Certificate Transparency Simplified Like Never Before
The SSL/TLS certificate industry has been in the midst of some substantial fundamental changes, and Certificate Transparency (CT) is one of them. Most people first learned the term ‘Certificate Transparency’ in 2015 when Google mandated that all certificate authorities log their EV SSL certificates for CT. Now, this requirement is going to be mandatory for all the certificates starting April 2018.
So, what is Certificate Transparency? Let’s find out.
What is Certificate Transparency?
Fundamentally, Certificate Transparency is an open-source framework for the CAs under which, they log and report the certificates they issue to domain name owners. This way anyone can see which CA has issued certificates for which domains. Anybody, let us repeat, anybody can see these logs. Basically, it’s like an inventory of all the certs, CAs, and domains.
We hope this has cleared up some confusion for you.
As far as the SSL/TLS ecosystem is concerned, there are several elementary shortcomings, and certificate mis-issuance/fraudulently is a major one. DigiNotar – once a certificate authority – had to file for bankruptcy as a result of fraudsters issuing 500 certificates illegitimately from its infrastructure. Certificate Transparency is aimed at curbing such attempts and creating an environment of trust.
What is Certificate Mis-Issuance?
Certificate mis-issuance is a lot what it sounds like. Certificate mis-issuance occurs when a certificate isn’t issued to the intended party.
The certificate is called mis-issued if…
- A CA issues a certificate to the wrong party
- A certificate is issued maliciously without the consent of a CA
Consider these two cases:
- Case 1: If a CA mistakenly issues a certificate to an incorrect domain. Let’s say, instead of issuing a cert to domain example.com, the CA issues one to exemple.com. Now the domain name owner of example would be wondering where his/her cert is and the one of exemple.com would be wondering where the hell that cert came from. And if an ill-intended party is in control of exemple.com, god help the CA!
- Case 2: Let’s say you are a certificate issuing authority and you issue thousands of certificates on a daily basis by validating identities of certificate issuers. One day, unfortunately, a hacker issues a certificate by circumventing your validation process and poses as someone else. This way, he/she gets a good platform to execute cyber-attacks. This scam is discovered by a security researcher and fingers will be raised at you for issuing an SSL/TLS cert to a malicious party. Such incidents have happened in the past and have turned out to be catastrophic for such CAs (you, in this case).
Here’s How Certificate Transparency Can Help (Immensely)
In both of these cases, had the CA logged the cert details, it would have helped immensely.
In the first case, the CA wouldn’t be at fault for issuing a cert to a malevolent party (although questions can still be raised how the verification was bypassed).
As far as the second case is concerned, the domain owner of example.com could go to CT logs and see that his/her cert has been mistakenly issued to exemple.com and report this to the CA. Thus, any further damage could have been avoided.
In short, certificate transparency is a win-win for everyone.
Here’s how Certificate Transparency works
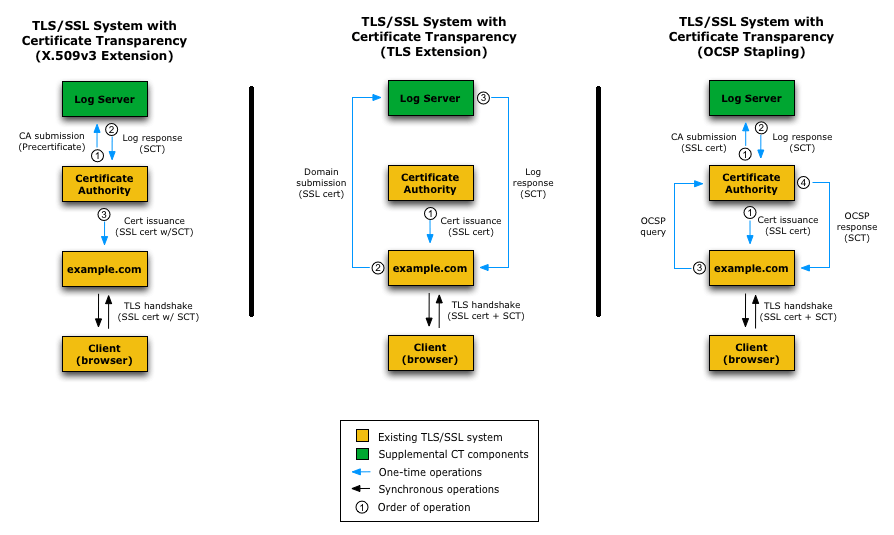
When a user requests an SSL/TLS certificate, a CA must (from April 1, 2018) submit the certificate details to a CT log. Once a CA does this, the log responds with a signed certificate timestamp (SCT). This stamp must be given by the CA to the domain name holder. Simply put, this is an assurance from the CA that certificate will be submitted to the CT logs. When it comes to delivering the SCT to the domain holder, there are three methods through which this can be done.
These methods are illustrated in the below diagram.
How to Check Certificate Transparency in Google chrome
Google has launched a new Project called as Certificate Transparency Project aka Certificate Transparency Check, which reviews the certificates details that are active in the Certificate Transparency logs. Enter your domain name or a website in Certificate Transparency Checker tool and check whether the Certificate Transparency enabled or not for your domain name or a website.
Per Google official update, there are 1,509,642,997 logs already being placed and they are growing on each of second.
Certificate Transparency Impact on Chrome
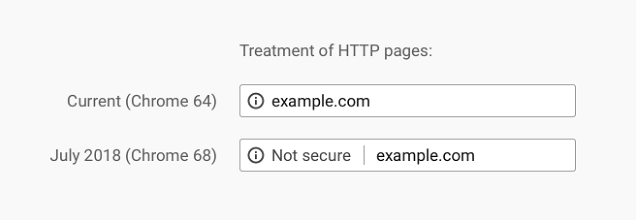
After the implementation of Certificate Transparency policy, Chrome 68 & its upcoming version will no longer support HTTP & encounters the “Not Secure” warning in the address bar.
This image shows how Chrome will treat HTTP pages.
It is the right time to all unencrypted websites to move with an SSL certificate in NO TIME.
Here, we got the latest and official updates in regards of Certificate Transparency from top Certificate Authorities, who are dealing with the large market in SSL security industry.
“Certificate Transparency (CT) helps you monitor certificates issued for your domains by making the certificate information available in a public log. All certificates issued after June 1, 2016 include CT.”
“Symantec is pleased to extend support for Certificate Transparency (CT) for our Organization Validation (OV) products, a key certificate management capability for all SSL/TLS certificate types and customer channels. This is just the next step in empowering organizations with the ability to detect and mitigate security concerns for domains they own.”
Wrapping Up

Buy Sectigo SSL Certificates – Save 53%