The FBI IC3 reports consumer victims reported total cybercrime-related losses of $4.2 billion in 2020, a 69% increase from 2019. Part of these losses resulted from malware attacks — so let’s talk about how to stop malware attacks
Knowing how to prevent malware attacks is essential for any business that operates online or handles digital data. Cybercriminals want your data — it’s a valuable resource that they can use to carry out crimes or sell to other bad guys.
But how big a deal are malware attacks? Big. They’re often used to help carry out cyber attacks that result in data breaches, noncompliance, and many other issues. IBM’s Cost of Data Breach 2020 reported that the average cost of a data breach was $3.86 million and took 280 days to identify and contain. Gartner’s research predicts the global research security market will reach $170.4 billion in 2022. 23% of the data breaches resulted from human error observed IBM.
So, this brings us back to our original question of how to prevent malware attacks. But before we dive into that, let’s quickly recap what malware and malware attacks are in the first place.
What Is Malware and What’s Its Role in a Malware Attack?
Malware is a type of software or code that users create to cause harm or disruptions to others. A malware attack occurs when someone uses one or more types of malware to gain unauthorized access to a target’s device, network, or other resources. The malware infection may cause obvious disruptions or may be stealthy, operating unseen in the background.
Malware can be divided into 10 broad categories based on their programming and uses, or how bad guys distribute or spread them. Some types of malware tend to overlap, and many sophisticated cyber-attacks use more than one type of malware. The following figure shows a quick overview of the different types of malware:
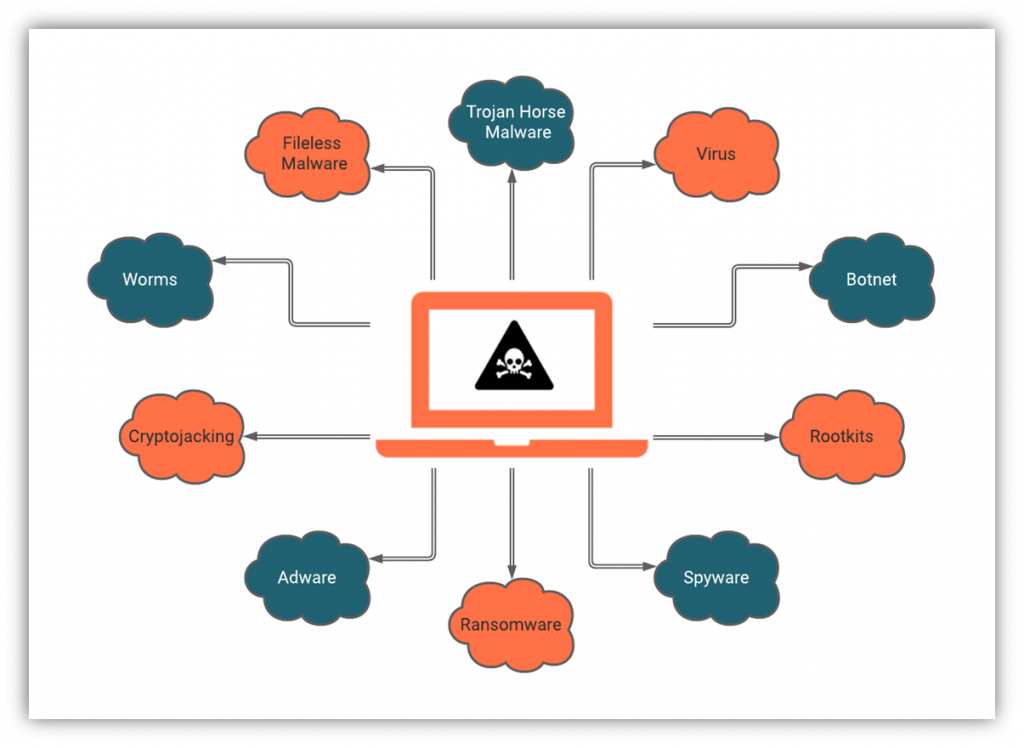
Let’s look at a short explanation of these types of malware and how they’re used in malware attacks. After that, we’ll get to how to prevent malware attacks from being successful against your business.
- Trojans. This kind of malware is masked as a software update or app. When the software update is installed, the malware is also installed on your computer. A trojan horse malware can lead to other malware attacks, including ransomware, cryptojacking malware, and spyware.
- Viruses. A virus is malware attacking the victim’s computer by piggybacking on other programs. When the host program is run, the virus is activated. After activation, a virus multiplies itself and spreads the infection within the computer. It is also programmed to send itself to other computers in the same network.
- Worms. A worm is a type of malware that does not require a human to activate it. A worm is quite dangerous as it can infect, multiply, and send itself to other computers. Due to this, worms spread quickly and are hard to stop.
- Spyware. Spyware is a category encompassing many types of malware. Cybercriminals use it to observe and record users’ behaviors and keystrokes to capture sensitive data (such as login credentials).
- Adware. Compared to others, adware is often considered a relatively harmless type of malware. Adware collects users’ data, including their browsing and search histories, shopping preferences, and cart details, to sell to advertisers or display targeted ads.
- Fileless Malware. Fileless malware does not have its own file for malicious code. It candidly attaches its malicious code to other programs. It is improbable to discover fileless malware due to this feature. This kind of malware often links its code to white-listed programs to avoid detection in a routine scan.
- Ransomware. A cybercriminal uses malware to encrypt victims’ data, devices, or IT systems to carry out a ransomware attack. They demand a ransom in exchange for a decryption key. In some cases, they’ll exfiltrate the data to a server they control to use as they please. Verizon describes ransomware as a “big problem getting bigger.”
- Cryptojacking Malware. Cybercriminals use cryptojacking malware to mine cryptocurrencies such as Bitcoin and Ethereum. They create a network of infected computers that run mining programs in the background without the user’s knowledge. As a result, the performance and processing capabilities of the victims’ devices will decrease drastically.
- Rootkits. A rootkit is a remote access tool (RAT), often malicious, that provides an attacker with remote administrative access to a target’s device, network, or other IT resources. The criminals can use this access to change or even pull down the infected website.
- Botnet malware. Cybercriminals sometimes infect the computer, not for the data stored on that computer but to use it as a puppet to commit some other crime. They build armies of such computers referred to as bots or zombies. These armies work for the criminals per se, or the criminals rent it to others to use maliciously. The bots or the zombie computers are unaware of them being used maliciously.
How to Prevent Malware Attacks — 7 Things You Should Start Doing Now
Understanding how to stop malware attacks is critical to your organization’s security and sensitive data. Preventing a malware attack boils down to having the processes, policies, and IT security tools in place to prevent them from occurring. However, it also required training your end-users to recognize and respond to common methods cybercriminals use to spread malware.
1. Use Network and Endpoint Security Tools

First on our list of how to prevent malware attacks: use the right tools. Your IT experts should look into every possible route through which a criminal can use malware attacks against your organization’s devices and network. Using a combination of endpoint and network security protection tools is the answer to preventing many malware-related security woes.
Install Antivirus or Anti-Malware Software
Antivirus and anti-malware tools are useful for identifying and protecting your endpoint devices or larger network against many traditional and new malware-related threats. And it’s easy to see why such tools are necessary considering that Kaspersky detected an average of 360,000 new malicious files every day in 2020.
Different antivirus and anti-malware tools offer varying levels of protection:
- Browser-level protection: Some browsers (like Chrome) have built-in malware protection tools that help to protect you from such threats online. This helps to prevent malware from reaching your device via the browser but doesn’t scan your device for existing threats.
- User device-level protection: This tool, which you download onto your mobile device or computer, scans for malware or viruses that may already exist on your device. If it detects any, it’ll notify you so you can choose to quarantine or remove them.
- Network-level protection: This type of network appliance guards against malware attacks and other threats that come in through your network’s traffic.
- Server-level protection: This software is great for protecting your organization’s servers against viruses and other malware-related threats.
Use A Firewall
A firewall is another layer of protection that gives you more robust security of your devices and network. A firewall acts as a barrier between the internet and your IT infrastructure, blocking many types of malware attacks and other malicious activities (both inbound and outbound). They come in hardware and software varieties, although many organizations use both. So, if you’re wondering how to prevent malware attacks, this is a good way to do it.
Any unauthorized access to your network is identified, and the traffic is stopped if found malicious by the firewall. A firewall also allows the user to configure what traffic is allowed and what has to be blocked. That means the user can specify the IP addresses or ports that have to be blocked or allowed. While not 100% effective, a firewall can make a lot of difference in protecting your network and devices from malware attacks.
2. Use Encryption to Secure Data In Transit
Cybercriminals use every possible opportunity to hijack your data, including the time when it is in transit. The conversation between the website and server, the email correspondence with outsiders, the internal correspondence of the organization can be intercepted and used by the bad guys for their malicious purposes. The enterprise must keep the data-in-transit secure from their prying eyes. Some of the ways to achieve this goal are as follows:
Use SSL/TLS Certification For Your Website
An SSL/TLS certificate (which enables the secure socket layer or, more accurately, the transport layer security protocol) is a digital certificate that’s a core component of public key infrastructure (PKI). It’s what organizations use to authenticate their servers and establish secure, encrypted connections between their websites and users’ web clients. This is what makes the “HTTPS” appear in your browser’s address bar!
Most browsers (including Chrome and Mozilla) brand websites as being “not secure” if they don’t have TLS certificates installed. The visitors’ trust in your website dwindles when they see this ugly warning in their browser’s address bar. Needless to say, HTTPS plays a pivotal role in a company’s online business.
Use Email Security Tools like S/MIME Certificates to Protect Sensitive Messages
Keeping your email data secure is a concern for every business. An email signing certificate or S/MIME certificate is a PKI-based tool that enables you to exchange digitally signed and encrypted emails with other S/MIME certificate users. It also ensures that recipients know it’s secure, legitimate, and arrived in an unaltered state.
It works by having you (as the sender) encrypt the email using the recipient’s public key, which they can decrypt upon receipt using their corresponding private key. This process ensures data integrity (letting your recipient know you sent it and it hasn’t been altered in any way) and secures your message before it leaves your mailbox.
Using an email signing certificate ensures only your intended recipients can access your messages and prevents outsiders from accessing or modifying your messages. This protects your email data both while it’s in transit and at rest on your recipient’s server until they decrypt it.
3. Educate Your Employees to Recognize Common Cyber Threats & Scam Tactics
The security of your organization is only as strong as its weakest link. Kaspersky reports that 52% of the businesses regard their employees as their biggest vulnerability or risk factor. These statistics of human errors are alarming. Regular training of the employees should be done in every organization to raise awareness about cyber security and curb the risk of malware attacks.
No matter how much you spend on cybersecurity tools and IT staffing, if your non-IT employees are not trained to watch out for possible threats, all of those investments still might not help. Cybercriminals target those employees, which is why all employees should be trained regularly in cyber security procedures.
Cyber awareness training educates users about real-world threats and scams and how to respond to them. This training should cover:
- General cyber security best practices.
- Your organization’s cyber and acceptable use policies.
- Common types of cyber attacks and online threats (using real-world examples of phishing emails, malicious websites and ads, etc.).
- Common tactics cybercriminals use (such as social engineering, email spoofing, malicious URLs or email attachments, etc.).
- How they should react or respond to suspicious/potentially malicious messages and situations.
- Who they should reach out to internally (i.e., report a situation to someone in IT) and how to report when something goes wrong.
Here are some quick examples of topics to cover with your employees to help you prevent malware attacks.
Don’t Open Emails From Dodgy Sources
Phishing is a type of cyber attack cybercriminals love to use. These campaigns incorporate social engineering techniques to manipulate or trick victims into handing over sensitive data or downloading malware onto their devices. This is why users should never open or otherwise engage with suspicious emails.
Our article on examples of phishing emails will give you a peek into what fake emails look like.
Beware Phone Call Scams
Cyber scams can occur online or over the phone. Fake tech support scams continue to rise, according to the FBI’s IC3 Report 2020. They received 15,421 complaints from 60 countries, and the total loss to victims amounted to $146 million, a 171% increase from 2019. The following figure illustrates the increasing losses sustained by tech support fraud victims:
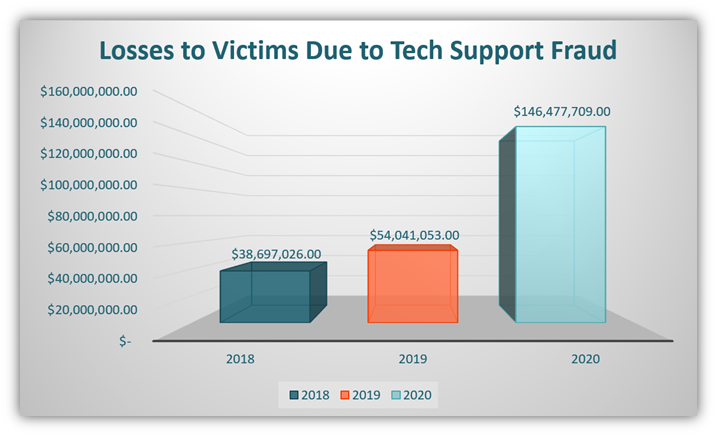
These scams are an effective way for cybercriminals to get unsuspecting users to download malware onto their devices. They can and will say virtually anything to make you trust them and reveal personal information or download something dangerous. Teach your employees that if they get a call or computer message saying their devices are infected with malware, they should call your IT team immediately.
Don’t Click on Popups or Malicious Links
Malicious links and popups are one way to get malware on your device. If you see a popup saying your device is infected by malware and the popup asks you to call a certain helpline number, it’s likely a scam. The popup might even want you to click on a particular link for your benefit. If you click on such a link, you might be the next victim of cyber-crime.
4. Update Your IT Systems, Plugins & Software Regularly
When developers discover a vulnerability in their software, they release patches or other updates to fix those issues. However, many businesses take these updates for granted and procrastinate. They may wait weeks or months to apply them — or never apply them at all — leaving their systems vulnerable to malware and various cyber attacks.
Cybercriminals know this and take advantage of the situation. They can use these unpatched vulnerabilities to attack organizations that haven’t updated their software. Thus, it’s crucial to roll out updates as soon as possible.
This applies to everything from software applications to your IT infrastructure’s firmware and operating systems. Additionally, anti-malware or antivirus software also need to be updated regularly. This will give you protection from some of the latest known threats.
5. Use Secure Authentication Methods
Continuing on our list of how to prevent malware attacks, we now turn our gaze to authentication. An enterprise can secure its network by using strong authentication methods. Instead of using just passwords, organizations should frame a policy of using more robust authentication methods, including:
Employ Multifactor Authentication (MFA)
Multifactor authentication method involves the use of two or more types of identifying factors that fall within the following three categories:
- Something you know (such as a password or a passphrase);
- Something you have (such as a mobile authentication app, a CAC card, or a physical security token); and/or
- Something you are (biometrics such as your fingerprint, facial scan, retinal scan, voiceprint, etc.).
It’s unlikely that a cybercriminal will have access to two or more of the above identifiers for your account. Thus, MFA enables a higher level of security to prevent malware attacks.
Use Strong Passphrases Instead of Passwords
Modern secure passwords are incredibly complex, using combinations of uppercase and lowercase letters, numbers, and special characters. They’re difficult to type and even harder to remember (especially when they have dozens of them). However, they’re not always hard for computers to guess.
The National Institute of Standards and Technology (NIST) says that password length is more important than complexity. This is why the FBI recommends using passphrases instead of complex passwords. So, instead of using a complex password like Yif38%4vHJXelr, users should opt for a secure passphrase like CandlestickElephant23MoonTusks or GrilledTrickFort900Noon.
Check out this FBI video to learn more:
Use Passwordless Authentication Methods
Passwordless authentication is a lot like it sounds — it’s a way to authenticate yourself without using a password. That’s because it relies on other methods of identifying and authenticating someone to allow them access to a protected resource. These identifiers include:
- One-time PINs (OTP), codes, or links,
- Physical pieces of hardware such as tokens or ID cards, or
- Client authentication certificates.
The last category allows users to authenticate themselves to your server through the use of PKI digital certificates. So long as their user profiles have the right permissions or authorizations, they can establish a secure connection with the server to access your secure resource or service.
Speaking of authentication, this brings us to our next related approach for how to prevent malware attacks.
6. Implement Identity Management & Access Controls
Identity and access management (IAM) is a framework for authorization and authentication. It’s all about verifying a user’s identity and permissions before giving them access to a particular system. Employees of the organization should have limited access to sensitive data even if they are trustworthy.
It’s considered a good practice to grant limited privileges to the least number of people (i.e., only those who need it to do their jobs). By giving administrative rights to everyone on the network, you increase your organization’s attack surface and risk. Even if you trust everyone on your network, they might make a mistake, leaving the network door open to cybercriminals.
If you have admin privileges, use a separate account to browse the net and perform non-administrative duties. Only when you need to perform administrative tasks should you log in to the admin account. This way, you can guard your computer and network better. Additionally, avoid using use your administrative account on an open network. Remember to log out of your admin account when you’re not handling administrative tasks.
7. Download Files, Software & Tools From Official Sources Only
This brings us to our last item on the list of ways for how to prevent malware attacks. Downloading software or files from dodgy websites and stores is often a source of malware. If your infected device connects to a network, then you’re giving cybercriminals a way to gain access to your network. There, they can move laterally to try to find other vulnerable devices to infect or sensitive information they can steal.
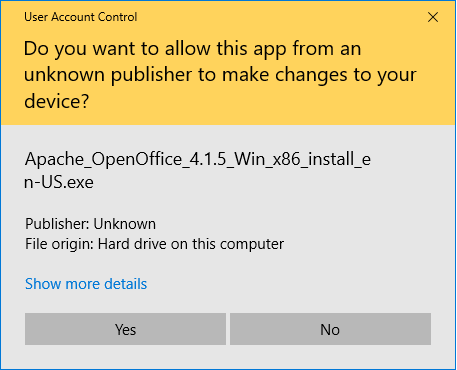
This is why every company should ensure that the software should come from reliable sources. The software should be signed with a reliable code signing certificate. Companies that use code signing certificates with the highest level of validation avoid displaying these types of messages when desktop users download their software:
But what about mobile devices? Does your company use mobile or “smart” devices? Mobile and IoT devices can become an easy target for criminals to find a way to your entire network. Kaspersky reports that their mobile products and technologies detected the following in 2020:
- 5,683,694 malware installation packages,
- 156,710 new mobile banking trojans,
- 20,708 new mobile ransomware trojans.
Kaspersky’s report for 2019 and 2020 identifies multiple types of malware among the top mobile threats:
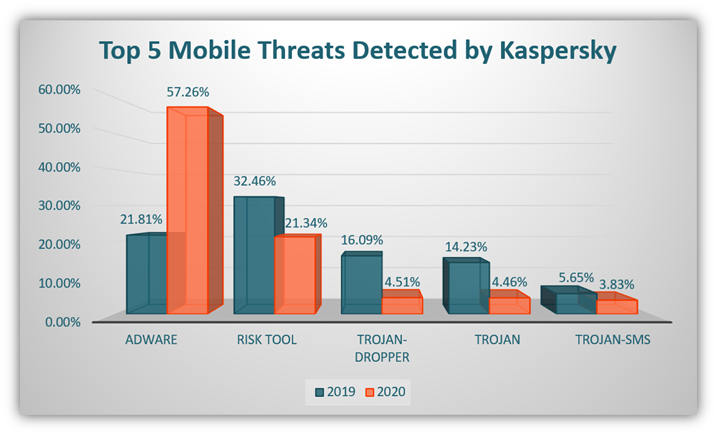
Although that brings us to the end of the methods of how to prevent a malware attack, there is still one more thing that we think is relevant to this topic.
Create and Maintain Regular (Encrypted) Backups of Your Data
Although creating regular backups is not a method to secure your network from malware attacks, it certainly helps when you face a malware attack. That’s because backing up your company’s data and files is not just a good rule of thumb, it’s often a compliance requirement as well.
Following the 3-2-1 data backup rule is a great way to be data-ready in emergencies (like when you’re trying to stop a malware attack or recover from one). The technique, which the U.S. government’s US-CERT, United States Computer Emergency Readiness Team recommends, entails the following:
- Keep three copies of any important files. This includes one primary version and two backup copies.
- Use two different media types to store your files and data. This approach provides additional projection against multiple hazards.
- Always securely store one copy of your data at an off-site location. Sometimes, it’s even recommended to keep a copy in a different geographic area in case of a natural disaster.
The following figure shows this technique:
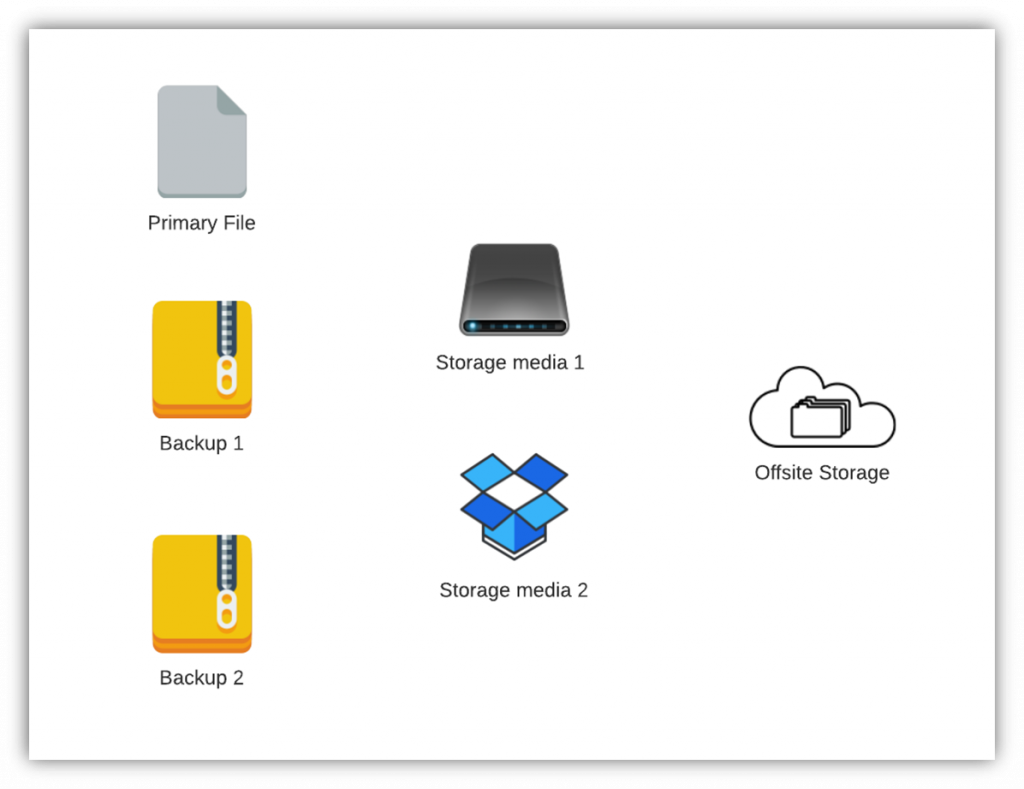
By following this technique, you can ensure that you have access to your data through backups in an emergency.
Final Words On 7 Ways To Prevent Malware Attack
A cybercriminal can attack you from any side, anywhere, anytime, and anyhow. They use different types of malware and deployment tactics to infect your devices and networks.
I will leave you with a statement by Jeh Johnson, the former U.S. Secretary of Homeland Security, as food for thought:
“Cyberattacks of all manner and from multiple sources are going to get worse before they get better. In this realm and at this moment, those on offense have the upper hand. Whether it’s cyber-criminals, hacktivists, or nation-state actors, those on offense are ingenious, tenacious, agile, and getting better all the time. Those on defense struggle to keep up.”
This is why having strong cyber defenses and cyber-aware employees and users is critical. By following strict preventive measures and educating users, you can reduce the chances of malware attacks & scam techniques being successful against your organization.


![A 6-Minute Overview of the PCI DSS Requirements [For PCI DSS v.4.0]](https://cheapsslsecurity.com/blog/wp-content/uploads/2022/12/pci-dss-requirements-v4-370x245.jpg)