24+ billion credential pairings — many of which compromised credentials were available for sale on the dark web in 2021, according to research from Digital Shadows. That’s 65% more than in 2020. Learn how credential theft attacks operate and how you can protect your customers and organization because everyone is just one weak password away from a security breach
“Password,” “123456,” “qwerty,” and “12345678.” Among the four, which one do you think was the most commonly used password in 2021? While all of them can be cracked in less than one second, the correct answer is “123456,” according to Nordpass.
With Verizon’s data indicating that 80% of the breaches in 2021 involved the use of stolen credentials, passwords are one of the weakest links for many organizations. Why? Because credential stealing is usually easy and many cybercriminals are social engineering experts. One weak password is enough to put your organization and all of its data at risk of breach or compromise. And no one wants that — particularly not your customers.
Companies like Colonial Pipeline, SolarWinds, and Twitch were all victims of data breaches due to stolen credentials. Keep your company out of the headlines as the victim of the next breach. Discover the most frequent credential theft attack techniques and learn:
- How they work, and
- What you can do to prevent them.
What Is Credential Theft? Exploring Credential Theft Attacks
Credential theft is the cybercrime act of stealing a victim’s personal user ID and password (i.e., proof of identity). Its main goal? To gain access to secure systems, accounts, and networks, and gather sensitive or critical information. It’s the first step of a cyber attack that enables malicious actors to work undetected throughout an organization’s system and wreak havoc.
It’s a bit like a spy movie when a secret agent wants to get ahold of a precious document:
- The agent steals the victim’s house keys (ID and password).
- He then lets himself into the victim’s house, unnoticed, while the victim is out.
- He looks for the document, steals it, and leaves.
Easy, right? And, much like in credential stealing, it might take a while before the victim notices what happened.
Many credential theft attacks have been carried out using weak passwords. Considered one of the costliest security scenarios with an average of $804,997 remediation costs per occurrence, its frequency has nearly doubled since 2020. This alone is already a very good reason why every organization should get familiar with the most popular attacks. However, before going into the details of the most used credential-stealing techniques, let’s see a few examples of “easy to break” passwords.
5 Examples of Weak Credentials
Have you ever used the name of your beloved pet as a password? That would be a perfect example of a weak password. Why? Because “Fluffy” or “Spot” are easy to guess, and if you’re a big fan of your pets, it’s likely you’ve talked about them or posted about them online. Other characteristics of weak passwords are:
- Short passwords. No one likes having to remember an overly complicated, long password. However, the shorter the password, the easier it is to breach. A six-character password for example could be cracked in less than one second. A 12-character one including uppercase and lowercase letters, digits and symbols could take a computer two million years to examine each possible combination. That’s a huge difference, right? But how short is too short? Nowadays, all passwords shorter than eight characters are considered weak — and eight is the bare minimum as NIST’s Digital Identity Guidelines recommend.
- Passwords using keyboard patterns. Qwerty is the typical choice for users with an English keyboard. Why? Because all letters are positioned one after the other on the keyboard. The minimum memorizing effort, maximum hackability.
- Passwords using repeated or sequential numbers or letters. ABCDEFG or 123456 are typical examples together with password123 or passwordABC. And in this case, it doesn’t matter how long — they’re all easy to crack.
- Passwords using personal information. Your birth date, the name of your best friend, a family member or pet, or your favorite band or team are all information publicly available that is very easy to find out via social engineering and data mining.
- Passwords with obvious character substitutions. Substituting a character with something else can sound clever, but hackers have thought about this too. Their hacking tools and algorithms include common substitutions enabling them to discover password variations like m1pa$$0rd.
And there are more. But if you want to have a better idea about the factors making a password weak, you need to know and understand the main credential theft attack tactics used by hackers. And this is exactly what we’re going to discover next.
How Does Credential Theft Happen?
From phishing to brute force attacks and malware, there are many ways malicious actors can get their hands on your credentials. In this article, we’re going to discover the most common credential-stealing methods and how they work. Did you find out that you’re using too many weak passwords and you’re too busy changing them all? Don’t miss out on key information and check out our credential theft attacks reference table below to get a quick summary.
| Credential Theft Attack Types | Examples | Prevention |
| 1. Social Engineering | Phishing. Spearphishing. CEO fraud. | Train your staff. Set verification processes and procedures in place. |
| 2. Malware | Spyware. Keylogger. Trojan. | Strong encryption. Patch management. Train your staff. |
| 3. Automated Attacks | Brute force attack. Credential stuffing. Password spraying. | Passwords. Strong encryption. Strong authentication. Patch management. Train your staff. Use a secure password recovery mechanism. |
| 4. Application Vulnerabilities | Unpatched applications and systems. Outdated applications and systems. Unsigned application downloads. | Passwords. Strong encryption. Strong authentication. Train your staff. Patch management. Use a secure password recovery mechanism. |
Notice an important pattern? All of the attack method categories listed above list “Train your staff” as one of the prevention methods. There’s a good reason for that: your employees are your organization’s “human firewall.”
1. Social Engineering
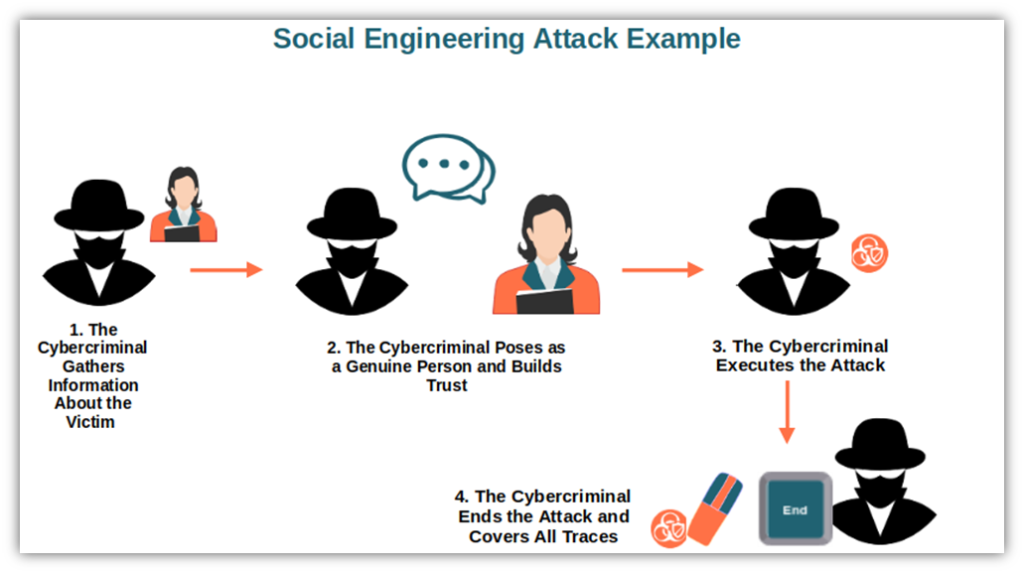
Have you ever done something just because you completely trusted the person who suggested you do it? That’s how social engineering works. It exploits human psychology by first gaining the trust of the victim (emotional manipulation) so that they lower their guard. Then the attacker pushes the victim to take a specific action (e.g., share sensitive information, click on a dubious link, etc.). And once the damage is done, it’s too late.
Social engineering is more effective and faster than trying to guess passwords and usernames. Let’s explore several attack methods that rely on social engineering attacks tactics.
Phishing
Did you know that in 2021 alone, TrendMicro identified more than six million credential phishing attempts? Phishing is one of the most popular social engineering attacks, and it can be easily perpetrated even by someone with limited or no technical experience. It also doesn’t require the attacker to know any personal details about you or your company — it’s just about trying to throw out a bunch of hooks to see who bites.
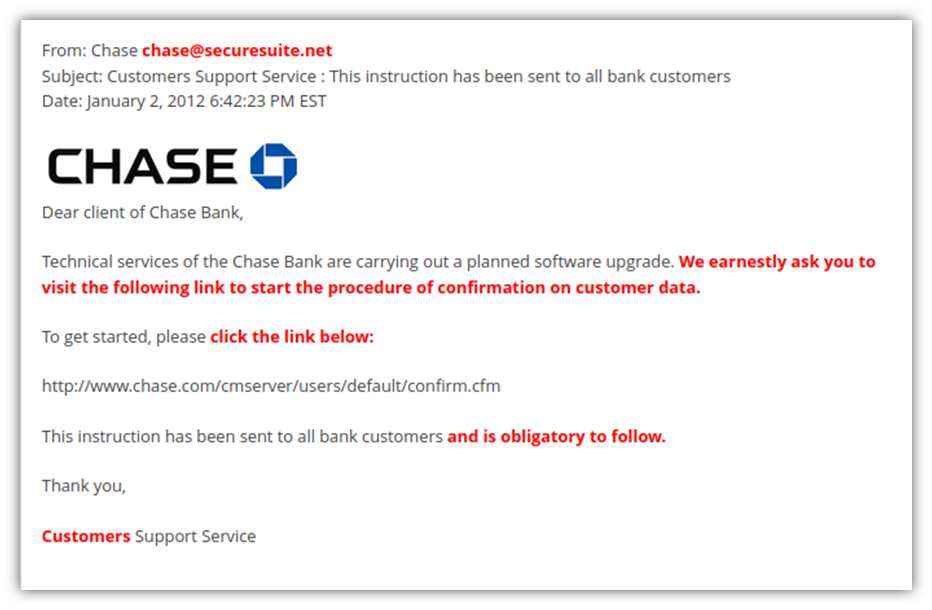
- How does phishing work? A cybercriminal sends you an email or text message posing as a legitimate organization or a trusted person (say, a popular company or service provider like Amazon or UPS). The message usually includes a link to a fraudulent company website requesting you to fill in some sensitive information or contains an attachment to download. If you trust the email and fulfill the request, then it’s game over.
- Explore an example of a phishing attack. An email is sent to users of an online banking service requesting them to immediately confirm their password and user ID due to suspicious activity on their online bank accounts. The email includes a link to an illegitimate website, very similar to the real one. The user enters his current ID and password together with the new password. Once he clicks submit, the attacker receives everything he needs to get access to the victim’s online banking account.
Spearphishing
This is a more sophisticated and specifically targeted version of normal phishing. It’s highly detailed and requires a lot of research to enable an attacker to successfully impersonate a known individual. It targets a specific organization or individuals.
- How does spearphishing work? A malicious actor identifies a piece of information they want (e.g., credentials or other sensitive information) and the individuals who have it. The attacker then sends an email to the targeted individuals masquerading as one of their trusted sources and convinces them to share the desired information. It usually has the following characteristics:
- The display name may be different from the email address.
- The message appears to come from a trusted person.
- The email contains links or attachments.
- The text gives a sense of urgency.
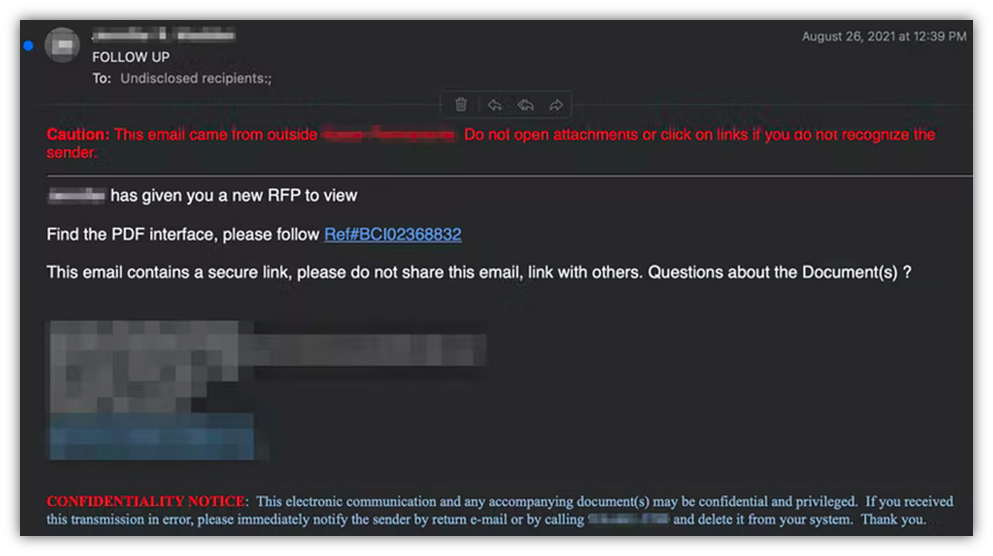
- Explore an example of a spearphishing attack. This is an interesting one that has been identified by Abnormal Security in 2021. The screenshot below shows that an attacker impersonated a trusted lawyer and sent an email to some healthcare employees. The message requested them to check the PDF document included in a “secure” link taking the victim to a Confluence page. Once on the page, another link tricked the victim into entering their Office 365 account credentials.
CEO Fraud and Whaling
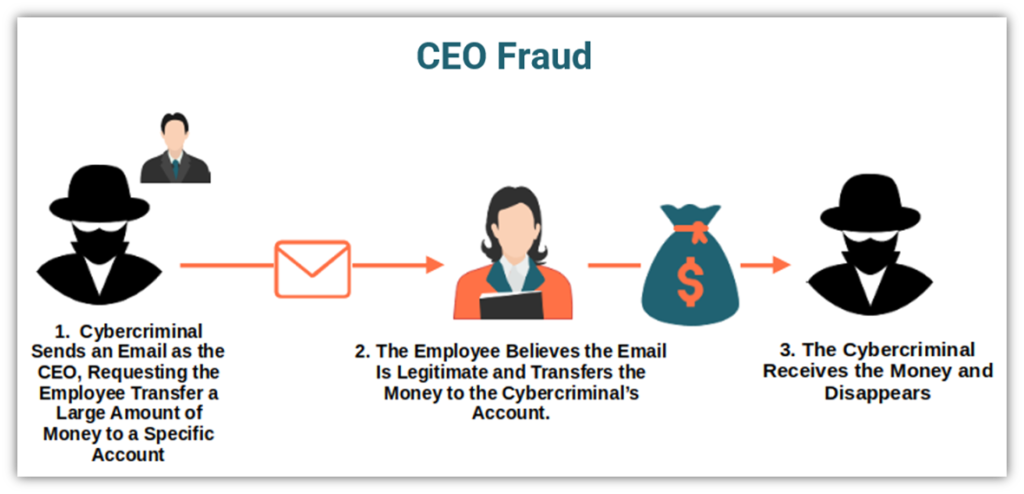
CEO fraud is a form of phishing that I’ve seen a lot when working as an email application security engineer. It involves bad guys targeting employees while pretending to be the CEO or another executive within the company.
On the other hand, whaling is another popular related method of phishing in which an attacker targets an organization. But instead of targeting middle- and lower-level employees, they instead target the c-level executives (i.e., they try to land one or more of the “whales” within your organization).
According to the FBI’s IC3 Internet Crime Report 2021, business email compromise incidents (which can be involved in some CEO fraud and whaling attacks) resulted in $2.4 billion in losses to U.S. businesses in 2021 alone. While phishing targets non-specific individuals and spearphishing specifically identified persons, CEO fraud adds something more to the equation by making the message appear to come from a highly influential individual within the targeted organization.
- How does CEO fraud work? An email is sent to specific employees in an organization asking them to reveal sensitive data or transfer a huge amount of money. As the attacker poses as the organization’s CEO or another senior member (e.g., finance manager, HR manager), the staff receiving the request will be reluctant to refuse a request from someone so high up the chain of command.
- Explore an example of a whaling phishing attack. In September 2020, trustees and the administrator of the Australian hedge fund Levitas Capital were led to approve more than $8 million in fraudulent invoices. How? The founder and other members received a fake invitation to a Zoom conference. When the founder clicked on the link malicious software was installed onto the company’s network. The same software gave the hackers control of the organization’s email system and enabled them to send fake invoices. The invoices were approved and the damage was done. Levitas Capital closed down in November 2020.
2. Malware
Based on the latest Accenture’s Cyber Threat Intelligence report, 10% of malware is identified as information and credentials stealing programs. According to the report, this kind of malware is used by hackers to steal credentials and sell them on the dark web for as little as $10 to $200. This is providing attackers with a pretty cheap gateway into organizations’ networks. Nowadays, there are countless varieties of malicious programs, including:
Spyware
Have you ever downloaded free software from a third-party website or by clicking on a pop-up on a site you visited just to save a few dollars? If you did, I’d suggest you scan your device and change all your passwords. Why? Together with the free software, you might have also installed spyware without knowing it.
- How does spyware work? The spyware is installed on a device by downloading an application/file attachment or visiting an infected website. Once installed, the spyware gets to work and steals the user’s credentials and login information through screen captures, keyloggers (we’ll talk more about it in a minute), and tracking. Then the data gets sent to the attacker who can sell it or use it to carry out a cyberattack or other crime.
- Explore an example of spyware infection. PhoneSpy is an example of spyware that was hidden in some Android regular phone applications used by Korean citizens. Once infected, the device would transmit all data (including user credentials) to the attacker. The application would request specific permissions to steal credentials and open a fraudulent KakaoTalk (a widely used Korean messaging app) login page, prompting the user to enter their ID and password.
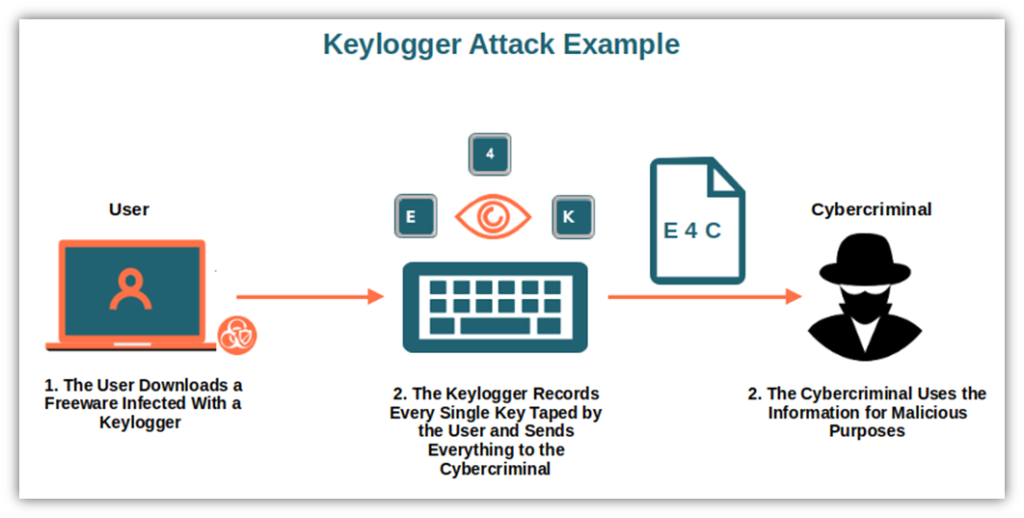
Keylogger
This is one of those malware programs that really freaks me out. It’s a kind of monitoring software that registers every key you press, even on your mobile virtual keyboard. Can you imagine the damage it could do if it’d register your online banking ID and password?
- How does a keylogger work? A keylogger can be installed on a device without your permission through the same methods used by spyware installation. This malicious software records each keystroke into a text file that will be then used by cybercriminals to steal your credentials. Some tools can even record what you copy, cut or paste, calls, or camera footage. They can be software (e.g., API-based or kernel-based keyloggers) or hardware (e.g., USB devices, hardware), placed in line with your keyboard’s connection cable).
- Explore an example of a keylogger infection. In 2015, five Anthem employees were tricked into downloading a trojan (we’ll talk more about it in a bit) with keylogger software. The attackers managed to steal credentials to gain access to nearly 80 million medical records. All this occurred because of a series of just five emails.
Trojan
When talking about malware, we can’t forget trojans. Much like its mythic name implies, a trojan is a malicious code or software program that looks perfectly legitimate but, once executed, can take control of your device.
- How does a trojan work? It usually spreads by email. Let’s say you receive a message you believe is coming from someone you trust. You click on what looks like a genuine attachment. And there we go — malware is installed on your device and a bad guy can now steal your credentials.
- Explore an example of trojan infection. The Vultur trojan was hidden in a two-factor authentication app (2FA) that was available to download from Google Play. The infected app managed to infect more than 10,000 devices before it was removed from the app store. How? Once downloaded, the app installed Vultur, a remote access banking Trojan, to steal online banking credentials and data.
3. Automated Attacks
Just like robots, bots and scripts automate repetitive tasks, malicious bots and automation are leveraged by hackers to automate large-scale credential theft attacks. The most popular are:
Brute Force Attack
Bruce force is cyber attack method that’s truly one big guessing game. It’s a trial-and-error method that often utilizes automated malicious software to test thousands or even millions of possible combinations of usernames and passwords. It uses simple random strings, common passwords, or dictionaries of common phrases until a correct input is identified.
- How does brute force attack work? In the traditional brute force attack, the cybercriminal uses an automated tool to attempt multiple logins till the system returns a valid response. Some hackers may use advanced tools, enabling them to pre-compute rainbow tables to crack unsalted password hashes (i.e., passwords converted into fixed-length strings of hexadecimal characters)
- Explore an example of brute force attack. In 2018, the Northern Irish parliament was the victim of a brute force attack. Cybercriminals used automated software and managed to get access to the Parliament members’ mailboxes before being disabled by the internal IT department.
Credential Stuffing
Classified by MITRE as a more sophisticated version of brute force attack, it exploits lists of stolen or leaked usernames and password combinations by testing them on several websites’ login pages simultaneously. Sooner or later, the hacker gets lucky and manages to get access to systems that the credentials are used for.
- How does credential stuffing work? The attacker uses a botnet to automatically try to log into multiple user accounts and on different websites using fake IP addresses. Once they find a successful combination, they’ll be able to steal sensitive information and other data from the compromised account.
- Explore an example of a credential stuffing attack. In 2020, the Canadian Revenue Agency (CRA) was the victim of a credential stuffing attack. As a result, 48,500 accounts were compromised, thereby exposing sensitive personal and financial information. This was facilitated by the fact that users often reuse passwords over and over again.
What? Are you also reusing your password? If so, you’ll want to change it immediately (or else risk suffering the same fate)!
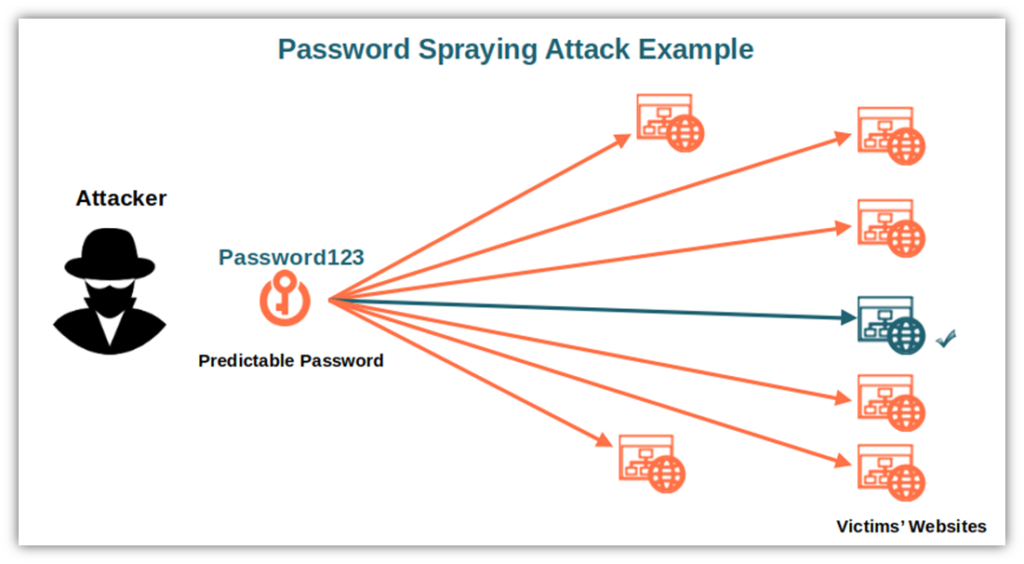
Password Spraying
Also called low and slow attack, it’s another version of a brute force attack. It’s often used to target single sign-on applications, cloud services, and email applications.
- How does password spraying work? Here the hacker tests (sprays) one single predictable password across many different websites and organizations. This allows him to avoid the account being locked by security policies when trying to log in with the same account and different passwords.
- Explore an example of a password spraying attack. In March 2019, Citrix‘s infrastructure was violated by hackers through a password spraying attack. The fact that some of the tech company’s customers were corporations, the FBI, and the U.S. government made things even more critical. The breach enabled the attackers to steal sensitive business documents and files stored on a shared network drive. As you can imagine, this had a serious impact on the organization’s reputation.
4. Application Vulnerabilities
In 2021, Edgescan identified more than 700,000 vulnerabilities out of 3.4 million scanned endpoints. That’s more than one-fourth of potentially opened doors that cybercriminals can exploit for credential stealing. But what are the most common vulnerabilities making organizations easy targets for attackers?
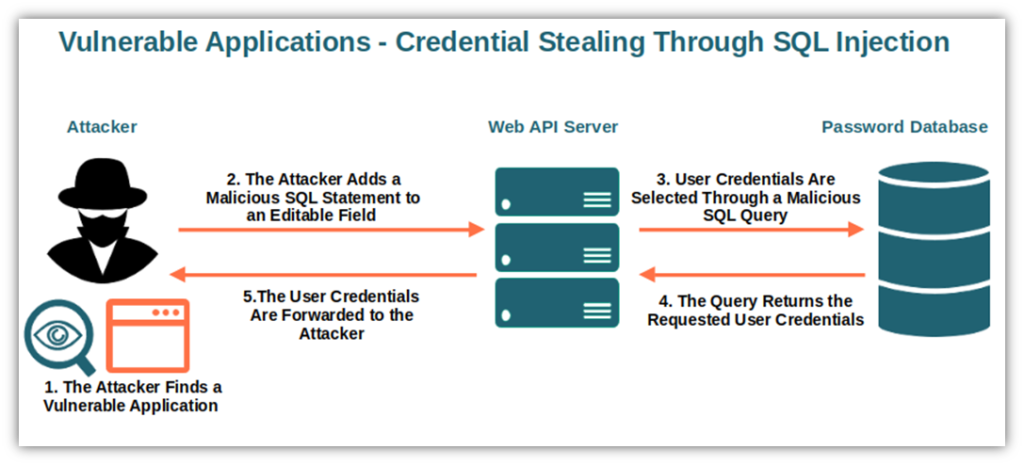
Unpatched Applications and Systems
62% of organizations interviewed by the Ponemon Institute that suffered attacks confirmed that the malicious actors scanned for open ports and vulnerable applications/systems beforehand. I get it, patch management and regular vulnerability scans cost money and time. However, they also can help you prevent the majority of credential-stealing attacks.
- How do attacks on unpatched applications and system work? The attackers scan the internet to find easy targets by looking for well-known vulnerabilities. Once they find one, they use it as an entry point to get ahold of sensitive data and credentials. When such attackers target websites, they often exploit SQL vulnerabilities. The latest above-mentioned Edgescan statistics confirm that 33% of web application vulnerabilities were exploited for SQL injection attacks. In fact, through an SQL code injection, hackers can extract credentials to access and manage the website’s content management system (CMS), download a whole database, or steal credentials.
- Explore an example of an attack on an unpatched system. Do you remember the massive data breach Facebook faced in 2018 when 50 million users were impacted due to three separate vulnerabilities that remained unpatched for more than a year? Well, as a result, the company has been slapped with a fine of $18 million by the Irish Data Protection Commission due to the violation of the European General Data Protection Regulation (GDPR). Believe me, you don’t want this to happen to your organization.
Outdated Applications and Systems
I loved Windows XP. It was easy to user-friendly, easy to use, worked well, and had a nice graphic. But, like other great things in life, I had to let it go when Microsoft announced the operating system’s end of life. Are you still using XP or some outdated software? Are you or your employees or colleagues procrastinating by postponing pushed updates as much as possible? It’s time for a change. Because that’s like rolling out the red carpet for malicious actors at your organization’s entrance.
- How do attacks to outdated applications and systems work? An employee postpones an update until later but fails to follow up. An attacker uses malware to target older versions of software to exploit vulnerabilities that have been fixed by the most recent updates. They easily manage to get into the organization’s system. From there, the attacker’s just one step away from stealing your organization’s sensitive information and user credentials.
- Explore an example of an attack exploiting an outdated application. In March 2021, Microsoft released a series of patches and updates for their 2010, 2013, 2016, and 2019 versions of Exchange to fix a vulnerability identified in January. However, it took Microsoft three months to release the updates and patches and not all affected organizations applied them immediately. As a result, the issue escalated. 30,000 organizations were affected. It was so bad that even the White House got involved, requesting IT administrators to urgently apply the updates.
Unsigned Application Downloads
Code signing has been used for years to sign executables and applications. It enables users to verify that the code really comes from where it says “on the box” and that it hasn’t been modified. Do you really want to install something of dubious origins and put your organization at risk?
- How does an attack exploiting unsigned application downloads work? Let’s take the employee example again. Say, one of your employees downloads unsigned free software from a third-party website that has been infected with keylogging malware. As the employee can’t verify if the software is genuine or if it has been modified, they install it without realizing that it’s inauthentic. The attacker uses the keylogger (do you remember when we talked about malware?) to steal the employee’s credentials and, once again, the damage is done.
- Explore an example of an attack exploiting unsigned applications. In 2017, Patrick Wardle, a cybersecurity expert who was the director of research at Synack, demonstrated in a video that hackers could steal macOS keychains using unsigned apps. And they didn’t even need root permission to do that as long as they managed to compromise the system first.
If this list of different credential theft attack techniques isn’t enough to make credential theft prevention one of the top priorities in your cybersecurity strategy, let’s add something else to the plate. Let’s have a look at the potential impact that one of these attacks could have on your organization.
What Is the Business Impact of Credential Theft?
In the previous chapters, we’ve already seen a bunch of examples of the devastating effects of a single credential theft incident. The consequences are numerous, from reputational damage to fines and lawsuits, and some may end up putting your organization out of business. Among them we find:
- Brand/reputational damages and lost trust. When talking about business, nothing is more important than your organization’s reputation and the trust of your customers. Damage your reputation and you’ll have to sweat bullets to recover customers’ trust in your brand. Take Equifax for example. Since the massive data breach it suffered in 2017, its reputation still hasn’t recovered as the settlement went on for years.
- Credential theft mitigation costs. The latest Ponemon research (as cited earlier) evaluated the average annual cost an organization has to bear to mitigate an incident to $6.6 million. That’s more than enough to put many companies out of business.
- Ransomware costs. Ransomware is a particularly nasty type of malware that an attacker could install by exploiting a system’s stolen credentials. If successful, your organization will lose access to all files and folders on the infected device(s). The hacker will then usually ask for a hefty ransom (often in the range of millions of dollars in the case of large corporations) to unlock them. (And there’s no guarantee that the attackers will follow through with decrypting your data or systems even if you do pay.)
- Lawsuits. Credential theft incidents and data breaches can also end up in lawsuits. Like the recent multiple class-action lawsuits that have been filed against MCG Health due to a data breach that affected more than 10 healthcare organizations and nearly 800,000 individuals.
- Fines due to violated privacy/security regulations. This is exactly what we mentioned before about the fine issued to Facebook due to the 2018 data breach. Do you still think this won’t happen to you? GDPR violation fines increase by 113.5% between July 2020 and July 2021. And to get a fine, you don’t even need to be a data breach target (as shown by fines listed in the GDPR enforcement tracker). You can be fined by simply being caught breaking regulations even if no breach results. A GDPR violation could cost you up to €20 million or 4% of your annual global turnover. A PCI Data Security Standard (PCI DSS) violation could be fined by credit card agencies, with costs ranging from $5,000 up to $500,000 per month.
So, what can you do to protect your organization from all this?
How Can I Prevent Credential Theft?
If you’ve read this far, you
- Know what credential theft is,
- Understand the characteristics and the vulnerabilities that could lead to an attack, and
- Are also well aware of the catastrophic impact it could have on your business.
Now, it’s time to have a brief look at what you can do to prevent credential-stealing attacks.
Use Strong, Unique Passwords (Or, Better, Passphrases)
Ensure you use strong passphrases with at least the following characteristics:
- Have a minimum of 8 characters. If you want to be really sure, aim for 12 or more.
- Combine upper and lowercase letters, symbols, and numbers.
- Aren’t used on more than one website/application.
- Are long random phrases like EgretMareBlueRodioPhone instead than traditional complex passwords consisting of a random combination of alphanumeric characters and symbols. This has also been recommended by the Federal Bureau of Investigation (FBI).
In addition, to create a really hacker-proof password make sure you follow the National Institute of Standards and Technology’s (NIST) password guidelines. This will protect your organization from:
- Automated attacks,
- Application vulnerabilities-based attacks, and
- Fines due to regulations violations.
Use Strong Cryptographic Measures
Never store plain text passwords. The best solution is to save only salted password hashes using a strong hashing algorithm (i.e., a one-way mathematical function that generates a unique string of random alphanumeric characters practically impossible to reverse). This is effective protection from:
- Automated attacks,
- Malware-based attacks,
- Application vulnerabilities-based attacks, and
- Fines due to regulations violations.
Implement Strong Authentication
Did you know that, based on a recent Microsoft’s analysis, implementing strong authentication solutions like those listed below could help you protect your organization from 99.9% of credential theft attacks?
- Multifactor authentication (MFA). Requiring the user to utilize two different ways to verify their login credentials (e.g., a password, a PIN, a QR code).
- Passwordless authentication. The user’s identity is verified without them needing to enter a password. Microsoft Azure AD has offered this option since 2021. The identity can be verified using biometrics, hardware tokens, and QR codes and relies on the same principle of digital certificates (i.e., client authentication certificates). The user relies on a public and private key pair that’s stored on the user’s device and will enable the user to access the chosen system without ever having to type a password. (Since the user doesn’t need a password, then there’s nothing for bad guys to target with credential theft attacks.)
- Transport layer security (TSL) security. Ensure that during login, all passwords are transmitted only using the secure TLS protocol using a website security certificate. You can get one from a trusted third-party certificate authority (CA).
- Alternative login protection mechanisms. If you can’t implement MFA, use alternative secondary security features like security questions, setting login rate limits, or using CAPTCHAs for each login attempt.
- Implement authentication protocols that don’t ask for passwords. Oauth and OpenId enable users to log in to multiple cooperating websites using a third-party identity provider without the need for a separate ID and password for each website.
These approaches will protect you from:
- Automated attacks (such as brute force and credential stuffing attacks),
- Application vulnerabilities-based attacks, and
- Fines due to regulations violations.
Set Verification Processes and Procedures
Sometimes, employees receive requests for sensitive customer information by email or phone. These requests often come from legitimate law enforcement agencies, senior managers or colleagues, but sometimes the requests also might come from malicious third parties. To avoid your employees just giving out sensitive or confidential information when someone asks, make sure to:
- Implement policies and verification processes. For example, require employees to always verify the person’s identity directly using other official channels, such as by calling them on an official directory phone line before giving out the information requested. Make this part of your organization’s official documented processes and procedures.
- Train your employees (and test them periodically). Everybody should be familiar with such procedures. A bit of training and some real-life examples will go a long way in helping them avoid providing information to the wrong persons. We’ll touch on this more shortly.
- Apply the concept “if you aren’t sure, don’t do it.” Never give out sensitive information if you aren’t 100% sure that it is really needed, or that the person requesting it is who they claim to be. Even the smallest doubt should be cleared with the help of colleagues or senior staff.
Follow these suggestions and you’ll be relatively safe from:
- Phishing.
- Spearphishing.
- Whaling.
Manage Your Patches
Implementing a patch management strategy with regularly planned patch days (e.g., once a month) will ensure that your systems will be always up to date and all known vulnerabilities will be promptly addressed. This is particularly useful against:
- Automated attacks,
- Malware-based attacks, and
- Application vulnerabilities-based attacks.
Monitor and Analyze Logins and Traffic
We’re not asking to spy on your users. Actively monitoring logins and traffic will definitely help you prevent unwanted data breaches. Analytic tools like Tableau and Kibana will help you identify suspicious peaks of login attempts. And if you find dodgy IPs, you can always proactively add them to your login blocklist to keep the bad guys out. These actions are good ways to prevent:
- Automated attacks, and
- Application vulnerabilities-based attacks.
Train Your Staff
Show your employees and colleagues how they can recognize phishing and suspicious emails. Promote online security best practices. Education is key to reducing the risk of attacks. Enforce strict password-changing policies as listed in the above-mentioned NIST password guidelines. Explain to them the danger of using the same password for different systems. It’ll keep your organization safe from:
- Social engineering tactics,
- Automated attacks,
- Malware-based attacks,
- Application vulnerabilities-based attacks, and
- Fines due to regulations violations.
Use a Secure Password Recovery Mechanism
I don’t know you, but I tend to forget passwords all the time. In fact, I did use a few “forgot password” services and noticed that some were better than others. One of the best ways to have a strong password recovery mechanism is to utilize URL tokens that are randomly generated using a strong encryption algorithm. This approach minimizes the risk of:
- Automated attacks, and
- Application vulnerabilities-based attacks.
Congratulations! You now know everything you need to help protect your organization from the next credential theft attack.
Final Thoughts on What Credential Theft Is – Credential Stealing Explained
No organization will ever be 100% hacker-proof. However, knowing the most common issues, understanding credential theft attack techniques, and taking some basic precautions will help you minimize the risk of a data breach.
Be proactive, monitor logins and traffic, detect and fix vulnerabilities fast and don’t forget to follow data privacy and security regulations. Because leaving a door open to attackers could have devastating consequences for your business and customers — everything from financial losses to reputational damages and loss of customers’ trust. These are just a few examples of the aftermaths of a data breach.
Now that you know your enemy and how credentials can be hacked, choose your passwords wisely and implement a good password security strategy. They’ll enable you to stay one step ahead of the attackers and effectively protect your systems and data.


![A 6-Minute Overview of the PCI DSS Requirements [For PCI DSS v.4.0]](https://cheapsslsecurity.com/blog/wp-content/uploads/2022/12/pci-dss-requirements-v4-370x245.jpg)