This 5-step process will help you build a successful security awareness training program template
Question: What is the weakest line of defense in the cybersecurity world? The answer is people. Yes, human error is dangerous when it comes to protecting your organization’s data and assets. One wrong decision by an employee can lead to disaster. From stolen financial data to your whole network being held hostage in a ransomware attack, employees who don’t receive adequate security awareness training can hurt your organization.
Kaspersky’s IT security economics in their 2019 report discovered “that both enterprises and SMBs were most frequently affected by incidents as a result of inappropriate IT resource use by employees (52% enterprise, 50% SMBs).” Furthermore, the Netwrix 2018 IT Risks Report showed that human error was the leading cause of data loss (responsible for 50%).
I’m sure after reading these stats that you want to make sure your employees aren’t going to cause this type of damage to your organization. Well, the best way to stop this from happening is to train your employees to NOT make these mistakes. This type of training is called security awareness training or cybersecurity awareness training.
In this article, we’ll take you through a five-step process that will help you develop and manage a security awareness training program. This can be loosely used as a security awareness training program template. But first, here is a more official explanation of what security awareness training is.
What Is Security Awareness Training?
Security awareness training is what prepares your employees to respond to and handle security-related concerns. While security awareness training can touch on several topic areas, it’s commonly used for cybersecurity training. From phishing emails to data breaches, the purpose of security awareness training for employees is to ensure they are ready to deal with any cybersecurity issues that come their way.
Here is the five-step process to building a security awareness training program.
Security Awareness Training Step One – Choose Who Teaches the Course(s)
The first step of the security awareness training process is to decide who is teaching the course or courses. Some of the questions you need to ask yourself and your team to get this figured out include:
Do You Have a Professional Who is Equipped to Teach the Course?
Looking in-house is always a great place to start. This approach allows you to capitalize on your existing resources and not have to bring someone in from a third-party agency. If you do, this person would most likely be someone from the IT department.
Does Our In-House Expert Have the Bandwidth to Tackle This Project?
It’s important to remember that this won’t be a small project. Planning what should be covered, preparing the materials, conducting the courses, and potential follow-up lessons could all be included in the process. Don’t stress your IT team if they don’t have the time.
Who Else Can Teach This Training If Not an Internal Person?
There are several third-party services that you can hire to do this if you don’t have an in-house candidate with bandwidth. Obviously, you will need to weigh the expenses to determine what’s possible your budget when deciding who should head the security awareness training program.
But remember: Even if you have to shell out money for some quality training, the cost is still going to be significantly less than leaving your employees as uneducated, sitting ducks. People who have no cyber awareness are what cybercriminals love to prey upon.
Consider this following painful example of what happens when people lack phishing and cyber security awareness. Back in 2014, Xoom Corporation “disclosed that $30.8 million in corporate cash was fraudulently transferred to overseas accounts” due to a phishing attack. With results like that, you surely want your employees trained as well as possible.
Security Awareness Training Step Two – Decide How Often You Will Offer the Course (and Who Should Complete It)
Security awareness training is not a less-is-more type of thing — it’s a more-is-more type of thing. But just how frequently should you require your employees to complete this type of training?
The Advanced Computing Systems Association (USENIX) released a 2020 report titled “An investigation of phishing awareness and education over time: When and how to best remind users.” In it, they shared that around the six-month mark after receiving security awareness training is when employees typically start to forget what they learned.
The training used for this study focused largely on phishing, but regardless, it shows you that people can be forgetful. Based on these findings, it makes sense to hold security awareness training every six months. You should also include the training when you first hire a new employee because they are unfamiliar with your systems and methods.
As far as who should receive security awareness training, the short answer is everyone. Every user (employees, interns, executives, etc.) who has access to your network, systems, data, and other resources should receive training because any of them could be a potential target. If you have contractors who use your network and/or other resources, they should also undergo training as well.
Security Awareness Training Step Three – Decide What Topics to Focus on In Your Training
The answer to step three very much depends on how your organization operates. Are you a shipping company that handles physical belongings on a daily basis? Do you have a large sales team that interacts with customers on the phone and via email often? Do they handle customers’ personal information?
These are important questions to ask yourself. For most companies, there a few key areas that need to be covered in the training program.
The Dangers of Social Engineering
Social engineering is a tactic where a hacker tricks or manipulates targets into providing information or performing other actions that they normally wouldn’t. Cybercriminals try to create a sense of urgency or elicit reactions (fear, panic, curiosity, etc.) to get people to do what they want. A cybercriminal may attempt to get someone (often an employee) to:
- Provide personal or financial information (like a credit card number).
- Click on a link that leads to a dangerous website.
- Or download an attachment that carries malware.
Social engineering is integral to various types of cyber security attacks, including phishing and spear phishing. The latter is when a cybercriminal performs a very targeted phishing attack on a particular group or individual. This often involves the cybercriminal researching you personally and your organization’s hierarchy to learn what they need to be convincing enough to pull off their attack.
So, if an employee can be reached by an outside party on any platform, then that platform is a topic that you should cover in your security awareness training. This includes email, text messages, phone calls, and social media. Phishing is a huge problem for organizations. Verizon’s 2020 Data Breach Investigations Report discovered that the top threat action varieties in breaches is phishing (coming in at more than 20%).
Employees need to be able to:
- Recognize the signs of a phishing attack.
- Know what to do when they come across an attack (who to contact, how to notify the rest of the organization).
- And, also, they need to know what NOT to do (not clicking on anything whatsoever).
Managing Access to a Website
Employees who manage websites must know how to do so in a safe and secure manner. You may have a lot of employees interact with your website(s) on the back end, such as writers, SEO analyst, admins and so on. This is even more reason to include it in your security awareness training program template. Some topics that should be included in this section include:
Managing & Implementing CMS Updates
Not updating your content management system (CMS) can create vulnerabilities in your CMS. These vulnerabilities can be exploited by hackers and result in your website becoming compromised. CMS updates are designed to patch these vulnerabilities. It’s important to ensure through your training that all employees are aware of this. This helps create accountability to ensure the updates are made.
Determining Who Can Access Your Website
Another important topic your security awareness training should cover relates to accessing your organization’s website. It’s important to have a plan to eliminate accounts when employees leave. It’s also important to limit access to the CMS based on what capabilities an employee needs to perform their job. This method is called POLP (principle of least privilege). A common example is a copywriter who publishes blogs — they likely don’t need access beyond being able to publish their work.
Protecting Login Information
Employees need to know how to protect their login information. They are the keys to your systems, network, etc. A Google / Harris Poll from 2019 shows that 66% of people use the same password for more than one account. The same poll also shows that 43% of users have shared their passwords with someone in the past.

If you think sharing passwords is bad, then you’re really going to love this next stat… The 2020 State of Password and Authentication Security Behaviors Report discovered that “42% of IT professionals report that their organization relies on sticky notes to manage passwords.” Yes, you read that right: sticky notes! 42%!
If these stats show anything, it’s that there are many organizations out there that are susceptible to brute force attacks and physical security intrusions. This means that password login credentials are likely to end up in the wrong hands. It’s important to cover how to create strong passwords and how to manage your login credentials properly.
Another important thing for IT admins to keep in mind concerns secure password storage. You should never, under any circumstance, store passwords in public-facing environments. All passwords should be salted and hashed on the backend, and those salted password hashes are the only things that should be stored. Be sure to review NIST’S recommendations regarding secure password storage in their special publication “Digital Identity Guidelines” (SP-800-63B).
Safe Internet Browsing
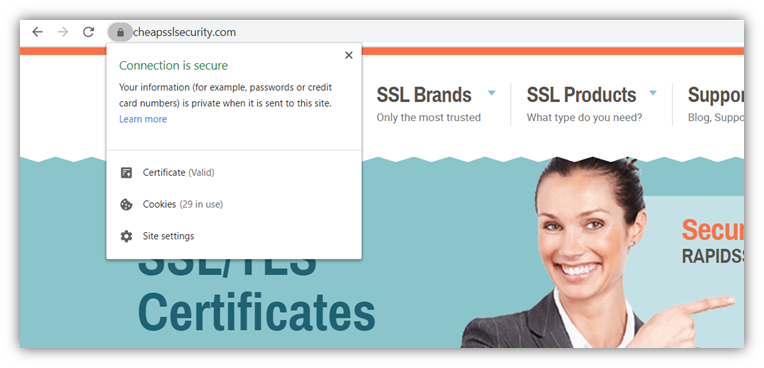
Employees should know how to spot a suspicious or malicious website. Users should only interact with websites that showcase the HTTPS and padlock icon beside that website’s URL. And not just that — they should also click to read the certificate’s details to verify the company’s identity (both pictured below) to ensure they’re connecting to the legitimate site. What this tells you is two things:
- Your communications are protected by HTTPS encryption and you won’t have to worry about your interactions being stolen by a hacker.
- The website utilizing the HTTPS encryption has been authenticated in their certificate details and you can trust the site.
You should also look for a privacy policy on a website to know if it is legit. A privacy policy should tell you how a website safely collects and handles your personal information. Knowing how this is done should provide you peace of mind when interacting with a website and act as a way to tell if a website is legit.
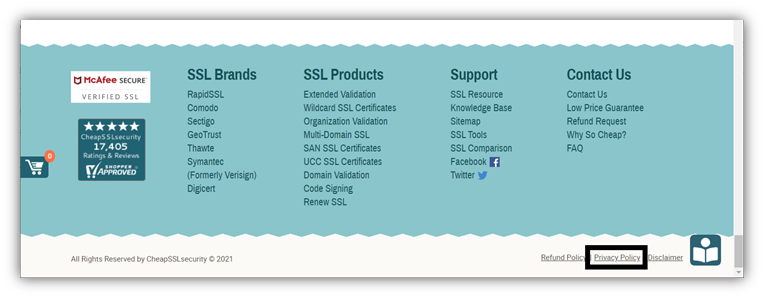
You should also look for websites that display site seals (which are also sometimes called trust badges). Similar to an SSL certificate, a site seal shows that a company has been vetted and deemed safe by a trusted third party (known as a certificate authority or CA). This is just another way to know a website is both secure and safe.
Physical Security Considerations
Another important topic to cover is physical security. An easy way to think about physical security is to think of your job like your house. Do you let random strangers into your house? No. So, don’t do it at your job! Make sure to cover basic things like not holding the door open, checking for IDs, and not leaving guests untended.
Also, just like your house, there are certain rooms or areas that are higher security and should be off-limits to everyone except select individuals. If you throw a party, you don’t want your guests rummaging through your jewelry box or safe. Similarly, you don’t want unauthorized individuals in sensitive areas. These are great topics to cover in your security awareness training for employees.
Using a VPN
A VPN (virtual private network) basically turns a public network connection into a private network connection. Public networks are typically not encrypted, which makes them unsafe to browse on. This is important for your employees to know if they work remotely or decide to take off to a coffee shop to work on their lunch break. It is much safer to use a VPN in these situations. It’s another great topic to cover in security awareness training for how they can stay safe online while on the go.
Security Awareness Training Step Four – Have a Plan for Everything
It’s vital employees know what the plan is if they come across a cybersecurity issue. But before they can know that you first need to have a plan in place for that training to draw from. This means you’ll need to figure out these items before putting together your cybersecurity awareness training program:
- Who do employees contact when they come across an issue?
- How do they contact them?
- Who should they contact when the first point of contact is out of the office/unavailable?
- In what circumstances should the rest of the company be notified of an issue? And how will that be done?
Answering these questions will help ensure you have a plan set in place for you and your employees when a cybersecurity issues arises. And remember, it’s a matter of when something will happen and not if.
For more ideas on how to develop your cyber security awareness training and the topics to cover in it, be sure to check out the following resources:
- The Cyber Security Awareness Toolkit
- CISCO’s Security Education Plan Template
- SANS’ Security Awareness Planning Kit
- KnowBe4’s Security Awareness Training Resources
Security Awareness Training Step Five — Ensuring Success
It’s important to follow up with your employees to make sure they are prepared. You can simulate a phishing test to see if your employees:
- Open phishing emails,
- Click on any links or engage with attachments,
- Take the appropriate steps you outlined in the training program.
This isn’t about catching people making mistakes to humiliate them. Doing tests like these help you make sure your employees are prepared for the worst. Heck, for a little fun, complete Google’s phishing quiz just to see how easily you can spot phishing scams yourself.
Security Awareness Training — Final Word
We hope that these five steps will help you create a security awareness training for employees that is effective and seamless to manage. If you follow these steps, you will know:
- Who is managing the program.
- How often it will take place and for who.
- What topics are covered (phishing, internet browsing, physical security, etc.).
- What processes need to be implemented to ensure there is a plan when an issue arises.
- And how you will follow-up with your employees and ensure they are prepared.