Malwarebytes reports that adware was the top consumer category of malware detected in 2020. Although the number of adware detections fell 23% from 41.1 million in 2019 to 31.5 million in 2020, adware maintained its top position in MacOS malware detections.
What is adware? Although it’s considered to be one of the least malicious types of malware, the reality is that adware isn’t just pop-up ads. At its core, adware is a way for shady companies (or cybercriminals) to secretly gather data about you and your online behaviors so they can target you with benign or malicious ads! Regardless of whether you use a PC or a smartphone, or which operating systems (OSs) your devices use, adware can still affect you and your business.
In this article, we’ll give you a more in-depth adware definition and breakdown of what this type of malware entails. We’ll also share some adware prevention tips you can use to protect your business against this type of threat.
What Is Adware? An Adware Definition

Adware, which is the common term for advertisement-supporting software, monitors your online activities to serve up targeted ads. This can cause your device to suddenly start displaying a bunch of advertisements that seemingly take over your screen. In many cases, experts consider adware a type of malware because it’s intrusive and often operates without the victim’s knowledge.
Adware is a way for unscrupulous advertisers and cybercriminals to make money off you. They use this tool to infiltrate your machine or browser to track your online activities and display ads based on that data. It’s kind of like having a shady person with a camera following you around all the time, recording everything you do. While in some situations it’s “just” an annoyance, in others it can be dangerous and invasive.
As you can imagine, adware can have a significant effect on your device’s performance. Whenever you go online, pop-ups and other unwanted ads may bombard you. And while many of the ads are just annoying, others may contain malware or link to malicious websites. Every time you work online, there will be tons of pop-ups in your browser.
Another harmful effect of adware is slower internet browsing speeds. Adware (and all of the pop-ups it creates) eats up your data and bandwidth, thereby affecting your work capabilities. Your personal choices and interests are sent to these shady advertisers for marketing purposes via these ad-promoting malware. Hence, you will find that the ads displayed are customized for you.
What Are the Main Types of Adware?
Different companies and resources break down adware in different ways or by using different classifications. For example, here are a few of the ways Security.org classifies adware:
- Legitimate adware: This type of adware requires you to consent to ads or software promos. You might get a free demo or some other benefit for agreeing. This is the legal and ethical way to go about advertising.
- Potentially unwanted applications (PUAs): Then there is PUA. The PUA includes everything you had not agreed to yet you still get (much to your chagrin). There are grey areas where PUAs can be called legal. This is where the advertisement has an unknown malware embedded in it. However, sometimes they are totally illegal, malicious, or abusive. The PUA can be called illegal if you have not consented to be the subject of the advertisement or if the advert contains actual malware.
- Browser hijackers: Browser hijackers often affect your default browser, changing your home page and search settings without your knowledge.
Different operating systems require different programming, hence why different types of adware affect users’ systems differently. Some types of adware are device-specific, whereas others work universally across all kinds of devices or operating systems.
6 Real-World Examples of Adware
Here are five real-world examples of adware that pose threats to users worldwide:
- FakeAdsBlock is malware that pretends to be an ad blocker app but, ironically, displays high volumes of ads to Android device users instead.
- DeskAd is a malicious malware that’s marketed as ad-supported software to provide targeted advertisements. After starting as a relatively harmless adware, DeskAd morphed into something far more sinister. It would add buttons, toolbars, and links to your browser and, over time, redirects users’ web requests to malicious websites.
- Fireball is a Chinese adware operation that infected more than 250 million Windows and MacOS computers globally. Dubbed Fireball, this browser hijacking adware turns browsers into ad revenue-generating zombies. It also gave the cybercriminals the ability to run whatever malicious code they want on victims’ infected devices or infect them with other types of malware. Fireball is largely spread by bundling it with other apps, so when users download their intended applications, they also unknowingly get Fireball, too.
- HiddenAds is a family of adware-deploying trojans that hides within other apps, most commonly gaming apps. Malwarebytes describes it in their 2021 State of Malware Report as a “close cousin” to FakeAdsBlock. In October 2020, the security company Avast discovered almost two-dozen apps containing the adware in the Google Play Store. Avast researchers report estimate that more than seven million users downloaded the apps prior to their removal from the Play Store.
- MobiDash is a type of adware that Malwarebytes describes in their 2021 report as hides “within the code of repackaged legitimate apps.”
- Shlayer is a family of adware dropper trojans that target MacOS devices and systems to install adware variants. This malware has been an ongoing issue for MacOS users. In April 2021, Apple released a fix for a zero-day exploit (CVE-2021-30657) that allowed the Shlayer malware to bypass their OS Gatekeeper security measures. This family of malware was recognized by Threatpost as the “No. 1 Threat for Mac” in 2020.
How Does Adware Work?
We’ve already touched on some of this a bit, but there are a few main ways that adware can infect your device(s):
- You can accidentally download and install adware hidden within or bundled with free software applications.
- Adware also can enter your system through other types of malware such as trojans and browser hijackers.
- You can pick up adware from visiting malicious websites and viewing “malvertisements” (malicious ads) that use auto-downloaders.
Let’s explore these ideas a little more in depth.
Peer-to-peer sharing of free software is a way in which adware enters the computer system. Ticking the wrong permission box while installing your intended program might lead to installing adware as well since they sometimes come as a bundle. Furthermore, some developers use adware to fund their open-source programs. While using such programs, the victims download the adware. Once the adware is in your computer, it will find a niche where it cannot be found among legitimate programs.
Cybercriminals and adware operations are also known to use trojans and browser hijacking malware as a way to deploy malicious payloads onto users’ devices. This is another way that cybercriminals can get adware onto unsuspecting users’ devices to generate ad revenue or direct them to malicious websites.
When a person visits a malicious website, it downloads adware in the background without the user’s knowledge. After the adware installs, it starts monitoring your activities and will show you advertisements and pop-ups that sync with your preferences. Often, your internet browsing experience will get affected by the installation of adware.
Why Cybercriminals and Advertisers Use Adware
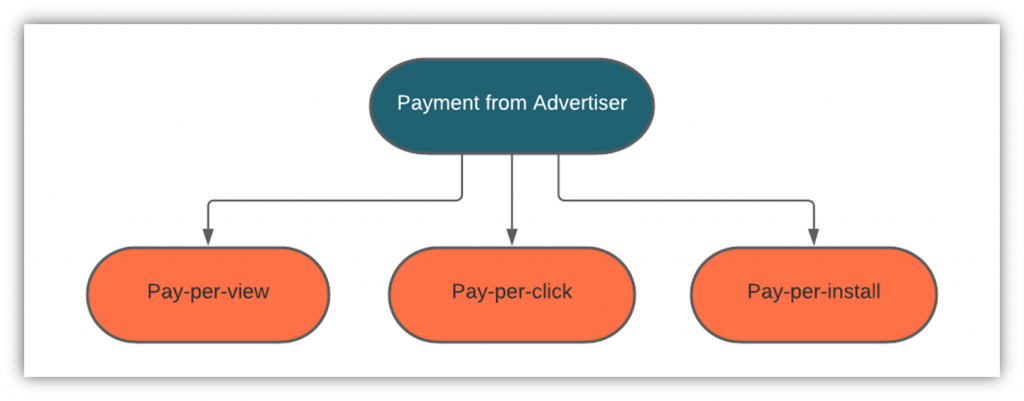
Adware generates revenue for the developer in three different ways. An advertiser will pay the developer based on the number of times their ad is viewed, clicked, or installed (in case of an app or game). The cost of an ad depends on the number of views or clicks it receives. Also, search engines like Google have auctions to sell digital ad spaces to advertisers. A lot depends on the type of goods/services sold by the advertiser. Let’s quickly explore how all of this works:
Pay-Per-View/Cost-Per View
Advertisers might just wish to tease the customers by showing them their ads multiple times. Hence, they pay a certain sum every time the advertisement is displayed on the user’s screen. It does not matter whether the customer clicks on the ad or not. This method is called pay-per-view.
Pay-Per-Click
Sometimes the contract between the developer and the advertiser is such that the advertiser will pay the developer every time the user clicks on the advertisement. This method is known as pay-per-click because it only counts how many times users click on the ad regardless of how many times users view it.
Pay-Per-Install
This method is generally used for ads promoting games, apps, or other programs. When the user installs the app, the advertiser pays the developer.
The following figure is a representation of the payments made by the advertiser:
How Can You Protect Yourself Against Adware?
So, how can you prevent yourself from becoming a victim of malicious adware? Well, there are a few simple things you can do regularly to prevent your device from the influx of adware:
- Use antivirus and anti-malware tools. By installing reliable antivirus or anti-malware tools and keeping them up to date, you can add a layer of protection to your device (and your network as a whole). These tools help you avoid installing adware onto your device (such as when you click on an infected website link by mistake) and enable you to scan your computer for malware. If it locates any, you can also use them to quarantine or remove the adware.
- Read before you accept. It is a general practice to accept all the conditions of an app or software without even reading them while installing it. A person does not even realize what permissions he is giving to the app and then blames it for spying on him. That said, the makers do not let you install the apps if you don’t accept all the conditions and grant all the permissions to them. Hence, you should always carefully weigh an app’s benefits versus its permission requirements before granting or accepting its terms and conditions.
- Download from reliable sources only. Download software, apps, or other files from reliable platforms and sources only. This includes official developer and manufacturer websites, official app stores (such as Google Play and Apple App Store), etc. Peer-to-peer file-sharing platforms and sites are notorious for hosting adware-infected files.
- Avoid “freeware” and “shareware.” Freeware or shareware is often a source of adware, and so are pop-up ads and notices. Hence, one should refrain from downloading or even clicking on them. Beware of free apps that are copies of commercial apps you have to pay for. Chances are, the free apps are home to malware, and your system will be at risk by downloading them.
- Use a reputable ad blocker. An ad blocker will prevent adverts from displaying on your browser. This will reduce your chances of accidentally clicking on them and infecting your computer.
- Buy devices from reputable sources. Sometimes, adware is pre-installed on the devices bought from fishy sources. For saving a few bucks, you might be making yourself an easy target for criminals.
Final Words on the Topic of Adware
Conclusively, adware is a potentially malicious software basically developed for marketing. Although annoying, the adware can be neutral in effect. However, if malicious code is inserted candidly in the adware, it can have harmful effects as well.
Prevention of adware is much easier to achieve than its removal after the fact. As such, always be mindful while accepting cookies or giving permissions while installing programs. And, of course, be sure to download apps and games from authoritative sites and platforms only. Taking a few extra moments to read the fine print or paying for a legitimate version of a software program can save you time, headaches, and the hassle of dealing with adware.



![A 6-Minute Overview of the PCI DSS Requirements [For PCI DSS v.4.0]](https://cheapsslsecurity.com/blog/wp-content/uploads/2022/12/pci-dss-requirements-v4-370x245.jpg)