SHA2 is now officially available, but it’s also official – SHA-1 Certificates are no longer issued.
So, if you purchase any certificate from Comodo, DigiCert, Thawte, or any other Certificate Authority, expect it to come with SHA-2, and not SHA-1.
Tech giants including Microsoft, Google, and Mozilla are all aboard with SHA-2. In fact, all sites with SHA-1 Certificates have been receiving warnings on Chrome calling for an upgrade to SHA-2.
But what is SHA 2?
For those who don’t know yet, SHA is an abbreviation for Secure Hash Algorithm, which is a group of cryptographic hash functions developed by the US National Security Agency (NSA).
SHA hash functions are used by Certificate Authorities when signing Certificate Revocation Lists and Digital Certificates. A Secure Hash Algorithm is meant to generate unique hash values from files.
Between 2011 and 2015, SHA-1 was the primary algorithm used by SSL Certificates. But that has since been upgraded to SHA-2, which contains six hash functions of different levels (224, 256, 384, 512, 512/224, 512/256).
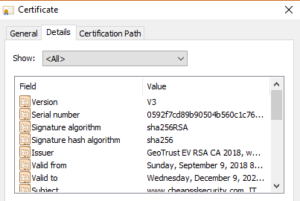
From the image above, this site uses SHA-256, which is the most popular hash function. It is usually referred to as SHA-2 since people tend to focus more on the bit length; SHA-1 is a 160-bit hash, while SHA-2 is a 256-bit hash.
With the basics out of the way, let’s understand the importance of transitioning from SHA-1 to SHA-2.
Buy Cheap Wildcard SSL Certificates with SHA2 Enabled
Why Upgrade to SHA2?
In 2011 the CA/Browser Forum (a group of Certificate Authorities and a few popular web browsers) decided to put in place basic operating guidelines for SSL Certificates. The set requirements advocated for an upgrade from SHA-1 to SHA-2.
The involved stakeholders found serious security weaknesses with SHA-1 that rendered most users’ information vulnerable. So, what exactly necessitated the upgrade?
SHA-1 Vulnerabilities
If you were in the internet business back in the 90s, then you know too well how ubiquitous SHA-1 was when it came to the signing of Digital Certificates. In fact, 98% of Digital Certificates issued up until 2013 relied entirely on SHA-1.
But in the last few years, increasingly powerful cryptographical attacks have continued to cast doubts in the minds of many – for this reason, experts believed that it was time to cut the losses for everyone and move on to a more advanced hashing algorithm, SHA-2.
Unlike SHA-1 which was found to be susceptible to collision attacks, SHA-2 is collision-resistant. Additionally, SHA-2 is a more powerful security algorithm that can match up to the high-tech computers being produced today.
Google and Microsoft Disapprove SHA-1
By 2017, Google Chrome started phasing out SHA-1 certificates. But in the real sense, the process began back in 2014 when they made public their SHA-1 depreciation policy as follows:
- Chrome 39 would display an error message on the address bar for any SHA-1 Certificate expiring on or after January 1st, 2017.
- Chrome 40 would show an error message on the address bar for sites with certificates expiring on or before January 1st, 2017. Such websites were treated as neutral and lacking security.
- Chrome 41, on the other hand, would display an ‘insecure’ message on sites using SHA-1 Certificates beginning January 1st, 2017.
The depreciation notices went on until January 2019 when all Google Chromes released ceased operating for sites with SHA-1 Certificates.
And just like Google, Microsoft wasn’t left behind.
The tech giant allowed Digital Certificate companies to issues SHA-1 Certificates until the start of 2016 – once the period elapsed, sites were required to install SHA-2 Certificates.
Next, let’s delve into some key aspects of SHA-2 SSL Certificates that are important to take note of.
SHA-2 SSL Certificate Compatibility
SHA 2 Compatible Servers
If you plan on installing a SHA 2 Certificate, make sure that you’re using it on a compatible server. Below is a list of the compatible servers:
| Apache Server | 2.0.63+ w/ OpenSSL 0.9.8o+ |
| Citrix Receiver | Varies (FIPS 140 & SHA2 Line) |
| IBM Domino Server | SHA2 Not Supported |
| IBM HTTP Server | 8.5 (Bundled with Domino 9) |
| Java-based products | Java 1.4.2+ |
| Mozilla | NSS Based Products 3.8+ |
| OpenSSL based products | OpenSSL 0.9.8o+ |
| Oracle WebLogic | 10.3.1+ |
SHA 2 Compatible Browsers
| Chrome | 26+ |
| Firefox | 1.5+ |
| Internet Explorer | 6+ (With XP SP3+) |
| Konqueror | 3.5.6+ |
| Mozilla | 1.4+ |
| Netscape | 7.1+ |
| Opera | 9.0+ |
| Safari | 3+(Ships with OS X 10.5) |
Which SSL Certificates are SHA-2?
All SSL certificates sold on our website use SHA-2.
Buy SSL Certificates at Only $4.97
Related Resources
- Convert a Certificate to PEM: CRT to PEM, CER to PEM, DER to PEM
- Guide for the “SSL Certificate Problem: Unable to get Local Issuer Certificate”
- SSL_Error_rx_record_too_long – The Trouble Shooting Guide
- ERR_CONNECTION_REFUSED in Chrome – Fixing Guide by SSLSecurity
- Explained: Hashing vs. Encryption
- Your Connection is not Private Error – A Fixing Guide for all devices
- Decoded: Examples of How Hashing Algorithms Work
- Explained: Hashing vs. Encryption vs. Encoding
- Digital Signature vs. Digital Certificate: The Difference Explained