An SSL certificate is a critical component of website security, facilitating encrypted connections that protect sensitive data in transit. But — and this is a big “but” — the SSL certificates have to be issued by a trusted entity called a certificate authority (CA) for them to be trusted by clients (your users’ web browsers). So, if you’re here because you asked your search engine “what is a self signed certificate,” allow us to explain what this all means for you and why it’s better to use a CA signed SSL certificate over a self-signed one.
The reason for such a cautious approach comes from the authentication provided by SSL/TLS certificates. An SSL certificate authenticates the identity of a website or organization. Now, keep in mind that web users aren’t the ones that are actually interacting with SSL certificates. Their browsers are — and browsers have a vested interest in keeping their users safe.
So, it makes sense that the browsers need some assurances before they’re willing to trust a certificate and, by extension, the entity it authenticates. That’s what validation is for. When a certificate validates an entity, it’s running a series of checks that the browsers require to trust the certificate. The more information that’s included in the certificate, the more checks that need to be performed.
Once the CA performs those checks, they sign the certificate, which lets the browser know that it can be trusted.
Let’s Talk About Why You Can’t Sign Your Own Certificate
A self-signed certificate is something that just about any server can create, but they won’t be trusted by web users’ internet browsers because they weren’t properly validated and issued by a CA. You can’t validate yourself. It should be obvious why — after all, you could simply issue a certificate for any website you want and there would be no way for the browser to figure out whether it’s fake or not. You’ll receive an error message like this if you try to use a self-signed SSL certificate on a public website:
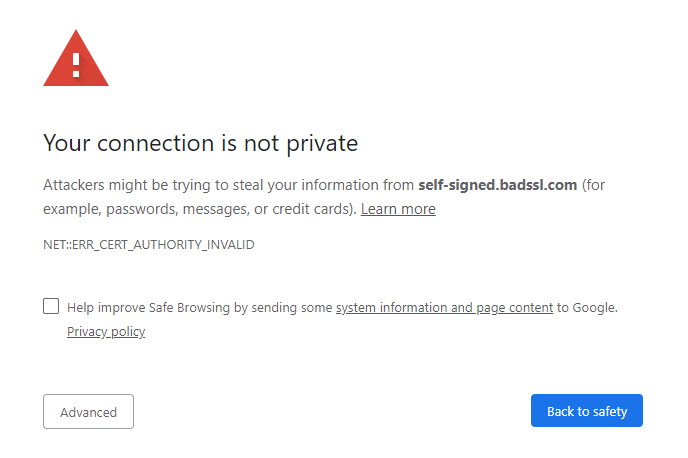
So, to avoid this issue, browsers don’t trust self-signed certificates. That’s categorical. For an SSL certificate on the public internet to be trusted, it needs to be signed by a trusted certificate authority. Period.
Purchase a Wildcard SSL Certificate & Save Up to 73%!
We offer the best discount on all types of wildcard SSL Certificates with DV and OV validation. We offer wildcard certificates from the leading CAs, including Comodo CA, Sectigo, Thawte, GeoTrust, and RapidSSL starting for as little as $52.95 per year.
So, Why Are Self-Signed Certificates a Thing?
For the same reason ear gauges and tongue rings are a thing — some servers like to express themselves. No, but seriously, self-signed certificates are a fine option for test environments and internal networks. With just a little configuration, the root that was used to self-sign the certificates can be extended trust by the network itself and anyone on it will then be able to use the self-signed certificates as if they were trusted.
This practice just doesn’t work on the public internet because that root isn’t trusted anywhere else.
So, if you’re securing a public website, don’t use a self-signed certificate. If you do, your visitors’ web browsers are going to issue error messages saying your website is “not secure” and may not be trustworthy.
Obviously, that’s bad for business. So, bottom line: use a trusted CA to issue all of your SSL certificates.
Purchase a DV SSL Certificate & Save Up to 88%!
We offer the best discount on all types of Domain Validation SSL Certificates (DV SSL). We offer certificates from the leading CAs, including Comodo CA, Sectigo, Thawte, GeoTrust, and RapidSSL with DV certificates starting as low as $5.45 per year.

