AV-TEST Institute registers more than 350,000 new malware and potentially unwanted applications (PUAs) daily. The sheer number of new malware is enough to make you shiver — so long as you understand what “malware” entails. But what is malware and what does it do? Let’s explore malware definition and meaning
Malware is a threat that can be found everywhere online. It’s hidden in app stores’ most popular apps, gets sent daily through email, and often can be found attached to some of your favorite share-site downloads. But what is malware and what does it do? We’ll break down malicious software and why it’s such a threat to businesses.
What Is Malware? A Quick Malware Definition & Meaning
What is malware and what does it do? The definition of malware is simple: malware is a program or even just code that’s written with an intent to cause harm to a computer system or a network of systems. Malware is short for malicious software (malware) — the term is an example of a portmanteau because it takes parts of two words and combines them.
So, what is malicious software in the sense of how cybercriminals use it? Malware is a catch-all term that describes a software program or code that helps people perform espionage, sabotage, or steal data from others. The history of malware goes back to the days when the internet was not widely available. Although it was once spread via physical floppy disks, malware now can be found in everything from malicious emails and websites to compromised apps and image files.
The AV-TEST Institute recorded the following increase in the number of malware and potentially unwanted applications in the last 10 years:
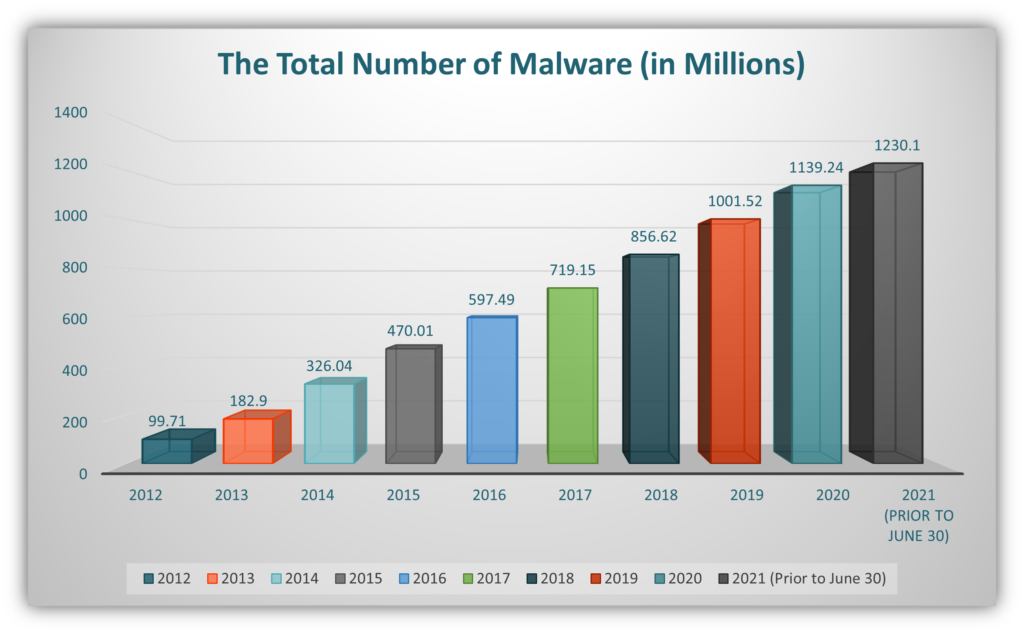
As you can see in the graph, malware attacks have been on a constant rise. Malware increased 13.75% to 1139.24 in 2020 from 1001.52 in 2019. And the numbers for 2021 are even more alarming. Data on the number of malware attacks that occurred between Jan. 1 and June 7 have already surpassed the total number of attacks observed in 2020. And the year is still young… What the cumulative figure for 2021 will be, only time will tell. Till then, we can only take precautionary measures to stay safe.
Types of Malware and What They Do
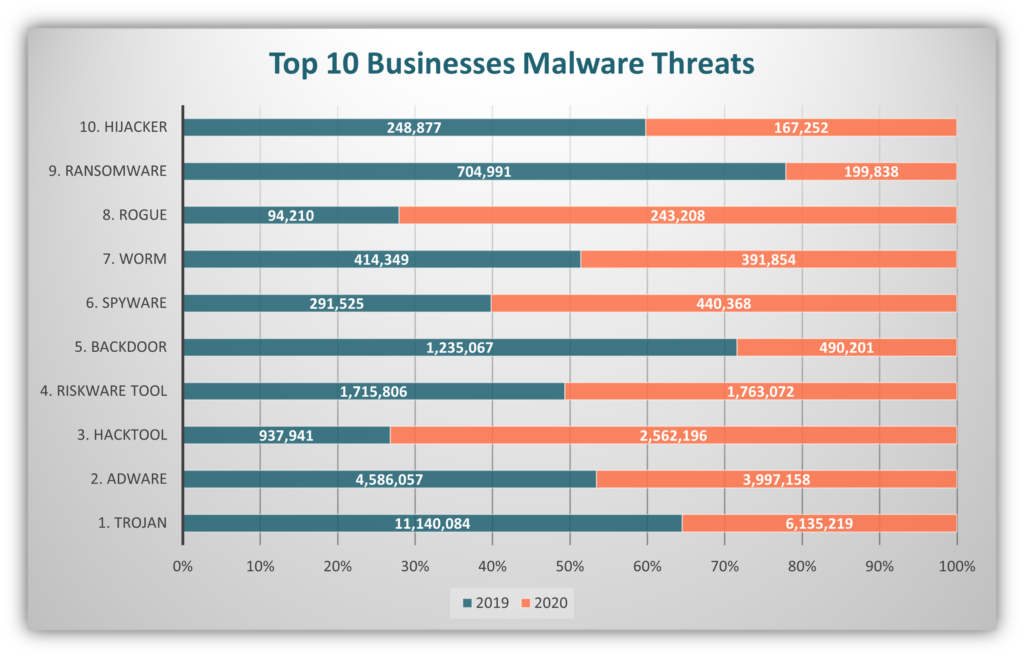
Malwarebytes observed the top malware varieties in the State of Malware Report 2021:
The influx of malware is so rampant that it’s possible you may have undetected malware on your device right now and not know it. Criminals, nowadays, use a combination of two or more types of malware for a stronger attack. They also keep on changing their tactics often to achieve their goals without being detected. The following malware definitions and examples of malware can help you recognize a potential threat.
Adware
Adware is a type of malware that, once installed on your device (mobile or laptop), will display spam, phishing, or other malicious ads that will lure you to click on them. Sometimes adware contains other types of malware with or without the knowledge of the advertiser. When a person clicks on the ad, his computer might get infected with the malware hidden in the ad.
2020 data from Avast called out adware as the most common type of malware for Android mobile devices. Adware represented 72% of the total malware on mobile devices they detected between October and December 2019.
Ransomware
Ransomware is a nasty piece of malware that uses encryption to prevent legitimate users and companies from accessing their own data. Bad guys use this leverage to demand ransom payments (often in cryptocurrencies like Bitcoin or Ethereum). They do this by saying that if the target pays, they’ll provide a decryption key. But there’s no guarantee that the victim will actually receive the key — or that the key will work — even if they do make the payment.
What makes matters worse is that in some cases, cybercriminals will use their access to exfiltrate the victim’s data so they can leak it online, use it for other crimes, or sell it to others.
In a recent event, BleepigComputer reported that the electronic manufacturing giant Foxconn was hit by a ransomware attack and the actors were demanding $34 million as ransom in Bitcoin payments. The criminals DoppelPaymer hit Foxconn over the Thanksgiving weekend of 2020. A strategically located company facility in Mexico was the target of the attack.
Rootkits
Rootkits are a set of tools or programs that can make administrative changes to a device at the kernel level. Some rootkits might be harmless, but some are malicious software programs that operate in the background. The latter are designed to work under-the-radar of your antivirus and anti-malware programs, which means they can go undetected for a long time.
Kaspersky researchers unveiled a previously unknown rootkit they discovered was being used to control the networks of regional organizations. Called Moriya, this rootkit was used to create “passive backdoors on public-facing servers” that allowed the devices to be silently controlled via C&C communications.
Spyware and Keyloggers
These types of software are very useful in surveillance without the knowledge of the subject. They can also be used for constructive (although questionable) purposes like keeping track of the activities of the employees during work hours. However, when cybercriminals use the same types of software with malicious intentions, it becomes malware.
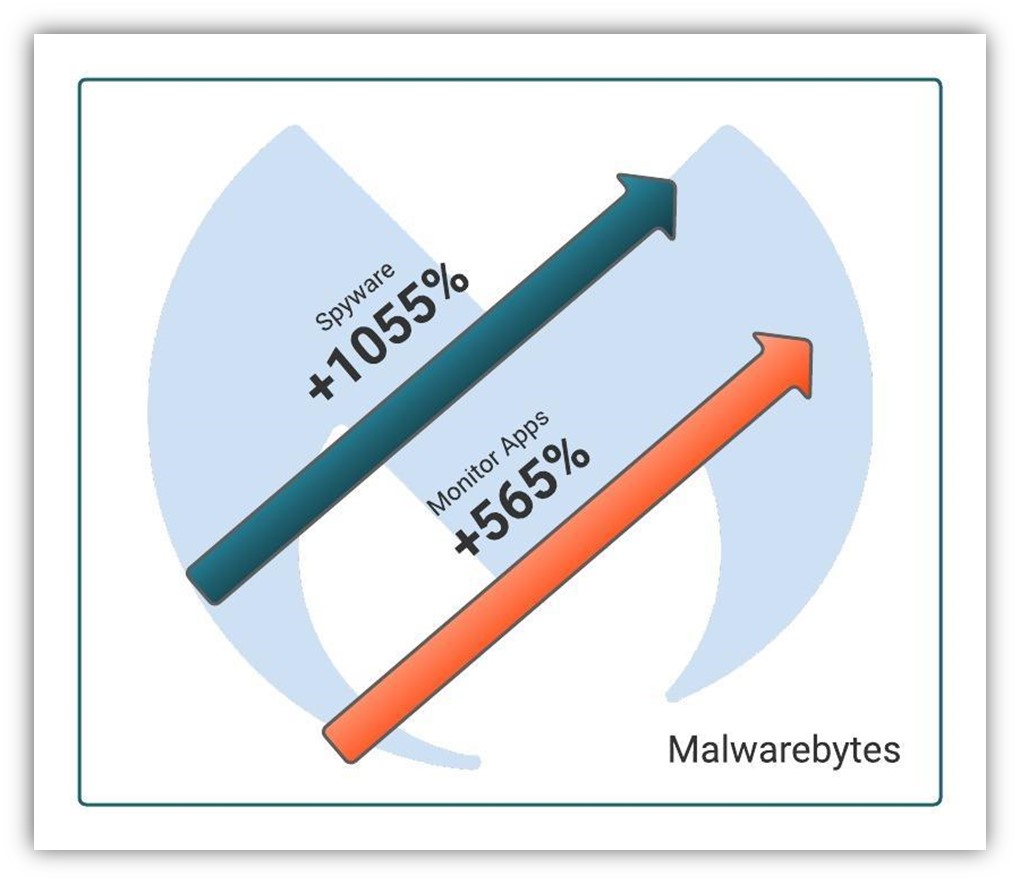
Malwarebytes categorizes keyloggers as “Monitor” apps. In their 2021 State of Malware Report, Malwarebytes reports the detection rates for monitor apps on Android mobile devices rose 565%, and that spyware surged 1,055% between January and December 2020.
Trojans
Trojans are fraudulent and dangerous malware that often reach your computer while disguised as a legitimate program or app. Cybercriminals create fraudulent versions of legitimate software to try to trick people into downloading their fake/malicious version instead of the legitimate software. This type of malware gets its name from the Trojan horse of Greek mythology because of its subterfuge-like uses.
Bad guys took advantage of the COVID-19 global pandemic by creating a fake COVID tracking application for Android devices. Researchers at domaintools.com report that although the app claimed to provide real-time tracking information about coronavirus outbreaks, it was really a Trojan and unleashed ransomware when downloaded on the device. A file locker malware “Covidlock” locked the files on your device when the app was downloaded. Allegedly, the ransom of $100 was demanded from all the victims.
Viruses
A virus is an example of malicious software that infects your device and spreads to your network devices. A virus requires a user to trigger or activate the program. Often virus is connected to a legitimate program and when you install the legitimate program, it is also installed.
Worms
Although worms work in ways that are similar to viruses, they should not be confused with them. A virus requires some type of user interaction to activate it; worms, on the other hand, can be activated without such a trigger. They can also spread to the network of the victim without the knowledge or the help of the victim.
Common Methods of Malware Deployment of Malware
There are many ways that threat actors can get malware onto your device. Let’s explore a few of them.
Phishing Campaigns
Cybercriminals use different communication methods to spread malware that they can use to steal your personal information. Here are a few quick examples:
- Email phishing: Bad guys can use emails to send malicious file attachments or links to sites that contain malware.
- Vishing: Vishing, or voice phishing, is another tactic bad guys love to use. Cybercriminals sometimes use vishing (on its own or in combination with other tactics) to impersonate tech support companies. They use this ruse to trick users into visiting malicious websites or providing their email information, which the bad guys can use to send malware.
- Smishing: SMS phishing text messages are another way that bad guys love to share malware. They can do this by sending messages containing malicious code or sending links that direct users to visit malicious websites.
Check out our article on how to prevent phishing emails and attacks from being successful.
Fake or Compromised Websites
Cybercriminals create fake websites that look legitimate to trick users into clicking on them. When a victim clicks on the fake website, malware auto-downloads and installs onto their device without their knowledge. In some cases, bad guys opt to exploit vulnerabilities in legitimate websites and use those platforms to spread malware to those site’s unsuspecting users.
Malvertisments
When online advertising is used for malicious purposes, it is called malvertising (short for “malicious advertising.”). Malvertising is a fake ad that displays on legitimate websites to trick users into clicking on them. If a user clicks on a malicious ad (or, in some cases, simply views it), it’ll download malware onto their device. This is different from adware, which is malware that gets installed onto your device to observe your behaviors and web searches to display targeted ads.
Of course, there are plenty of other ways that bad guys deploy and spread malware. But these three are among the most common methods.
What Is Malware & What Does It Do? 4 Alarming Consequences of Successful Malware Attacks
A malware attack causes harm on multiple levels to the victims, either individual or enterprise. Let’s consider the effects of a malware attack on a business organization:
1. Results in Data Exposure and Theft
In the words of Clive Humby, a British mathematician and entrepreneur: “Data is the new oil.” As such, every organization should treat their data like their most valued assets. Everything from customers’ names to their social security numbers are valuable pieces of data that cybercriminals want to get their hands on.
IBM’s 2020 Cost of a Data Breach report shows that malicious attacks were responsible for 52% of data breaches they analyzed that occurred between August 2019 and April 2020. Malware attacks can cause data breaches and be used to steal data that attackers can publish online, use to commit other types of crimes or sell to other bad guys to use as they choose.
But how much are various types of data really worth? Privacy Affairs shared the prices of stolen data on the dark web for 2021:
| Item Category | Item Name | Average Sale Price |
| Personal finance | Bank account login details for accounts that contain a minimum of $2,000 | $120 |
| Verified U.S. user’s LocalBitcoins account | $350 | |
| PayPal login details for accounts that have a balance of up to $1,000 | $120 | |
| Personal Identification (stolen real IDs or forged) | Legitimate Russian Passport scan | $100 |
| Legitimate Canadian (Alberta) driver’s license scan | $32 | |
| Valid U.S. social security number | $2 | |
| Social media accounts | Hacked Facebook account | $65 |
| Hacked Gmail account | $80 |
2. Causes Financial Losses
IBM reports that the average cost of a data breach for businesses globally amounted to $3.86 million in 2020. In the United States, these costs soared to $8.64 million in the same period, making it the most expensive country. Their data shows that the average cost of “destructive malware” was $4.52 million and $4.44 million for ransomware. This is more than the average cost of a malicious attack, which they put at $4.27 million.
According to the same report, IBM found that healthcare was the most expensive industry with an average loss of $7.13 million for a data breach. If this was not enough, one in five companies that suffered malicious data breaches was infiltrated with stolen credentials that increased the loss further.
Financial repercussions of data breaches can deal substantial blows to businesses in direct and indirect costs. The following figure shows the average breakdown of costs due to a data breach.
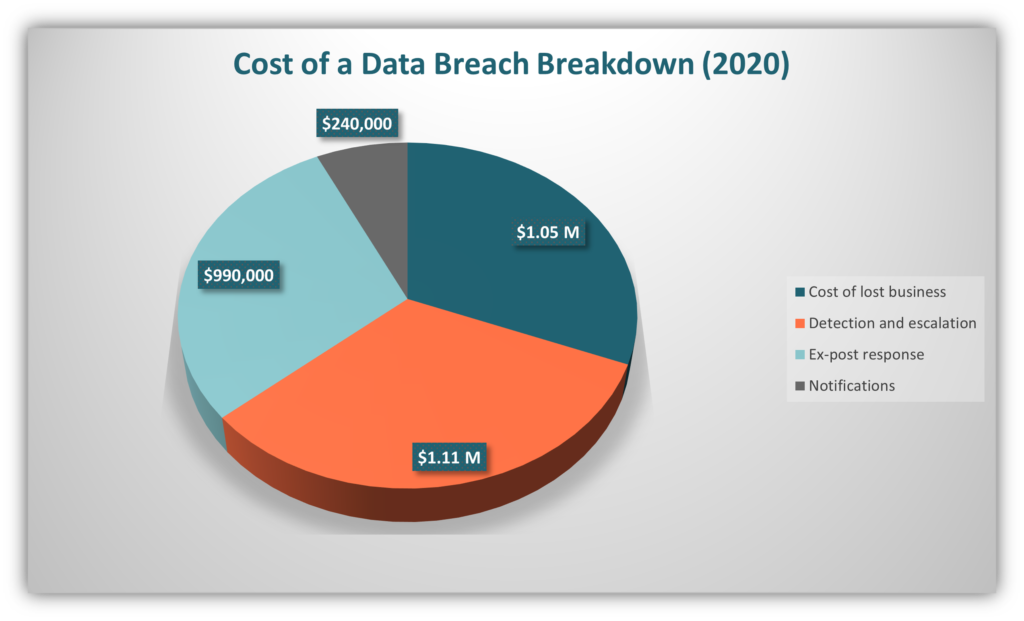
Chart showing the segregation of cost of a data breach. Data source: IBM’s Cost of a Data Breach Report 2020.
3. Damages Your Brand and Reputation
“It takes 20 years to build a reputation and few minutes of cyber-incident to ruin it.”― Stephane Nappo, Vice President of GroupeSEB.
In the wake of a data breach or a malware attack, every business or organization must deal with one of the most damaging factors: the loss of their reputation and standing within the industry. Contrary to the financial liability damages, which an insurance company can cover (depending on your insurance), the damage to your reputation is sometimes irreversible. It might take years for a company to nullify the reputation damage caused by a malware attack.
The worst part is the loss of customer trust. Considering that IBM’s 2020 data breach data shows that it takes an average of 280 days for companies to detect and contain data breaches, and that 80% of breaches involve customers’ personally identifiable information, it’s no wonder why your reputation can take a hit with customers.
4. Creates Noncompliance Issues That Result in Penalties
There are government and non-government bodies that specify the rules and regulations that organizations within specific industries or regions must abide by. The business enterprise is obligated to follow and to file the proof of following the compliance procedures from time to time.
Specific compliance requirements are based on a variety of factors. When a business falls prey to a malware attack, it must pay the penalties and the fines laid out by the governing bodies. These fines are in addition to the detection and other expenses to be borne by the enterprise. Some of the governing bodies and their relevance are mentioned below:
GDPR (General Data Protection Regulation)
GDPR is applicable to the entities operating in the European Union (EU) for the protection of data and privacy in the EU and the EEA (European Economic Area). The GDPR has regulations on the processing of personal data of the people on a legal basis. The data subject must provide consent to data processing for one or more purposes in order for them to use their data.
If a company violates GDPR, they may be subjected to heavy penalties. Many companies have been sued under GDPR for processing the data without permission or with “forced permission” including WhatsApp, Instagram, Facebook, Apple, Microsoft, and Google LLC.
California Consumer Privacy Act (CCPA) of 2018
The California Consumer Privacy Act aims to protect the privacy of California residents. The legislation applies to every business that collects the personal data of CA consumers (regardless of whether the company is located within California) and fulfills one or more conditions:
- Has annual gross revenue that exceeds $25 million;
- Buys, receives, or sells the personal data of at least 50,000 consumers, households or devices; or
- Earns more than half of its annual revenue from selling consumers’ personal data.
Although consumers typically can’t sue under the CCPA (in most cases), statutory damages are to be paid in case of violation:
- The companies falling prey to a data breach/theft must pay $100 to $750 per incident, per California resident, or the actual damages, whichever is higher. The court may ask the company to pay any other relief as it may deem fit.
- A fine of $7,500 in case of an intentional violation and $2,500 in case of an unintentional violation.
Payment Card Industry Data Security Standard (PCI DSS)
PCI DSS is the information security set of standards that all organizations and companies globally that handle credit card data must abide by. The PCI standards must be followed by all the companies that accept online payment and process consumers’ credit card details. In case of a data breach, the council will levy penalties on the company. Even if the data breach is due to a malicious attack, the victim company is liable to pay the penalties.
Final Words on Malware
Malicious software or malware causes losses both financial and non-financial losses to businesses and organizations. There are insurance policies available that may be able to mitigate your financial losses to a certain extent, but your organization and the trust your customers have in it are still going to suffer as a result.
The only way to minimize the chances of incurring all these losses is by doing everything in your power to prevent a cyber attack. This includes educating your employees and taking the necessary steps to prevent malware attacks from being successful.