The Hiscox Cyber Readiness Report 2021 states that one in six firms attacked by cybercriminals in the last year faced a survival crisis and that the average firm now spends 21% of its IT budget on cyber security (63% more than in 2020). Man in the middle attacks are some of the most difficult types of cyberattacks to detect and can do a lot of damage — let’s look at what you can do to protect yourself and your business.
In the wake of 9/11, the United States government passed the Patriot Act, granting the government the right to carry out surveillance on its own citizens without a warrant. In the 20 years since then, many US citizens have fought against these measures in favor of privacy. Whistleblowers like Edward Snowden exposed to the world the extent of mass data collection by the NSA.
In the case of the NSA, it’s the ‘good guys’ listening to our conversations. But even so, many people don’t like it. Imagine the bad guys doing the same thing — it’s a pretty scary thought. When someone intercepts our data and communications in transit so they can use it for malicious purposes, it’s called a man in the middle attack. This is why it’s crucial to know how to prevent a man in the middle attack and what the best man in the middle attack prevention methods are.
We previously looked at what man in the middle attacks are, how they work, and some different types of man in the middle attack. Now, let’s explore how to prevent a man in the middle attack.
9 Man in the Middle Attack Prevention Methods
Perhaps the most unsettling aspect of a man in the middle attack is that it is hard to detect and can remain undetected for a long time. Needless to say, prevention is always better than the cure. That’s why we’re going to jump straight into our list of man in the middle attack prevention methods so you know how to prevent man in the middle attacks from occurring in the first place.
1. Encrypt Your Data in Transit with SSL/TLS
First on our list of man in the middle attack prevention methods is to use the secure hypertext transfer protocol (HTTPS). One of the most efficient ways to secure your website and web app data in transit is by enabling HTTPS, which is what makes the security padlock appear in your browser’s URL bar. This involves the use of an SSL/TLS certificate, which fulfills two main purposes:
- Authenticates the identity of the website owner, and
- Establishes a secure channel to transmit data between a client and the server using encryption.
An SSL certificate enables two parties to communicate using asymmetric encryption. This process allows them to encrypt and decrypt data with two cryptographic keys: one public and one private. The data is encrypted using the public key and can only be decrypted with the private key, which only a legitimate receiver has access to. So, even if a bad guy can take a peek at your data stream in transit, they won’t be able to decrypt it without having access to the private key, so it will be unusable to them.
The two communicating parties use asymmetric encryption to exchange information so they can establish a symmetrically encrypted connection. Symmetric encryption is faster than asymmetric encryption because it relies on a single key to both encrypt and decrypt data.
Recognizing the importance of SSL/TLS certificates in the secure transmission of data, many browsers like Google Chrome and Mozilla Firefox now mark websites without SSL certificates as “Not Secure.” Search engines also reward websites that use SSL/TLS certificates with higher search rankings, which has pushed many website owners to use SSL certificates.
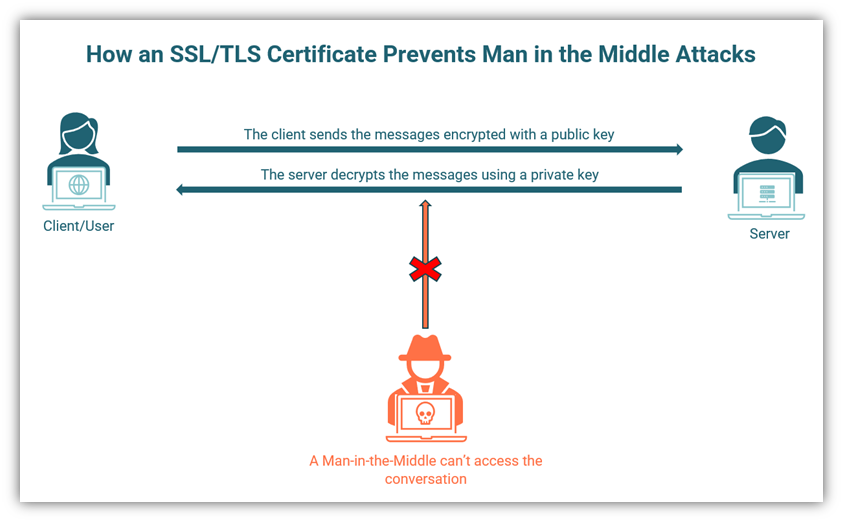
An illustration of how an SSL/TLS certificate prevents a man in the middle attacks by securing the communication channel.
2. Employ DNS Over HTTPS (DoH) or DNS over TLS (DoT)
The domain name system (DNS) is a system where domain names (like “cheapsslsecurity.com” or “wikipedia.org) are converted into internet protocol (P) addresses for faster identification. IP addresses are the numeric values assigned to each device. When a client asks for a particular website, the browser make a DNS request using the TCP protocol.
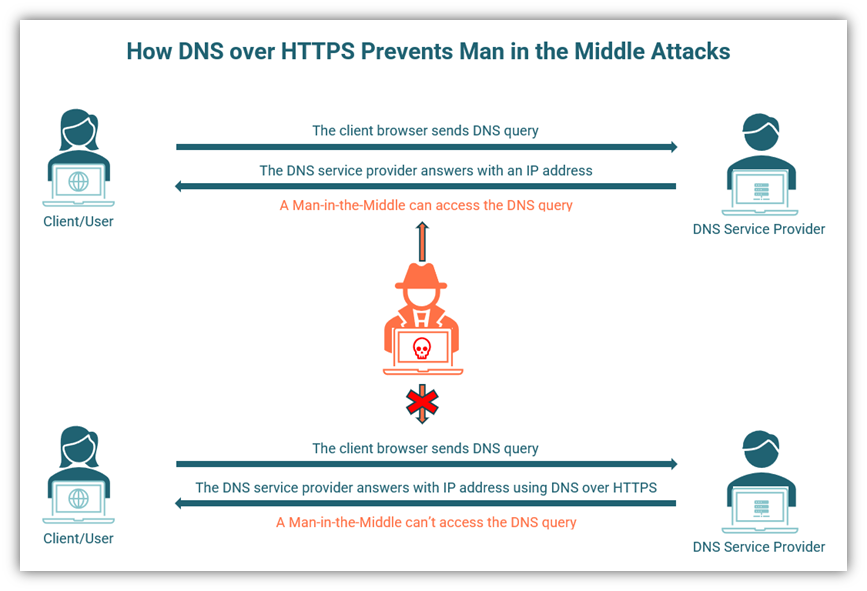
The problem arises when a criminal “sniffs” the packets to hunt for DNS entries. If they are successful, they can carry out a man in the middle attack. To counter this situation, the good guys have come up with a plan of their own. If a DNS query is sent through HTTPS or TLS to DoH-compatible servers, it’s encrypted. This means it’s impossible for cybercriminals to read without having access to the necessary decryption key.
Employing DoH or DoT will prevent the types of man in the middle attacks where the domain name system or its records are compromised, including:
- DNS spoofing (replacing DNS cache data with phony records),
- DNS hijacking (making end users believe they’re connecting with a legitimate domain), and
- DNS poisoning (targeting name servers that cache DNS records).
Therefore, many of the major browsers, including Google Chrome and Mozilla Firefox, support DoH. Here’s a basic illustrative diagram to show how this type of man in the middle attack works. In the top example, it shows that a cybercriminal is able to access the DNS records. The lower example shows that the DNS provider answers using DNS over HTTPS, which prevents the cybercriminal from accessing those records.
3. Implement a Virtual Private Network (VPN)
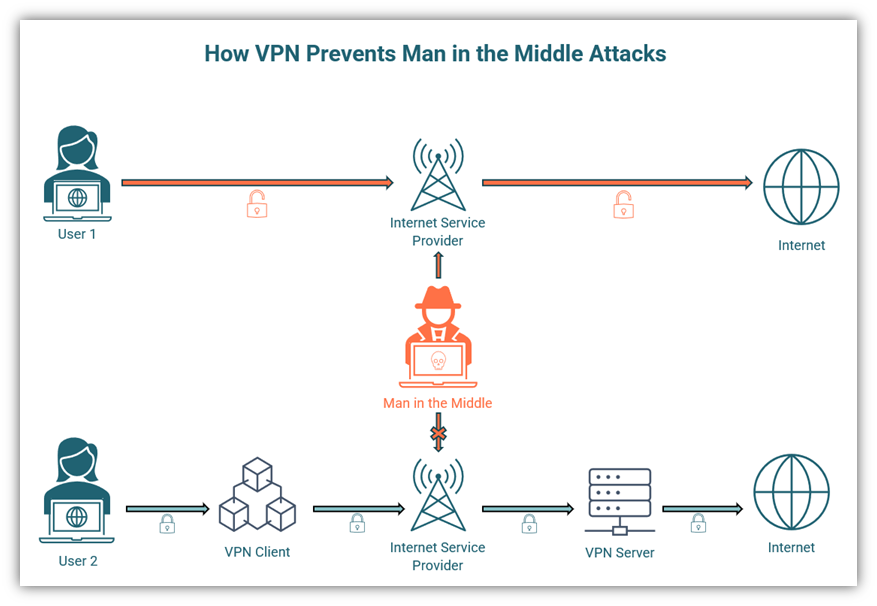
As a businessperson, you know that a ton of sensitive information is transmitted among your employees every day. This has serious security implications, especially if employees aren’t aware of or following proper cybersecurity protocols. Some employee behaviors that could make your business vulnerable to man in the middle attacks include:
- Allowing guests to use your company’s main Wi-Fi network
- Using insecure communication channels to collect sensitive data, including non-HTTPS websites
- Keeping the company’s Wi-Fi open and discoverable to eternal users
- Using public Wi-Fi to connect to the internet or your organization’s secure resources when working remotely
A VPN can protect you and your company against MitM attacks by concealing your IP address and the location of your device. A VPN creates a secure communication channel between the device and the VPN server. This means that all traffic — HTTPS and non-HTTPS alike — that passes through this channel is encrypted. Therefore, a criminal can’t read or change the data even if they somehow get access to it.
4. Employ HTTP Strict Transport Security (HSTS)
HTTP strict transport security, or HSTS, is a website security policy that can be included in your site’s header information. Its purpose is to force browsers to load your website using secure HTTPS connections. Why is this necessary? Let’s break it down…
Most people type only the domain name to get to a website. For example, they might type “cheapsslsecurity.com” instead of typing the full “https://www.cheapsslsecurity.com.” In some cases, the browser might load an insecure version of the site that’s delivered via HTTP. In that case, the user is sharing information with an insecure website, which is susceptible to a man in the middle attack.
A cybercriminal will launch an SSL downgrade attack on a legitimate website to carry out an MitM attack. An SSL/TLS certificate guarantees that the conversation between client and server is encrypted and that any person with malicious intent can’t access it. However, in an SSL downgrade attack (also known as SSL stripping), an attacker strips down the SSL/TLS protection to access the conversation between the client and server via the insecure HTTP protocol.
So, what man in the middle attack prevention tactics can help you protect your website and users against an SSL/TLS stripping attack? The answer lies in HSTS. Using an HSTS header on your site tells browsers to load the HTTPS version of your website. When a user opens the website for the first time, the browser will store the HTTPS version. This ensures that even if the user loads the website using either the domain name or the HTTP version, the browser will redirect them to the HTTPS version.
OWASP’s HTTP Strict Transport Security Cheat Sheet shows how HSTS protects the user against man in the middle attacks carried out by stealing unsecured cookies, DNS spoofing, or cross-site scripting. You should make sure that you include all the subdomains in the HSTS header to provide the most robust security. However, it’s important to note that when you employ HSTS, you must specify the expiration period. If the HSTS specified period has expired, you might leave yourself open to MitM attacks.
Another limitation of HSTS is that it will only operate after the user logs in to the server for the first time. Till then, the user is not protected. To deal with this issue, Google has come up with an “HSTS pre-load list,” which is supported by the most modern browsers. The pre-load list feature notifies the browser that it was trying to load an HTTP website. It also assists the browser in case of the max time in the HSTS header has expired and the HTTP site is being loaded.
5. Implement a Strong Encryption Point with Wi-Fi Protected Access (WPA)
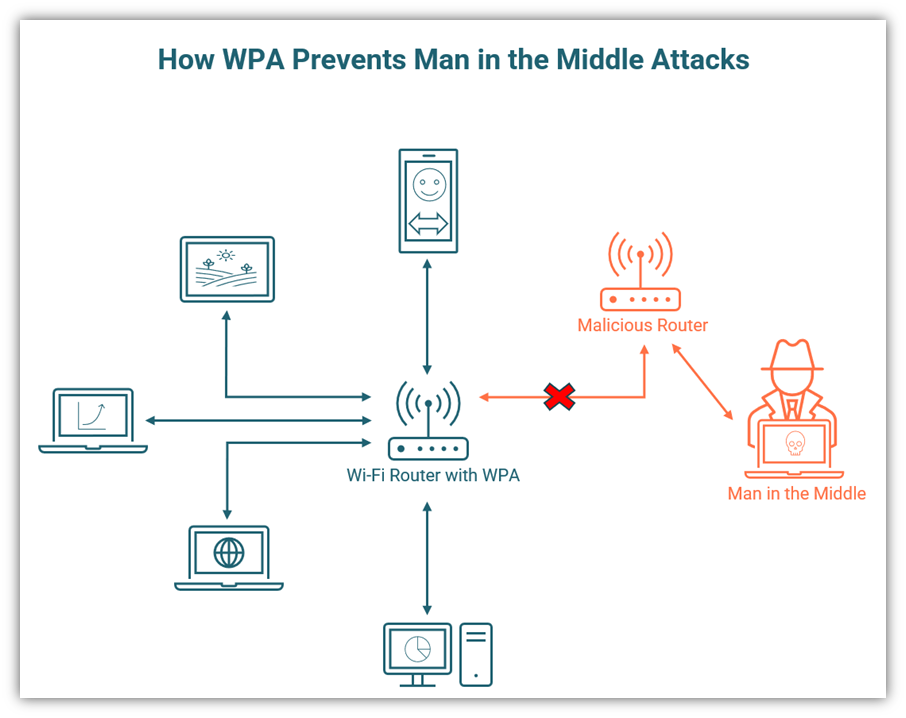
We’re now halfway through our list of man in the middle attack prevention methods. WPA, WPA2, and WPA3 are encryption protocols developed by the Wi-Fi Alliance to secure wireless computer networks. Most small and medium enterprises have wireless internet in their offices; this might be convenient, but management and employees can make some grave mistakes that may lead to man in the middle attacks. Cybercriminals might gain access to your network in the following circumstances:
- Your Wi-Fi password is weak
- Your Wi-Fi network is open
- Your Wi-Fi is discoverable by anyone in your area
- You let your guests use Wi-Fi with the same password as your employees
- You don’t change your Wi-Fi password regularly
WPA can secure your wireless network from MitM attacks. Still, cybercriminals could use brute force to crack your Wi-Fi password and enter your network. Therefore, it’s imperative that you buy certified routers that support the highest security protocols.
The WPA protocol uses temporal key integrity protocol (TKIP) that generates a new dynamic 128 bit key for each packet. WPA3, released in 2018, is the strongest protocol and is required for all Wi-Fi CERTIFIED devices, according to Wi-Fi Alliance. It uses advanced encryption standard (AES) strength up to 256 bits with SHA-384 for providing robust security to its personal and enterprise customers.
6. Implement a Precise Password Policy
Passwords are your first line of defense against any kind of cyberattack, including man in the middle attacks. A strong password can protect your systems and email accounts from cybercriminals who try to break in using brute force attacks. IBM reported that stolen credentials were the most common initial attack vector — they’re responsible for 20% of data breaches, resulting in an average loss of $4.37 million for businesses between May 2020 and March 2021.
It is also noteworthy that when stolen credentials were the initial attack vector, it took the longest number of days (341) to identify and contain the breach. This underlines the importance of having a precise password policy for your enterprise that is implemented in a stringent manner.
Here are some pointers to keep in mind while forming a strong password policy:
- The FBI recommends the use of passphrases instead of passwords
- Passwords should be kept secret
- All accounts should have unique passwords
- If a password becomes compromised, it should be changed immediately on the official account’s website
- Passwords should be hard to guess and should not contain words or numbers from the most common password list
- Use multi-factor authentication or two-step verification where possible
A trustworthy password manager can be helpful if you need to juggle a lot of passwords. It’s like an online locker to store all your passwords safely. Most password managers also help you generate random passwords for your accounts, so you just need to remember the master password for your password manager.
Employees should be encouraged to use two-factor authentication or two-step verification to log in to devices and accounts to make their systems more secure. These methods add a layer of security to password-protected accounts and ensure that the person trying to access an account is who they say they are. It also helps you to avoid having to use password resets, which cybercriminals can sabotage to carry out password reset MitM attacks.
7. Train Your Employees
You can implement every measure in the book, but if your employees don’t follow the rules — or they don’t know what rules to follow — your data is at risk. Cyber awareness training can help you fill in the knowledge gaps so your employees are aware of the threats, know what to look out for (such as fake or insecure websites), and what they should or should not do when operating online.
Cybersecurity training should not be conducted once or twice; it should be conducted regularly throughout the year. All employees – old and new, from junior team members to top management – should be trained to follow the cyber security policy. Some things to include in training:
- The company password policy
- Policy on using public or free wireless networks
- The importance of logging out of accounts and locking devices when they’re not in use
- Reporting abnormal activity to management
- Differentiating between regular emails and phishing emails
- Using HTTPS sites only
- The latest trends in cyberattacks and security
Training sessions should be mandatory for all employees and exercises should be designed to test their knowledge. Training can be conducted by an in-house security team or by third-party experts. Always remember, the security of your company is only as strong as your weakest link.
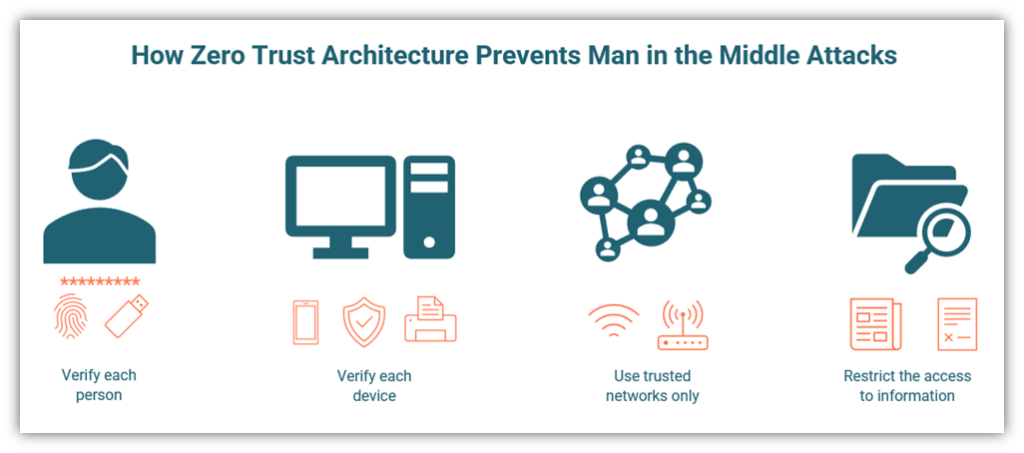
8. Implement a Zero Trust Architecture
The SonicWall Cyber Threat Report 2021 revealed that there were 4.77 trillion intrusion attempts during 2020, a sharp increase from 3.99 trillion in 2019. It is worth noting that 56.44% of attempts in 2020 were in North America. Using a zero trust architecture is one way to tackle this growing problem.
The concept of zero trust architecture was introduced by John Kindervag, VP and principal analyst on the security and risk team at Forrester Research. The zero trust technique means trusting no one and no device without verification. But zero trust is much more than MFA or 2SV — this architecture ensures that all employees use proper authentication to access information and ensure that they are authorized to access the information.
Basically, the idea here is that no employee can retrieve information that they are not specifically authorized for. Every person is treated as a potential threat, which makes the zero trust model incredibly powerful.
9. Monitor Network Activity
Man in the middle attacks are notoriously difficult to uncover. However, there are tell-tale signs of a man in the middle attack that can be observed if the activities of employees are monitored properly. A small or medium-sized business should have people assigned to monitor the online activities of all employees.
Here are some ideas to help you implement an effective monitoring architecture as the final man in the middle attack prevention method for our list:
- Define a clear-cut system for connecting devices
- Secure all devices and your network with firewalls and anti-malware software
- Formulate policies for information sharing in the organization and limit access to sensitive data on a need-to-know basis
- Observe and document account access behaviors of employees online
- Monitor all traffic coming in and out of the company network
- Ensure prompt reporting of any type of software or hardware glitches
Proper monitoring helps to ensure that a man in the middle attack is discovered sooner rather than later. Although there is no sure-fire way to know if you are being watched by a man in the middle, certain signs can alert you. We’ll look at these signs in the next section.
Man in the Middle Detection Tips & Signs to Look Out For
Detecting a man in the middle attack is challenging to say the least. There isn’t a one-size-fits all list of man in the middle detection tips because there are too many possibilities based on the technologies you have in place and how things are secured. Some quick examples of what you can do to detect potential MitM attacks include the following:
- Use network monitoring tools to inspect traffic entering and leaving your network
- Scan your website and network for malware
- Analyze connection records to look out for repeated disconnections
- Use tamper detection tools
If you or any of your employees see your systems behaving abnormally, you should check if you have become a victim of a man in the middle attack. Here’s a quick list of signs to look out for that can indicate a man in the middle attack. (Note: This list is in no way comprehensive.)
- You observe strange web addresses appearing in your browser
- Your browser unexpectedly switches to non-HTTPS websites
- There are unusual delays in your online requests or frequent disconnections
- Your internet usage rises unexpectedly
- You notice bank transactions that you didn’t make
- Any of your associates or customers receive communications claiming to be from you, but you did not send them
Final Words on Man in the Middle Attack Prevention
A man in the middle attack is not only a type of cyber attack but also a method used by cyber criminals to launch other types of attacks. Throughout this article series, we’ve explored several key areas to know about MitM attacks:
- What a man in the middle attack is,
- The different types of man in the middle attacks, and
- How to detect and prevent man in the middle attacks.
With the rise in incidences of this type of attack, it’s clear that we have to invest more time and effort to keep them in check — and the more you know, the safer you and your business will be. We hope you found this article on man in the middle attack prevention useful.





