How Does TLS Work – The SSL/TLS handshake process simplified like never before
As it goes with all handshakes, the SSL/TLS Handshake is where it all starts. The SSL/TLS handshake involves a series of steps through which both the parties – client and server, validate each other and start communicating through the secure SSL/TLS tunnel.
SSL Handshake Explained
The reason it’s called a handshake is that it’s when two parties – client and server come across each other for the first time. The handshake involves a number of steps that start from validating the identity of the other party and concludes with the generation of a common key – secret key if you may call it.
A TLS handshake marks the onset of TLS communication between the client and the server. During a TLS handshake, both the parties exchange messages verify the identity, agree on cipher suite and TLS version to be used in communication, and finally establish the session’s keys.
Fundamentally, the SSL handshake is nothing but a conversation between two parties (client and server) wanting to accomplish the same purpose – securing the communication with the help of symmetric encryption.
Imagine this SSL Handshake Process as a dialog between the two.
Let’s see how it goes.
Client: “Hello there. I want to establish secure communication between the two of us. Here are my cipher suits and compatible SSL/TLS version.”
Server: “Hello Client. I have checked your cipher suits and SSL/TLS version. I think we’re good to go ahead. Here are my certificate file and my public key. Check ‘em out.”
Client: “Let me verify your certificate. (After a while) Okay, it seems fine, but I need to verify your private key. What I’ll do is, I will generate and encrypt a pre-master (shared secret key) key using your public key. Decrypt it using your private key and we’ll use thing master key to encrypt and decrypt the information”
Server: “Done.”
[Now that both the parties know who they’re talking to, the information transferred between them will be secured using the master-key. Keep in mind that once the verification part is over, the encryption takes place through the master-key only. This is symmetric encryption.]
Client: “I’m sending you this sample message to verify that our master-key works. Send me the decrypted version of this message. If it works, our data is in safe hands.”
Server: “Yeah, it works. I think we’ve accomplished what we were looking for.”
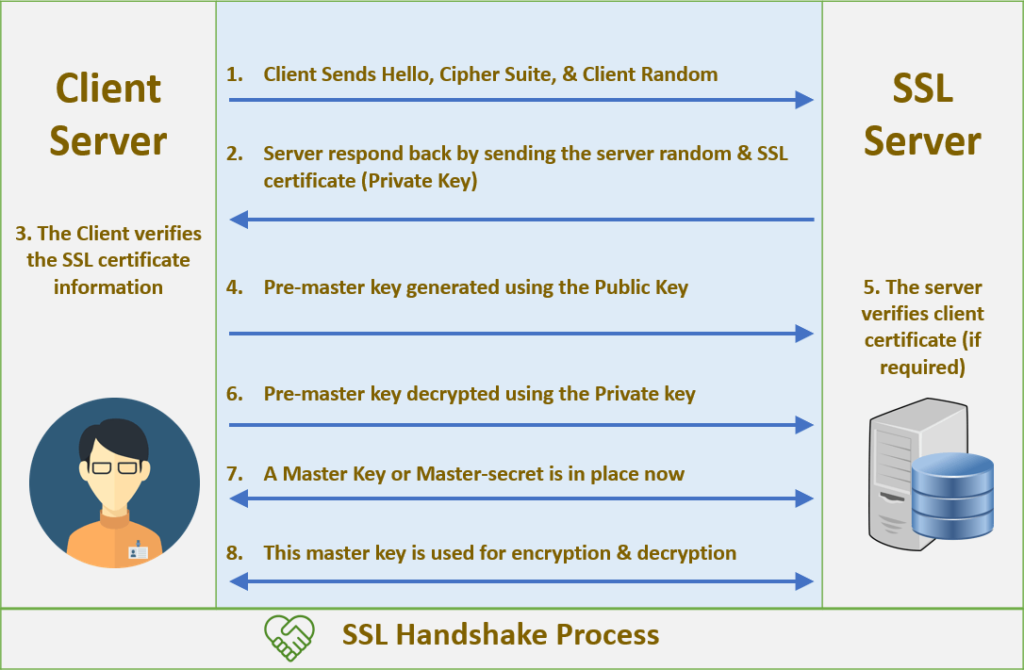
From now on, every bit of data transmitted back and forth between client and server will be encrypted. This is called the SSL/TLS handshake process.
Related Posts
- Why is SSL Certificate Mandatory?
- SSL Certificates for Website : #1 User Security
- HTTP vs. HTTPS, Do You Really Need HTTPS?
- How SSL protects personal information through encrypted connections
- How to Get Rid of ERR_SSL_PROTOCOL_ERROR in Google Chrome Browser
- How to Fix NET::ERR_CERT_COMMON_NAME_INVALID
- How to Fix ERR_CERTIFICATE_TRANSPARENCY_REQUIRED Error in Chrome
Save 89% on SSL or HTTPS Certificates
Secure a website in few minutes with HTTPS. CheapSSLsecurity.com offers cheap SSL certificate with 89% discount.