Identify and Prevent the Rising Force of Phishing Attacks
When we think of hackers and cyber criminals, we tend to think of them as masterminds wearing hoodies, shutting down websites with their out-of-this-world coding skills (and godly swagger of course!). Well, that’s not always the case. Using a simple yet highly impactful technique like Email Phishing, any Tom, Dick, or Harry can fool users to commit online fraud. You don’t need to learn a dozen coding languages to employ phishing scams and take control of systems. A huge part of the reason that phishing is so popular is its lack of sophistication.
What is Phishing?
You may not understand the term ‘Phishing’, but chances are, you would at least have heard of it. The thing about Phishing is that you may have fallen its victim without even realizing it. Basically, it is a con trick. In the email phishing method, the perpetrators send malicious links, viruses, malware, and detrimental files via fake messages, popups etc. The emails often impersonate well-known entity—a large company or, in the case of spear-phishing, a boss or C-level executive. These emails often show lucrative offers, lotteries, discounts or they may act like an urgent action needs to be taken in the form of a password change or an email confirmation. On clicking the mischievous link, the user is redirected to a malicious website which can ultimately lead to disasters.
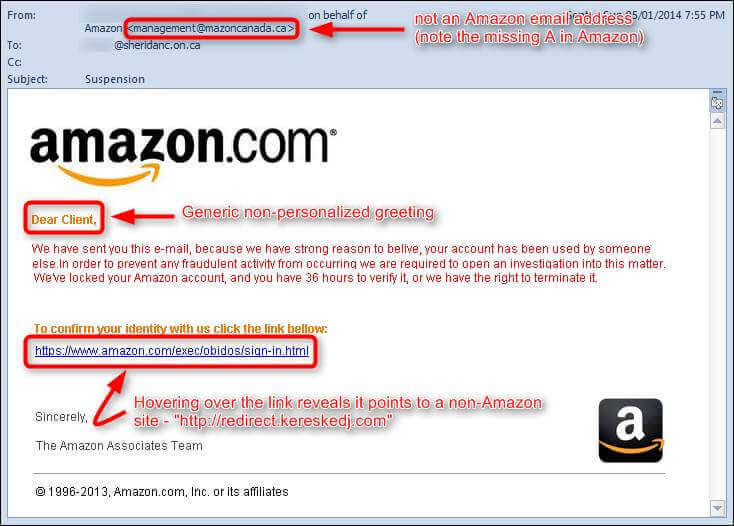
An example of such email phishing has been demonstrated in the image below. Here, it looks as if the email has been sent by Amazon, but it hasn’t been. If a user misses the tiny details pointed out and clicks it, they are now at the mercy of their attackers.
Phishing Statistics
From a cyber criminal’s point of view, phishing works like a charm. As a result, they have started widening their phishing net as much as possible. There has been a rampant rise in the number of phishing scams worldwide. Let’s have a look at the numbers involved.
- Around 85% of Organizations fall prey to Phishing attacks.
- Almost 30% of phishing emails are opened by the users.
- Email attachments are the number one medium to deliver malware.
- The average cost of a spear-phishing attack is $1.6 million.
- One in every three companies has reported being the victim of CEO fraud emails (also known as whaling).
- 2016 saw a record number of phishing attacks.
- A report conducted by IBM reported a 6000% rise in Ransomware-infected files.
How to spot a Phishing email?
If identifying phishing emails was an easy task, there wouldn’t be so many victims. Unfortunately, it isn’t. However, that doesn’t mean that you need Sherlock Holmes’s deduction skills to figure it out. Granted, these tricksters are pretty good at the art of conning. Nonetheless, if you pay a little attention, you can avoid being the next victim. To help you identify malicious emails, look for the following signs:
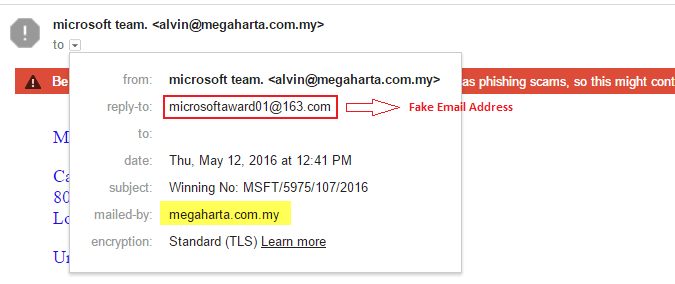
1. Fake Email ID
Cyber criminals send emails that attempt to make you believe that they are from a legitimate, trusted organization. These messages may even include an original logo along with accurate headers and footers. However, it comes with a catch. The fraudsters may use the original logo, proper images, and a thousand other things, but they cannot use the official email address of the company. That would be extremely difficult to accomplish. This is where you can identify the threat and slam the door in these imposters’ faces.
Next time you receive an email, make sure you check the email ID of the sender. Here’s an example:
 2. Grammatical Errors
2. Grammatical Errors
We know that you are probably not a stickler for grammar, well, neither are the perpetrators behind fraud emails. More often than not, these emails are comprised of some really silly grammatical mistakes. Spotting these mistakes is not rocket science by any means.
Spot them, dodge them!
3. No HTTPS
Reputed organizations such as PayPal must employ a secure connection between the client and the server to carry out transactions (in PayPal’s case it’s actually a matter of PCI compliance). An SSL certificate must be installed on its website. If a fraud email has been sent to you, most of the time the redirected website won’t have HTTPS as the prefix in the URL. That’s a dead giveaway.
4. No images or logos
Most of the times, phishing emails are written in HTML. As a result, these emails are found in text format only. They don’t have any logos or images whatsoever.
5. Unrealistic offers/discounts
The word phishing has its roots in the word fishing. How do you catch a fish? You give it a bait, right? Well, this is exactly what cyber criminals do. If you see an offer or a scheme that is too good to be true, it probably is.
Don’t fall for it. IT’S-A TRAP!
Tips to protect against phishing scams
No matter how much attention we pay, sometimes we might miss a tiny detail. This can be enough to shut down your entire organization’s systems (no pressure, right?). Therefore, it is always recommended to have a fool-proof plan in place. Here are our tips to steer clear of phishing scams.
1. Improve your computer security
Whether you want to guard against phishing attacks or ransomware attacks or any other attack for that matter, improving your computer security should be on top of the list. This can be executed by deploying a firewall, anti-virus, spam filters, anti-spyware etc.
2. Keep your system up-to-date
The updates exist for a reason—improvement. The developers keep rolling out updates every other day to remove the bugs and vulnerabilities present in past versions. So, keep updating all software including your operating system (OS).
3. Stay away from Popups
- DO NOT click on the links given in a popup.
- DO NOT share any of your personal information in a popup.
In short, don’t do anything on the popup. Stay Away!!
4. Keep checking your bank account statement
In order to prevent any thefts, keep checking your bank account on a regular basis to ensure that there aren’t any unauthorized, illegitimate transactions.
5. Enter your personal information in HTTPS-enabled website only
You may be aware of the fact that there are two communication protocols —HTTP and HTTPS. The ‘S’ in HTTPS stands for Security. Therefore, any data you enter, any transaction you make is safeguarded by means of an SSL certificate.
6. Avoid clicking on links from emails
This is one of the most widely used technique to fool the users and making them fall into the trap. Even if you receive a mail saying that a person wants to be friends with you on a social media platform, don’t click on the link. Instead, go to the social media site manually.
7. Avoid entering personal information via public networks
When you are connected to a public network, you are at the highest point of vulnerability. Even 12-year old Billy could creep into your device after watching a couple videos on YouTube and downloading an app. You certainly don’t want that, do you?
8. Report a phishing scam ASAP
If you are able to figure out a phishing scam, report it straight away. Ignorance is certainly not an option here. Where do you report it? First of all, report it to your email service provider. The service provider will stop the phishing emails from circulating. You should also report to the organization being targeted. For example, if you receive a spoof email from Amazon, then you should report it to Amazon.
Final Words
What do you do when you are in front of a con artist? You pay attention. All they want is to sidetrack us and gain the advantage of that single moment of distraction. Don’t worry. Be aware, take the preventive measures and you should be fine.

 2. Grammatical Errors
2. Grammatical Errors