TLS 1.3 is here, and we’re in safe hands
TLS 1.3, the latest and unsurprisingly the most advanced cryptographic protocol till date, has finally been approved by the IETF (Internet Engineering Task Force). Soon, TLS 1.3 will be adopted by all leading browsers and will soon become a reality from the theoretical concept it is. Needless to say, TLS 1.3 brings a host of improvements over TLS 1.2, the current occupant of the SSL/TLS family.
When it comes to browsing the internet, two things matter above else. These things are security and speed. TLS 1.3, with its faster handshake and security advancements, excels at both. It sheds away the insecure skin of TLS 1.2 and its predecessors and offers a quicker, secure way to communicate in the precarious world of internet.
Let’s first have a look at the improvement brought by TLS 1.3 when it comes to security.
Why TLS 1.3 is more secure
TLS 1.2, with all its benefits and successful serving tenure, has its pitfalls. These pitfalls come in the form of insecure protocols, ciphers, and algorithms. Don’t jump to the conclusion that TLS 1.2 is broken. It’s definitely not broken. However, these downfalls *might* get exploited even if there’s a very slim possibility of it. TLS 1.3 eliminates such possibility as it doesn’t consist of such obsolete components.
Here are some of the ciphers and protocols of its predecessors abandoned by TLS 1.3:
- DES
- 3DES
- MD5 Algorithm
- RSA Key Transport
- SHA-1 Hash Function
- RC4 Steam Cipher
- CBC Mode Ciphers
- Various Diffie-Hellman groups
- EXPORT-strength ciphers
Less traveling = More speed
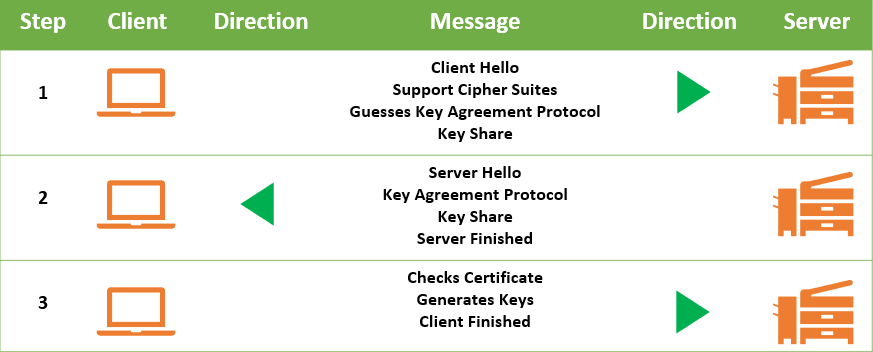
For a TLS-enabled secure connection to take place, a process named ‘TLS handshake’ must take place between the client and the server. This handshake involves a series of back-and-forth communication and verification steps between both entities. During these steps, they come to terms of data transfer and pave the way for encrypted communication. As good as this sounds, it comes with a constraint – speed.
The TLS 1.2 handshake incorporates two round-trips of communication between server and client. As a result, it takes a bit more time to perform the handshake and establish a secure connection. To give you a number, it takes around 0.25 to 0.5 seconds for it. This may not look like a lot on paper, but it can make some serious difference in reality as the data transfer takes place after the handshake.
With TLS 1.3, we’re about to see a radical change in the handshake time. TLS 1.3 introduces 1-RTT handshake that cuts the handshake time by almost half. In areas where even a microsecond can make a world of a difference, this is nothing less than a boon.
As good as the 1-RTT handshake is, it’s 0-RTT Resumption that has stolen the thunder from it. Yes, a handshake consisting of zero round-trips! If the server and client have come across each other before, the handshake will be of zero round-trips. 0-RTT Resumption is accomplished by using the stored information such as session IDs. This takes the handshake time down to the bottom. This way unprecedented connection speed will be achieved with the introduction of TLS 1.3.
TLS 1.3 Browser Support
TLS 1.3 supports all modern browsers and devices. It includes the major browsers like;
- Google Chrome
- Firefox
- Internet Explorer
- Safari
Concluding Thoughts
There’s no doubt about the fact that the internet will be a better place when TLS 1.3 arrives. Thankfully, it’s been passed by IETF, and it’s become a question of ‘when’ instead of ‘if.’ Keep following our blog to keep your pulse on TLS 1.3 and all significant changes happening within the SSL industry. Sayonara!
Resources
- Convert a Certificate to PEM: CRT to PEM, CER to PEM, DER to PEM
- Difference between SSL & TLS
- 3 Ways to Bolster Your SSL/TLS Security
- TLS 1.3 is now active in Firefox
- Enable TLS 1.3 in Chrome and Firefox
Buy Comodo SSL Certificates
As we’ve got to know that the TLS 1.3 is the most reliable, secure and speedy solution to keep the website information secured. Encrypt a website in a few minutes.
Buy SSL Certificates at $4.97