McAfee Labs reports observing more than 1.4 billion malware detections in Q4 2020 — and that number that doesn’t include Q1-Q3 2020 data! We’ll explore 10 types of malicious software you need to know to protect yourself in 2021.
The threat of malware is growing every minute. McAfee Labs reports observing 648 malware threats per minute in Q4 2020 in their Threat Report 04.21. As you can imagine, knowing the different types of malware and exploring some real-world malware examples will help you understand how better to protect yourself and your organization from these pernicious threats.
Malware is a blanket term for all software programs and code that people create with malicious intent. A layman might find the word “computer virus” more relatable, but a virus is just one type of malware. Not all types of malware are viruses. (We talked about that in another recent article on the differences between viruses and malware.) So, what are the different types of malicious software? Let’s look at some of the types of malware and how they affect us.
10 Types of Malware That Can Affect Your Business
Malware is a broad categorical term that encompasses many types of malware — as such, segregating it into a handful of specific types is difficult. That’s because malware categories sometimes overlap and some cybercriminals use multiple types of malware to achieve their goals. To create a botnet, for example, bad guys can use various types of malicious software and code to infect and control devices (trojans, viruses, keyloggers, etc.).
Keeping all of this in mind, let’s look at the fundamental types of malware and how cybercriminals use them.
1. Ransomware
Ransomware is a type of malware that prevents you from accessing your data and/or devices until you meet an attacker’s specific demands. Typically, the bad guy demands a ransom (typically a cryptocurrency payment in exchange for a decryption key or code that will free of the victim’s compromised resource(s). But even if the cybercriminal receives the ransom, they may not follow through with providing the victim with a valid decryption key or code.
This type of cyber-attack is gaining momentum in the digital world. This, no doubt, is largely thanks to the successful monetization of ransomware attacks and the availability of ransomware-as-a-service operations. In their April 2021 report we mentioned earlier, McAfee observed a 69% increase in new malware variants from Q3 to Q4 2020. Among ransomware attacks, some malware families took precedence over the others.
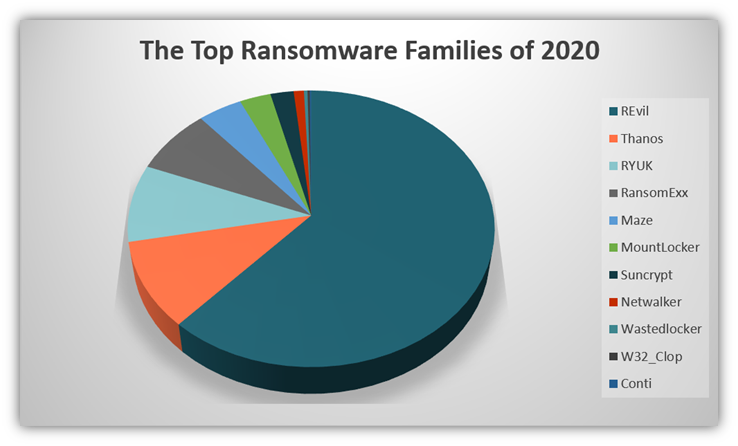
The following chart shows the most observed ransomware families in the year 2020:
The FBI’s Internet Crime Complaint Center (IC3) reports that they saw an increase in ransomware attack reports against the U.S. public over the last three years. Moreover, the ransom amounts demanded also increased in 2020. The chart below shows the number of complaints and losses complainants suffered over the last three years:
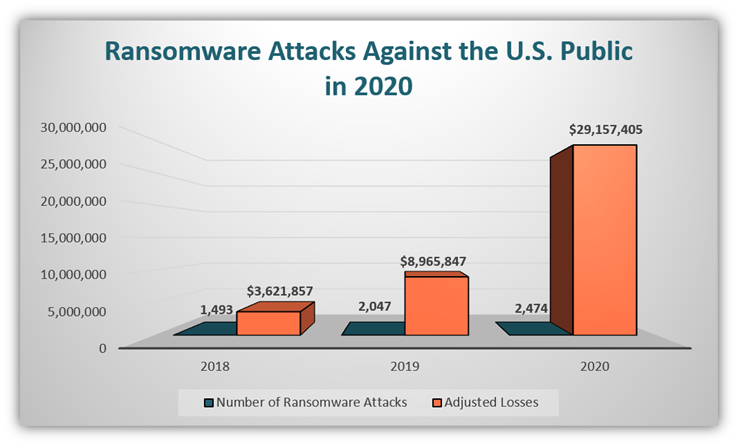
The chart shows the data of the three most recent years recorded by the IC3 team. The chart explicitly indicates that the rise of the average loss due to ransomware is much higher than the number of ransomware attacks. This clarifies that the losses incurred by the victims due to ransomware are rising.
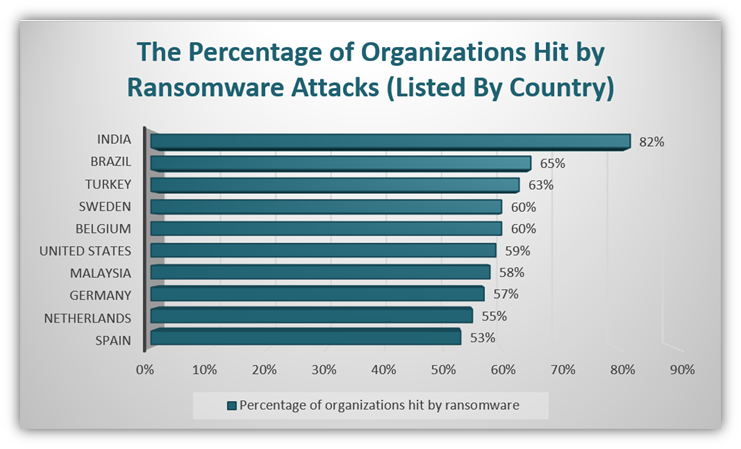
The State of Ransomware 2020 report by Sophos ranks the U.S. sixth globally for the highest rates of known ransomware attacks. The following chart shows the top 10 countries where Sophos reports organizations were hit by ransomware in the previous year:
An Example of a Ransomware Attack: REvil
The data shows the widespread reach of ransomware as malware. Would you believe me if I told you that the tech giant Acer was recently hit by a REvil ransomware attack? (Although it’s important to note that BleepingComputer reports that Acer hasn’t openly admitted to the incident involving ransomware. They just said that they observed “abnormal situations” within their IT systems.)
In this situation, BleepingComputer also reports that cybercriminals allegedly demanded a ransom of $50 million. The threat actors also published extracts of the company’s financial data on REvil ransomware site.
Check out this article on ransomware to learn more about this type of malware, how it works, and how to prevent it.
2. Computer Viruses
A computer virus is a malicious code that attaches itself to critical hard drive files or executables. When a victim runs the infected files or installs an infected program, they inadvertently activate the virus.
A virus is, perhaps, the most recognizable kind of malware in the general public. Whenever a normal person (non-geeky kind) talks about any kind of malware, they often use the terms “virus” and “malware” interchangeably. Although a virus is a type of malware, you now know that malware includes many different types of malware, including but not limited to viruses.
Because computer viruses typically attach themselves to legitimate programs and files, they’re difficult to detect and remove. A micro-organism requires a human host to infect and spread further. In much the same way, a computer virus also needs a human to install or run the infected program/file to infect the system and spread to other computers. As the virus infects other files, the only way to clear them out is to remove the infected programs or files from the system or quarantine them.
But how prolific are computer viruses? The FBI IC3 reported 1,423 cases of computer malware/scareware/viruses, causing $6.9 million in damage to the U.S. public in 2020 alone. (Note: this estimate does not include ransomware, which the IC3 categorized separately in their report.)
An Example of a Well-Known Computer Virus: Thanatos
MalwareHunterTeam discovered a ransomware-style virus called Thanatos in 2017. This virus could enter your IT systems through seemingly harmless sources, including:
- Spam emails,
- P2P (peer-to-peer) networks like Torrent or eMule,
- Unofficial software download services on free download sites, and
- Fake software updates.
Once the virus enters your system, you’d observe the following changes:
- The infected files have “.THANATOS” as an extension, and you can’t open those files because they’re encrypted.
- A file named “README.txt” would appear on your desktop, naming the ransom amount ($200 in Bitcoins) and payment directions.
Unfortunately for their targets, the cybercriminals behind Thanatos wouldn’t bother to decrypt their data even after they paid the ransom. The only way out of this situation is to maintain regular backups that you can rely on in case of infection from Thanatos (or another type of malware).
3. Computer Worms
Next on our list of the types of malware you should know is a type of malware whose name belies its danger. A computer worm is a malicious code that attaches itself in a program, executables, or critical hard drive files. Contrary to a computer virus, a worm is designed to run and self-replicate without a trigger, enabling it to send itself to other systems via email or networks to infect them.
Although they’re similar to viruses, worms are even more formidable. Unlike a virus, a worm can spread without a host. While a virus needs a host (like a browser, word processor, or executable) to replicate, a worm can self-replicate without requiring anything to trigger it. It can run, copy, and send copies of itself to other victims on its own.
Worms are some of the most dangerous and costly types of malicious software. Worms can weigh down your device or network by doing one or more activities:
- Modify, delete or steal your files and data,
- Install backdoors to allow hackers access to your device or other IT systems, and
- Replicate itself or inject other malicious software onto network-connected devices.
Some of the well-known computer worms include:
- Stuxnet,
- Wannacry,
- Cryptolocker,
- ILOVEYOU,
- Code Red, and
- Slammer.
A Well-Known Example of a Computer Worm: Mydoom
HP Tech Takes regards Mydoom among the worst malware outbreaks in history. Mydoom is a worm that cybercriminals embed in email attachments to spread via infected systems’ users’ email contacts. Mydoom.A was first discovered and then Mydoom.B followed soon after. All devices infected with Mydoom.A were automatically infected with Mydoom.B without the need for additional emails.
Cybercriminals used Mydoom-infected systems to launch a DDoS (distributed denial of service) attack against the websites of the SCO Group and Microsoft on two days in February 2004:
- Systems infected with Mydoom.A launched attacks against sco.com on Feb. 1.
- Systems infected with Mydoom.B launched attacks against microsoft.com on Feb. 3.
According to Computer World, both the SCO Group (now Xinuos) and Microsoft offered six-digit bounties to anyone who could give any information on the worms’ creator. Mydoom was reportedly responsible for slowing down internet speeds because of the bandwidth required to carry out the DDoS attacks.
At its peak, Mydoom self-propagated in one of every 12 emails sent and HP Tech Takes estimates the combined losses resulting from both Mydoom variants in 2004 was $38 billion. After more than 16 years of the creation, Mydoom is still active. Unit 42’s report indicates that it sent 465,896 emails between January and June 2019.
4. Trojans
Trojan horses are types of malware that masquerade as legitimate software programs, software updates, and files. Using a disguise allows a trojan to enter your device or network by essentially walking through the front door. Some trojans are hard to detect, which makes them difficult for traditional antivirus tools to remove. But once it enters your IT system, the trojan can take total control and may even use your device’s resources as part of a larger botnet.
First mentioned in the Greek poem Odyssey, the Trojan Horse story is one of the classics known to all regardless of geographical borders. It describes how the Greek soldiers won the war for the city of Troy by hiding in a giant wooden horse offered as an offering to the goddess Athena. The 10-year war finally came to an end because of the ruse.
Whether the Trojan horse is a myth or a fact is best left to historians, but computer trojans are definitively real and equally frightening. Trojan malware is much like this Trojan Horse of old — it relies on trickery. Threat actors disguise trojans as legitimate code or software programs to trick people into downloading and installing them.
Like a virus, a trojan needs the victim to execute the host code for it to activate. Remote access trojans (RATs) are variants of trojans that are popular among cybercriminals. These types of malware allow threat actors to control victims’ devices remotely and, without their knowledge, will move on to infect the rest of their network. Trojans are so common and easy to write that they’re readily available on the dark web at low prices.
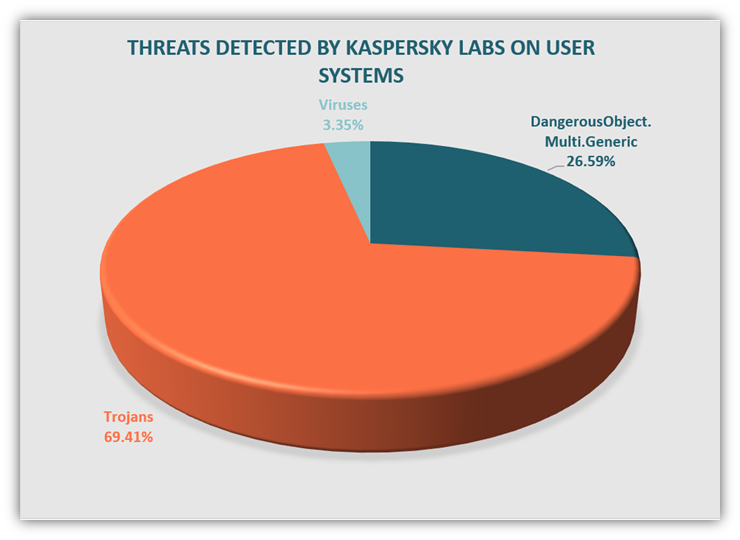
Kaspersky Labs identified the top malicious threats detected on user’s computers. Their data shows that the total number of trojans residing on users’ systems far exceed any other types of malware:
An Example of a Well-Known Trojan: Zeus
Zeus, also known as ZeUs or Zbot, is a notorious trojan variant that cybercriminals used to steal banking information to deploy ransomware such as CryptoLocker. This typically involved the use of fake technical support pop-up ads that would appear on users’ devices. The ads would make users believe their devices were infected with malware. However, their devices weren’t infected until they clicked on the misleading pop-ups!
This type of malware infected countless computer systems, including those belonging to government organizations and companies such as:
- Amazon,
- NASA,
- U.S. Department of Transportation (DoT),
- Monster.com, and
- Cisco.
In October 2010, the FBI announced that Zeus had successfully infected computers in eastern Europe. Zeus can still infect weak systems around the world. There are many other Trojans built on the basic code of Zeus that are active today.
5. Fileless Malware
Number five on our list of the types of malware you should know is a bit tricky and misleading. Norton describes fileless malware as a memory-based malware that “piggybacks” on legitimate programs, applications and scripts. That’s because, unlike traditional malware that relies on executable files to house its code, this memory-based type of malicious software only uses a dropper to get its party started initially.
Fileless malware resides in the memory and runs in the memory without making any apparent changes to the system files. Because it doesn’t rely on files and leaves no footprints, it’s difficult to detect remove. Normally, anti-malware software scans suspicious files to protect the computer. Threat actors stay under the radar of anti-malware software by not adding new files to the host device.
Many types of fileless malware take advantage of Microsoft Windows PowerShell, a legitimate tool used by administrators for configuration management and task automation. PowerShell becomes the bridge through which the actors can gain access to infected device(s).
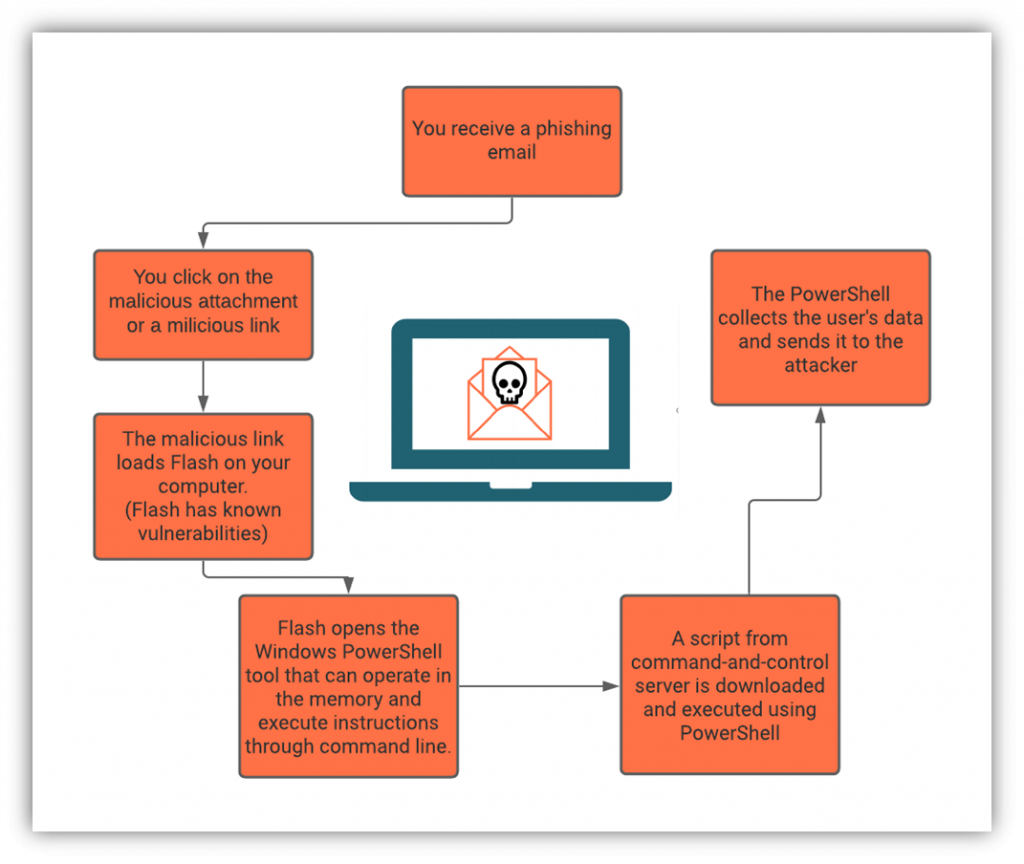
Let’s break down a typical chain of events in a fileless malware attack:
- A cybercriminal uses social engineering techniques to enter the victim’s computer (such as a through a phishing email or a malicious app link)
- Once the victim clicks on the attachment or link, the malware attaches itself to one or more whitelisted programs.
- The malware downloads and installs Flash to access your PowerShell.
- Your PowerShell is then used by a command-and-control (C&C) server to download a script onto your device.
- PowerShell now acts as a tool to collect the user data and send it to the bad guys.
Here’s a quick visual example that demonstrates how a fileless malware attack works:
An Example of a Fileless Malware Attack: Cobalt Kitty
Let’s explore one fileless malware attack example to give you greater clarity. A recent attack, called Cobalt Kitty, was carried out on a global corporation based in Asia by OceanLotus Group. According to information published by Cybereason, it appears this attack involved common elements of fileless malware attacks:
6. Adware
Adware, also known as ad-supporting software, is a type of malware that developers use to displays ads on your device without your permission. It’s an easy way for them to make money through the revenue they receive from advertisers. While some variants of adware are harmless, others can be used to deliver other types of malware.
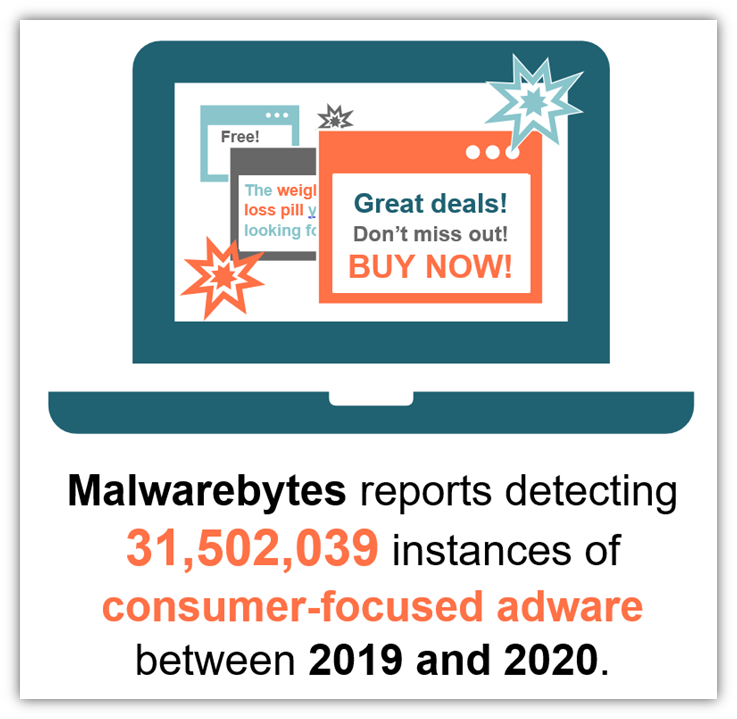
Avast reports that mobile malware made up 72% of the adware they observed in the data gathered between October and December 2019.
Adware tracks your online searches and just about everything you do online to create a database. They can then either use this database or turn around and sell it to any interested party for a price. Advertisers use your data to send you personalized adverts. The major drawback of adware is the loss of privacy. Even though your keystrokes are not captured, you lose all your privacy due to adware.
The advertisers pay for adware based on:
- Pay-per-view: Every time an advert is shown to you, the advertiser pays — even if you don’t click on it.
- Pay-per-click: In this method, the advertiser pays only when you click on the ad.
- Pay-per-install: The advertiser will pay every time the bundled software is installed on your device.
Check out this article on adware to learn more about this type of malware, how it works, and how to prevent it.
7. Cryptojacking Malware
Cryptojacking malware is a type of malicious software that cybercriminals use to hijack your device’s processing and power resources. Why? As the name would imply, it’s to mine cryptocurrencies or even steal other people’s cryptocurrencies from their wallets. This malware, which is designed to remain hidden and causes your device to operate as part of a larger botnet, operates on your device without your knowledge to carry out what’s known as cryptojacking attacks (i.e., malicious cryptomining).
Cryptomining is frequently a blockchain-related process that involves using computers to solve critical mathematical equations. When successful, it results in the generation of a cryptocurrency unit. But cryptomining requires vast quantities of power and computing resources — far more than the average cybercrimimal has access to on their own. As a way to compensate, cybercriminals will use cryptojacking malware to infect other people’s devices and use their resources without the device owners’ knowledge.
When cybercriminals activate the cryptomining programs on users’ infected devices, the users may experience sudden hikes in their power and data usage. Their devices will become slower and might have a shortened life. A typical cryptomining farm can include a collection of devices, including:
- Mobile phones,
- Laptops,
- PCs,
- Servers, and
- IoT devices.
Cryptomining apps are generally categorized under PUAs (potentially unwanted applications) or sometimes fall within the category of trojans. A more advanced form of cryptomining uses your browser to carry out the task. The following picture shows the process of cryptojacking.
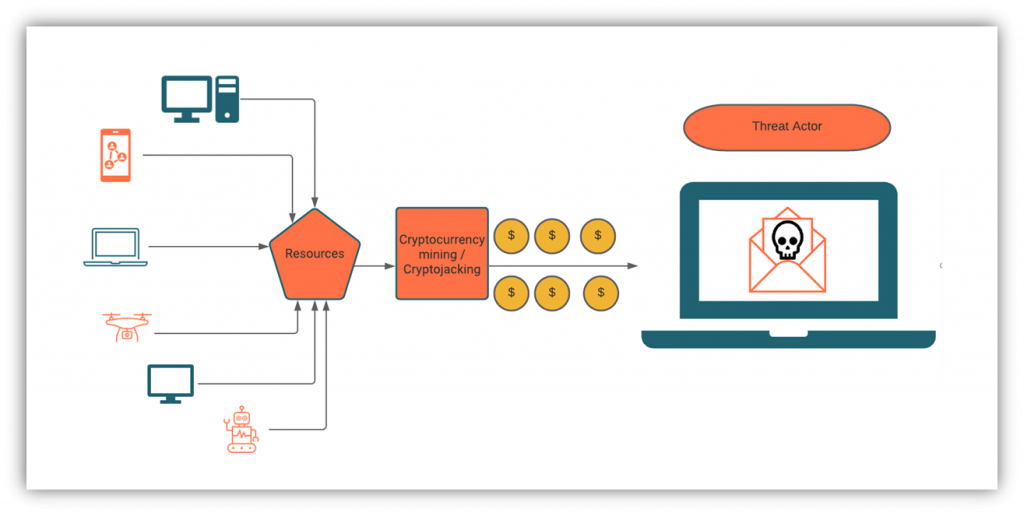
As you can see in the above figure, all kinds of devices that can be connected to the internet are used by cybercriminals to launch cryptomining malware. For obvious reasons, the criminals will keep all the cryptocurrency mined from the attack while the victims will be left with gigantic electricity and data bills along with the damage to their devices.
An Example of Cryptojacking Malware: Malicious AMIs
Researchers at the incident readiness & response company Mitiga sounded an alarm in August 2020 when they discovered malicious crypto-miner code embedded within an open-source Amazon machine image (AMIs). The AMI, which was published in the Amazon Web Services (AWS) Marketplace where other users could find and use them, would cause EC2 server instances that use the AMI to mine Monero coins (cryptocurrency) for them. Mitiga warned AWS users only to use AMIs from trusted sources.
8. Botnet Malware
Botnet malware is a category that describes different types of malware that infect devices with the purpose of controlling them as part of a larger network. This can include trojans, viruses, worms, and some other types of malware.
The infected devices that comprise a botnet are known as zombies or bots. Cybercriminals use these infected devices to carry out a variety of large-scale, malicious attacks — everything from attacking websites to stealing data. Some botnets are even available for other cybercriminals to rent or use as a service-for-hire.
- DDoS attacks: When bad guys want to carry out large-scale cyberattacks, they often use botnets to do so. In a traditional DDoS attack, these devices act as puppets that the cybercriminals use to overwhelm their targets’ servers with traffic. Voila! The targeted servers crash as a result.
- Brute force attacks: In this type of attack, bots use username-password combinations to try to gain access to accounts on different websites, services or web apps. All the bots have different sets of combinations. The idea is to guess the correct username and password by trying out enough number of combinations.
- Botnet-as-a-service: Cybercriminals who want to monetize their bot network in other ways sometimes rent out the botnets or hire out their botnet services to others on the dark web. This means that these networks of infected devices can work for virtually anyone who hires them.
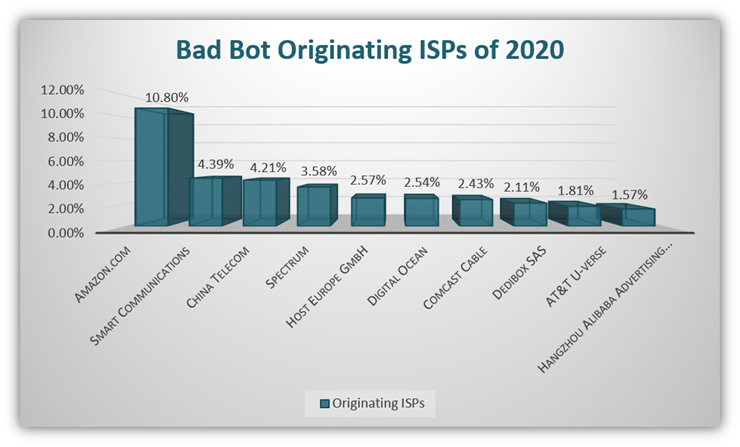
Bad Bot Report 2021 by Imperva found that the United States was the country where 40.5% of the bad bots originate. The below figure shows the top 10 bad bot originating ISPs of 2020 according to the same report:
Some well-known botnet malware variants include:
- Mirai,
- Qbot, and
- Kaiten.
An Example of Botnet Malware in Action: Mirai Botnet
The Mirai botnet is a botnet of devices that are infected with the Mirai malicious code. Mirai, which means “Future” in Japanese, is responsible for many seemingly futuristic cyber attacks. For example, the Mirai botnet was responsible for bringing down much the internet in the U.S. via a large-scale DDoS attack back in 2016.
In the attack, cybercriminals used the Mirai botnet to coordinate and carry out the massive, targeted attack on servers controlled by Dyn. The company, which was responsible for controlling much of the internet’s DNS infrastructure, faced an estimated 1.2Tbps DDoS attack.
9. Rootkits
Rootkits are remote access tools (RATs) or software that provide remote administrative access to a user’s device — with or without their knowledge. As a one of the types of malware we’ll cover in this article, just know that rootkits are stealthy; they can modify files and hide other types of malicious software within your device. Because they can conceal themselves within your OS or the antivirus tools that you rely on to find them, this makes rootkits incredibly difficult for many tools to detect.
Cybercriminals typically pair rootkits with two other tools to help them deploy:
- Dropper — This is the executable that installs the rootkit. Cybercriminals often deliver malicious links and files to transmit droppers,
- Loader — This is the nasty little sucker that installs the rootkit onto a target device or IT system.
There are several different types of rootkits:
- Hardware rootkits. This type of rootkit, also known as a “firmware rootkit,” uses hardware (such as your device’s hard drive) or even your BIOS to gain a foothold in your system. It alters your device’s firmware and allows cybercriminals to steal data and monitor your behaviors.
- Bootloader rootkits. This type of rootkit, also sometimes called a “bootkit” rootkit, affects the bootloader of the victim’s computer. The bootloader is what tells your device how to load its operating system. This means that whenever you restart your device, it automatically consults the bootloader and, therefore, loads the rootkit as well.
- Memory rootkit. This rootkit hides in your computer’s random access memory (RAM). Although this rootkit will disappear once you reboot your system, it will carry out malicious activities in the background without your knowledge in the meantime.
- Application rootkits. This rootkit, also known as a user rootkit, operates at the application layer and affects your system libraries. As such, it can swap your device’s standard files with rootkit ones and attach itself to the programs you likely use daily. This rootkit gives bad guys access to these programs without you being any wiser.
- Kernel mode rootkits. These type of rootkits affect the very core of your computer systems and can change how your devices function. They have access to your system through the very core and, hence, they can steal your personal information easily.
This remote access tool can be useful in many ways. But in the hands of the wrong person, this useful tool becomes a weapon. A cybercriminal can use a rootkit to manipulate a device by attaining administrative access. So, while you go about your business on the device, you’ll be unaware that a rootkit is lurking in the recesses of your system, making changes and collecting data.
An Example of a Real-World Rootkit in Action:
Remember the Stuxnet we mentioned earlier? Stuxnet was developed by the U.S. and Israel that targeted the centrifuges at Iran’s nuclear facilities more than a decade ago. The goal was to cause those systems to malfunction while displaying data that led its operators to believe it was functioning normally.
So, if Stuxnet is a worm, why are we talking about it here? It’s because this worm relied on multiple rootkits to conceal its presence and activities so it could operate without detection.
10. Spyware
Last but not least on our list of malicious software… Spyware is a classification of malware that can be used for neutral or malicious monitoring purposes. It overlaps with some other types of malware, such as trojans and adware, and includes many types (such as keyloggers and password stealers to browser hijackers and banking trojans). Its overall purpose is to track your online and offline activities and collect sensitive data cybercriminals can use.
Companies use spyware to keep track of the employees during working hours. However, criminals use this for their own benefit to spy on unsuspecting users and to collect their information, including:
- Account login credentials,
- Credit card details,
- Identity documents,
- Account PINs and OTPs,
- Browsing habits, and
- Email addresses.
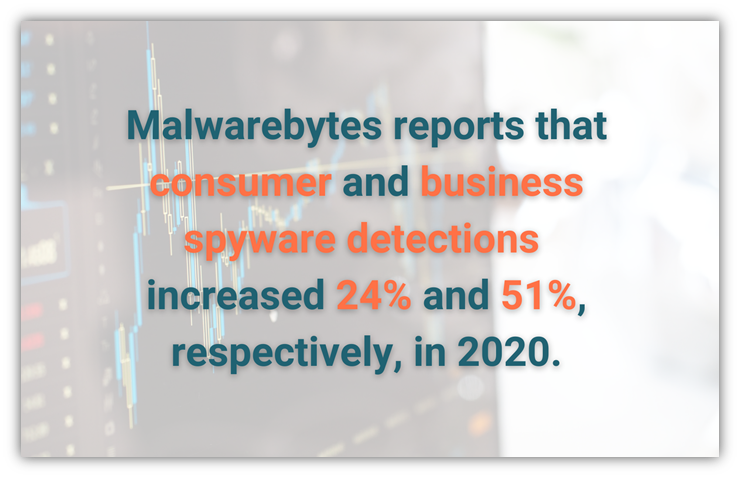
Malwarebytes observed that consumer spyware detections rose 24% from 1.96 million cases in 2019 to 2.43 million in 2020. On the other hand, business spyware increased 51% from 292,525 in 2019 to 440,368 in 2020 according to the same report. Of course, the information collected through spyware is used to commit other crimes, including:
- Identity theft,
- Credit card cloning,
- Hacking email accounts and websites,
- Selling sensitive or proprietary information to competitors, and
- Selling login credentials to third parties.
An Example of Real-World Spyware in Action
Remember how we mentioned earlier that not all spyware is developed or used only by cybercriminals? FinFisher (aka FinSpy) is a type of spyware that a German IT company developed outside the shadows. It primarily targets mobile devices but does also have a desktop version that targets multiple operating systems.
This type of spyware gives a bad guy almost unfettered access to an infected device. Kaspersky reports that FinFisher allows threat actors to monitor and records a wide variety of information on a compromised device, including the device’s:
- Physical location,
- Contacts and call histories,
- VoIP calls and phone calls it makes or receives,
- Incoming and outbound SMS text messages and instant messages, and
- Mobile app communications and file transmissions.
Final Thoughts on the Types of Malware
Whether it’s stealing data or controlling users’ devices, different types of malware serve various purposes for cybercriminals. And as long as there are bad people who have malicious intentions, then there’s likely always to be uses for nefarious software and code. The best way to protect yourself is to:
- Implement reliable cybersecurity tools to protect your network, user devices, and other endpoints.
- Keep your software, hardware and other resources patched and up to date.
- Teach your employees to recognize threats and to not engage with malicious URLs and emails.
- Avoid open-source software, AMIs, and code from unknown or untrusted sources.
- Only download apps and updates via official sources (such as manufacturer websites or Google Play and Apple App stores).





