46% of organizations interviewed by PwC were victims of fraud activities in 2021. Don’t give a chance to business identity thieves! Get a crash course in organization impersonation protection. Discover the ultimate tactics to minimize your vulnerabilities and maximize your defenses
$5.8 billion. This is how much consumers and organizations lost in 2021 due to identity theft, according to the latest Federal Trade Commission (FTC) data. This marks a shocking 70% increase compared to the previous year. And with business information available to anyone owning a computer, business identity theft is becoming a hot topic. The FTC has even proposed a new rule to fight government and business impersonation scams.
Why? Because corporate ID theft is much more lucrative (and dangerous) than personal ID theft. Companies have higher credit limits, big bucks in their bank accounts, and they often make large payments (so some fraudulent transactions might go unnoticed among the legitimate ones). They also have trusted brand names and reputations that they can capitalize on to sucker other companies — and everyday John and Jane Does — into handing over sensitive personal and financial information (such as credit card numbers).
Your business is unique, much like its corporate identity and brand. Don’t put your organization’s reputation or success at risk. Here are nine cutting-edge ways you protect your company against business identity theft. Get to know the what, why, and how of corporate identity theft. Be prepared. Don’t let your business become the latest addition to the FTC’s business identity theft statistics.
Business Identity Theft Definition
Business identity theft is the act of impersonating an organization for fraudulent activities. In 2021, we saw a massive instance of this happen when 1.2 million small business owners’ business IDs were stolen and used by cybercriminals to apply for loans managed by the Small Business Administration (SBA).
How did they do it? Organizations are full of useful, sensitive information like;
- Tax numbers,
- Bank account numbers and details,
- Employment identification numbers,
- Employees’ or CEOs’ names.
And when even just one single piece of information can be used for several fraudulent activities, like the ones listed below, the game becomes even easier.
- Website defacement or hijacking. Where the attacker completely alters the appearance of a website or modifies information such as contact details, payment-related URLs, just to name some. It’s a bit like when walls are messed up by graffiti. Even worse, the attacker creates a phony website that look like yours to attract the victims via typosquatting (i.e., using a mistyped version of your name or URL) or hijacking attacks.
- Trademark ransom. When your brand name or logo is stolen and registered as an official trademark. The cybercriminal will ask you for a ransom for releasing it.
- Financial and tax fraud. When hackers request and obtain a loan or a credit card using your organization’s name (financial fraud) or submit fraudulent tax returns using your organization’s name to get government refunds (tax fraud).
How does it all happen? This is what we’re going to find out next.
How Does Business Identity Theft Happen?
Cybercriminals can be very creative in finding ways to get hold of organizations’ information. They don’t even need to make a lot of effort. Often the information they’re after is already available in a mailbox or online. Among the most used tactics, we can find:
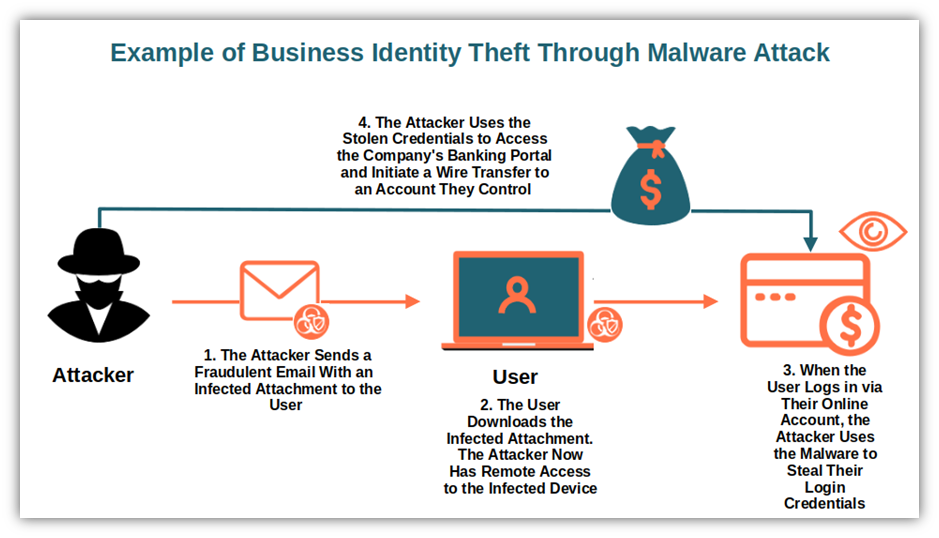
- Spyware and malware. Hackers infect an organization’s device(s) with malware to get hold of information, such as a finance department’s employee’s account credentials. The attackers use the credentials to initiate wire transfers to their foreign bank accounts. Fraudulent wire transfers have been plaguing many U.S. businesses in 2021. In fact, the FBI’s Internet Crime Complaint Center (ICR3) report showed total losses reaching more than $115 million.
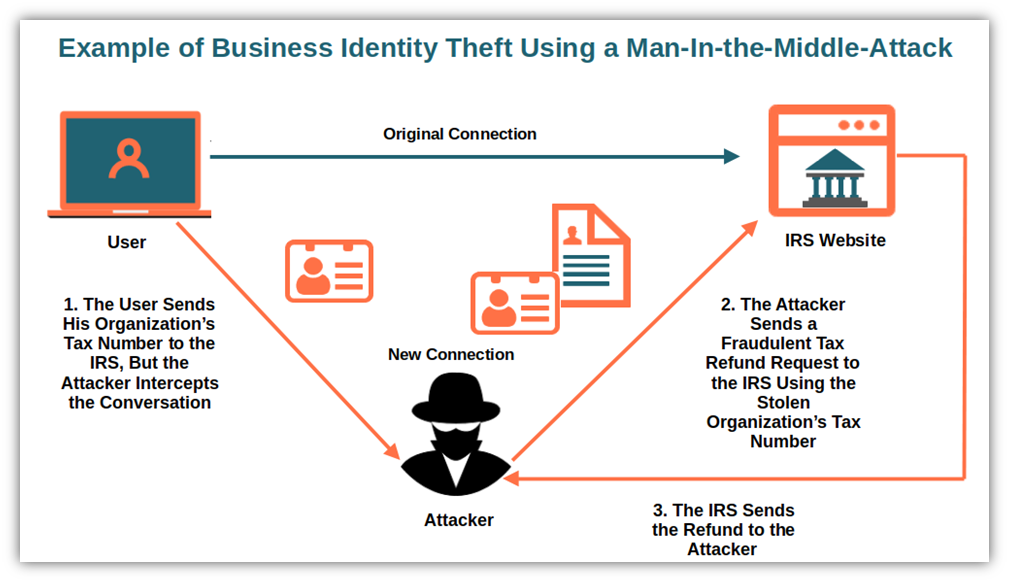
- Man-in-the-middle attack. The attackers intercept a conversation or data transfer (e.g., credentials, bank account numbers, IRS numbers) between two parties in transit, which enables them to observe and steal info from the parties without their knowledge. This way, the attacker can manipulate the sending party’s data before it moves on to the receiving party. This method was used by a cybercriminal group that managed to steal €6 million from medium and large European companies just by monitoring payment requests.
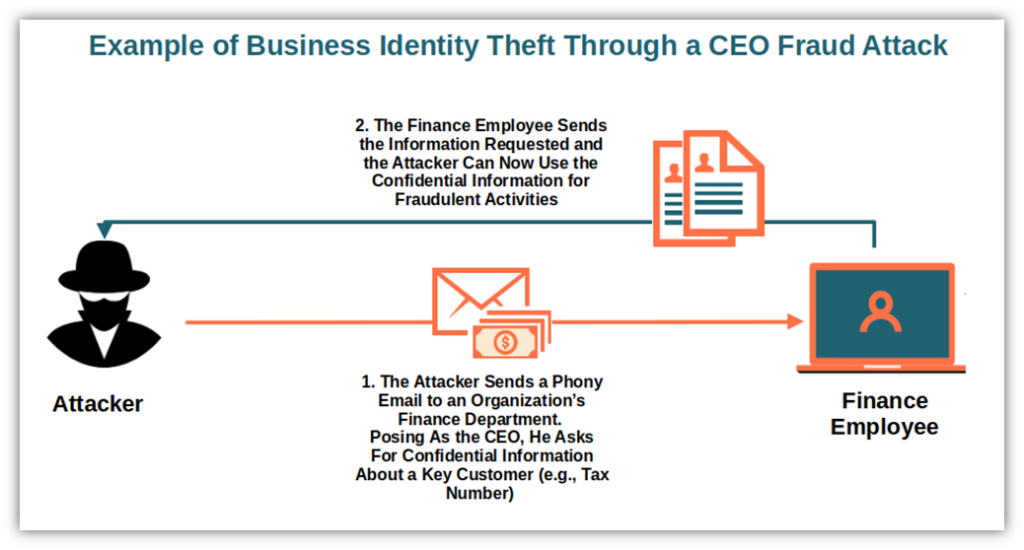
- Social engineering. In other words, by manipulating an individual (e.g., an employee) to reveal specific confidential information that the cybercriminal can then use for fraudulent activities. The attacker could use an email or a phone call to pose as a government agency or a CEO (a specific social engineering attack called CEO fraud). They’ll then push the victim to share the sensitive information they’re after. Cisco had a taste of this type of attack in May 2022 and, boy, it was a bitter experience. The analysis went on for months until September 2022, when Cisco confirmed having implemented a series of remediations.
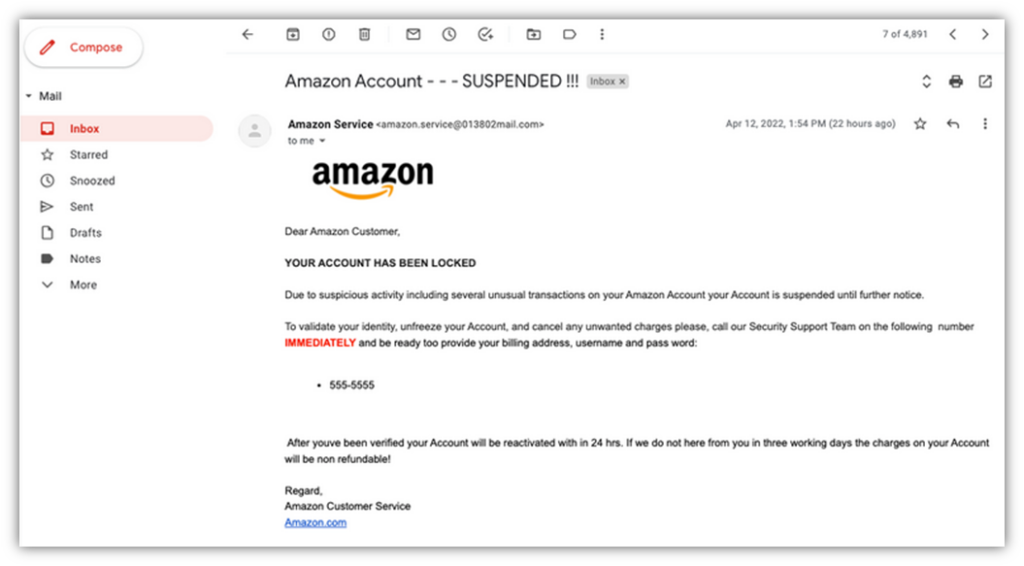
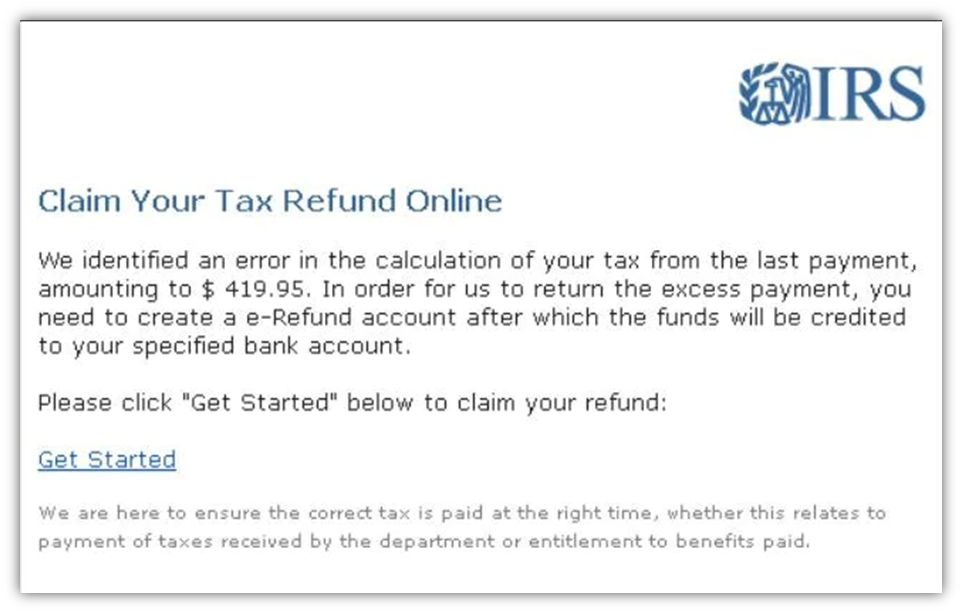
Other examples of social engineering can be phishing emails like the ones in the screenshots below. Once again, the attacker exploits fear or a sense of urgency to push the recipient to share sensitive information.
And this is just a peek behind the curtains that reveals some of the deception and techniques that enable cybercriminals to prey on organizations’ business IDs.
Time to fight back now! Let’s learn some tricks that’ll avoid your company from falling into the shadows of corporate identity theft.
10 Tips to Protect Your Business From Corporate Identity Theft
42% of U.S. small businesses have been victims of identity theft or at least one data breach. How can you protect your organization against these scenarios?
| Business Identity Theft Tips | Business Identity Theft Tips Examples |
| 1. Protect Your IT Systems | Set up a firewall. Restrict access to your network, systems and other IT resources. Use a virtual private network (VPN). Monitor and report suspicious activities. Install updates. |
| 2. Implement Sophisticated Multi-Factor Authentication (MFA) | Location-based MFA. Adaptive MFA authentication. |
| 3. Shield Your Passwords | Use strong passwords. Store password hashes only. Use a password manager. |
| 4. Facilitate Your Identity’s Verification and Confirmation | Sign your emails. Sign your files and codes. Prove your users your website is legit and encrypt your data transfer. |
| 5. Secure Your Website and Data | Back up your website and data regularly. Scan your website for malware. Keep your software and devices up to date. |
| 6. Keep Close Tabs on Who Uses Your Accounts (and Their Activities) | Regularly review your bank and credit card statements for fraudulent activity. Implement a strong access control system. |
| 7. Register Your Trademark | Trademark your name and logo in all states and/or countries where you operate. |
| 8. Display Your Trademarked Logo In Your Customers’ Inboxes | Adopt brand indicators for message identification (BIMI). Add a verified mark certificate (VMC). |
| 9. Ensure Compliance With Privacy and Security Regulations | Be compliant with: The EU General Data Protection Regulation (GDPR), The California Consumer Privacy Act (CCPA), The Payment Card Industry Data Security Standard (PCI DSS), and The EU Payment Service Directive (PSD2). |
| 10. Educate Your Employees | Show them some free videos. Get your employees certified. Use free and paid online courses and resources available on the internet. |
1. Protect Your IT Systems
143%. So high was the increase of Windows business device threats identified by Malwarebytes in 2021. Don’t be easy prey — take the following steps to protect your organization’s devices and network:
- Install antivirus software. Having a strong, updated antivirus and anti-spyware software installed on all devices (including mobile ones) can do wonders in keeping malware and spyware at bay.
- Set up a firewall. Put up a barrier between your organization’s network and attackers. Firewalls help you filter malicious content and activity flowing to and from your network. You don’t know which one to choose? Check out some independent reviews for enterprise firewalls or for small business ones.
- Restrict access to your network, systems, and other IT resources. Do you have a kind of open-door policy where everyone can access everything and do anything? Time to draw some boundaries. Document and manage who (and what) should have access to what and how. Apply the principle of the least privilege to users and devices so that they have only access to the resources they need. Want to be even more rigorous with critical resources? Implement a deny-by-default policy.
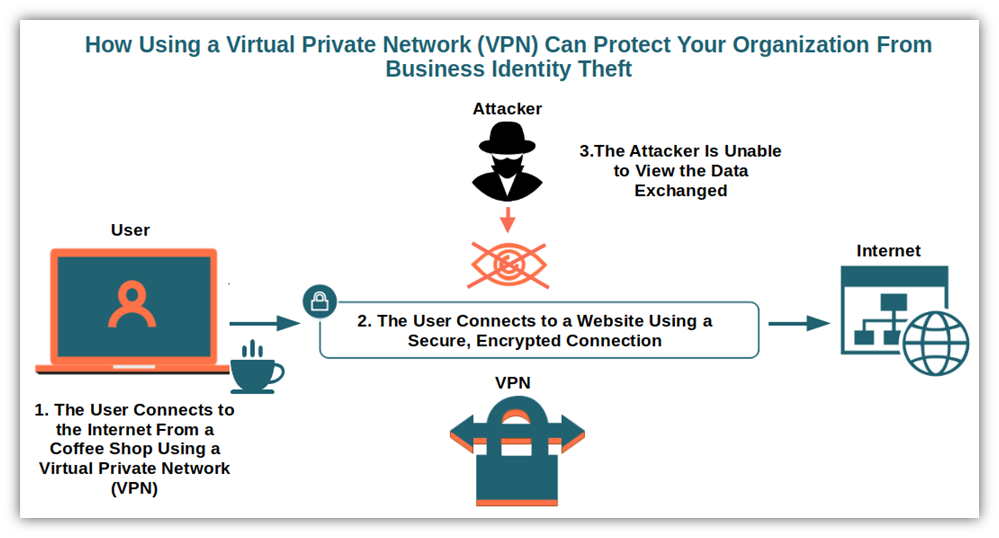
- Use a virtual private network (VPN). Add another layer of security to your network by giving remote employees access to internal applications and data through a VPN. This internet security service creates an encrypted connection tunneling between devices and servers.
- Monitor and report suspicious activities. Monitor everything from your organization’s credit report and account statements to suspicious login traffic and activities. On top of using general security monitoring software to help you spot anomalies in your system, you may also want to add identity theft software. Many offer several services, including alerts, dark web monitoring, credit report tracking, and more.
- Install updates. Update your software regularly and often, including open source components and third-party libraries. Create a software bill of materials (SBOM). This list of all components included in your applications will help you ensure you don’t forget to update vulnerable third-party modules. This helps to prevent malicious code injections and cross-site scripting attacks associated with those vulnerabilities.
2. Implement Sophisticated Multi-Factor Authentication (MFA)
ForgeRock reports that two billion credentials were compromised in 2021. This stat means that nearly half of all records breached in that year included login credentials. You aren’t worried because your organization is using two-factor authentication everywhere? Unfortunately, the latest Uber cyberattack showed that isn’t enough anymore.
For enhanced protection, enforce a refined version of multi-factor authentication such as:
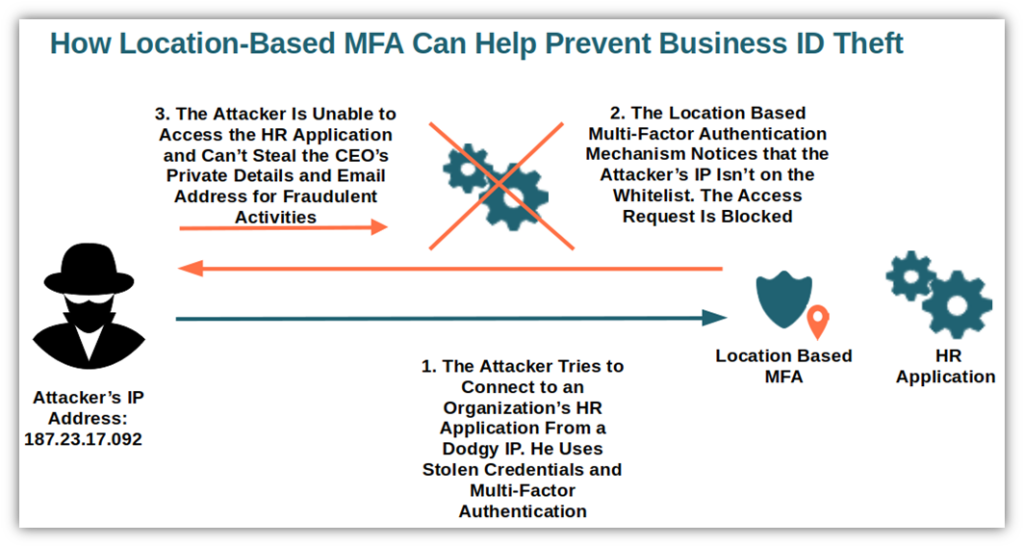
- Location-based MFA. If the IP address of the user requesting access doesn’t match a list of allowed (i.e., whitelisted) IPs, it’ll enable you to block them or require an additional form of authentication (e.g., answer a secret question, or enter a one-time PIN).
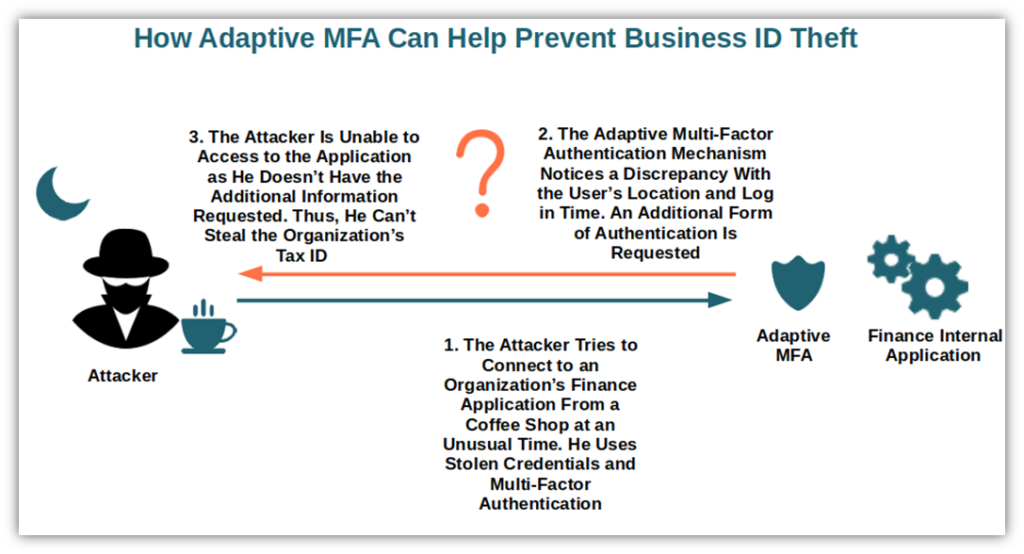
Adaptive MFA authentication. Also called MFA risk-based authentication, this method analyzes specific risk factors based on behavior and context (e.g., the time of log in, the type of network) before allowing access to a resource or prompting the user for an additional form of authentication.
3. Shield Your Passwords
Even with multi-factor authentication, your users will still have to use a password. And if those passwords are too weak or badly managed (e.g., saved as plain text), you’ll be at risk of credential theft. Therefore, it’s paramount that you:
- Use strong passwords. Use hard-to-guess, complex, long passwords (e.g., at least eight characters, including a mix of numbers, special characters, and lowercase and uppercase letters). Say no to commonly used, default, or compromised passwords. We know you love your pet, but it isn’t a good idea to use its name as a password.
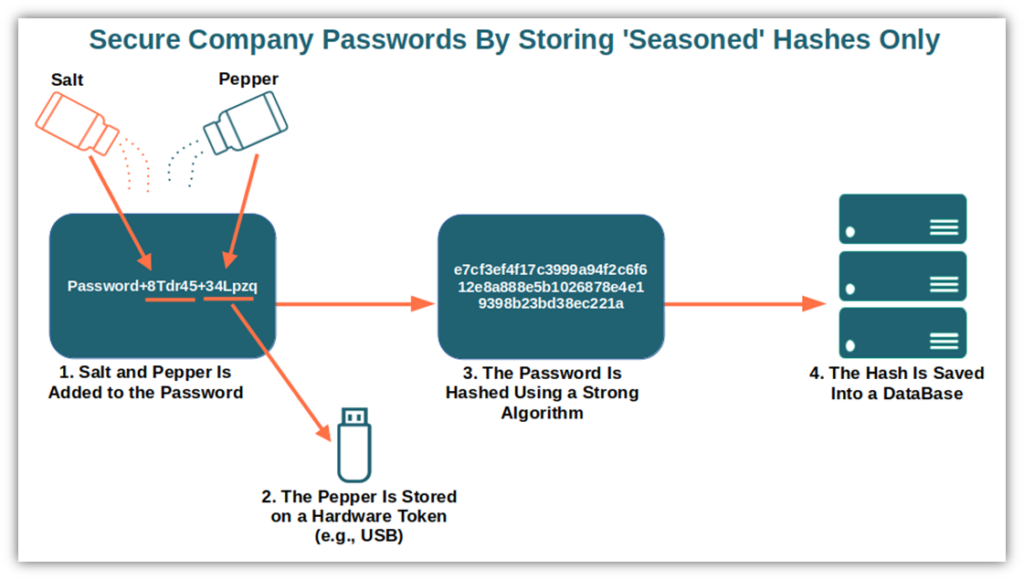
- Store password hashes only. Everybody makes mistakes. Even Facebook admitted that it once stored millions of passwords as plain text. You don’t want your organization to be the next on the news? Only save password hashes (an output of random characters of a fixed length that can’t be reversed) instead of plain text passwords. Oh, don’t forget to:
- Use a strong hashing algorithm. Follow the National Institute of Standards and Technology (NIST)’s digital identity guidelines.
- Salt it. Add a unique, random string to the password during the hashing process.
- Add some pepper. Add another random string of characters to the hash that you store on a hardware security module (HSM), like a USB token as suggested by OWASP, to add an additional layer of security.
- Use a password manager. How many times do your users forget their passwords or write them on pieces of paper? Everyone has done this at least once. Help them avoid this bad practice with a password manager. It’ll also store their passwords in a secure, encrypted password vault.
4. Facilitate Your Digital Identity’s Verification and Confirmation
Do you remember when we talked about CEO fraud? Wouldn’t it be great if the targeted victims could have a way to confirm that the emails received were really coming from your organization’s CEO? Or, perhaps, you want to have a way to confirm to recipients that your files or code are legitimate… but how do you do this?
- Sign your outbound emails. Assert your identity by signing your emails with a digital certificate. It’ll also enable you to encrypt your emails with a public key and reassure your recipient that the message hasn’t been altered.
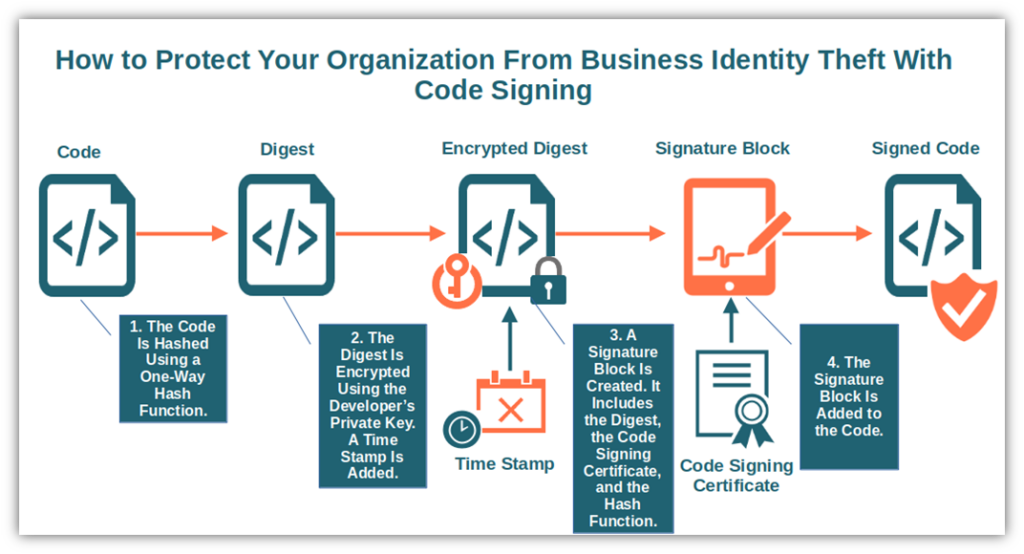
- Sign your files and codes. In 2022 AV-Test has identified an average of 3.7 new malware and potentially unwanted applications (PUA) per second. Confirm to your employees and customers that your software is virus free and it’s really coming from you. Sign all your executables, files, and codes with a code signing certificate.
- Prove your users your website is legit and encrypt your data transfers. Adding a secure socket layer/transport layer (SSL/TLS) security certificate to your website will let your users and customers verify that they’re connecting to your legitimate site. It’ll also let you encrypt all communication and file transfers by redirecting all your traffic through the more secure port 443. Isn’t it cool? You’ll hit two birds with one stone while shielding your organization from those dreaded man-in-the-middle attacks.
5. Secure Your Website and Data
Let’s go back to malware and website defacement for a moment. At the beginning of my cybersecurity career, I worked as a web hosting abuse support engineer for a major corporation. You have no idea how many phone calls and support requests I received every day from desperate customers who had lost their whole website due to a malware attack or a website defacement. And when I asked them if they had a recent backup, eight out of 10 either didn’t have one or, if they did, the files were outdated.
The company I worked for regularly backed up their customers’ websites, but sometimes that wasn’t enough. And, usually, disaster strikes when you aren’t prepared. Therefore:
- Back up your website and data regularly. Don’t get caught unprepared. Back up your whole website and key data. This will save you days of work and prevent you from starting from scratch in case of an attack or malware infection. Play it even safer and store another backup offline. This practice helps keep your data safe from ransomware. Because with 95% of interviewed security leaders confirming they have experienced ransomware attacks in 2021, nothing is too much.
- Scan your website for malware regularly. Did you scan your website for malware? That was an important question I asked when speaking with customers about their websites. Many didn’t even know how to do it. Regularly scan your URLs and files online and for free with tools like VirusTotal, Sucuri, or Quttera.
- Keep your software and devices up to date. Every week, it seems like new content management system (CMS) related vulnerabilities are coming out. One of the latest was related to WPGateway. A WordPress plugin that, if left unpatched, would allow a full takeover of websites using it. The solution? A fix has to be installed. Keep your CMS up to date and you’ll be safe. Ignore the warnings and risk being the next victim of business ID theft.
6. Keep Close Tabs on Who Uses Your Accounts (and Their Activities)
A good businessman knows his numbers, and I would add, knows exactly where the money goes. OK, no need to be obsessed like uncle Scrooge McDuck, who knows exactly where every single cent he owns is or how it’s (rarely) spent. But having a good overview of where your money goes can help you spot potential corporate identity theft. How?
- Regularly review your and credit card statements for fraudulent activity. A monthly review is sufficient. Did you notice an unauthorized charge or a small deposit you don’t recall? Notify your bank. In some cases, attackers may deposit a few cents on a business’s bank account just to verify that the account is valid. If successful, they try to use them for their expenses or transfer funds from your account. Are you part of a big organization? Get your accounting department to take care of it and send you a high-level report. Good financial reporting software will ensure automation and rigorous account statement reconciliation and accuracy.
- Implement a strong access control system. Do you know the story of the perfect employee who used her employer’s name to sign some “extra” checks for herself? Another example of the consequences of business ID theft. Once again, limiting who has access to what and the actions that every employee can perform (e.g., the principle of least privilege we talked about before) will minimize risks. Last but not least, never let just one person control a whole financial transaction.
7. Register Your Trademark
144% — that’s the total increase of ransomware cases handled by Unit 42 in 2021 over the previous year. But there’s another very dangerous form of ransom that is hitting businesses: trademark ransom.
Imagine this scenario: You’ve been using your business name for years. Your customers know it and recognize your products just by hearing your name. One day, a cybercriminal legally registers your business name as a trademark. He then notifies you that you’re using their trademarked name illegally and requests a ransom. The damage is done. What can you do? Pay the ransom? Go to court? Either way, it’ll cost you an awful lot of time and money.
To avoid this issue altogether, ensure your name and brand are adequately protected by trademarking your name and logo in all countries where you operate ahead of time.
8. Display Your Trademarked Logo in Your Customers’ Inboxes
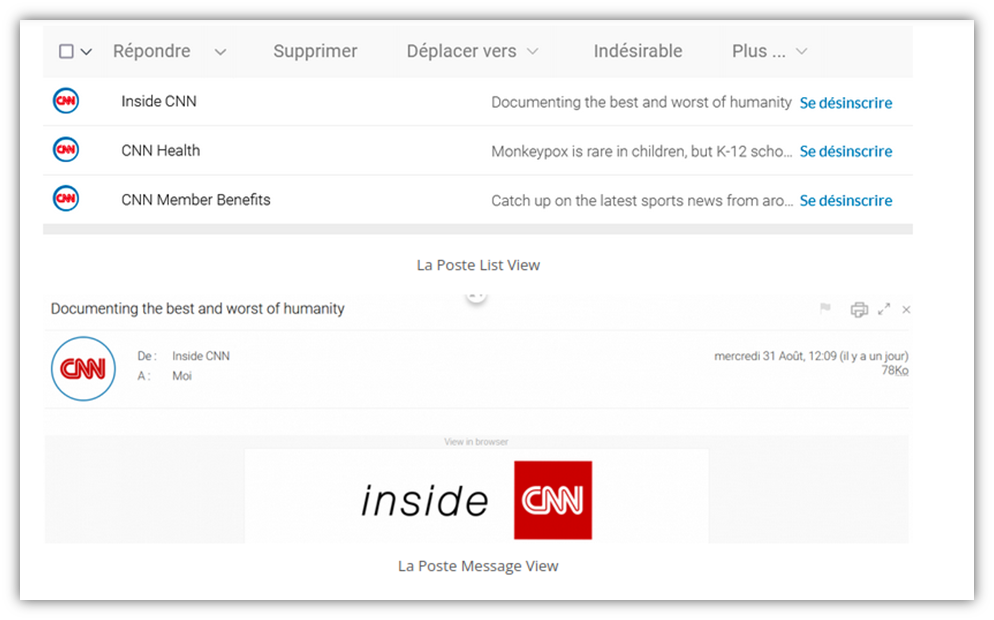
Phishing attacks mimicking brands and retailers increased by 29% in 2021 compared to 2020. Now that you’ve registered your trademark, make sure you protect it from such attacks. How?
- Adopt brand indicators for message identification (BIMI). Have you ever seen a brand logo next to an email you received in your inbox? BIMI is an email standard that adds your brand’s logo to your authenticated emails sent from your organization’s domain. Once implemented, your customers will be able to immediately spot your email even before opening it. The best part of it? The verifying process is free.
- Add a verified mark certificate (VMC). Add another layer of security to prove to your customers that the logo displayed near your email in their inbox is original and really coming from you. A VMC can do that by acting like the email equivalent of Twitter’s verified user blue checkmark. Want to know how to get it? Check out the information on BIMI Group’s website.
9. Ensure Compliance With Privacy and Security Regulations
Did you know that in the U.S., the Identity Theft Protection Act requires businesses to protect customers’ information by establishing appropriate policies and procedures? Protect your customers’ data and your organization from corporate identity theft. Ensure compliance with privacy and security regulations such as:
- The EU’s General Data Protection Regulation (GDPR),
- The California Consumer Privacy Act (CCPA),
- The Payment Card Industry Data Security Standard (PCI DSS), and
- The EU Payment Service Directive (PSD2).
10. Educate Your Employees
In 2021, 65% of surveyed executives and employees reported being approached by attackers. Do you recall the infamous Colonial Pipeline attack? In that case, the password of one single low-level employee was enough to wreak havoc.
Train your employees on how to be vigilant and inform them about common business identity theft methods as part of your cyber security awareness training. Make sure they’re familiar with your organization’s cyber security plan, even if you’re a small business. To do so, you can:
- Share educational resources and videos. There are several videos on business identity theft available on YouTube like the two below:
- Help your employees get certified. Get some of your employees certified as red flag specialists or data protection specialists. They’ll be a precious security resource for the whole company and help you spread the word among their colleagues.
- Use free and paid online courses and resources available on the internet. A few examples are those offered by the Open University, the resources available on the National Cybersecurity Society website, or the courses offered by the Association of Certified Fraud Examiners.
Be sure to take even greater care of your HR, IT, finance, and legal departments. They’re most at risk as they have privileged access to sensitive information and critical systems.
We’ve now reached the end of our list. As you can see, securing your business against corporate identity theft can be challenging but it’s also a task that should be taken seriously. Why? Let’s have a quick look at some of the consequences of business ID theft.
Consequences of Business Identity Theft
If the real-life examples in this article haven’t been enough to scare you, we have a list of shocking consequences that’ll make you reevaluate the tips listed above.
- Damaged reputation. Nearly 60% of companies interviewed by Customer Management Insider confirmed that brand reputation was essential to their businesses’ success. Can you imagine having your name used fraudulently by cybercriminals? It happens more often than you think. In one case, the customers who took the bait sent a total of $98.9 million to the hacker’s bank account. Let it happen once and your brand will be immediately tainted. And once it does happen, it’ll also impact your relationship with current and future creditors and business partners.
- Revenue loss. What happens when your reputation takes a hit? Your sales go down with it. Customers don’t trust you anymore, thus, they go elsewhere. As a result, you may end up being unable to pay your taxes, your employees’ wages, or purchase supplies. Simply put, it’s a real disaster.
- Negative credit report. If cybercriminals manage to get their hands on your credit cards or apply for a loan in your name, there’s a good chance that the unpaid bills will impact your organization’s credit score. This can get even worse if you are a small business owner, as it could also affect your personal credit report as well.
- Remediation costs. In November 2021, the IRS released its latest Yearly Criminal Investigation Report. The report showed over 2,500 investigations and $10 billion from tax fraud and other financial crimes. What has this to do with remediation costs? Let’s say that an attacker used your business ID to fill in a fraudulent tax report to get hold of a juicy refund from the government. Once discovered, you’ll have to face a great deal of struggle (and money) to resolve the dispute with the IRS or your state tax agency.
These are just a few of the consequences an organization could face in case of business identity theft. Therefore, beware of the cybercriminal attempting to steal your business’ identity!
Final Thoughts on Tips to Prevent Business Identity Theft in Your Organization
Identity theft won’t only damage you and your business, it’ll also have a serious impact on your customers’ relationships with your organization. But if you’re a small business, you’re not somehow magically shielded from this threat: business identity theft could happen to any kind of business, big or small.
Attackers could use your brand for fraud, to spread malware, and to scam your customers. Just one single action could spell disaster for your business — from significant income losses to reputational damages and lost customer trust.
I know. Fighting sophisticated attacks aimed at corporate identity theft isn’t a piece of cake. However, the above-mentioned tips can be your best bet in building a strong defense against business ID theft. Be on your guard, ramp up security standards, tighten your account security screws and register your trademark. All this will help you keep your organization’s private information secure.