FBI IC3’s 2020 Internet Crime Report reveals that U.S. consumers lost $13.3 billion over the last 5 years (2016-20) to cybercrimes — many of which include the use of ransomware and other types of malware. We’ll break down what malware attacks are and why they’re a threat to your business.
A malware attack is something that makes headlines virtually every day around the world. These cyber attacks involve the use of malicious software (malware), which can loosely be defined as any code or software that’s designed with malicious intentions. Bad guys can use malware to disrupt your company’s operations, acquire sensitive information or even get you to pay them money. Some of the different types of malware they may use include trojans, viruses, worms, ransomware, and spyware.
As a result of a recent cyber attack on the U.S. fuel company Colonial Pipeline, BBC reported that the prices for unleaded gasoline at the pumps rose by 6 cents to $2.967 per gallon and stock shares of energy firms increased 1.5% within days. Although the attackers — a Russia-based cybercriminal group called DarkSide — say they’re apolitical and “didn’t mean to create problems,” the BBC says they’ve successfully created additional tensions between the United States and Russia.
All of this leads us to answer the core question that’s led you here: “What is a malware attack?” We’ll also go over the types of threat actors that carry out these attacks, their motives, and some common signs of malware attacks and infections.
What Is a Malware Attack? Here’s Your Malware Attack Definition…
A malware attack is a way for cybercriminals to gain unauthorized access to your network, IT systems, data or other digital resources by using malicious software. Cybercriminals use one or more types of malware to infect individuals’ and businesses’ devices, typically without their knowledge, to achieve personal goals or other agendas (which are often financially motivated).
Cybercriminals carry out malware attacks through many channels (or what we call attack vectors), including:
- Sending malicious URLs and attachments in phishing emails, SMS texts, and social media messages.
- Creating malicious websites that impersonate legitimate websites.
- Using malicious advertising (what’s known as “malvertising”) to trick or persuade users to click on them.
- Infecting software or other files that they share through peer-to-peer file-sharing services and third-party app stores.
- Sending out fake software updates that impersonate legitimate software programs and companies.
Which Devices & Operating System Are Prone to Malware Attacks?
A malware attack can affect virtually all types of devices and operating systems. This includes:
- Mobile devices,
- Laptops and desktop computers,
- Web servers and other IT systems and infrastructure,
- Smart technologies (IoT devices), and
- On-prem and Cloud networks.
While connecting devices to your wireless network is convenient, that convenience doesn’t come without risks. Cybercriminals can target a vulnerable connected device as a way to gain access to your network and other devices that connect to it. There, they can deploy malware that allows them to spy on you, encrypt or steal your data, or block you from accessing various systems.
Whether you’re a user or Apple or Windows devices, you can still find yourself the target of a malware attack. Malware attacks can be device- or OS-specific, or they can be universal in their approach.
But it should come as no surprise to say that mobile malware is a booming business. Trend Micro’s 2020 Annual Cybersecurity Report states that mobile malware jumped 67% in from 2019 to 2020. The following figure illustrates this increase:
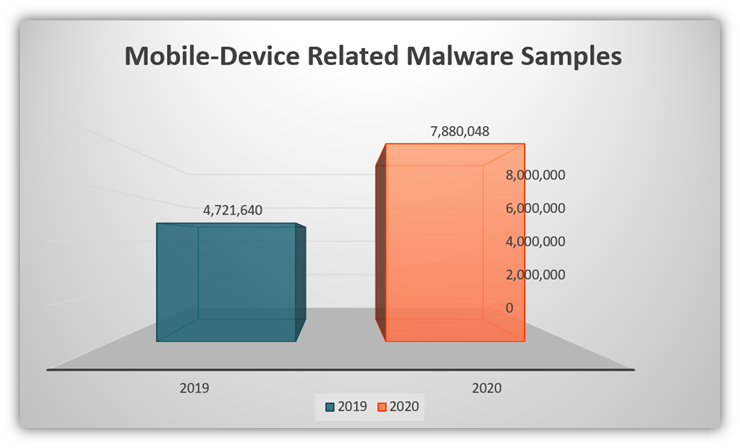
Malicious apps, links, attachments, and software for the mobile devices proved to be the culprit behind the infected devices. Trend Micro recorded a new variant of the Joker family of malware, which was discovered in a wallpaper app offering HD and 4k wallpapers. Google announced in January 2020 that it removed 1,700 Bread (Joker)-infected apps from its Play Store over the previous three years and that the list is still growing.
But why is Joker such a threat? Trend Micro reports that the malware is responsible for many malicious activities, including:
- Stealing contact information from users’ infected devices,
- Signing users up for premium services without their permission, and
- Compromising SMS messaging.
The Joker continues to remain a threat because the actors tweak the malware code to seek gaps in the Google Play Store’s security measures. In previous techniques, the actors have encrypted the malicious code to remain under the radar of the analysis engines. The other technique, dubbed “versioning,” involved uploading a clean version of the app and then adding malicious codes to it. The new Joker variant incorporated GitHub and repositories to avoid detection.
What Are the Motives Behind a Malware Attack?
We touched on this a bit earlier, but the goal behind malware attacks is typically to gain unauthorized access to data or systems. Once a cybercriminal infects your device or network, they can use that access as a way to observe your behaviors and activities or gain control of your device.
Of course, there are many reasons why cybercriminals launch malware attacks and use other methods to carry out cybercrimes. IBM and the Ponemon Institute’s 2020 Cost of a Data Breach Report 2020 breaks down cyber attack threat actors and motives into several categories:
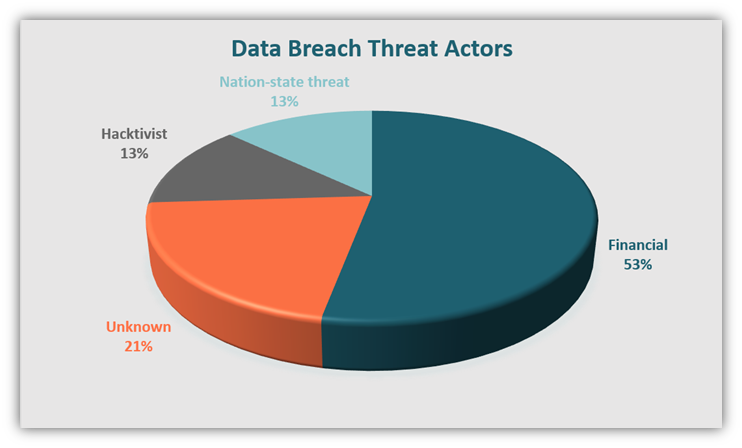
The chart shows that more than half of malware attacks are financially motivated. Motives that fall within the “Unknown” category include:
- Espionage,
- Revenge,
- Fun or entertainment, and
- Testing the knowledge/testing security.
However, IBM’s report also compares the average costs of malware attack vis-à-vis their motives or the type of attacker, and the resulting figures were interesting to say the least. Their research shows that financially motivated breaches had the lowest average cost for victims. On the other hand, the attacks perpetrated by nation-state actors were the costliest breaches. Take a look at the figure below:
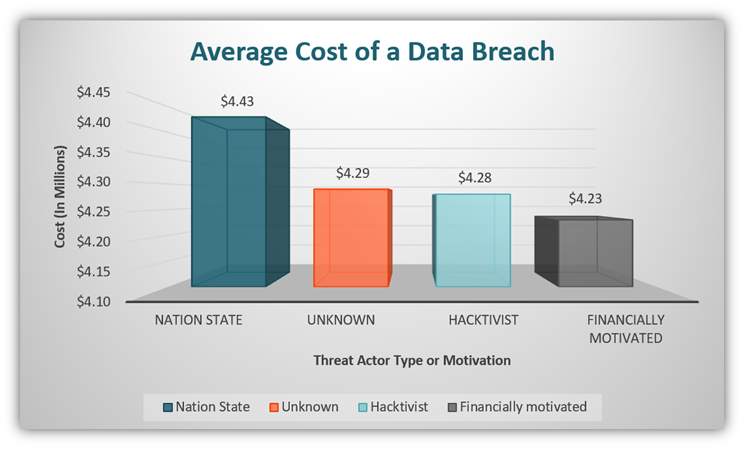
Regardless of whether a bad guy has one or multiple motives, the result of a cyber attack or malware attack is never good for victims. There are times when victims are unaware of the breach and continue to bleed information, money, or worse — both — for a long time. So, how do you know you have been attacked? Well, read on.
What Are the Signs of a Malware Attack or Infection?
To better answer the question “what is a malware attack?” you first need to know how to identify them. But how do you know whether your device or network is infected with malware? After all, not all cybercriminals make announcements about your device being infected and prefer to be stealthy about their activities. Of course, you should be keeping your systems updated and running cybersecurity monitoring and detection tools. (We’ll speak more on those shortly.) But there are some easy things you can keep an eye out for as well…
10 Signs You Might Have a Malware Infection
Here are some of the tell-tale signs that your device or network has malware:
- Frequent browser redirects: If you find yourself being redirected to unknown websites, or if your default homepage keeps changing on its own, it can indicate that you have an unwelcome guest on your computer. Common redirects will take you to adult websites or phishing sites.
- Your computer is super slow or laggy: If your computer takes years to load or perform basic tasks, you should check your system for malware. If you’re not tech-savvy, this would be a good time to contact your IT person for help.
- A lot of ads and popups display when you browse online: Do you remember our article on adware? Your computer might have frequent popups and ads if you are a victim of adware.
- Issues turning your computer on or off: Taking too much time to shut down or power up your device might mean that you have malware on your device. However, there are other reasons for this problem — running an outdated operating system, having too many files or insufficient RAM on your device, etc. So again, talk to your IT person if this problem persists.
- Low memory or storage issues: If you haven’t used a lot of data on your device but it’s reporting storage space issues, you might have an uninvited guest within your system. Be alert and check how your memory is utilized. You might discover that you have a malware infection.
- Your electricity bill or device’s CPU usage is unusually high: Is your device’s CPU usage a lot higher? How about your power bill? You should check how your computing resources are being utilized. Higher-than-normal usage may indicate that you have malware hijacking your resources without your knowledge.
- Your identity is stolen: Identity theft can occur in many ways. Cybercriminals can get their hands on your personally identifiable data via data breaches, phishing scams, or by installing malware onto your device that steals your information. If you discover any new accounts opened in your name or other tell-tale signs of identity theft, be sure to check your devices and network for signs of malware.
- Your intellectual property or trade secrets are no longer secret: Cybercriminals love to use phishing tactics and malware to steal businesses’ intellectual property and trade secrets. If you discover your sensitive information being used or published externally, you may have malware that’s transferring your data to a third party.
- If your contacts receive suspicious emails or messages from you: If some of your friends or customers tell you that they received emails or texts from you that you never sent, it can indicate that your device is infected. The threat actor might be impersonating you as a way to trick your contacts into opening a malicious link or attachment.
- Unknown and low-value transactions appear on financial statements: If you observe small or unusual entries on your account statements that you don’t recognize, it may indicate a big issue. If a cybercriminal installs malware onto your device or network, they can use it to capture or intercept sensitive information such as your account credentials.
If you receive frequent notifications warning that your device is infected that direct you to click on a link or call a specific phone number, beware. Either you might already have adware on your device, or someone is trying to infect your device through fake antivirus notification scams.
If you have more than one symptom, your chances of being a victim of a malware attack are higher. Hence, it’s imperative that you keep a close eye on your IT systems, keep your systems patched and updated, and use reliable cybersecurity and threat detection tools (which we’ll talk about momentarily).
If you think you’re the target of a malware attack, alert your IT department immediately so they can take action and also contact outside agencies. Some examples include including any cloud service or managed service providers you work with, as well as the cybercrime divisions of local, state, or federal law enforcement.
How Do You Detect Malware?
If you think you are a victim of a malware attack, contact your IT person right away. If you’re tech-savvy and want to explore on your own, you can use some of the following tools and methods:
- Antivirus and anti-malware tools: Scan your devices and IT systems regularly with reliable antivirus or anti-malware programs.
- Network monitoring tools: Many malware infects your network, and many network monitoring tools in the market can help you detect malware.
- SIEM tools: SIEM (Security information and event management) are tools for holistic cyber-security of the enterprise. They give a real-time view of the security issues of the organization.
- Signature-based detection tools: This type of detection method aims to identify unique patterns that exist in known malwares’ underlying codes. These unique code patterns form digital footprints or signatures that antivirus and anti-malware can use to identify known threats while scanning your device. When they identify a known malicious signature in a file, they will flag it. But what if a malware variant changes its code (which is the case with self-altering polymorphic and metamorphic malware, which can re-write part or all of their code)? This brings us to our next method…
- Behavior-based detection tools: This method of detection, also known as heuristic analysis, evaluates software and code rules to identify malicious intended behaviors (via a process known as static analysis) or executed actions (via a process known as dynamic analysis).
- Virtual machine: If the file is suspicious or dodgy, you can test it in a contained virtual environment known as a virtual machine or VM. Although similar to a sandbox, a VM is a different technology: it’s a simulated environment that allows you to run and safely test files to determine whether they’re safe or malicious.
Final Words on Malware Attacks
A malware attack is an attack that affects your IT systems and devices through malicious software or code. It’s a threat that has been known to cross the line between our digital and physical worlds. is crossing the thin line between the virtual and the physical world. For example, Iran’s nuclear facilities were the target of malicious software known as Stuxnet about a decade ago. The incident became known as the world’s first act of cyber warfare.
After considering Stuxnet and the more recent U.S. fuel pipeline scenario, cyber warfare no longer looks like something out of The Matrix. It’s real, and it’s happening now. A malware attack can be severe, moderate, or mild. A computer expert can treat your computer to recover from the attack based on the level of infection and the type of malware. However, the first thing you should always do in case of an attack is to isolate the infected device. This limits the attack from spreading to other devices on your network.
Many types of malware exist and are in use daily by malicious the world’s malicious hackers, nation-state actors and other cybercriminals. All of them require your business to have stringent cyber security measures and processes to prevent, detect, and remove them from your IT systems.
Remember, a single crack in your cyber defenses can make your organization fall like a house of cards to a malware attack.



![A 6-Minute Overview of the PCI DSS Requirements [For PCI DSS v.4.0]](https://cheapsslsecurity.com/blog/wp-content/uploads/2022/12/pci-dss-requirements-v4-370x245.jpg)