Root certificates and intermediate certificates are two terms website owners will come across when they get SSL certificates for their websites. Roots is the basic difference between the two certificates. The root certificate authority will have its own roots in the browser’s trust stores. Intermediate roots are issued by sub-certificate authorities or intermediate certificate authorities. These intermediate roots will not have roots in the trust stores of browsers. Such intermediate roots will be pointed to trust-party roots. Let’s get into the details.
What is Public Key Infrastructure
PKI (Public Key Infrastructure) helps protect confidential data and communications between the web server and the browser. PKI supports services like data integrity, confidentiality, and other security-related services, for which public and private keys are used. Similarly, SSL certificates also involve the implementation of public/private key pairs. It encrypts a website’s data based on a private key. The right public key has to be used by users to access the site. Using a certificate file, the public key is distributed to users and this file is used every time a viewer tries to visit the website. Websites with invalid certificates are considered unsafe to visitors as invalid certificates mean the website has not been verified.
SSL certificates are issued by trusted certificate authorities like DigiCert, Comodo, GeoTrust, etc. These certificate authorities require the website owners to go through a verification process to make sure the website for which they are applying for an SSL certificate is genuine. Once the verification process is completed, CAs issue SSL certificates to eligible websites with expiry dates. Website owners have to renew their SSL certificates when they expire to keep their sites protected. SSL certificates give assurance to website visitors that the websites they are visiting are genuine and that the sites have been validated by a trusted certificate authority. SSL certificates are mandatory to establish secure and encrypted connections. Website visitors are most likely to become victims of data breaches and other threats if there is no SSL certificate.
Certificate Chains
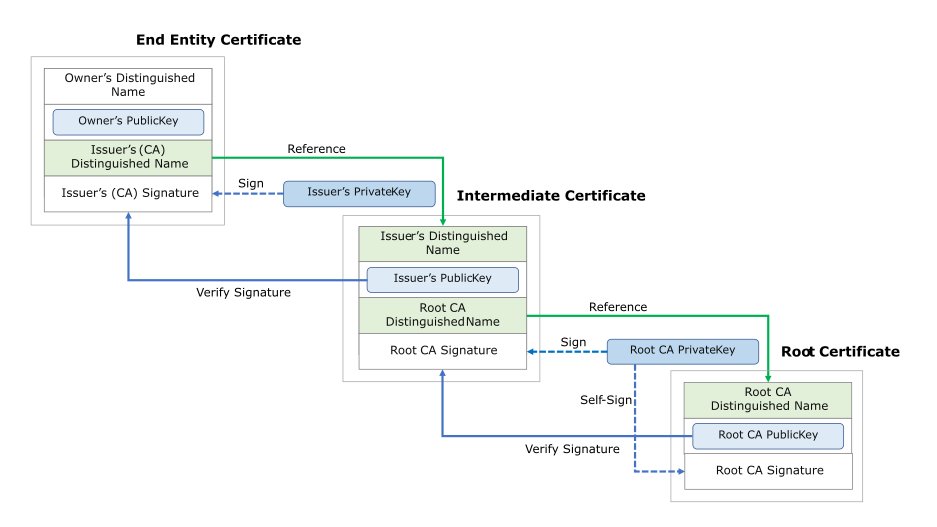
A certificate chain or the chain of trust is something that has a series of certificates. This includes the certificate from the certificate authority, a self-signed certificate, and the end-user certificate. An SSL certificate will be trusted only if it is traceable back to the trust root by which it was signed.
Properties of certificates in the certificate chain:
- The certificate chain will include details of the issuer of the certificate. The subject of the next certificate will match the details of the first certificate in the chain.
- Except for the last certificate in the chain, all the other certificates in the chain will be signed by the private key corresponding to the next certificate in the chain of trust.
- The chain’s last certificate, which is different from the other certificates in the chain, is known as the trust anchor, which is the CA certificate issued by a reliable entity.
Server certificate, intermediate certificate, and root certificate are the three parts of the chain of trust.
Root Certificate
Digital certificates issued by CAs to the websites using SSL certificates are root certificates. Most browsers have these certificates stored in their trust stores. Root certificates are generally protected by the issuing CA.
Intermediate Certificate
Next in the certificate hierarchy comes the intermediate certificate. Every certificate chain will have one or more intermediate certificates. These certificates that are more like the root certificate’s branches stand in between the root certificate and the server certificates issued to the end users.
Server Certificate
This is the certificate issued to the domain that requires SSL encryption.
Root Program
Of the above three certificates, the root certificate is the most important. This is the certificate that will validate the end-user certificate. Root certificates and their public keys are stored in the root store and the root certificate and its keys are managed with the help of a root program. The location of the root store will differ based on the OS and apps used. Google, Mozilla, Apple, and Microsoft provide popular root programs. All these root programs comply with the CA/B regulations.
Root Certificates
The most important part of the SSL protocol is the root certificate. That is because browsers will recognize and trust all certificates signed with the root certificate’s private key. Root certificates are critical as they help establish trust and make the website trustworthy. So it is important to make sure these certificates are issued by trusted CAs that undergo a series of compliance procedures and verifications to be considered reliable. So, the trust anchor for a certificate authority is established through its root certificate and this, in turn, makes the websites using the signed security certificates trustworthy, as well.
Trusted certificate authorities like DigiCert, Comodo, GeoTrust, RapidSSL, etc., deliver root certificates, also known as a trusted root. This digital certificate uses the X.509 format and is used to issue intermediate certificates and other certificates.
The lifespan of a root certificate is not as short as an SSL certificate or an intermediate certificate and it can be valid for up to 25 years. Depending on the digital signature used and certain other attributes, there can be any number of root certificates. The root store application is where one can view the certificate properties. Other certificates are validated and the private key is signed through the root certificate. Every intermediate certificate chain must be traced back to a root certificate. If not, the certificate will not be considered valid.
As mentioned above, the CA issuing the root certificate has to be technically strong and secure enough to issue a root certificate. It has to undergo public scrutiny, audits, etc., to be considered trustworthy.
Intermediate Certificates
Intermediate certificates are more like substitutes to root certificates as the CAs consider it quite dangerous to directly issue an SSL certificate to the end users from a root certificate. They issue intermediate certificates to add an additional layer of security. Intermediate certificates are like a bridge between the root certificate and the certificate issued to end users.
Intermediate certificates assure browsers that the installed SSL certificate is trustworthy. Intermediate certificates generally have a longer validity period when compared to SSL certificates, but their lifespan may not be as long as the root certificates.
A new CA may seek the help of a well-established CA as it may not have undergone compliance procedures to be considered secure enough to issue root certificates. So, such CAs will form a chain of trust by using the services of another well-established CA and link its certificates to a root certificate issued by the other established CA. This way, the trusted root certificates will be linked to a few intermediate certificates. Once the new CA undergoes all the compliance procedures and gets the required validation to issue root certificates, it will add its roots to the root store and replace the other CA’s root certificates with its root certificates.
Intermediate certificates, in general, help new CAs by acting as a middle-man between the trusted root certificate and the intermediate CA. This way, new CAs grow their customer base and also establish themselves.
Intermediate certificates help mitigate security risks by controlling the number of root certificates being used. Having too many root certificates can be risky so intermediate certificates will take some of the responsibilities of root certificates and act as their substitutes.
Most CAs use intermediate certificates to add an extra layer of security. That is because only the intermediate certificate and not the root certificate will have to be revoked in case of a security attack.
Difference Between Root Certificates and Intermediate Certificates
One can easily differentiate between a root certificate and an intermediate certificate by checking details from the root store. Follow the steps below to check certificate details.
Go to the root store and open the certificate to check its details. Go to the Certification Verification Path, where you will see various levels. Here, you can see the name of the CA that issued the certificate and the expiration date of the certificate.
How to Know Whether a Certificate Is a Root Certificate?
The certificate is a root certificate if
- you see just one level in the certificate path.
- the same CA’s name is present in the issued to and issued by fields.
- the certificate is valid for two years or more. Root certificates have a valid life span of over two years and their validity is up to 25 years. But this is not the case with intermediate certificates, as they will be valid for two years or less.
In the Windows root store, you can easily differentiate between root and the intermediate certificates as it will have the root certificates listed under Trusted Root Certification Authorities and the intermediate certificates under Intermediate Certification Authorities.
Conclusion
Both intermediate certificates and root certificates are crucial in the PKI’s chain of trust. The trust chain could break even if one of these certificates is absent. We hope this article helped you understand what are intermediate certificates and root certificates.




