There are some obvious signs that alert us that the email we have received is a fake. If we pay attention to these signs, we might save ourselves from the losses and embarrassment that result from fraudulent emails
Wondering how to tell if an email is fake or real? We’ll get to that in a moment. But first, let’s consider how much email has become an indispensable part of our lives, both private or professional. Regardless of the convenience that emails offer, there are a few pitfalls we all should be concerned about. As more people connect via email, hackers are having a field day in duping them of their hard-earned wealth.
Several factors make emails particularly attractive attack vectors for cybercriminals:
- Email accounts are free or inexpensive.
- Anyone can set an email account without much knowledge.
- It’s easy to send one or more emails at once.
- Emails are extremely fast.
- You can send and receive emails using computers, tablets, and other mobile devices with an internet connection.
And if you think you are too smart to fall for an email scam, think again! History has proved time and again that even the best of us can become victims of email hustles. Sounds unbelievable? Well, that’s the truth. Companies like Sony, Google, Facebook, Upsher-Smith Laboratories, and Ubiquity Networks have become prey to email fraud scams. Millions of dollars are lost when there are attacks on large corporations. However, what people like us — individuals and small-to-midsize businesses — might lose when we get conned is our hard-earned money kept aside for a rainy day.
So, this is why it’s important that everyone knows how to tell if an email is fake or real (legitimate).
How to Tell If an Email Is Fake: 7 Ways to Detect a Phishing Email
Cybercrime units are set up almost all over the world and still, there is a constantly lingering threat over our heads. The 2019 Internet Crime Report published by FBI’s IC3 (Internet Crime Complaint Center) shows that there were 114,702 phishing attack victims reported in the year 2019 in the United States alone. These attacks caused a loss of $57.84 million to the victims during that time. Thus, it becomes important that you know how to detect a phishing email.
Let’s explore seven things you should keep in mind and look out for when trying to determine whether an email is fake or real.
1. The Sender’s Email Address Has a Generic Public Domain
Perhaps the very first giveaway of a fake email is the generic domain in the sender’s email address. Generic email domains include but are not limited to Gmail, Yahoo, Hotmail, and such. These domains are free to anyone who wants an email address. They also require minimum validation for the creation of the email address.
While having a Gmail account might not be unusual for an individual, it’s highly unusual for a business to send emails from them. Hence, people with malicious intentions are likely to use them to run scams.
You can check the sender’s email address by hovering the cursor over the display name. This will help you to check the sender’s full email address. If the sender’s address is not trustworthy, then you should not even read the email further. In case you are reading the email on your mobile device, you can check the sender’s email address by clicking on the arrow beside the recipient’s address.
If an email is from a legitimate business, it should come from an email address associated with its official domain name. Suppose you receive an email from Bank of America. This email should come from the domain bankofamerica.com. However, in a phishing attack, the domain name of the sender might be one of the public domain names like:
- [email protected]
- [email protected], or
- [email protected] (or something to that effect).
If you’re a Bank of America client, you should check the bank’s actual email address from the official documents given to you. Compare this domain with the sender’s email address in the suspicious email you received and then move forward.
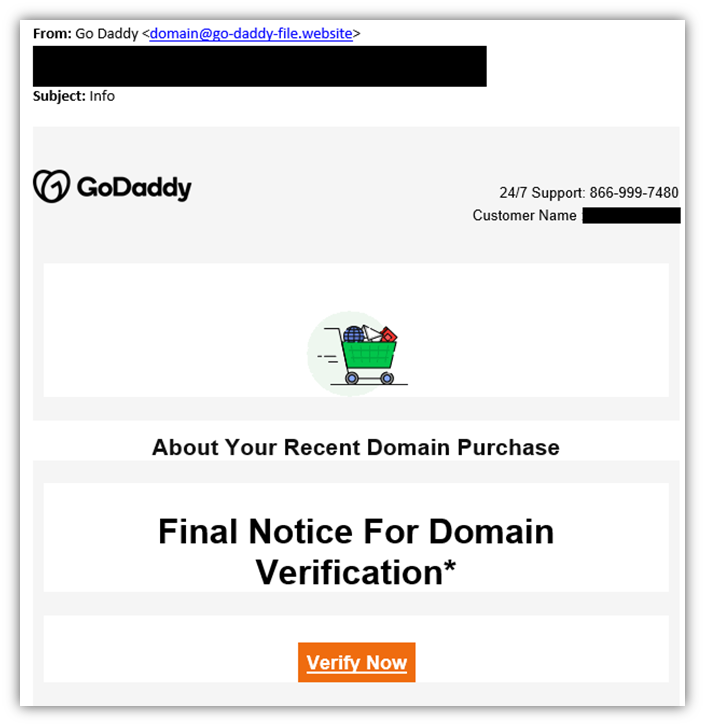
2. The Domain Name Is Completely Wrong Or Slightly Misspelled
A very common trick to manipulate the public is to use domain names with similar spellings and phishing for the information. There is another trick for phishing that uses an unrelated domain name. in this kind of email, the email body will claim to be from a different user, and the domain name will have no connection at all to this user. Let’s look at both these kinds of attacks in detail:
Misspelled Domains
In recent times, hackers have started “investing” in domain names that sound like or look like well-known companies. For example, to imitate “amazon.com” they can come up with names like “arnazon.com” or “amazons.com.” At a quick glance, the recipient of the email will not be able to tell the difference and will treat the email as official.
Secondly, the attacker might choose a display name that leads you to believe the sender’s authenticity. However, their email address is a dodgy one and that uncovers the truth. The display names are the ones you can see in the sender’s name when you first open the email. The user can choose this name. No verification of any kind is required for this display name. Hence the conman will make use of this facility to jeopardize the safety of a layman.
Notice the subtle differences in the address. A single letter change can mean that the sender is not legitimate. Our brains are programmed to skim the content rather than reading it. For instance, when I write “believe” or “beleive” you might read the same. However, it will make a huge difference when the address of the sender is concerned. So, beware of email addresses with domain names like “netfilx.com” or “whastapp.com.”
A textbook example of this kind of BEC (Business Email Compromise) happened with Barbara Corcoran, founder of the real estate brokerage firm the Corcoran Group, who is also an investor on ABC’s Shark Tank. There was an “oops” moment for her when she realized that she was being scammed out of $400,000.
Corcoran’s accountant received an email from scammers in China who were impersonating her assistant, asking the accountant to transfer the sum for a property that needed renovations. The email address of the sender was fake. It was made by leaving out one letter from the name of her assistant. As the transaction looked like an everyday transfer, the accountant did not realize the fake email address and started the wire transfer. However, he added the assistant’s real email address during the conversation about the transfer and that’s when everyone realized it was a scam.
Although no money was lost by Corcoran since the bank in New York stopped the transfer before it reached the scammers, it alerts us how a simple email can be used to con us of our money.
Crooks can even go to the lengths of replicating the logos of the companies they’re impersonating in their emails. Sometimes, these logos are nearly identical while other times the logo might have slight discrepancies. When you notice the logo isn’t the same, you should delete the email immediately. This might save you from potential fraud.
Unrelated Email Domains
Most of us are time-bound to finish the work assigned to us. Also, we often fall into the habit of multitasking, which diminishes our focus and capabilities. As a result, we are a lot less aware of little details and we fail to observe glaring errors.
Think about it: How many times do you look at the sender’s email address to confirm it’s legitimate before doing something? How many times do you read an email while paying full attention to the details instead of just skimming? Have you ever replied mechanically to an email about a staff survey or other surveys or other stuff that does not matter much in your opinion? You might have already realized your mistakes by now.
Look at the figure below. It is a screenshot of an email received about an employee survey. The interesting part about the routine employee survey here is the address of the sender that is highlighted. The employees who received this email have never worked for something called the “Texas Guitar Showcase.” This clearly has nothing to do with their company or an HR-type role. Had they not checked the address of the sender, they would have been easily phished.
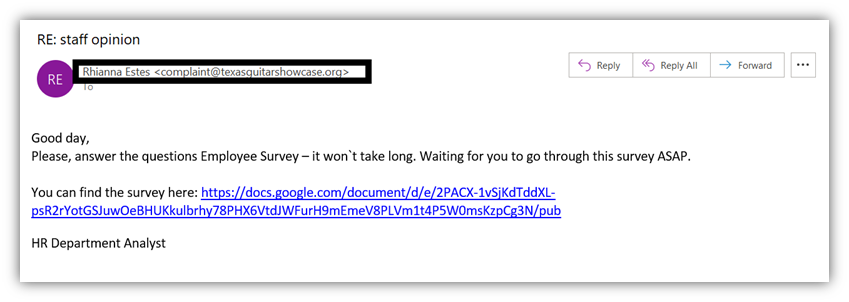
If you see that the sender’s domain doesn’t match the company it claims to be from, that should throw up a big red flag. In this case, why would TexasGuitarShowcase.org send an email about an employee survey? It just doesn’t make sense from a logical standpoint.
3. The Email Is Poorly Written in Terms of Grammar and Spelling
At the risk of sounding politically incorrect, many attackers who carry out phishing scams are either from non-English speaking communities or are not very educated. Moreover, even if they use a spell-checker, their grammar will still be dubious. This is especially evident whether they try to imitate large corporations — emails from these types of companies will never be written in a sloppy manner.
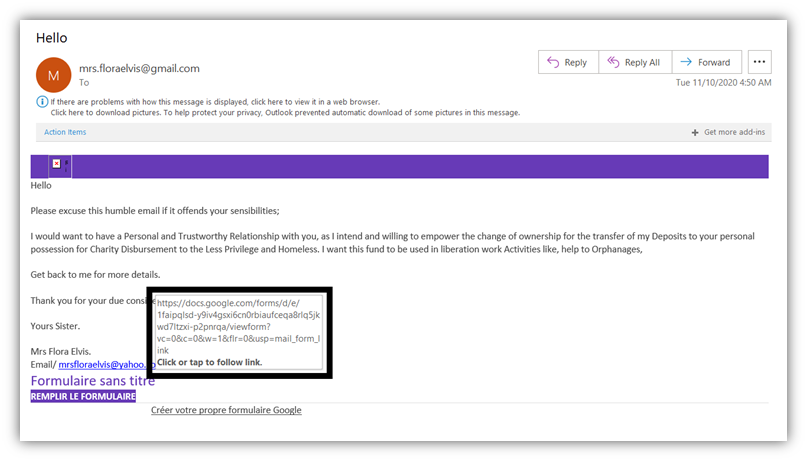
If you read the text in the email below, it is evident that the email is not written by someone fluent in English. The words used in the email seem fancy but the grammar is downright awful. The sentences do not form clear meaning. The whole text is mere mumbo-jumbo trying to lure a person into revealing their personal or financial details.
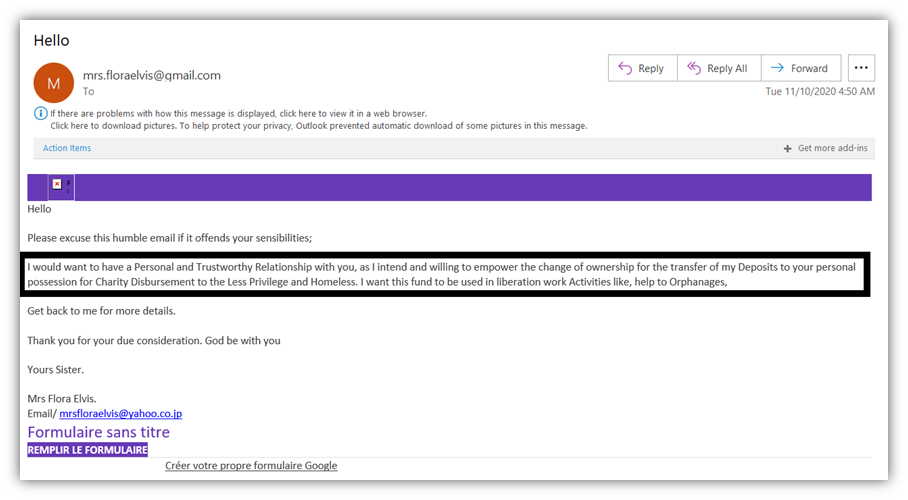
If you’re a fan of the TV show Friends, you’ll likely remember Joey looking up every word in a thesaurus to write a reference letter for his friends. He managed to use the most difficult word replacements for the letter he had previously written in order to sound knowledgeable. If you do not know the episode, then let me quickly explain. The person who does not know the language will try to Google the words they’re looking for and often will choose words without any context to the content. Scammers will also do something like this. They will try to sound well informed but, in reality, they are far from it.
Although everyone makes spelling errors from time to time, when an email is written poorly as a whole, you should not trust the sender. A simple, old-fashioned phone call will help you to clear your doubts.
4. The Tone of the Email Is Urgent and Requires You to Act Swiftly
If you receive an email from your colleague explaining that he’s stuck somewhere and urgently needs some money to get out of a situation, think twice. Ask yourselves a few questions:
- Does his story check out? Ask yourself from a logical standpoint if his message or request makes sense.
- Is he that close to you? Do you share a relationship where it would make sense for him to contact you in this situation instead of a family member or friend?
- Wouldn’t they call instead of sending you an email? If he needs your help immediately, wouldn’t he call instead of sending an email you might not receive or see for hours?
When you take time and think instead of just responding emotionally, you will see right through the racket. The scammer might know somethings about you, but not everything.
Learn to think through your response and not just react. It’s not only the Zen way to live but the right way, too. When you get emails that demand immediate action, think logically before taking a step. Some emails will say you need to pay a specific amount of money or else they’ll cancel your membership or will charge you high penalties. Respond to these types of emails with a cool head. Is this the email address that you had given as your contact email? Is this how the sender normally communicates with you, or is it abnormal to send an email like this?
Most of the official emails will never ask you to pay any overdue sum in a rushed manner. They will give you some time to make the payments. So, be careful before transferring the amount in a rushed manner.
5. The Attachments or Links Are Dubious
Attachments and links are not only used for phishing but also for infecting your system with malware. When you click on the link sent to you, you’re risking the security of your computer as well as that of every device linked to the network your computer connects to.
The purpose of the phishing email with attachments is to gain access to your personal or financial information. These types of information can include:
- Login credentials,
- Social security number or another identifying number,
- Credit card details,
- Bank account numbers, and
- Phone numbers.
One way in which this is done is by asking you to click on the link. When you do, you’ll be taken to a page that says you’re logged out and need to log in again to continue. This will help the hacker to register your details from the fake login page.
Some hackers take this kind of scam a step further. They call first and let you know that you should expect an email containing, say, an overdue invoice from them. Then, once you receive the email and open the attachment called “Invoice,” it will be too late. You’ve opened a malicious file and now the attacker will be in your system, creating havoc.
Apart from checking the email address and the things we mentioned above, there is something else you can do: check the link they have sent you and see whether the URL matches the context of the email. For example, let’s consider the phishing link in the email below. You’ll notice that when I hover my mouse over the purple embedded link text near the bottom of the email, it displays a link to an unknown Google Doc file. If you don’t know this sender and they’re sending you an unsolicited link, beware!
The figure below shows that the email is asking me to click on the link. However, when I hover my cursor on the link, you can see that the link would take us to the sender’s Google drive. It is not an actual site.
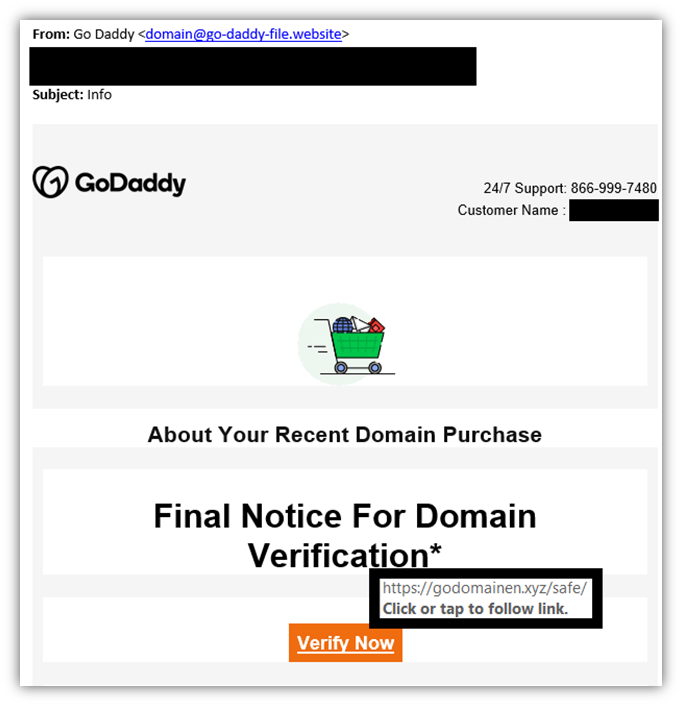
The same goes with businesses that you do know or regularly work with. Check to make sure that any email links are legitimate as well as the domain that the message is coming from before engaging with them. In the following example, the embedded link is clearly not going to take you to a legitimate website.
6. The Email Promises Financial Windfall or Grave Penalties
There are no free lunches in this world. The people who win the lottery and other prizes are extremely rare. So, if the email you received informs you that you have just won a contest that you have no memory of participating in, it’s a fake email.
There are countless phishing and other financial scams whose victims are ex-pats and immigrants. Many governments have issued official notifications and warnings against such scams. The scammer will impersonate the country’s Home Ministry or government and ask for money or information from the person. The person is most likely to give in at once as they do not want to leave the country of their residence and go back to their homeland.
In recent times, when the entire world is affected by the pandemic, the COVID-19 has given way to another type of scam. In COVID-19-related scams, cybercriminals often pretend to be:
- Affected by the pandemic,
- Working for the people who are affected by it, or
- Working in emergency response and relief organizations or at official government agencies.
They ask for financial help and donations with the hope that you’ll have a good heart and want to help those affected by the situation. However, if you donate, you’re actually paying the criminal instead. Fake charities are, unfortunately, a symptom of this dark time when we all should be helping each other fight this global illness
7. Your Gut Instincts Tell You the Email Is Fake
When something doesn’t seem right, trust your instincts. They are generally right. You might not have figured it out, but your subconscious mind might already know that what you’re seeing is not right or seems “off” in some way.
An example can be when you receive an email from your boss at an odd hour asking you to make immediate payment to somebody. If your boss has a habit of doing this often, you might think of going ahead after making a phone call to him. However, if your boss is behaving weirdly, he might not really be the one who sent you the email. If you cannot confirm it with him personally, it’s best not to do anything until you do. Truth is, as the saying goes, it’s better to be safe than sorry.
Putting It Together: How to Tell if An Email is Real
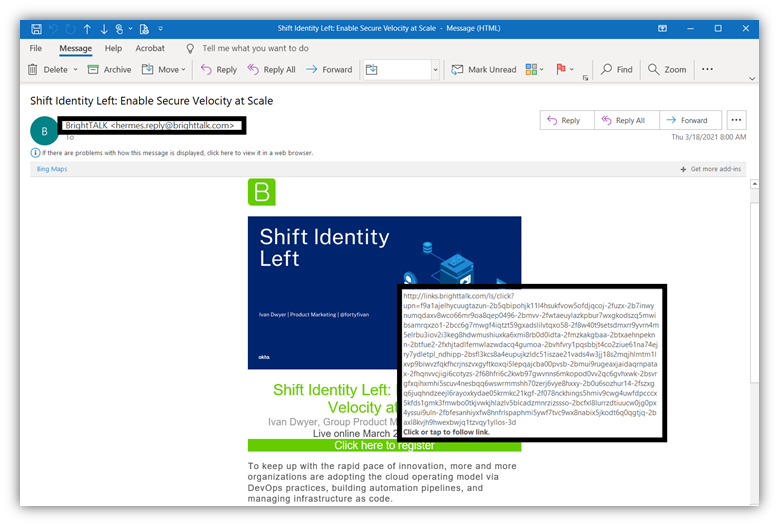
Okay, now that we’ve covered all that. Let’s take a quick look at an email of a real (legitimate) email from a company. Let’s consider this email from BrightTALK:
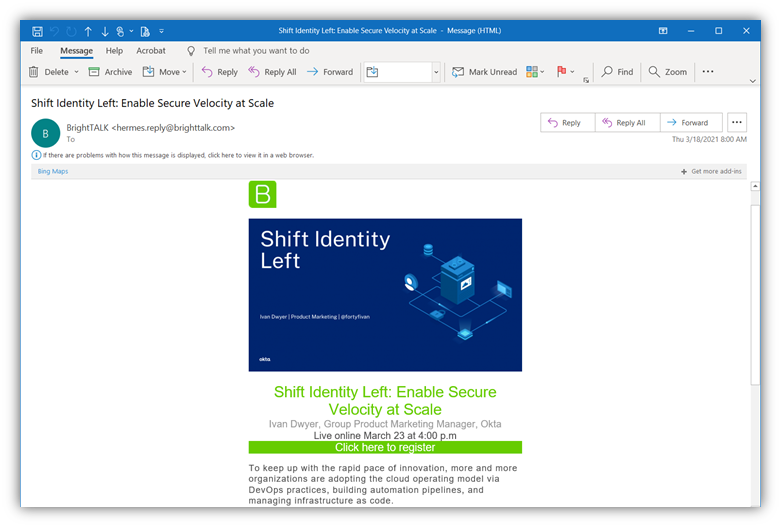
In this example, we can see that the sender’s email address comes from the company’s legitimate domain. That’s a good sign. Next, we can also see that the “Click here to register now” link will take us to a legitimate URL on the domain brighttalk.com.
Now, ask yourself the following questions:
- Did you sign up to receive emails from the sender?
- Does the sender use correct grammar, spelling, punctuation, etc.?
- Does the message make sense?
- Is the email written to convey a sense or urgency or to get you to do something immediately?
- Is there anything that seems “off” or not right about the email?
If your responses to these questions add up in a good way, then it’s likely that this is a real email and not a fake.
Educate Your Employees & Colleagues on Cyber Awareness & Security Best Practices
You are as strong as your weakest link. At the end of the day, if one of your employees or coworkers fall victim to phishing tactics, your organization will end up paying for it one way or another. Therefore, it’s better to train them professionally to deal with such crime attempts ahead of time — an knowing how to tell if an email is real or fake is an important part of that process.
Many agencies help you train your employees, and these training programs will help your organization be more secure. Or, you can choose to have your in-house IT team offer training on how to tell if an email is fake or real.
Final Words on How to Tell If an Email is Fake or Real
As we saw in the examples above, a single email can make a normally secure environment vulnerable. It can lead to financial losses as well as damage the reputation and goodwill of the company in the eyes of customers and investors.
Cybercriminals are coming up with innovative ways to entice people to divulge important personal information. As such, we must verify all the details of an email sender before taking any concrete action, such as a transfer of funds or sharing personal details. Therefore, knowing how to tell if an email is fake or real is crucial. And taking the time to confirm these details face to face or over the phone is a good way to protect yourself from phishing, malware, and other cybersecurity risks.