Is your organization still supporting insecure TLS protocol versions? That’s a bad idea when more than 85% of attacks in 2022 were found to use encrypted connections. Discover everything you need to know about the different TLS versions and which ones you should use to take your business’s data security to new heights
Did you know that the first kind of data breach ever recorded goes back to 1834 when the Blanc brothers stole confidential financial market data by exploiting the telegraph line? 189 years later, 34% of the cybersecurity professionals interviewed by WithSecure still consider preventing data breaches their top concern.
And they aren’t the only ones. On Jan. 6, 2023, the Federal Communication Commission (FCC) released the new Data Breach Reporting Requirements (NPRM) for telecommunication carriers. The document proposes several substantial changes to their customer data regulation in the event of a data breach.
The transport layer security (TLS) is “the” cryptographic protocol that provides internet communication security. Want to know more about it to learn the basics and use it at its full potential? Read on to discover:
- What TLS is and why it’s important.
- What different TLS versions are available, their supported algorithms, and their characteristics.
- Any vulnerabilities that exist with the different TLS protocol versions.
What Is TLS?
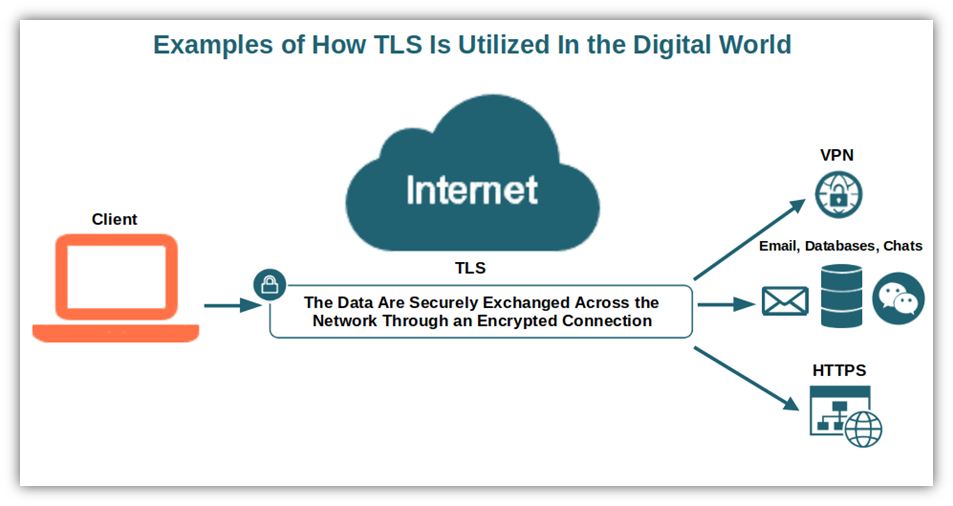
TLS, or transport layer security, is a cryptographic protocol (i.e., a set of rules that enables secure communication) that major websites use to protect data as it transmits from users’ browsers to their servers. TLS provides three important functions:
- Authentication (so users know they’re communicating with the legitimate party),
- Data integrity check (so users know data hasn’t been modified since it was sent), and
- Encryption (so users’ data are secured and only authorized users can read it).
The goal of TLS is to protect communications across the network so that the transmitted message remains private and unaltered, and so that you know it was sent by the legitimate entity.
How Does TLS Work?
Let’s put it simply, just to give you an idea without going too techy. To summarize:
- Before establishing the connection, the client checks the server’s TLS certificate (more on this in a minute).
- Then the asymmetric key pair (public and private keys) are verified between the client and the server (handshake).
- If the verification is successful, a symmetric session key will be exchanged to allow encryption and decryption of the transmitted data.
Where Is Transport Layer Security Used?
Have you ever noticed the small padlock icon in the browser’s address bar? That’s an indicator that the website you’re visiting is using TLS to establish an encrypted connection. In fact, the TLS protocol can be used to protect:
- Data and file transfers (e.g., HTTPS, which is TLS on top of the traditional hypertext transport protocol).
- Emails (e.g., simple mail transfer protocol – SMTP and internet message access protocol – IMAP).
- Instant messaging (e.g., the extensible messaging and presence protocol – XMPP – the old Jabber for those old enough [like me] to remember it).
- Video and audio-conferencing services.
- Virtual private network (VPN), where the encryption and authentication features are used to create a quasi-tunnel connecting hosts and networks.
By the way, did you know that according to the latest Gigamon TLS Trend research report, 19% of the traffic going in and out of organizations’ networks isn’t encrypted at all? And that the percentage of unencrypted internal data transmission is even higher, reaching an astonishing 35%?
What TLS Is Not
But let’s go back to our TLS protocol. One day, I was reviewing an FAQ document about TLS that was supposed to be published on our internal website. I immediately noticed that the author was using TLS and secure socket layer (SSL) as interchangeable terms. This is a common misunderstanding, but it isn’t the only one.
- TLS isn’t the same as SSL. Why? First of all, SSL is the TLS ancestor and is now deprecated (i.e., not recommended). Moreover, even if they practically do the same thing, at the technical level they’re pretty different protocols. For example, they establish connections differently (i.e., SSL uses explicit connection where the client requests SSL encryption while TLS uses implicit, where the connection is automatically encrypted from the beginning). The algorithms used (i.e., cipher suites) during the handshake are also different as TLS uses more secure ones.
- A TLS certificate isn’t TLS. Confused? Let me clarify it for you. Despite the term “TLS” often being used to describe TLS certificates (i.e., domain validation [DV], organization validation [OV], and extended validation [EV] digital certificates), they’re actually two separate (but related) things. A TLS certificate is a digital file that enables you to encrypt HTTP traffic using TLS, while TLS is the actual protocol.
- It doesn’t secure data on end systems. Want to keep the data residing on a client or a server secure? You’ll need to opt for something else because TLS can’t help you with that. Why? Because, as we’ve just seen, it’s a protocol that can only secure your data while in transit.
Want to dive more into the technical side of things? If you want a more in-depth look at the TLS protocol, be sure to check out this great video from Computerphile:
Otherwise, now that you’ve got a high-level overview of the TLS protocol, let’s move on and explore the different TLS versions.
Discover the Different TLS Protocol Versions
After the first version of TLS (v.1.0) came to light in 1999, three subsequent versions were released. Version 1.0 and 1.1 were officially deprecated in March 2021 (i.e., no longer recommended) by the Internet Engineering Task Force (IETF) after it was discovered that they had several critical vulnerabilities (more on that later).
Let’s have a look at all of them one by one. Hint: check out our summary table for a quick overview of their features. Interested in more details? Read on.
| TLS Protocol Version | TLS Version Characteristics | Deprecated or In Use? |
| TLS Version 1.0 | – Based on SSL 3.0. – The connection can be downgraded to SSL 3.0. Supported by 33% of sites. – Supports only old and deprecated algorithms. | Deprecated. |
| TLS Version 1.1 | – Released in 2008. – Supports authenticated encryption ciphers. – Accepted by 35.9% of sites (according to SSL Labs). – Can only use deprecated and insecure algorithms like MD5 and SHA-1. | Deprecated. |
| TLS Version 1.2 | – Uses more secure algorithms like SHA-256. – Enables the server to ultimate select the cipher from among those supported by both parties. – This version isn’t vulnerable to the previously mentioned attacks. – Supports authenticated encryption with extra data modes. – Allows the utilization of advanced cipher suites. Required by the National Institute of Standards and Technology (NIST) for all government TLS servers and clients. Its full handshake has two round trips of communication. | In use (supported by 99.9% of the websites). |
| TLS Version 1.3 | – Constitutes the most recent and secure TLS protocol version. – Mandates perfect forward secrecy (PFS), which involves generating a unique session key for every user to protects keys from being used to decrypt past or future sessions’ data. – Uses only simple and stronger cipher suites that have no vulnerabilities. – Replaces the RSA key exchange process with the ephemeral Diffie-Hellman. – Merges encryption and authentication into a single roundtrip. – Uses a smaller set of simplified cipher suites. Involves a faster (and shorter) handshake. – Requires digital signatures, always. | In use (supported by 59.8% of the websites), although many haven’t implemented it as the default protocol. |
The Deprecated TLS Versions (And Why You Shouldn’t Use Them)
These are the oldest TLS versions: v1.0 and v1.1.
1. TLS Version 1.0
It’s the Macintosh 128k of TLS — the first and original one. It’s based on SSL 3.0, but at the same time, it’s different when you look at it under the hood. TLS 1.0 is the result of negotiations between Netscape (the creator of the SSL protocol), Microsoft, and IETF. TLS version 1.0:
- Allows the connection to be downgraded to SSL 3.0 without changing the protocol, if necessary.
- 33% of sites surveyed by SSL Labs were still supporting it (January 2023).
- Supports only old and deprecated algorithms like MD5 and SHA-1.
2. TLS Version 1.1
Released in 2008 and documented in the RFC-4346, this enhanced TLS version has the following characteristics:
- Supports authenticated encryption ciphers (i.e., a form of encryption ensuring at the same time authentication and confidentiality of data).
- Is supported by 35.9% of sites surveyed by SSL Labs (as of January 2023).
- Like its predecessor, it supports only old and deprecated algorithms like MD5 and SHA-1.
Why Were Both Early TLS Versions Deprecated?
TLS isn’t like wine; unfortunately, it doesn’t improve with age. TLS is more like humans: the older they get, the more vulnerable they become. And for TLS v.1.0 and v.1.1, their vulnerability to attacks was the driving force behind their deprecation that put an end to their cycle.
Over the years, the two TLS protocol versions were victims of several attacks that capitalized on their vulnerabilities. Among them:
- BEAST. Similar to man-in-the-middle attacks. The cybercriminal decrypts the contents of a TLS-encrypted session between a browser and a website. Often used to steal sensitive information like HTTPS authentication cookies, it exploits vulnerabilities in block-based cipher suites.
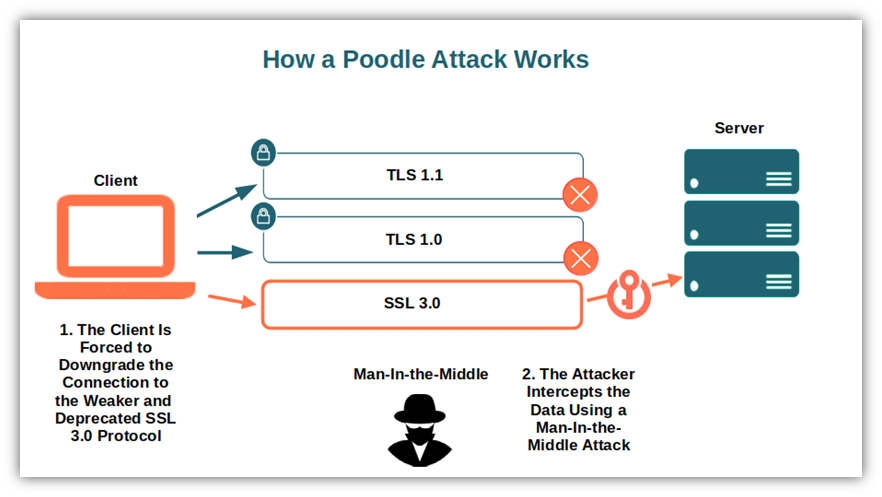
- POODLE. The padding Oracle on downgraded legacy encryption (POODLE) was announced as a security flaw by the U.S. Computer Emergency Readiness Team (US-CERT) in 2014. It allows the attacker to snoop on information exchanged between a client and server acting (once again) as man-in-the-middle after having forced the TLS connection to downgrade to the more vulnerable SSL 3.0 protocol.
- ROBOT. This old attack exploits a vulnerability in RSA encryption. During the RSA handshake between a client and a server, the attacker sends a series of client key exchange messages with incorrect padding. Based on the server’s responses, they can determine if the server is vulnerable. If it is, they can record traffic and then decrypt and access the information or data later using the server’s private key.
- SWEET 32. Exploiting vulnerabilities in the previously mentioned block-cipher algorithms (e.g., data encryption standard [DES] and triple-DES), the attacker uses JavaScript to bombard the server with millions of requests creating a collision (i.e., two cipher blocks with the same key). He can then easily decrypt and access the information.
- LUCKY 13. Probably the most complex of the whole lot mentioned here, it’s similar to the padding Oracle attack. The attacker relies on the different processing times between TLS messages (e.g., two bytes of padding are processed faster than one-byte padding). With OpenSSL, the attacker can recover the full transmitted plaintext.
I guess these are more than enough reasons to justify the deprecation of these two TLS versions, don’t you think? So, what about the latest TLS versions that are still in use and haven’t been deprecated? This is what we’re going to discover next.
The Latest TLS Versions in Use
TLS 1.2 and TLS 1.3 are the latest addition to the TSL family. Both offers improved security, performance, and reliability over their predecessors. Let’s explore their key characteristics in more detail.
3. TLS Version 1.2
Based on TLS 1.1, TLS 1.2 was released by the IETF in 2008 with the RFC-5246. To date, it’s the most commonly used TLS protocol version. It’s supported by 99.9% of the websites analyzed by SSL Labs (as of January 2023). Yup. It’s basically used by everyone, and it should be the minimum version utilized. Its most important features?
- The old and insecure algorithms MD5 and SHA-1 used in the previous versions have been replaced by the more secure SHA-256.
- The cipher used is ultimately selected by the server among those supported by both parties.
- This version isn’t vulnerable to the previously mentioned attacks.
- Supports authenticated encryption with extra data modes.
- Allows the utilization of advanced cipher suites supporting elliptic curve cryptography, an alternative to RSA, offering the same level of security with a smaller key size. This is often used in combination with the advanced encryption standard (AES) encryption that was announced in 2001 by the Federal Information Processing Standards Publications (FIPS).
- TLS 1.2 is required by the National Institute of Standards and Technology (NIST) for all government TLS servers and clients.
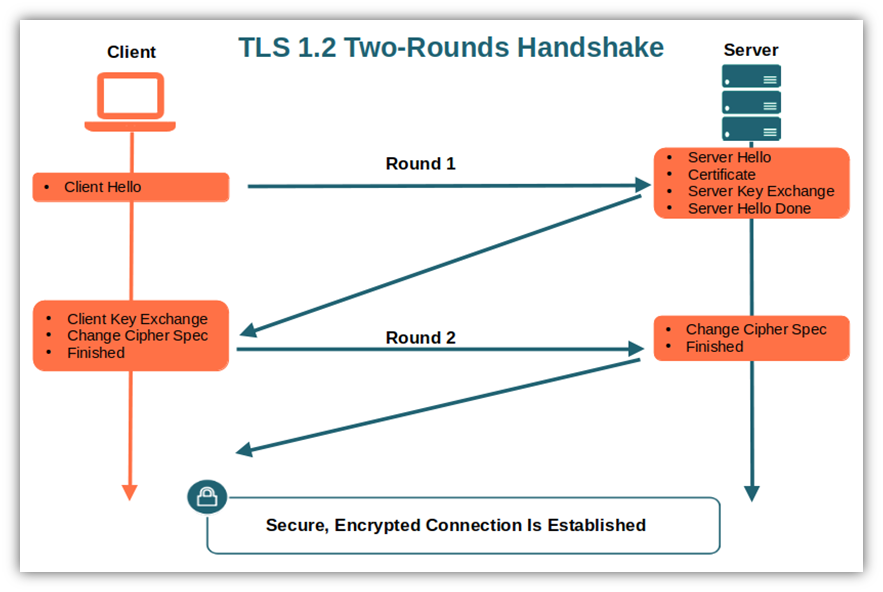
- Its full handshake has a total of two roundtrips of communication, making it a bit slower compared to the latest TLS version 1.3 (more on that in a minute).
Speaking of benefits… by implementing TLS 1.2, you’ll kill more than two birds with a stone. Why? It’ll help you get compliant with geographic and industry standards such as:
- The EU General Data Protection Regulation (GDPR),
- The Health Insurance Portability and Accountability Act (HIPAA) and,
- The Payment Card Industry Data Security Standard (PCI-DSS).
Be careful, though, as TLS 1.2 is considered a secure protocol only if you remove old algorithms and ciphers! Don’t forget it during your implementation. Want to know more about it? Don’t miss our next article where we’ll take a closer look at this popular protocol.
4. TLS Version 1.3
This is the most recent TLS protocol version. Launched in 2018 with RFC-8446, it offers the highest security possible, in part because it mandates the perfect forward secrecy (PFS). With this system, unique session keys are generated for every user session and are discarded at the end of the session.
What this does is help to prevent old session keys from being used to decrypt data from old sessions (or future sessions since the same session keys won’t be reused and shouldn’t be stored). This is the reason why this encryption system is also used by Google and Apple.
Why is it so secure? Because even if your most recent key is stolen, the damage will be limited as the compromised key has only been used for one communication session. It’s the perfect way to limit the damage of SSL/TLS bugs like Heartbleed, which was discovered in 2014.
But there’s more. TLS 1.3:
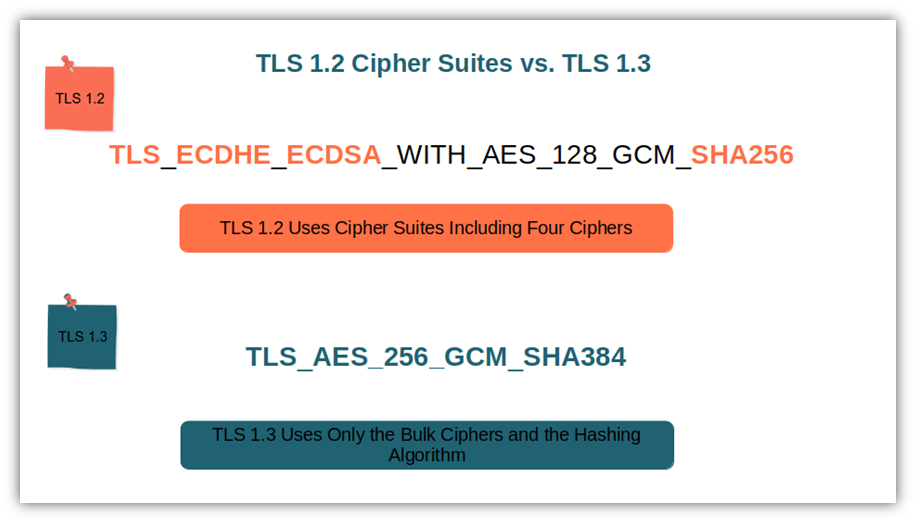
- Eliminates support of old and weak algorithms and cipher suites. That’s right — no more MD5, SHA-1, RSA key exchange, and RC4 cipher (just to name a few). The latest TLS version uses only simple and stronger cipher suites that have no known vulnerabilities.
- Replaces the RSA key exchange process with the ephemeral Diffie-Hellman. One of the biggest attractions of TLS 1.3 is the concept of perfect forward secrecy. To enable PFS, the client and the server must generate a new shared key for every session using unique parameters. Doing this helps to prevent past or future sessions from being compromised (except, of course, for the one that uses the single compromised key).
Learn more about Diffie-Hellman and PFS in the following Computerphile short video:
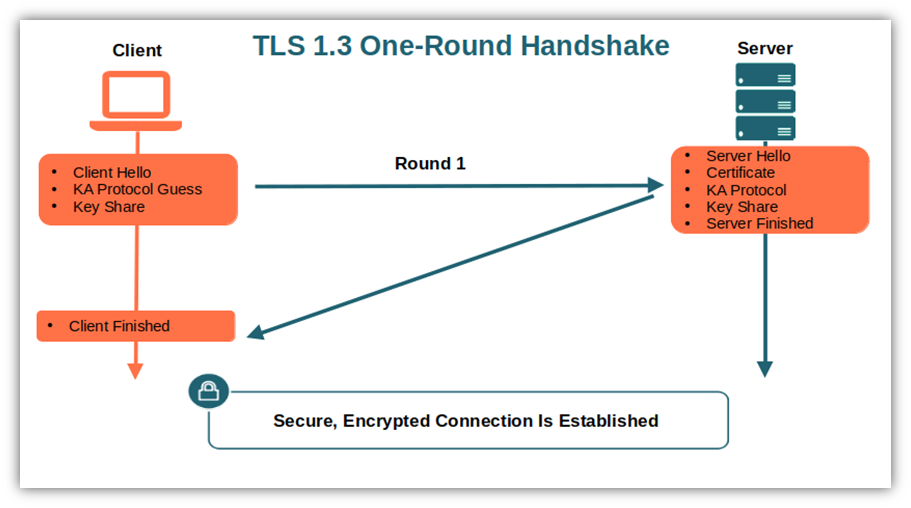
- Merges encryption and authentication into one single step. This reduces the number of negotiations between the client and the server, making everything faster. In practice, the server sends the shared cryptographic key right after the first connection attempt request.
- Uses a smaller set of simplified cipher suites. All previous TLS versions included multiple ciphers (see the example in the graphic below). In TLS 1.3, the key exchange and the signature algorithm are eliminated. Moreover, the number of possible combinations has been reduced to five. Less is more when it comes to choices of cryptographic ciphers.
- Has a faster (and shorter) handshake than its predecessor. This is, in part, because the number of negotiations has been reduced, resulting in a single roundtrip instead of multiple roundtrips.
- Requires the server to cryptographically sign the whole handshake. This makes downgrading attacks (e.g., POODLE) impossible as the attackers are unable to modify any parameters.
So, if TLS 1.3 is the most secure TSL protocol version, how comes it’s only supported by 59.8% of the sites (as of January 2023, so far) even if it works with the latest versions of all major browsers? Well, first of all, we all know that it takes time to adopt new standards, above all when many organizations are still using legacy (i.e., outdated) software and if you take into account that TLS 1.2 is still considered “secure enough” for many uses.
Just to give you an example, I remember taking my friends to a hotel recently and seeing the receptionist typing on an old Windows XP computer. Yup! Even if its support ended in 2014, some people are still using it nearly 10 years later. (According to statistics, in December 2022, Windows XP was still used by 0.49% of Windows users). See how long it can take for popular software to be fully replaced?
Another reason is also that, sometimes it could be a double sword. How? Let’s take PFS. It’s great for security as the TLS sessions are nearly impossible to decrypt without the proper key. No doubt about that. On the other hand, PFS makes TLS sessions impenetrable not only to the attackers but also to security teams and organizations trying to intercept malware and malicious attacks during data transmission. Some tools can help, of course, but teams will have to adapt.
Having said that, even if it will take time to reach TLS 1.2 adoption numbers, TLS 1.3 remains the more secure, light, and fast TLS version actually available. So, the question to ask is: are you willing to trade some of the convenience offered by TLS 1.2 (e.g., easier to monitor for malware) to gain greater security? I would.
By the way, do you know what version(s) of your systems use or support? No? We’ve already put together a TLS checker resource that will walk you through how to check the TLS version of a website uses and supports. It’s easy and it takes only a couple of minutes.
Final Thoughts on TLS Versions: What They Are and Which Ones Are Still Supported
TLS is one of the most reliable tools to help you address the most critical data transmission security issues:
- Ensures that the person you’re communicating with really is who they claim to be.
- Makes sure that the transmitted data haven’t been altered in transit.
- Shields your data from prying eyes during transmission.
Want to boost the security of your internet communications between web browsers and applications with TLS?
- Follow the most common standards from NIST, IETF, FIPS. Keeping your data as secure as possible will also help you stay compliant with any industry and regional regulations such as:
- European Union’s General Data Protection Regulation (GDPR),
- Health Insurance Portability and Accountability Act (HIPAA), and
- Payment Card Industry Data Security Standards (PCI-DSS).
- Migrate to TLS version 1.2 as a minimum if you haven’t done it yet.
- Disable the deprecated TLS versions 1.0 and 1.1. Most major browsers have already deprecated them. You’ll no longer be vulnerable to attacks like BEAST and POODLE.
Last but not least, now that you know the basics of TLS, don’t miss our next article dedicated to the most widely supported TLS version: 1.2. Learn where it’s used, why it’s important for data security, and much more. Next, on this blog!





