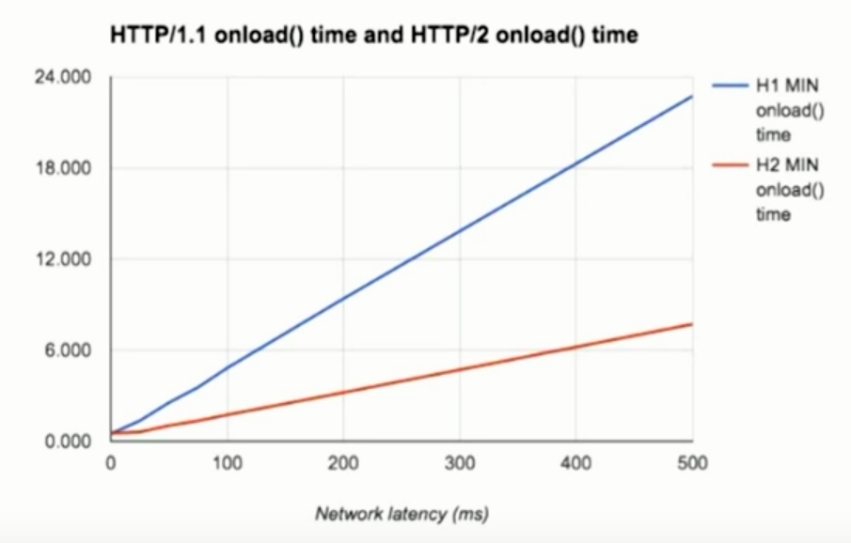
Bringing about a new alternative to performance hacks that don’t have developers bending over backwards to improve page loads speeds, IEFT’s Working group gave netizens HTTP/2 in 2015. HTTP/2 introduces significant improvements over the previous versions of the HTTP protocol, including but not limited to enhanced security features. Apart from removing the need for time-consuming performance optimizations, it is also resilient to header compression attacks that could, in turn, lead to session hijacking. It gives us a simplified yet efficient framework that is easier to parse, more compact, and less error-prone.
Limitations of HTTP/1.1
HTTP/1.1 is the protocol that has served us for around two decades and is not without its own merits. However, HTTP/1.1 has its drawbacks, which is why a new version was developed to overcome its flaws.
Drawbacks of HTTP/1.1:
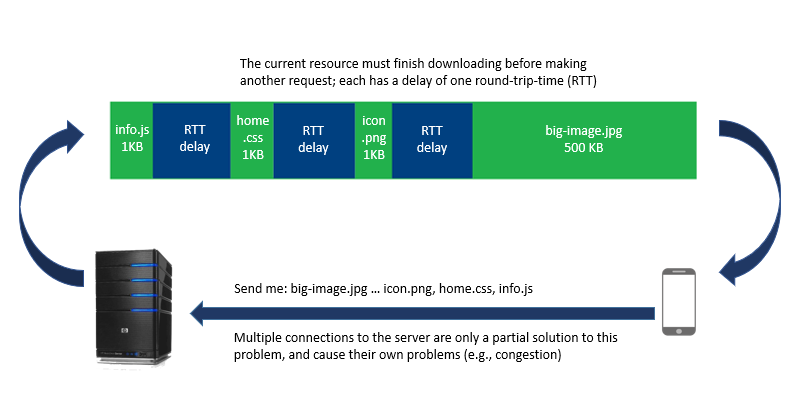
- Network latency due to multiple open TCP connections and optimization hacks
- Head-of-Line (HOL) blocking problem when input packets to the same destined output port get blocked either due to contention from other packets or due to output congestion (output buffer is full)
- Headers were sent repeatedly for every request leading to duplicate data over the wire creating redundancy
- Being a text-based protocol in the human-readable form introduces some inherent security weaknesses
- Persistent connections used in HTTP/1.1 consume resources even when idle and are vulnerable to denial of service attacks
- Developers used performance hacks such as domain sharding, image spriting, concatenating, etc. that created their own set of sub-optimization problems.
Advantages of HTTP/2
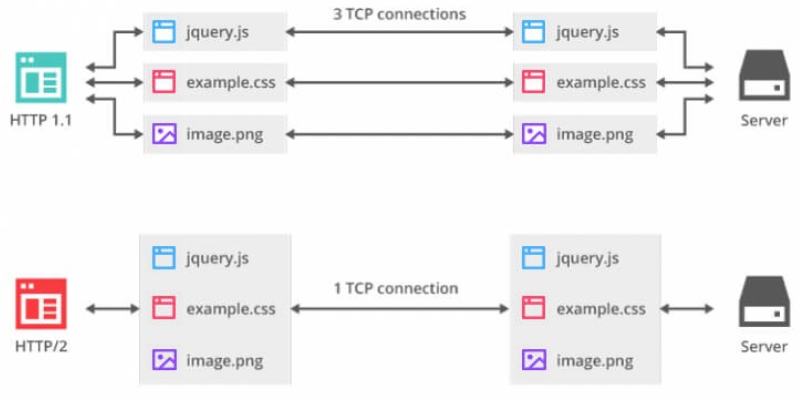
- Multiplexing: The binary framing layer allows HTTP/2 messages to be broken down into independent frames. Multiplexing interleaves the requests or frames, without head-of-line blocking (as seen in HTTP/1.1) and does so over a single TCP connection. Multiple requests can be sent over one connection with responses arriving out of order, eliminating the need to have more than one connection between client and server.
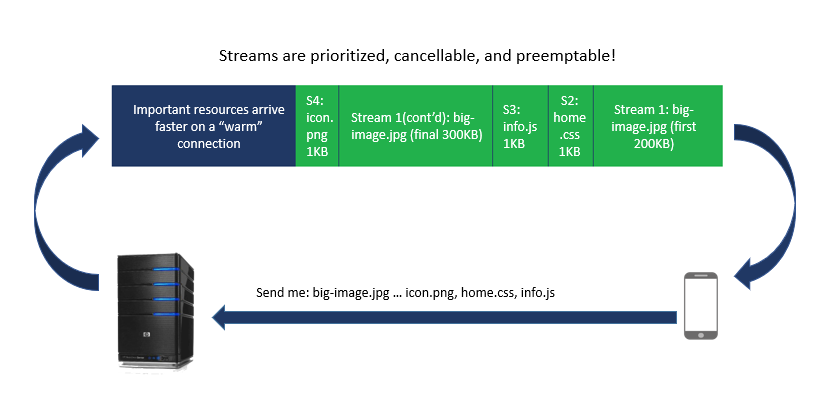
- Stream prioritization: Stream prioritization allows developers to allocate dependency levels according to which the streams get delivered to the client. This improves performance by serving only the resources required to render the page. The client constructs a prioritization tree that communicates to the server the order in which it would prefer to receive the responses.
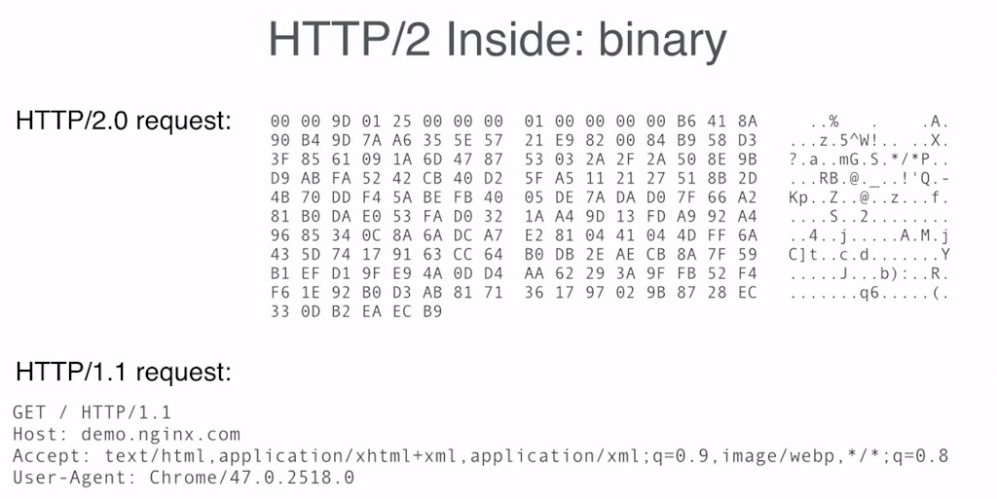
- Binary protocol: HTTP/2 is a binary protocol. Since only binary commands in the form of 0s and 1s are transmitted over the wire, it removes the security issues that come with text-based protocols.
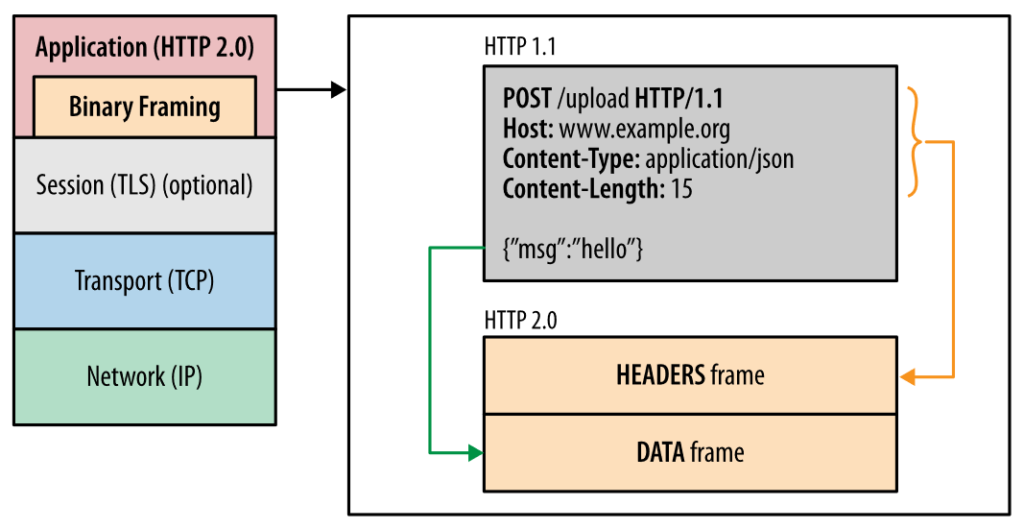
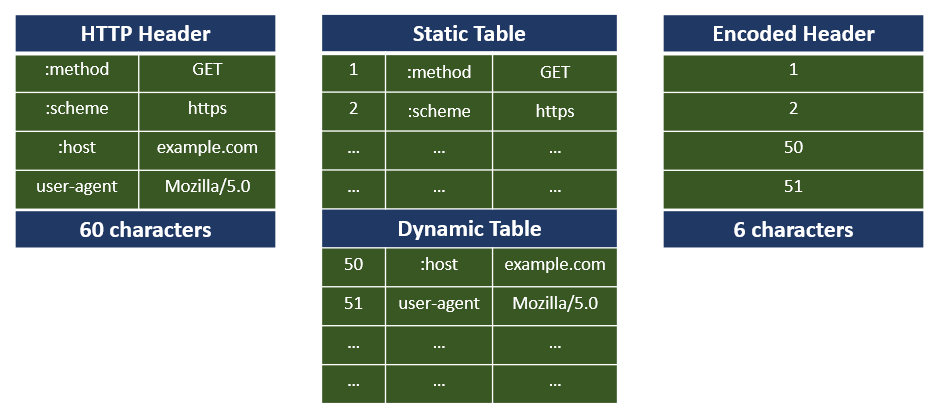
- Header compression using HPACK: Headers need to be sent only once over the connection in the form of binary codes that are easier to be parsed. Mobile users experience a notable difference in page load times since HTTP/2 provides an optimized web experience.Previous versions of HTTP and SPDY used formats like gzip and DEFLATE that were vulnerable to header compression attacks. HPACK uses static Huffman code to compress headers and is resilient to such attacks providing a more secure environment.
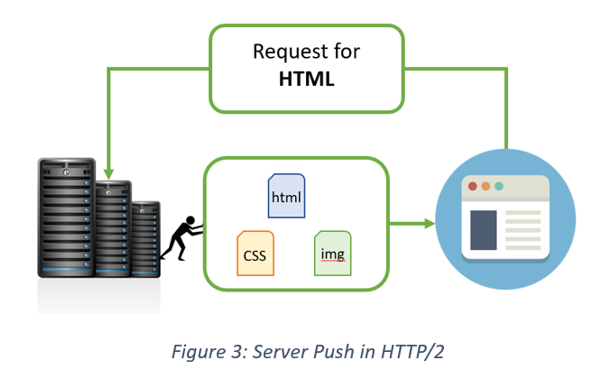
- Server push: Instead of waiting for the client to make requests for additional assets, the server intuitively sends the resources that will be required to render the page, thereby avoiding the round trip. The client can either allow or deny the server push.
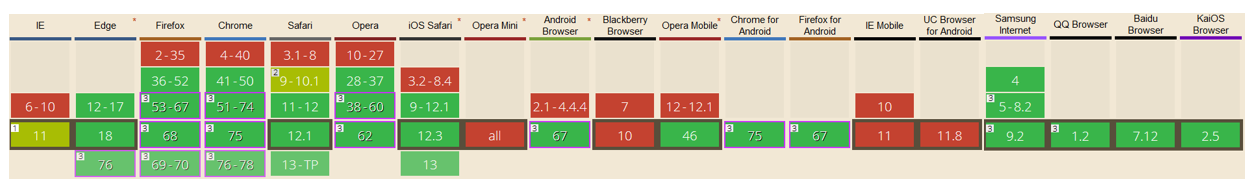
- Browser Compatibility: HTTP/2 is compatible with almost all browsers and is backward compatible with previous protocol versions like HTTP/1.1. The standardization effort was supported by most client browsers including Chrome and Firefox with the condition that it should be used only over TLS. By the end of 2015 most major browsers had added HTTP/2 support.
- HTTPS with HTTP/2: Though HTTP/2 supports both secure and non-secure connections, almost all prominent client browsers like Chrome, Mozilla have decided to extend support for HTTP/2 only over a secure connection. For enabling HTTP/2, it is essential to get an SSL/TLS certificate and make every page on the website https.
In short, we can list the advantages of HTTP2 as follows:
- Multiplexing in HTTP2 makes it a lot faster than its predecessors.
- HTTP2 uses a single TCP connection to transmit requests and frames, thus eliminating the need for multiple connections.
- HTTP2 streaming uses a prioritization tree for more efficient transmission.
- HTTP2 is more secure as it uses binary protocol instead of plaintext.
- HTTP/2 allows the user to have a better web experience by reducing the page load time considerably. It needs the header to be sent just once in binary codes to increase speed.
- HTTP/2 gives an option of server push to clients to further speed up the process.
- HTTP2 provides higher compatibility with most of the browsers and backward compatibility with previous protocols.
- HTTP2 is a mandatory requirement for SSL/TLS certificate.
Purchase Comodo SSL Certificates & Save Up to 89%
We offer the best discount on all types of Comodo SSL Certificates. It includes Comodo Wildcard SSL, EV SSL, Multi-Domain SAN/UCC SSL, and Code Signing Certificates.
Limitations of HTTP/2
- With multiplexing, the application server receives short bursts of a lot of requests that could potentially overwhelm the server if not throttled at the load balancer. Some server applications might need to tweak their code or application design to make it more suited for handling HTTP/2 traffic.
- Software supporting HTTP/2 is not as mature as existing HTTP/1.1 software, and sometimes have glitches in their implementations.
- While using HTTP/2 only over HTTPS has its perks in terms of security, it complicates matters in development and debugging environments where TLS might not be desirable between different components, thus creating usability issues.
Should You Move to HTTP/2?
HTTP/2 is a more robust protocol giving us increased page load speeds and security. It uses a single TCP connection and keeps it warm enough for concurrent downloads. Slow websites kill user experience and affect sales adversely. HTTP/2 improves a website’s infrastructure without the need to get developers to spend hours writing optimization code. Especially with the added advantage of backward compatibility, making the switch seem seamless for customers still on previous versions of the protocol, there appears to be no apparent reason to fear the upgrade.
The good thing about HTTP/2 is that one might be using it without even realizing that the pages being served are over HTTP/2. A quick and easy way to check if the website is using HTTP/2 is to enable addons or to check the protocol being used under the network tab in the developer tools option.
- Firefox Addon to check for HTTP/2 enabled pages: HTTP/2 Indicator by Cheng Sun, Brandon Siegel

