Have you heard about ransomware and fear it will happen to you? Learn what it is and how to prevent ransomware below…
In today’s digital world, we all need access to some type of online data or system. This could be as simple as accessing your home computer or as vast as accessing a company network. Now, imagine if you were blocked from being to access that data or system and then a cybercriminal demanded some type of ransom payment in exchange for you regaining access. That would not be fun. And this is what ransomware is. And yes, the point I was making is ransomware = not fun.
How “not fun” is it? Well, let’s consider the ISS World ransomware attack as an example. The Demark-based company was the subject of a ransomware attack that involved their employees losing access to their company emails for three weeks. When all was set and done, which included “regaining control of the affected IT systems and re-launching critical business systems,” ISS World was on the hook for $74 million.
Well, if you weren’t scared before, I’m sure you are now. Don’t worry. We got you covered. In this article, we’ll answer the question “what is ransomware?” and look at a few ways you can prevent it.
What Is Ransomware?
We’ve already touched on what ransomware is from a high level, but let’s dive into the topic more in depth. A ransomware attack is a cyber-attack that involves an unwelcome party (hacker) using malware to prevent you from accessing your devices or data. But what makes this worse — and is the reason why it’s known as a ransomware attack — is that they want something in return for giving you back access.
In actuality, there are two components here that make up ransomware:
- The ransomware infection. A cybercriminal infects a device with a malicious software (malware) known as ransomware. This malware creates the denial of access to the device and/or its data by either locking up the device or encrypting all of its files and other data.
- The attacker’s ransom demand. The cybercriminal uses the leverage they have to make a demand. Most commonly, they ask for cryptocurrency in exchange for a decryption key to give you back access to your data.
But what exactly are ransomware operators trying to deny you access to? A hacker could be denying access to:
- Home or work computers,
- Mobile devices,
- Website or web servers,
- Other types of servers (like the aforementioned attack on ISS World’s email server),
- IT systems, or
- Any other type of data or network.
What is asked for in exchange for the access back is, typically, a monetary demand. Ransomware hackers are notorious for demanding payments in digital currencies such as Bitcoin, Ethereum, and Monero. This is due to many types of cryptocurrencies being pseudonymous. (This means that there is little to no identifying information attached to the digital transactions.)
Who Do Ransomware Hackers Target?
So, who’s at risk of falling prey to ransomware? The reality is that there’s really no limit in terms of who a ransomware hacker can target. They attack individuals, small businesses, governments, and large corporations alike. However, small to medium businesses often get the brunt of the attacks. According to Coveware’s Q3 2020 data, 70% of ransomware attacks were aimed at small to medium-sized businesses.
But what makes SMBs such a tempting target? The reason SMBs get attacked most could be attributed to:
- Small and medium-sized have a lot to lose when being denied access. (We’ve all seen what happens when small businesses have to halt operations via the current Covid-19 pandemic.)
- SMBS carry plenty of sensitive data that may not be well protected.
- SMBs often don’t have the funds — or choose to not allocate the proper funds — to cybersecurity that a larger corporation would.
And not having a limitless budget for cybersecurity is all the more reason to be prudent with preventing an attack!
How Does a Ransomware Attack Occur?
Theoretically, ransomware starts with you or one of your coworkers. A hacker can only take over a system when there’s an opening for them to get in. It’s your job to close those openings by eliminating vulnerabilities they can exploit. Below are a few ways you or your coworkers enable hackers into carry out ransomware attacks:
- Clicking on dangerous links,
- Downloading unknown attachments,
- Making weak passwords,
- Being careless with login information,
- Not running updates or patching security vulnerabilities.
Let’s consider the unpatched security vulnerabilities example. In May 2017, the WannaCry ransomware attack ran rampant, affecting more than 230,000 computers globally. It crippled the United Kingdom’s healthcare system and affected businesses in more than 150 countries.
But what was WannaCry’s opening? A vulnerability in Microsoft Windows operating systems. And it could have been avoided as Microsoft provided a security patch for the vulnerability (which was dubbed EternalBlue), but the problem is many opted not to use the patch.
Needless to say, preventing ransomware requires accountability, and that accountability starts with you.
How to Prevent Ransomware (What to Know to Fight Ransomware)
After placing the responsibility of preventing ransomware on your shoulders, I’m sure you’d like some actionable items that will help you fight ransomware. Below are a few actionable items that will help you know how to prevent ransomware.
Patch Vulnerabilities and Keep Your Systems Up to Date
Fitting we start here. You’ve already been made aware of the dangers of an unpatched security vulnerability. So, how do you fix the problem? It’s pretty simple: you keep things patched and up to date. Updates and patches are a manufacturer’s way of fixing vulnerabilities that exist within their products.
Let’s say you use WordPress as your website’s content management system. You’ll want to ensure you install the updates provided by WordPress for your themes and plugins. You will also want to ensure you are using the latest WordPress version.
You can find these updates in your WordPress admin panel, typically found on your dashboard. Simply click on dashboard and run the updates, then you’re good to go. WordPress also offers the ability to set up auto updates, so you don’t even have to think about it.
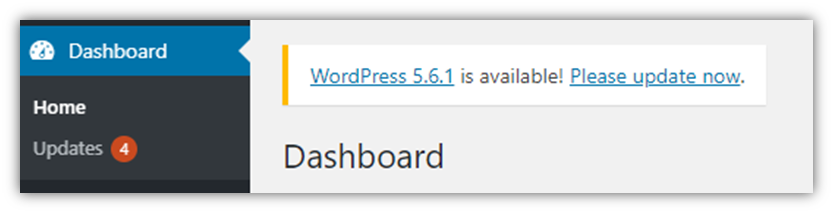
You’ll see in the screenshot above, under dashboard there is an Updates tab. The orange “4” signifies there are four available updates. Also, you can see that this website needs to be upgraded to the latest version — WordPress 5.6.1. It’s wise to run all of these updates. I mean, they did say “please,” after all…
Run Vulnerability Scans
Got bigger fish to fry? Let’s say you need to look for vulnerabilities on your entire company network, not just a website. Well then, I recommend getting a network vulnerability scanner. These bad boys will scan your entire network searching for updates and unpatched vulnerabilities.
Going back to websites, you may still want to consider using a vulnerability scanner versus CMS auto updates. If a plugin is not maintained by the creator, then an update may not be released by your CMS. However, many vulnerability scanners will detect this unmaintained plugin and alert you. If your scanner detects such a plugin, then you should delete the plugin immediately as it could create a high-risk vulnerability (since it’s no longer receiving updates).
Protect Your Email
Think of emails as a gateway to your network — they’re constantly going out and coming in. It is important you secure this “gateway” as soon as possible. But how do you protect your email? Spam filters, blacklists, and cyber awareness training are a few things that come to mind.
Spam filters help you filter out potentially dangerous emails. Similar to a firewall, spam filters work on a set of predefined rules that help defect unwanted incoming emails. These predefined rules typically include algorithms that:
- Analyze wording, email addresses, and attachments,
- Utilize a malware scanner, and
- Respect the Sender Policy Framework (SPF).
When a malicious email makes it past your spam filter (and I say “when” instead of “if” because it will happen), you’ll need to ensure your employees know how to handle them. This is where employee security awareness training comes in. This training aims to ensure your employees know how to handle potential cybersecurity issues, such as:
- Operating safely on social media,
- Knowing how to identify malicious emails and websites, and
- Creating unique and secure passwords.
In relation to email, it’s vital your employees know how to spot phishing emails as they come in. The goal of a phishing email is to trick employees into:
- Clicking on a dangerous link,
- Downloading a dangerous attachment, or
- Performing some sort of other action that will ultimately allow the hacker into your system (such as providing them with your login information).
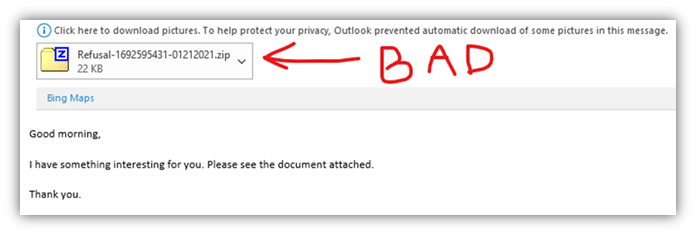
Here is a real-world example of a phishing email. If you’ll notice, the attacker is using common phishing tactics. They’re being vague because it lessens the likelihood something would stick out as being obviously suspicious. Also, they attempt to create a bit of intrigue with the attachment… possibly leaving the recipient thinking “what could it be?” These are all tactics your employees should be aware of to help fight ransomware.
Creating Backups Will Help You Fight Ransomware
Another way to fight ransomware is to back up your data or website. If a cybercriminal takes over your home computer, they won’t have much leverage if you’re maintaining current backups of your precious photos, documents, and other files on an external hard drive. And if you’re a website owner, there are plenty of ways to backup your website. Maybe the safest way is to get an automated website backup tool that will automatically create backups for you and store them on a non-public-facing server that’s separate from the web server your website is stored on.
Business owners should also consider using a secure cloud system to store important data on with login credentials that are unrelated to their network. This way, the ransomware hacker loses leverage and cannot completely wipe out your data.
The idea here is straightforward and simple:
- Backup your data/website,
- Keep your backups stored separately from your network and systems,
- Maintain multiple copies of your backups.
If you do these things, it’s likely that a cybercriminal won’t be able to hold your backups hostage because you’ll have more than one copy to rely on.
What Is Ransomware & How to Prevent It – A Final Word
Now that you know the answer to “what is ransomware?’ and how to prevent ransomware, I hope you are feeling more informed about this danger. It is important to be prudent, know the dangers you are dealing with, and do your part in preventing an attack. However, it’s also important that you do not live in fear and enjoy the wonderful perks of being a business owner, website admin, or whatever position you hold. Life is short, prepare for the worst and hope for the best!