Security Certificate Expired’ Message Mean?
Letting an SSL/TSL certificate expire can have devastating effects on your organization and customers. That’s why you should never underestimate the impact that even one expired SSL/TLS certificate could have on your business.
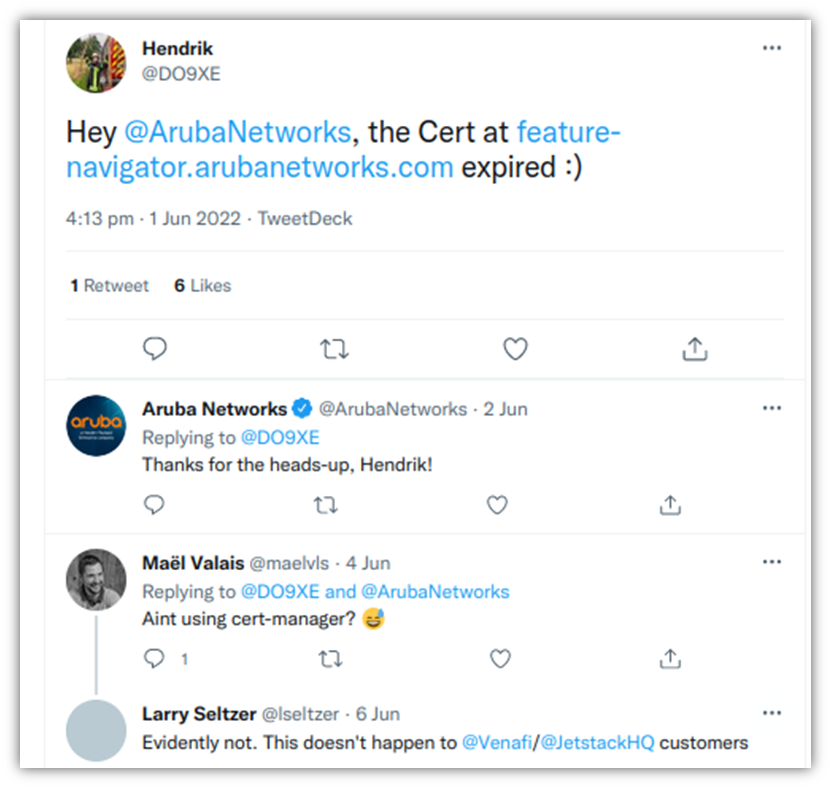
Let’s consider a certificate expiration incident that happened to Aruba Networks in June. Someone at the company forgot to renew the SSL/TLS certificate for their Feature Navigator website and didn’t notice something was wrong until a user informed them via Twitter on June 1. As a result, the website kept on showing the same warning at least until June 6. That’s not good for an organization’s reputation. But why did it take them so long to renew it? Because to renew a certificate, every organization has to go through the verification process again to ensure that the information on the certificate is still up to date.
Consequences For the Certificate Owner
Did you forget to renew your SSL/TLS certificate? These are the consequences:
Loss of Customer Trust
No valid certificate, no validation. Thus, all browsers will show your site as not secure in big, bold letters. It’s as simple as that. Yes, you might get a few users who won’t be scared by the warning message, but those will be the exception. The majority won’t trust you anymore if you don’t address the issue. So, don’t even think about them sharing their sensitive information and payment details. Forget it — they’ll be too afraid of leaks and data breaches.
The outcome? They’ll quickly move on to doing business with your competitors.
Loss of Revenue and Sales
Data from a Baymard study shows that 18% of surveyed customers don’t complete their orders because they don’t trust the website with their credit card information. Baymard also discovered that customers’ perceptions of website security is largely determined by how visually secure the website looks. Do you want to keep on making money? Don’t jeopardize your customers’ shopping experience. Ensure that your website will never show a warning message due to an expired security certificate.
Brand and Reputation Damage
As mentioned at the beginning of this article, many big organizations have issues with expired security certificates. Some of them, sadly, more than once. While the majority manage to survive and limit the damage by investing loads of money in cleaning their image, what about smaller businesses? Throwing money at the problem isn’t always so easy for them to do.
As a customer, would you buy a new tablet from a website showing that warning messages we showed earlier? I don’t know about you, but if I see such a warning on a website, there’s no way I’d buy anything from it or return to that website. Ever. Not even to just browse around once the security certificate issue is fixed.
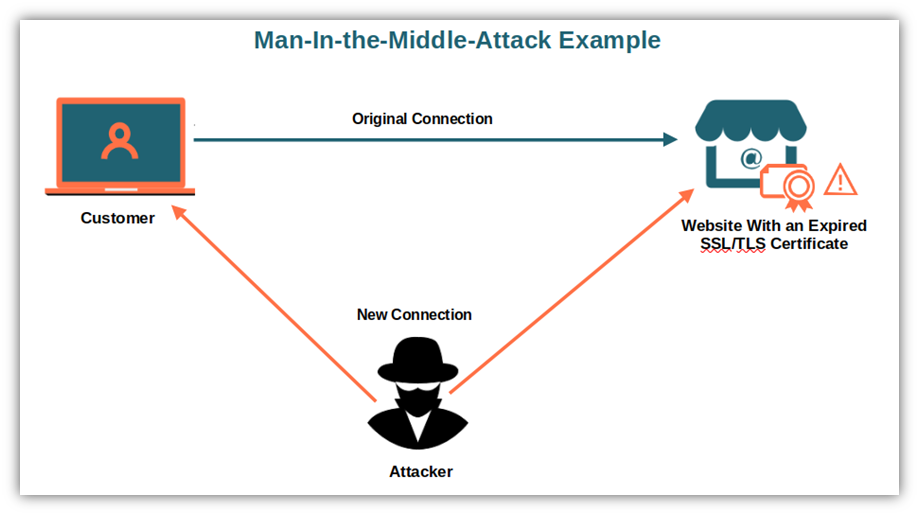
Higher Risks of Attacks
An expired certificate is like a door that doesn’t close properly or lock anymore. Everyone can see what’s happening on the other side of the door because it isn’t closed. And it’s a real feast for hackers. All information shared isn’t secure anymore and can be easily read by anyone. Or, even worse, cybercriminals can place themselves in the middle of the communication between the browser and the server (i.e., a man-in-the-middle attack). Posing as the website owner or a customer, cybercriminals can steal sensitive information or infect a target website, network or device with malware.
What about your customers and users, though? What are the consequences for them?
Consequences For Your Customers and Other Users
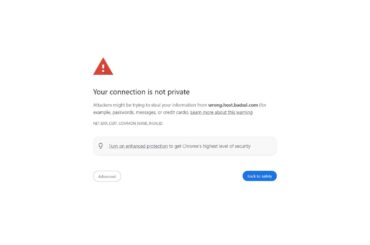
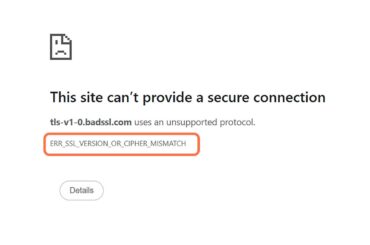
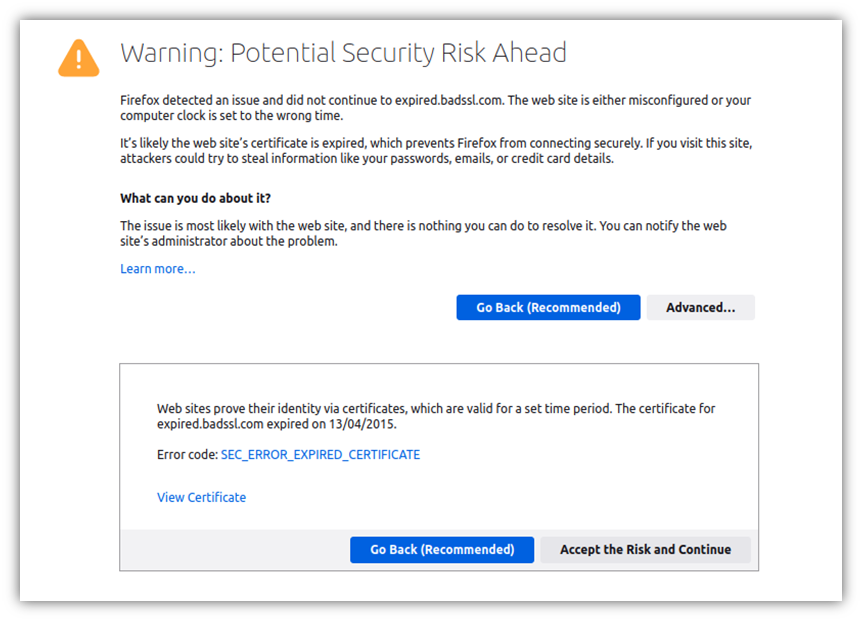
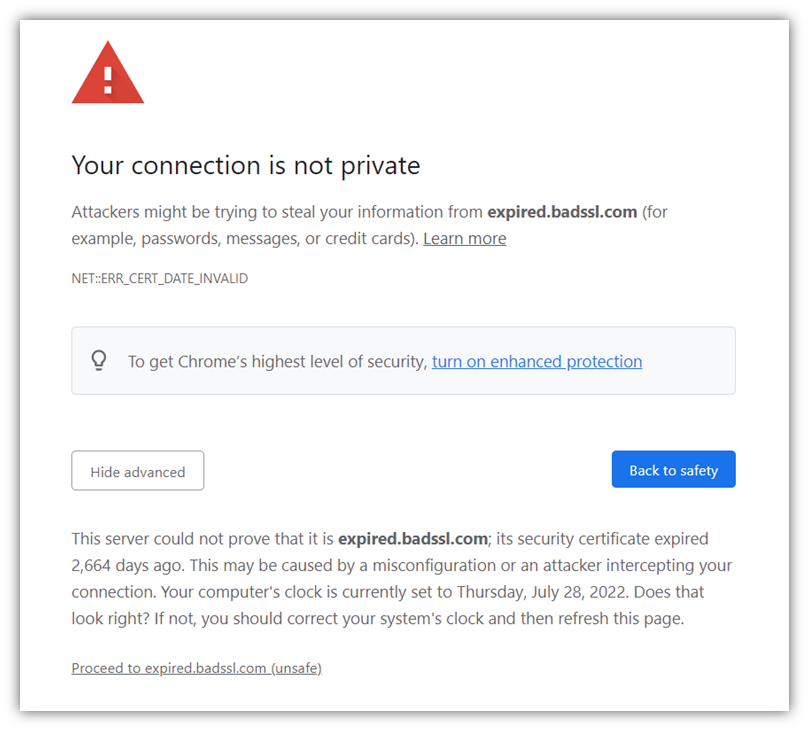
Warning Error Messages
‘This connection is not private,’ ‘This site is not secure,’ or ‘Warning: Potential security risk ahead.’ These are the typical messages that your users or customers will immediately see when visiting your website if you forgot to renew its SSL/TLS certificate. What would you do as a user? You’d likely run away. That’s what the majority of customers do, too.
Stolen Sensitive Information
As previously discussed, exploiting an expired security certificate is the low-hanging fruit for hackers. And once a customer’s credit card information or sensitive data is stolen because you forgot to renew your website certificate, all your efforts and hard work you put into your business will go down the drain. Stolen or even deleted, in an instant.
Inability to Use a Service or a Website
This is what happened in 2021 to Google Voice users worldwide. Due to an expired TLS certificate, customers were unable to make or receive voice-over-IP (VoIP) calls for more than four hours. Got an important conference call with your boss? Not possible. Do you need to call a customer to inform him that his delivery will be delayed? That’s not going to happen, either.
Can you see the magnitude of the impact that a single expired SSL/TLS certificate can have on your business now? And these are just a few examples. Find even more reasons to never miss to renew your SSL/TLS certificates in our article “What Would Happen If Your SSL Certificate Expired.”
Code Signing Certificates: What Does ‘Security Certificate Expired’ Mean?
Windows 11 was released to the public on Oct. 5, 2021. On Halloween of the same year, some features (including the Windows emoji panel, Snipping Tool, and the touch keyboard) failed to load due to an expired code signing certificate. Of course, the issue made it all over the tech news. That wasn’t really the best start for Microsoft’s new operating system, was it?
So, what kind of impact would have an expired code signing certificate on organizations and customers?
Consequences of Using an Expired Code Signing Certificate For You as the Certificate Owner
In addition to the points listed above referring to website certificates, an expired code signing certificate could cause:
Malware Being Signed in Your Name
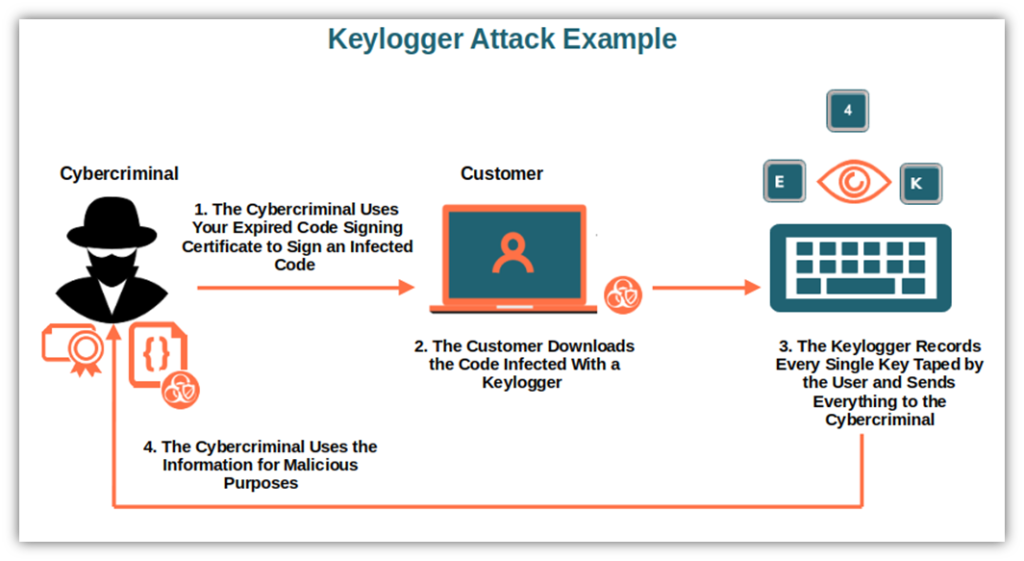
An attacker could use an expired code signing certificate to sign malicious software. This is what happened recently with the NVIDIA data breach. The hackers used two old code signing certificates that expired in 2014 and 2018 and used them to sign malicious codes. How did they do that? They took advantage of the fact that expired code signing certificates can still be used to sign some types of Microsoft drivers.
Imagine what would happen if one of your employees installed infected code, or if malicious code was uploaded on your website or on third-party sites posing as genuine applications developed by your organizations. Without a way for customers to see whether the software legitimately came from you and hasn’t been altered, the damage could be immense.
Reduced Number of Downloads
When a code signing certificate expires, the user will get a warning message during the download or installation of software that hasn’t been timestamped. Would you install an app or software when your browser or operating system is telling you that there’s something wrong with it? Of course not.
Your Application Is No Longer Trusted
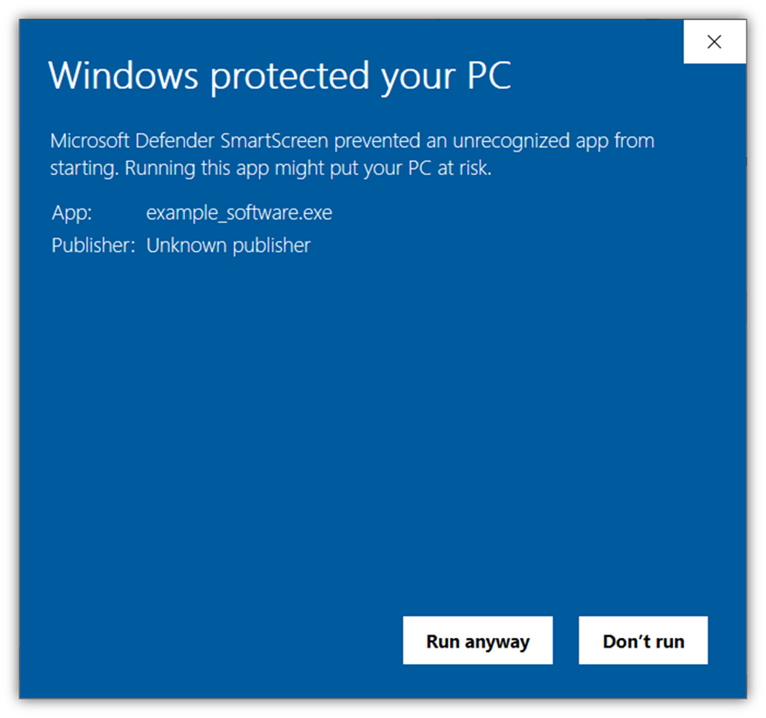
Have you ever seen the warning message below? That’s an example of what all your users and customers will see when downloading your windows application when its code signing certificate is expired. All major browsers and antivirus will also flag the application as untrusted.
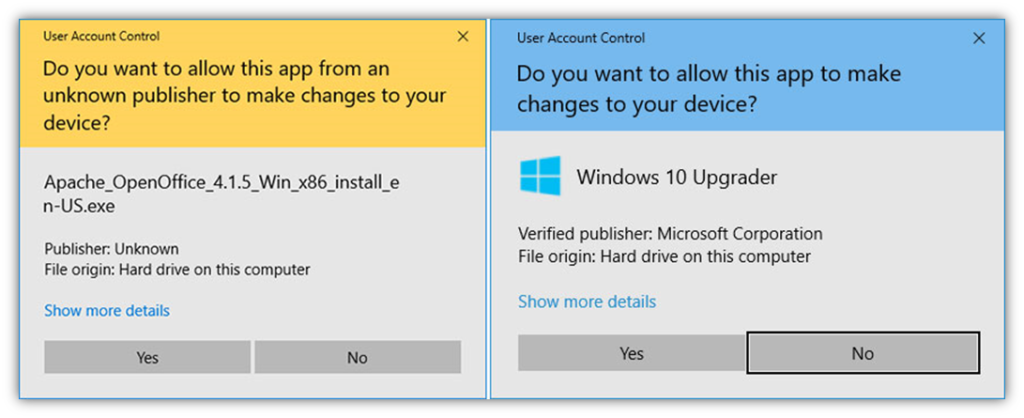
Otherwise, your users will likely see similar Windows User Access Control (UAC) warning messages indicating that the software is unknown and, therefore, shouldn’t be trusted:
Consequences of Using an Expired Code Signing Certificate For Your Users
- Risk of infection. Tricking a user into downloading a malicious driver by signing it with an expired code signing certificate isn’t too difficult. Above all, if the cybercriminal manages to upload it on a fake website that’s designed to look like a legitimate site. And with more than 46,000 phishing URLs identified by Vadesecure in Q1 2022, the risk of infection looks pretty high.
- Warning message. Like with SSL/TLS certificates, when downloading or installing a code with an expired certificate, the Windows user will see the warning message shown in the screenshot above. Do I need to say more? The sentence ‘Running this app could put your PC at risk’ says it all.
- Credential or sensitive information theft. This can be the aftermath of downloading an infected application or software we talked about before. A trojan, spyware, or keylogger is injected by the hacker into the application downloaded by the user. If this happens, it’s game over. The attacker can now steal the user’s passwords, IDs, banking details, you name it.
There we go. Now, you have enough reason to avoid forgetting to renew your code signing certificates. Last but not least, let’s explore what happens when an email signature expires. Will it have the same catastrophic impact? Let’s find it out!
Email Security Certificates: What Does ‘Security Certificate Expired’ Mean?
So, what does ‘security certificate expired’ mean with regard to email security? With an email signing (i.e., S/MIME – secure/multipurpose internet mail extensions) certificate, users can digitally sign and encrypt the content of their emails (attachments included) to:
- Guarantee its authenticity
- Offer assurance about the message’s integrity
- Ensure that only the intended recipient will be able to view its content
How? The email is signed and encrypted by using the recipient’s public key. Once sent, the recipient’s email client will verify the digital signature is legitimate and decrypt the message automatically using the private key. Easy as a pie! But what happens when you send an email and your certificate is expired?
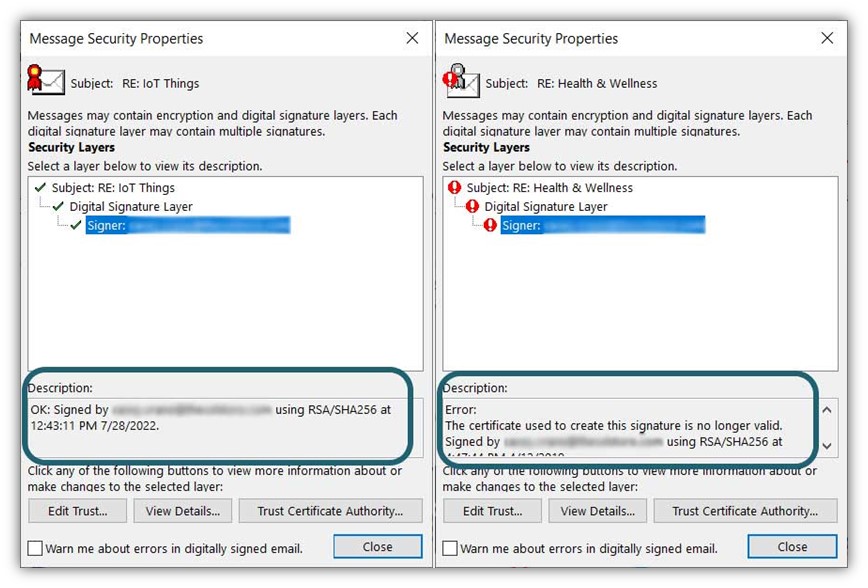
Consequences For the Certificate Owner
Now, let’s think of what all of this means as we answer the question “what does security certificate expired” mean in the context of email security?
- Emails will be sent unencrypted. This means that any third party intercepting the emails will be able to read them, attachments included. He could also alter the content of the email before it reaches the recipient. How? Two potential methods are 1) adding an infected attachment to it, or 2) by changing the content of the message. Neither of these options is good, especially if you’re sending your customer’s sensitive information or if the email includes a strictly confidential presentation.
- Your organization won’t be compliant with privacy regulations. Nowadays, virtually every business, small or big, handles sensitive information in one form or another. If you fail to meet industry or regional regulatory requirements, you’ll risk facing hefty fines and potential lawsuits. Email encryption helps organizations to protect that kind of information as required by many regulations, including:
- The European General Data Protection Regulation (GDPR),
- The Health Insurance Portability and Accountability Act (HIPAA), and
- The Payment Card Industry Security Standards Council (PCI SSC).
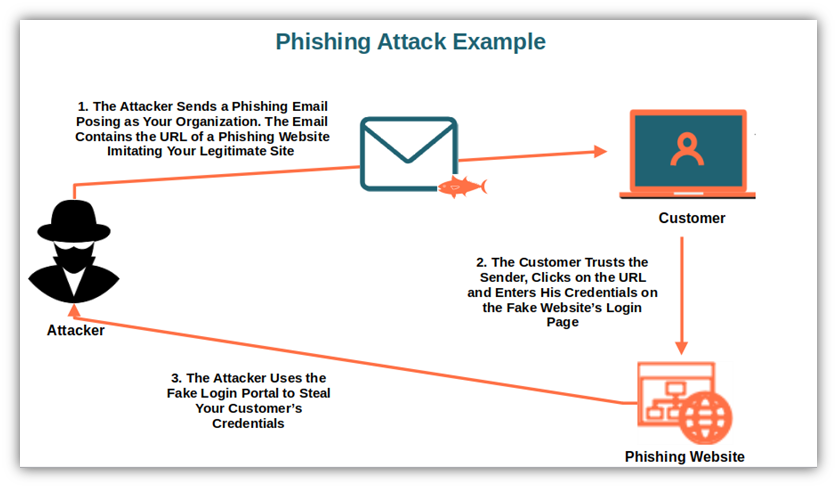
- Cybercriminals can pretend to be you. Without the digital signature capabilities offered by using a valid email signing certificate, your recipients will no longer have a verifiable way to differentiate your emails from cybercriminals impersonating you. They can do this to trick recipients into thinking that they’re really coming from you (i.e., email spoofing).
Consequences For the Users
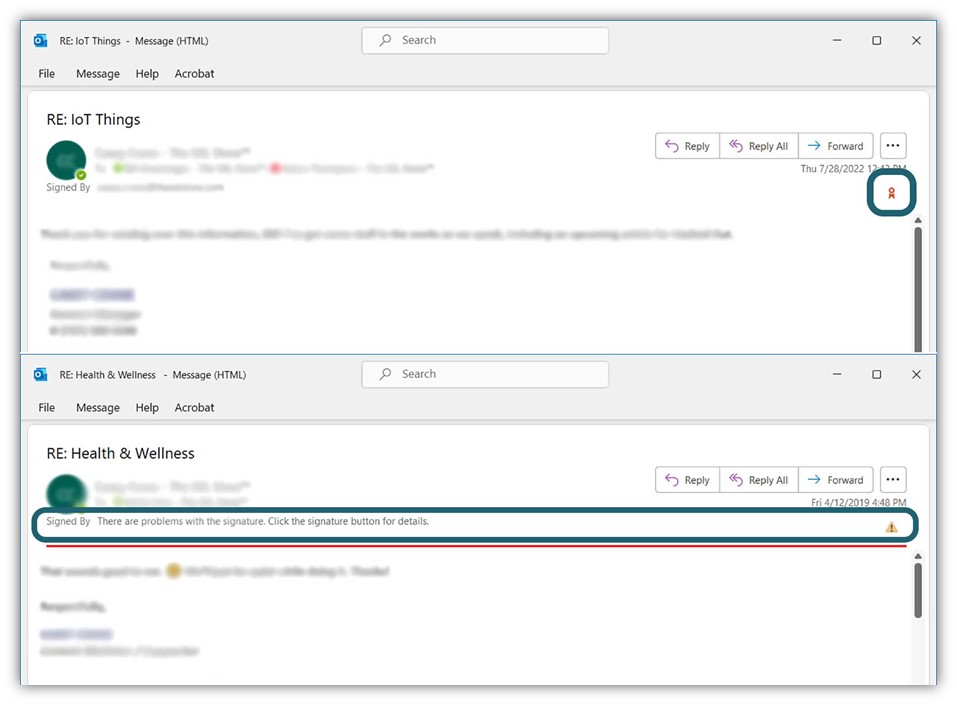
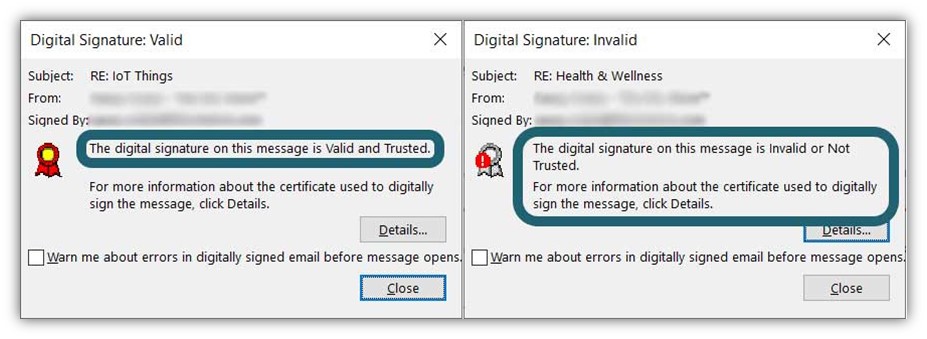
Displays Unsettling Warning Messages
Let’s say you sent an email to one of your customers and, a few minutes later, its signing certificate expires. If the recipient opens the email after the certificate’s expiration, if it isn’t timestamped, the email client won’t trust it and will display an error message. The recipient will still be able to read your email because it won’t be encrypted. However, they’ll will be warned that the signature isn’t valid. The same will happen when trying to reply to the email.
Can Be Used to Carry Out Phishing Attacks
Do you remember when we talked about email spoofing a few moments ago? Now, imagine that a customer receives a spoofed message and thinks that the email is from you, a brand they trust. In the email, the hacker asks the recipient to click on a link to a fraudulent website very similar to yours and confirm their credit card payment details. The customer, thinking that the email is genuine, follows the instruction and the damage is done. Do you think this customer will ever trust your brand again? Not likely, as highlighted by Axway’s Global Consumer Survey results.
Leak of Sensitive Information.
Once the email isn’t encrypted, everyone has access to its content. And if the email’s body includes some sensitive information (e.g., bank account details, usernames, passwords, health information) a malicious third party could easily get hold of it and use it to his advantage.
Now that you have a better idea of the often catastrophic consequences of forgetting to renew an expired security certificate, let’s see a few tips that’ll help you avoid you saying, in the words of a famous Britney Spears song, “Oops!…I did it again.”
How Can I Avoid Letting My Security Certificates Expire?
Tired of getting to the office in the morning and seeing the ‘This connection is not private’ warning popping up on your organization’s website? Do you want to stop receiving customers’ complaints about one of your applications showing the “Publisher Unknown” warning message during download or installation? End the misery now by implementing the following tips.
Use a Certificate Lifecycle Management Solution (CLM)
A certificate manager is a tool that virtually allows you to set-it-and-forget-it when it comes to managing your PKI digital certificates. In other words, a reliable CLM allows you to automate many certificate management tasks and manage them in a single tool. There are tons of solutions and tools out there you can choose from, depending on your needs and the number of certificates you’ll have to manage. Pick one, install it, and let it do the work from a to z — everything from certificate requests to provisioning and, of course, renewals.
Pay Attention to CA Notifications
You can’t afford a CLM? No problem, keeping an eye on the emails you’ll receive from the certificates’ issuing CAs. This method doesn’t cost you a dime but does require you to pay close attention to your inbox. It doesn’t matter what CA issued your certificates; they’ll all send you several expiration notification emails well before the certificate’s expiration date. All you have to do is:
- Ensure that the reminders are sent to the right people. This includes system admins, developers in case of code signing certificates, IT managers, etc. You can even create a specific distribution list that includes these specific individuals.
- Remember to review your email contacts from time to time and update if necessary. People move on, get sick, and go on holiday. Things change and you don’t want the email to end up in a black hole. Keep your list of responsible parties up to date by maintaining a current list of users and permissions.
Avoid Using Spreadsheets and Other Manual Tracking Methods
I know, sometimes money can be tight. However, being among that 42% of organizations identified by the Ponemon Institute still using spreadsheets to manually track certificates isn’t a good idea. Sure, you may save money on the front end, but it can cost you dearly later in case of a data breach or loss in sales because of an expired certificate.
One of the organizations I was working for was a big fan of “homemade” solutions. Don’t get me wrong, I love homemade when talking about biscuits, cakes, and food in general. But in cybersecurity, “homemade” solutions have always ended up creating more problems than benefits.
Limit the Usage of Self-Signed or Wildcard Certificates
Self-Signed Certificates
First and foremost, self-signed certificates should only be used internally (e.g., for internal testing); never use them to sign applications or exe that’ll be available to download to the public. OK, I know you’re a conscious developer, and you don’t do that. However, you have to remember that those certificates can still be exploited by cybercriminals to spread malware within your organization.
Wildcard Certificates
These certificates are incredibly handy as they can secure multiple subdomains (e.g., *yourorganization.com can be used for faq.yourorganization.com, blog.yourorganization.com, products.yourorganization.com, and so on) and save you money. However, the National Security Agency (NSA) raised a warning about their dangers, saying they are vulnerable to attacks. This is, in part, because when the certificate expires, you’ll have to update the private key on all servers using the certificate.
That’s a significant amount of work that’ll cost you time and money when doing this manually. Thankfully, the same NSA offers some risk mitigation strategies — one of which is to carefully manage your wildcard certificates and keys. This is where using a certificate lifecycle management solution can help.
Use Time Stamping
More than a solution, timestamping is a temporary workaround that can help you gain a bit of time in case you did forget to renew your code signing certificate.
Adding time stamping to your code signing certificate will enable you to give a kind of “longest life” to the codes you’ll sign with that certificate. When a customer downloads that code, even if the code signing certificate itself is now expired, they won’t see any alerts and will be able to download and install the code without issues. This is because the timestamp attests that the software was signed when the certificate was still valid.
Why? Because the customer’s device, to validate the code will check the signature based on the time it was signed (i.e., time stamping) instead of using the actual date. Beware, though: this is a temporary solution as you won’t be able to use the certificate to sign any new code or application with the exception of a few Microsoft drivers. It’s expired, remember?
Final Toughs on What ‘Security Certificate Expired’ Means
Email certificates, code signing certificates, SSL/TLS certificates. Even small organizations have so many security certificates to manage nowadays that it’s easy to forget to renew or replace one.
And one expired certificate is enough to:
- Drive away customers from your website,
- Negatively impact the customers’ trust in your brand or, even worse,
- Expose your entire organization to vulnerabilities and enable attackers to decrypt sensitive information.
Now that you are familiar with the risks, ensure an effective certificate management strategy is in place. Automation is the key. Many tools are out there that can help you and your team to stay on top of your collection of PKI certificates — as such, there’s no good reason left to stick to manual tracking.
Yes, certificates will keep on expiring. However, you now have the knowledge to make sure you don’t miss any certificate expiration date anymore. You can do it!