What is the POODLE vulnerability and does it affect users?
POODLE is the acronym of “Padding Oracle On Downgraded Legacy Encryption”. It is a new SSL vulnerability discovered by Google researchers Thai Duong, Bodo Moller and Krzysztof Katowice’s. As per their report, if a hacker tries to attack a public hotspot using a Man-in-the-Middle attack, the POODLE vulnerability helps the hackers to downgrade a browser’s SSL version with older SSL 3.0 instead of the highly secured TLS version.
Today, a large number of servers and browsers are supporting SSL version 3.0 (SSLv3) and hackers are more than happy to exploit them by forcing them to downgrade the browser’s security protocol version. Even in case, the browser is trying to use an upgraded version, due to this vulnerability, it will be forced to use the old SSLv3.
How do I get rid of the POODLE vulnerability?
- The only solution to get rid of the POODLE vulnerability is disabling SSL 3.0 from browsers and servers.
- And as a precautionary step, users are requested to avoid using public hotspots, WiFi, or they should access these networks using a VPN (Virtual Private Network).
How to Disable SSL 3.0 in Different Web Browsers for Windows Users
1. Disable SSL 3.0 in Google Chrome
The Google Chrome team has decided to completely remove its support towards SSLv3 from all their client products.
Here are a few simple steps:
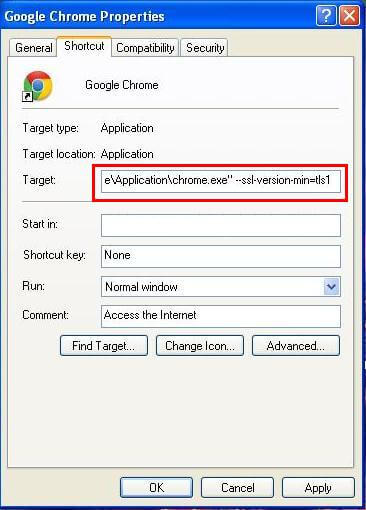
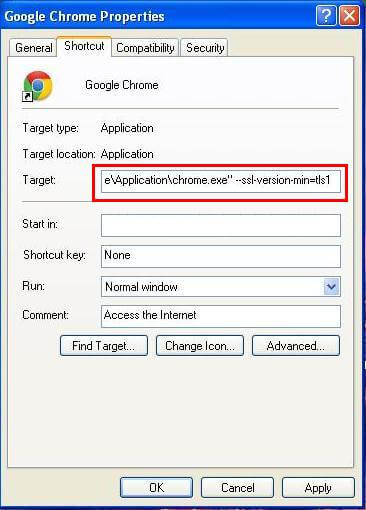
Step 1: Right-click on the Google Chrome icon and click on Properties.
Step 2: A new pop-up appears that shows information about Google Chrome Properties.
Step 3: Now in the Target Textbox after “\~\application\chrome.exe” write the following piece of code, including space:
--ssl-version-min=tls1
Your target text box should now look similar to this: “\~\application\chrome.exe –ssl-version-min=tls1”.
Step 4: Press ‘Apply’ and then click on the ‘OK’ button.
With this last step, Google Chrome is now free from SSL 3.0. After this, the browser will start rejecting SSL 3.0 certificates.
2. Disable SSL 3.0 in Mozilla Firefox
The Mozilla Firefox team has announced their decision to disable SSLv3 by default, which is set to release on November 25th, 2014. So, after updating the browser there shall be no need to perform the procedure of disabling SSL 3.0.
However, those who prefer not to wait until November 25, here is a step-by-step procedure to disable SSLv3:
To disable SSL 3.0 perform following Steps
Step 1: Open your Firefox Browser
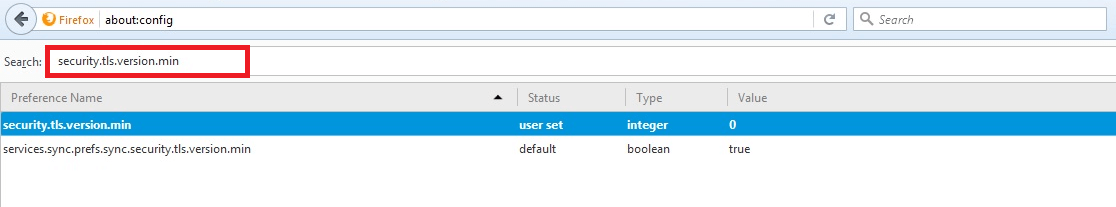
Step 2: In URL bar, write about:config & hit enter (to configure Firefox SSL settings)
Step 3: This might void your warranty! the alert will appear, now click on I’ll be careful, I promise! Button.
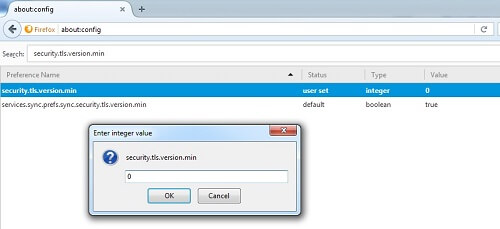
Step 4: In the Search box, type security.tls.version.min, now double click on the first result as security.tls.version.min.
Step 5: The integer value will be 0, now turn the value by 1 and press OK. (Minimum TLS version is 1.0)
Step 6: By setting up the integer value as 1 in security.tls.version.min, you have disabled SSL Certificate in Firefox.
After completing the above step, Mozilla Firefox will no longer accept SSL 3.0 certificates.
For more update on this Disable SSLv3 version, visit official firefox update.
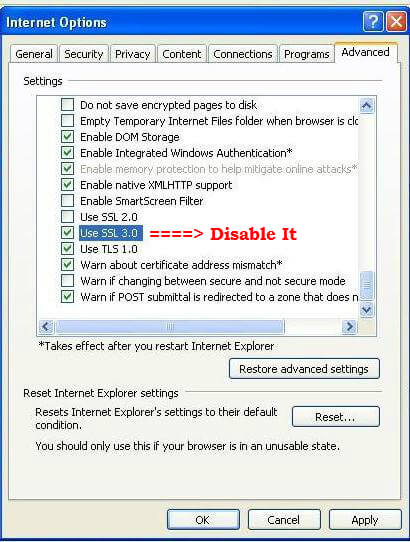
3. Disable SSL 3.0 in Internet Explorer/IE
Internet Explorer has not yet given an update about when they will discontinue their support for SSL 3.0. Therefore, users are left with no option but to take up the option to disable SSL 3.0 themselves. Here is the step-by-step procedure:
Step 1: In Run function of windows type Internet Options, or find it on the Tools menu and click open.
Step 2: Now, go to the Advanced tab, here is the Setting field.Go to the security section.
Step 3: Here you will find the checkbox of ‘Use SSL 3.0′ checked. Uncheck to disable it. Now, press Apply.
Step 4: Restart Internet Explorer. And with this step, the browser will no longer accept SSL 3.0 certificates.
Users across the world are concerned about affected web-browsers and compromised security due to the POODLE vulnerability. We will most definitely keep you posted about any new update on SSL version 3.0. However, if you have any query or suggestion on the related issue, please contact here.