Learn everything about RSA encryption and the algorithm that’s keeping us safe in the digital world. Discover the technology behind the first tool of choice used by businesses to protect sensitive data stored in the cloud, its benefits, and its uses
Nowadays, the prevalence of malicious hackers and other cyber threats is steadily increasing. According to Deep Instinct’s 2021 Threat Landscape Report, all types of cyberattacks increased by 125% from 2020 to 2021. That’s crazy, right?
No wonder security and, of course, encryption, have become two of the world’s hot topics! The buzz around these topics could be seen at the latest RSA conference in San Francisco. This event brings together the brightest minds of the IT industry, cybersecurity professionals, organizations, and the Cybersecurity and Infrastructure Agency (CISA) to share knowledge and learn from each other.
While we can’t take you to the conference, we can tell you everything about the RSA encryption algorithm that’s at the heart of internet security.
Get ready to discover in this first part of a series of two articles:
- What the RSA algorithm is,
- What this encryption algorithm does,
- What it’s used for, and
- Why it’s such an important factor in cybersecurity.
No matter how many technologies you can buy to protect your data, encryption is a critical element that no one can do without in our modern digital world.
What’s the RSA Algorithm? The RSA Encryption Function Explained
Is there a way to find a cryptographic function that can be reversed only if the receiver has a piece of specific, unique information? This is the question that Ron Rivest, Adi Shamir, and Leonard Adleman from the Massachusetts Institute of Technology (MIT) were trying to answer for a year until they had their “eureka!” moment in 1977. That’s when the Rivest-Shamir-Adleman (RSA) algorithm was born.
The RSA encryption algorithm has become the most widely used encryption method to securely transmit or exchange information in insecure (public) channels. It is one component in a process that creates the secure, encrypted connections that enable the padlock security icon to appear in your browser. Since it was formally adopted, RSA has been the basis of many encryption schemes.
It’s a two-way cryptographic algorithm that uses two separate keys (i.e., asymmetric encryption, we’ll talk more about it in a minute) to encrypt and decrypt data. (This basically means taking plain text, readable information and converting it into unreadable gibberish.) As there isn’t an algorithm that can identify the private key starting from the public key (you’d have to have immense resources [far beyond modern computing capabilities] to carry out factoring attacks in reasonable time), it’s virtually impossible to reverse engineer. And this is exactly what makes RSA encryption so difficult to break.
Have I stimulated your curiosity? Let’s see at a high level how the RSA algorithm works and what asymmetric encryption is all about.
What Does the RSA Algorithm Do?
The RSA algorithm transforms readable data into a gibberish string of hexadecimal characters (numbers 0-9 and characters “a” to “f” and “A” to F”) to protect data in transit. This cryptographic process enables organizations to add another layer of security when transmitting sensitive data on the internet. How? By using:
- A public key (to encrypt data),
- A private key (to decrypt data), and
- Two large, randomly generated prime numbers to create the key pair).
Asymmetric encryption provides a secure way to exchange sensitive information (such as keys that allow you to establish symmetric encryption connections [i.e., the same key is used to encrypt and decrypt data]). Think of old spy movies: spies would meet up face to face to exchange key that they can use to encrypt and decrypt communications. This is an example of symmetric encryption algorithm. In this case, the spies use the same key to both encrypt and decrypt the information.
But in the digital era, there isn’t time or ability to meet in person to exchange keys as we need to establish connections in real time via the internet. Therefore, asymmetric encryption uses two separate but mathematically related keys (asymmetric encryption) to securely exchange symmetric key information; once both parties have that information, thye can use it to create sessions that are secured via symmetric encryption.
At one of the IT companies I worked for previously, access to their data center was only possible if two authorized people were physically present. Each of them had its own separate access card (key) that had to be scanned within seconds of one another. Only then the server rack door would open.
RSA encryption (or asymmetric encryption) is based on a similar concept — each party has a separate key that’s related but handles different things. In this case, one key encrypts data while the other decrypts data, and only the authorized private key holder has access to the encrypted information. How exactly? Let’s check it out.
A Brief Look at Asymmetric Encryption
With asymmetric encryption, also called public key encryption, both the sender and the receiver use one key (public key) to encrypt a message and another different key (private key) to decrypt it.
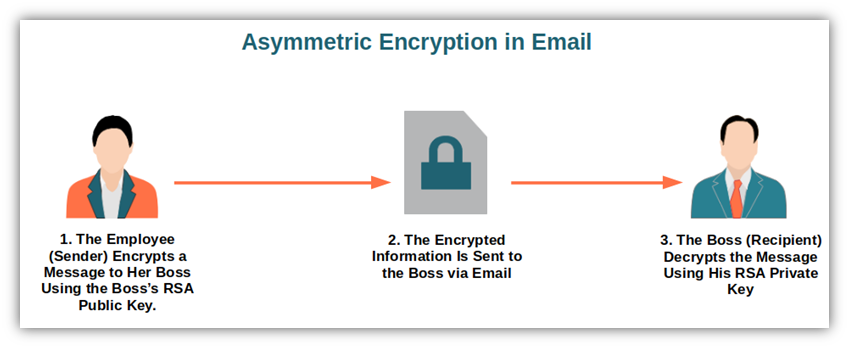
Let’s say you want to send some confidential information about the project you’re working on to your boss. RSA encryption (i.e., asymmetric encryption) helps you ensure the information will only be viewed by him and not any unintended parties. To do that, you’ll just have to follow a simple but ingenious process:
- Encrypt your message using your boss’ public key. Remember that the public key is available to anyone who wants to send him a message as it’s only used for encryption. It’s derived from factoring a large prime number.
- Send the encrypted information to your boss. Once encrypted, the information about your confidential project is sent by email to your boss.
- Your boss decrypts the message with its private key. Et voila’. Once your boss receives your email, he’ll be able to decrypt the whole message using its private key, known only to him. The confidentiality of your project is safe!
This doesn’t sound overly complicated, right? Yes, there’s some elaborated mathematical formula doing the magic behind the scenes, but this is something we’ll dig into in our next article. For now, let’s keep it simple and learn more about the basics of RSA encryption.
What Is the RSA Algorithm Used For?
The RSA algorithm is used nearly everywhere in the digital world, on its own or in conjunction with other encryption methods (i.e., hybrid encryption schemes). For example, when you first accessed this blog post, your browser just used it in the SSL/TLS handshake to establish a secure connection (hypertext transfer protocol secure — HTTPS).
Do you want to check it by yourself? Let’s consider how this looks in Mozilla Firefox:
- Click on the padlock you see next to your browser before the article’s URL.
- Select Connection secure.
- In the next window, click on More information.
- Under the Security tab, select View certificate. This will open a new window.
- The pop-up will show you the certificate details. Among them, you’ll also see the public key information indicating that the website is using RSA encryption.
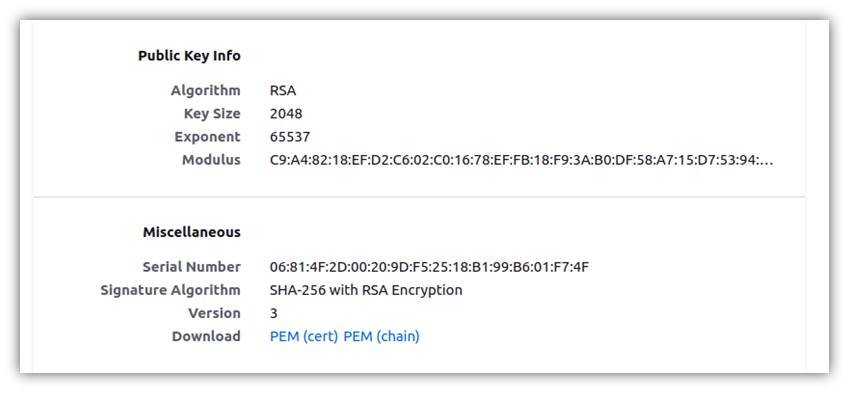
This means that any information you send to our website during the initial SSL/TLS handshake will be encrypted using the public key (RSA encryption), while the same information will be decrypted using our RSA private key. Once the verification is over, the main communication for the session will use symmetric encryption. Basically, RSA asymmetric encryption comes into play at the beginning of the handshake before switching to symmetric cryptography for the rest of the session.
OK, so we know now that RSA is used in HTTPS in conjunction with symmetric encryption to boost security. But this is just one example. So, where else is it used?
| RSA Encryption Algorithm Main Applications | Examples |
| Message encryption | Email providers. Chat rooms and messengers. |
| Digital signature | Email signing. Document signing. Cryptocurrencies. Executables and code signing. |
| Code signing | Commercially distributed software. Internal software. |
| Virtual private network (VPN) | Secure connections (TLS handshake). |
Message Encryption
Do you remember the example at the beginning of this article of you having to send confidential information to your boss? That’s message encryption with the RSA algorithm.
- Email encryption. You send an encrypted message to your boss by using his public key to encrypt the message and he decrypts it using its private key, which only he knows. This way, you don’t need to exchange private keys before sending the message. This is a major plus for the security and integrity of encrypted messages if you consider a malicious actor could easily compromise insecure communication channels. Pretty neat, huh?
- Chat rooms and messengers. The same process can also be applied to end-to-end secured chat apps to ensure that those two people and nobody else can only read the messages exchanged between two people within that specific chat.
Digital Signature
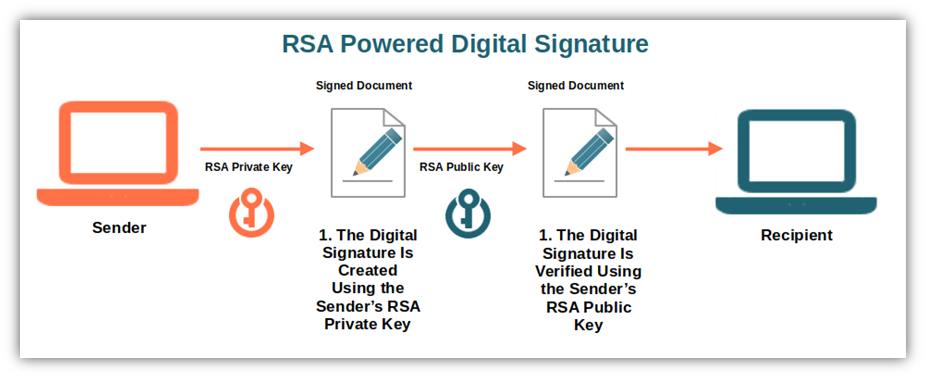
Digital signatures can be used for any kind of message, regardless of whether it’s encrypted or not. They’re widely used by private individuals and industries as the RSA private key is utilized to sign the cryptographic hash of the message or file.
Did you receive a digitally signed document? You can verify its authenticity by decrypting the signature with the RSA public key. If it works, the signature is authentic. Digital signatures are often used for:
- Email signing. Used to confirm message integrity and sender’s identity by attaching a verified cryptographic digital signature to it. How? By ensuring the recipient that the message he received hasn’t been tampered with and that the sender has really sent it. They’re supported by most email programs.
- Document signing. Frequently used to digitally sign documents in various formats (e.g., Word, Excel, PDFs), This process enables users to ensure that a document file hasn’t been altered since it was created. The digital signature is appended to the document by following simple steps. When the recipient receives the file, their client or operating system will automatically check if the signature appended to the file matches the one included in the certificate. This way, the recipient will be able to immediately spot any unauthorized modification.
- Cryptocurrencies. Used to authenticate the blockchain and manage digital currency transaction data. Are you a crypto user? With the RSA algorithm, you’ll be able to confirm your participation in a transaction.
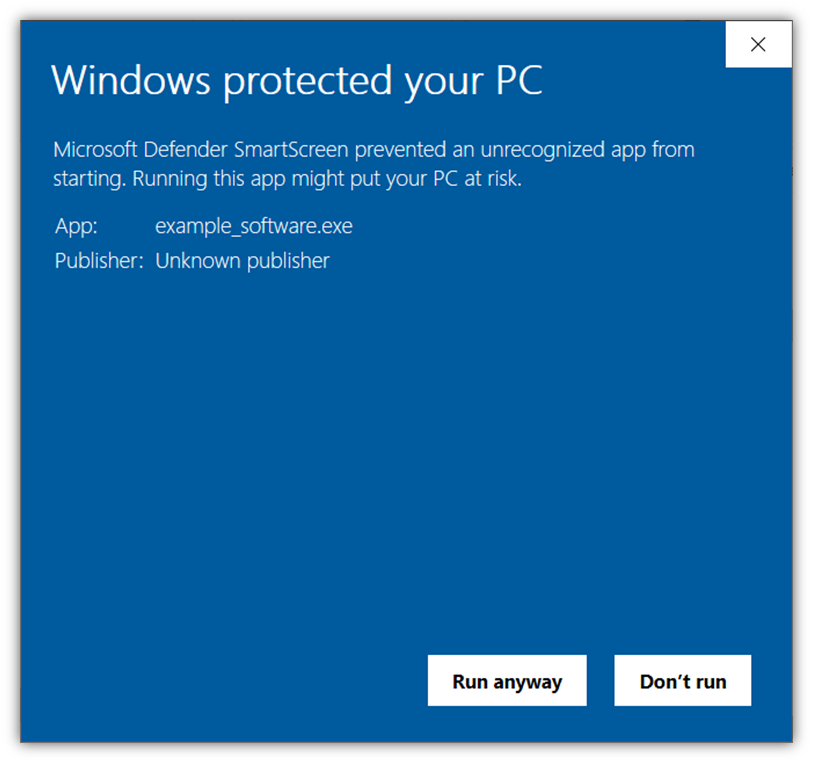
- Executables and code signing. Used by software developers and vendors to validate executables, drivers and software by confirming their identities and providing file integrity. The users downloading the file or executable will immediately know that it comes from you and it hasn’t been tampered with. Do you want to know more? Let’s find out how it works.
Code Signing
Do you want to reassure your users and/or customers that the software or app available to download is authentic and comes from a trusted vendor? Signing your codes with the support of the RSA encryption algorithm (using a key that’s 3072 bits or larger) will do the trick. How? By digitally signing your code, software, or other executables, of course!
- Select the code signing certificate that best fits your needs. You can choose between the standard (organization validation, or OV) or the extended validation (EV) code signing certificate. Tip: Opt for the extended validation certificate for enhanced security features and an improved customer experience. The process for purchasing and installing is different for these two types of code signing certificates. We’re talking about standard (OV) code signing certificates in this example.
- Get a CSR certificate and a private key. To apply for a code signing certificate, you’ll need a certificate signing request (CSR) and a private key. You can easily generate them both in a blink of an eye using a free CSR generator tool by following a simple procedure or with the Windows MMC console. And guess what? There, again, you can select to get your private key based on the RSA algorithm.
- Purchase the certificate. Once you have your CSR info and the related private key, you can forward them to the certificate authority (CA) and buy the code signing certificate of your choice. Some CAs have you purchase the certificate first and then submit your CSR.
- Get your identity verified. The issuing certificate authority (CA) will run some background checks to officially validate your organization’s identity before releasing the certificate. This is a key step that’ll help you increase your customers’ trust in your software.
- Install your code signing certificate and start signing your software. Once you receive your new certificate, you can install it and use it right away to start signing any kind of executables, software, and apps.
Where can you use your code signing certificate?
Commercially Distributed Software
Code signing is so popular nowadays that many major commercial software publishers use it. Why? Because it’s considered so fundamental to users’ security that many trusted app stores and third-party software vendors have it as a mandatory requirement to be able to distribute software on their platform. Also, because it allows your organizational name/brand to display when users try to download or install it.
Did you know that app stores like Google and Apple have even their own specific code signing certificates (different from the ones we sell)? We’ll talk more about its benefits later on in this article, but it’s important to know that the certificate will help you to get rid of the “Unknown publisher” warning that could put off many customers from downloading your code.
Containers and Images
Since the last few years the use of containers in production has increased exponentially, but so have malware attacks. Signing the image at creation will protect your organization by enabling your developers to verify the authenticity of the code they receive. Do you want an example? Check out how a big tech company like IBM uses image signing to protect containers.
Scripts and Code
Do you want to protect your scripts from unauthorized modifications? You can do that by signing them directly in PowerShell. How? By adding a digital signature to your scripts. This way, users will be assured that your script hasn’t been altered and can be trusted. Tip: use self-signed certificates only to sign scripts for your personal use. If you’re planning to share your script, even within your organization, it’s safer you use a certificate issued by a CA.
Patches and Updates
Patches and updates are being released continuously these days. Much like other cybersecurity experts, I’m almost paranoid when it comes to updates. Therefore, I’ve set my Ubuntu system to install updates as soon as they’re available. (And I can tell you that recently hasn’t passed a day without me having to install an update of some sort.) Anyway, digitally signing your patches and updates will reassure your users (even those as paranoid as me) that they’ve not been modified since the signature has been added. Not bad, huh?
Virtual Private Network
Does your organization use a VPN to provide its employees secure, encrypted access to online traffic when they’re working outside the office? Or do you use a VPN to protect your identity online, above all when you’re connecting to the internet through public Wi-Fi?
If you answered yes to at least one of these questions, then there’s a good chance that your VPN provider has been using RSA keys (public and private) to secure the transport layer security (TLS) handshake. Don’t get confused, though. This is another example of a hybrid encryption scheme as VPN uses asymmetric encryption only for the handshake to transmit shared keys. After, all data will be encrypted with a symmetric key (i.e., using symmetric encryption).
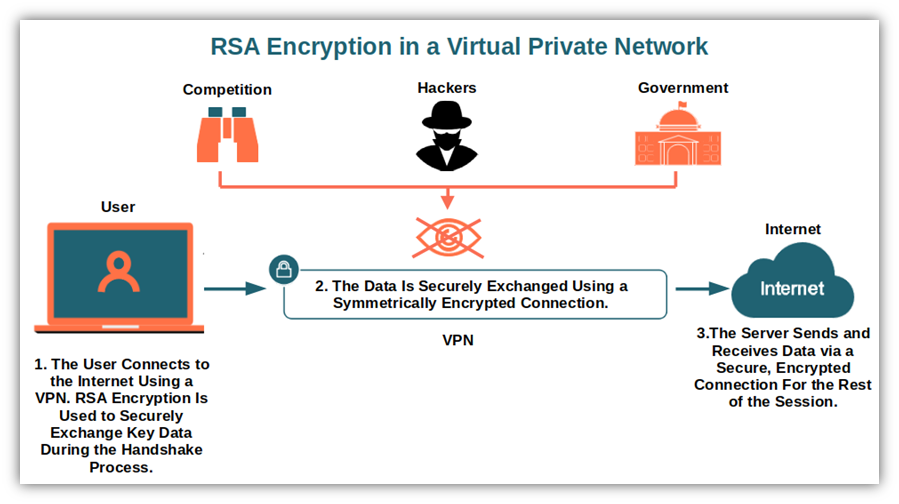
Last but not least, it’s essential to know that to keep the handshake secure, the RSA key size used shouldn’t be smaller than 2048 bits. Why? Because it’ll have to be sufficiently long to be resistant to factoring attacks. Remember: the longer the RSA key, the more secure it is. (Note: You don’t want to just keep using bigger and bigger keys, though… the larger the key, the more computational overhead required. This is why we use asymmetric encryption initially and then switch to symmetric encryption for sessions.)
These are just a few examples of the main applications of RSA encryption. But there are many more, from encrypting customer identity in e-commerce transactions to hybrid encryption to improve the security of internet of things devices (IoT). But why is the RSA algorithm so widely used? This is what we’re going to see next.
Why Does RSA Encryption Matter to Cybersecurity?
In the last two or so decades, new and less resource-demanding algorithms like the elliptic curve cryptography (ECC) have been gaining traction due to the advent of powerful computers (and future quantum cryptography) and the age of IoT.
However, the RSA algorithm remains one of the most trusted and used algorithms by many for secure data transmission to date. Why? Because the RSA algorithm is:
- Rooted in secure data transmission. Born in the 70s, it has been used as a well-oiled encryption scheme across virtually all industries.
- Faster in encryption than the Digital Signatures Algorithm (DSA). Compared to the digital signature algorithm (DSA), another federal information processing standard (FIPS) for digital signatures, it allows faster encryption, making it ideal for verification and encryption.
- Hard (though not impossible) to break. Did you know that in 2020 a team from France and the United States participating in an RSA factoring challenge (competitions organized to encourage mathematicians to break RSA encryption) managed to factor an RSA integer? Do you want to know how long it took them? Let me give you a hint: your lifetime won’t be enough. In fact, it took them the equivalent of 2,700 years in total to compute it. They achieved this by using tens of thousands of computers running for months, day and night. And that was considered fast! Yes, with quantum computing, things may change. But until then, it’s going to be too infeasible (e.g., too costly and time consuming) even for the best hacker to break it using modern resources.
- More secure than symmetric encryption (when using larger keys). If speed and resources aren’t an issue for you, then asymmetric encryption is going to be the best choice. Using larger keys will guarantee you a much higher level of security. But if you need to work at scale, symmetric encryption is the better option because it is highly secure using smaller key sizes.
- A proof of authenticity. Since the RSA key pairs are related to each other, if a malicious third party manages to intercept the message, he won’t be able to decrypt it as he won’t have the correct private key.
If I can add my two cents, I’d also say that I find it fascinating. Can you believe it? In an era where everything is programmed to be obsolete after a few years, there’s still something that works like a Swiss clock since 1977. Maybe RSA will be replaced in a few years with the advent of quantum computing, but its inventors must be proud as it had more than an honorable career. The RSA algorithm is a rarity, a cybersecurity mammoth.
I hope this article answered some basic questions about RSA encryption. Now that you know what it is and its advantages, you’re ready to go technical and discover how this cybersecurity Methuselah works. Find it out in our next article!
Final Thoughts on the RSA Algorithm in Cryptography
In today’s digital world, the RSA encryption algorithm and other encryption methods are becoming more and more important. From sensitive data and transactions to communications, the need for secure and private data transmission will never fade. Therefore, it’s important to have a strong understanding of secure algorithms like RSA.
Cyberattacks will keep on evolving, forcing security specialists to find new ways to keep hackers away. For almost 50 years, RSA has secured online transactions and sensitive data against malicious third parties and to date, it’s still considered one of the best encryption algorithms for cybersecurity.
Now that you know what the RSA is, be certain to include RSA encryption in your organization’s security tools to secure your email communication and stored data. That’s not all though. Stay tuned for our next article to learn in-depth how RSA encryption works.





