In a time where real-time communication and video streaming are predominant in the digital scene, discover how the power of UDP in computer networking can give you and your audience a smooth live streaming experience. Take an in-depth tour into the core of the user datagram protocol and get ready to shine!
The internet world has gone through major changes in the last few years. Cloud computing has become mainstream, and IoT devices, VoIP, virtual voice assistants, and broadcasting services are booming. According to Dialpad’s survey, 83% of people are spending a third of the week in virtual meetings and more than half of them are experiencing audio-related issues. With everyone heavily relying on real-time connectivity both at home and at the office, dealing with latency and speed issues has therefore become a top priority for businesses. This is where understanding how UDP works can be helpful.
In our previous article on the user datagram protocol (UDP), we learned the basics about what it is and what it does. For example, it’s a game-changer for such applications as video chat, live streaming, and multiplayer gaming. Now, as the use of UDP in computer networking gains momentum, we’ll take you behind the scenes of how this protocol works to help you learn everything you need to know about UDP’s role in computer networks.
The User Datagram Protocol (UDP) Explained: A Quick Overview of How UDP Works
Technology has completely revolutionized the way we communicate, enabling us to get in touch with people all over the world in an instant. You login into your favorite chat app and can speak to your friends and family, even if they’re in another country. Have you ever asked yourself how it’s possible? Nope, there’s no magic involved. All this is made possible by a set of rules (i.e., network protocols). These rules allow devices to communicate with each other, regardless of what their internal processes are or how they’re structured or designed.
The user datagram protocol is one of the main standard network protocols. As a quasi-scaled-down, lighter alternative to the transmission control protocol (TCP), UDP is used for the fast transmission of datagrams in IP networks without needing to establish a connection. In simple words, it’s a sleek, simple protocol that provides the basic transport layer functions requiring lower overhead and lower latency.
With UDP, there’s no guarantee of message delivery or message order and no way to avoid message congestion. It has no handshake, no session, no error control. However, sometimes less is more, and UDP is the go-to protocol when using real-time applications or for request-response queries like DNS ones.
UDP Features at a Glance
To understand how UDP works, we first need to know a bit more about its properties.
- UDP is connectionless. This means that datagrams are transmitted without the need for a connection between the source and the destination. Packets are sent to the IP address specifying the target port.
- UDP uses ports for data transmission. UDP typically specifies the IP address and destination port numbers in its datagram headers to send packets to the correct recipient. (We’ll discuss packet/datagram headers more a little later in the article.)
- UDP guarantees fast and delay-free communication. Because it doesn’t need to set up a connection or check transmission errors, it’s faster than TCP. This makes it well suited for all those applications where the loss of individual packets isn’t a big deal.
- UDP doesn’t care about data integrity or reliability. The user datagram protocol has no mechanism to check the completeness and order sequence of the packets. It also lacks the handshake verification process used by TCP, making it a kind of “send -and-pray” protocol. Therefore, data integrity and reliability are out of the deal.
- UDP can be vulnerable to denial of service attacks (DDOS). As a result, the server ends up being clogged like a plugged drain, and legitimate traffic can’t get through (denial of service). No handshake also means that it’s much easier for a source to bombard the recipient with datagrams without approval. Everything is not lost, though. The good news is that there are ways to limit the damages and protect users and organizations from these kinds of attacks.
OK, now you know what UDP is and what its key features are. But how does UDP work? What’s the technology behind it? Let’s get rolling and find out.
How UDP Works: An In-Depth Perspective
Being one of the simplest transport layer protocols, the process behind it’s very straightforward. With UDP data simply starts flowing between two systems.
- Data are gathered in one or more UDP packets.
- The header information — including the source and destination ports to communicate with, the packet length, and a checksum — is added to each datagram. This header information provides a wealth of necessary information about the data, where it came from, and where it’s intended to go.
- The datagrams are encapsulated in an IP datagram.
- The datagrams are sent off to their destinations.
This is much less complicated than other communication protocols, right?
It’s interesting to note that when a UDP datagram is sent, the host checks the port number and delivers the data to the corresponding application. This way, the host can send and receive data over multiple distinct ports (i.e., multiplexing over IP).
Understanding UDP Packet Format and Headers
Each UDP datagram is composed of a multi-part header with a fixed size of 8 bytes and an additional data section. The header is divided into four fields:
- Source port,
- Destination port,
- Length, and
- Checksum.
Each field is 2 bytes (16 bits) long. This small makeup makes it faster and lighter in terms of required overhead (which is better for real-time usage where latency can be an issue). The data section comes after the header and contains the actual data to be sent.
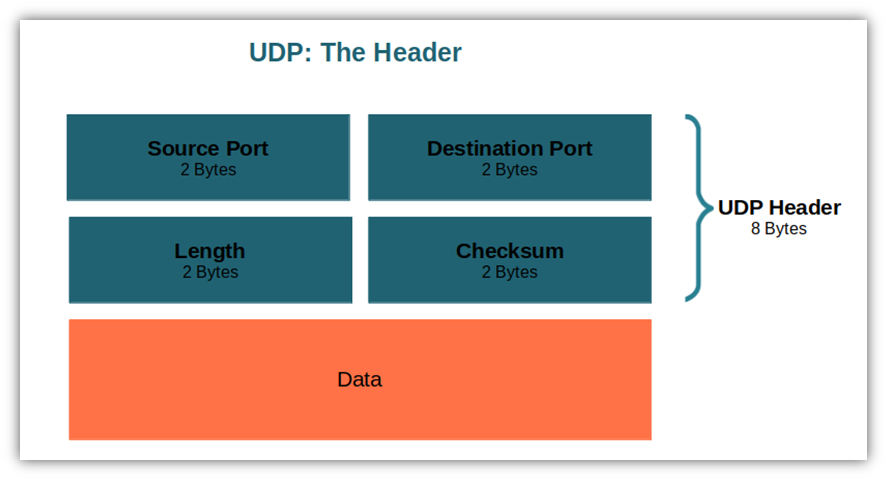
The UDP’s header contains all the information required for data transmission. Depending on the version of the internet protocol used, it’ll look slightly different.
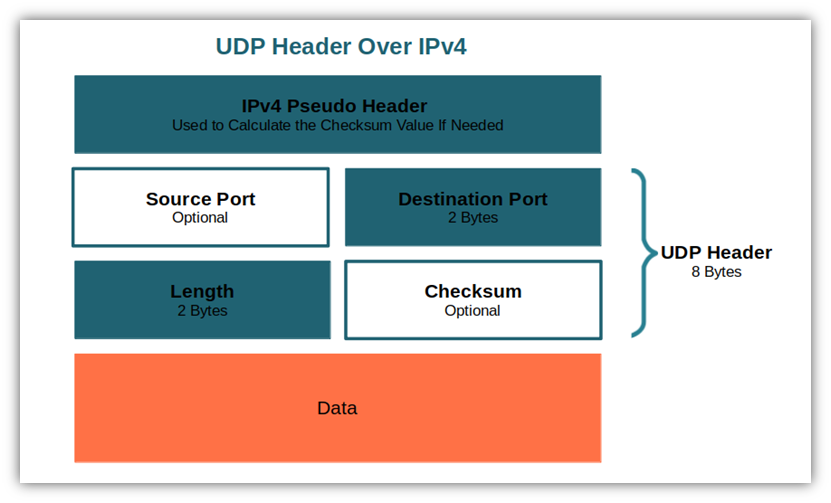
UDP Header Peculiarities in IPv4
IPv4 is the fourth version of the internet protocol, the set of rules that make internet communication possible. Deployed for the first time on Arpanet by the U.S. Department of Defense (DoD) in 1983, IPv6 is now replacing it (although IPv4 is still widely used).
With IPv4, both the UPD header checksum and the source port fields are optional. If the checksum is used to send a datagram (like with most applications), it will be calculated through a pseudo-header containing the same source and destination address included in the real IPv4 header. Why is it important? Because the checksum is the only way for UDP to find transfer errors and manipulations.
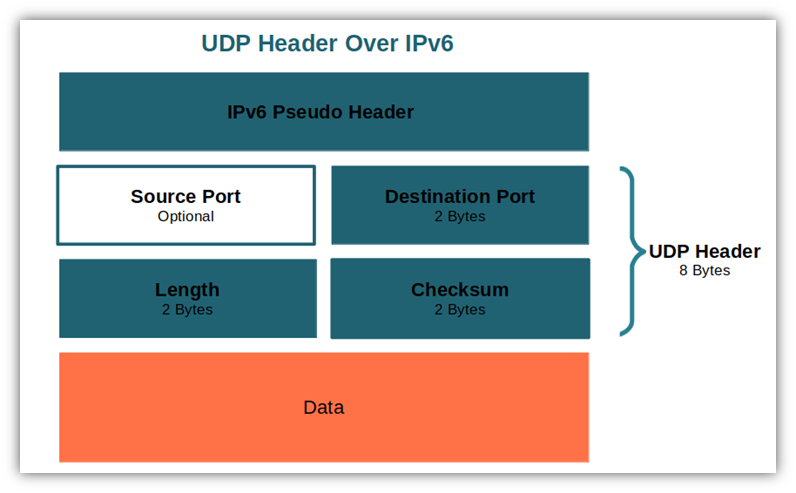
UDP’s Header in IPv6
With IPv6, the most recent internet protocol, the checksum is mandatory for the UPD header while the source port is still optional. This is because the IPv6 header itself no longer contains its own checksum. (It was viewed as redundant since most traffic “with UDP or TCP checksums enabled.”) The computation of the checksum follows the steps documented in RFC 2460 (which was obsoleted by RFC 8200). Once again, a pseudo-header containing some information, like the source and destination address, is added to the equation.
To learn more about the UDP header in relation to IPv6, be sure to read the IETF’s resources.
We talked a lot about UDP’s header — now it’s time to dig deeper and discover what lies behind each field.
How UDP Works: A Look at the UDP Header Source Port
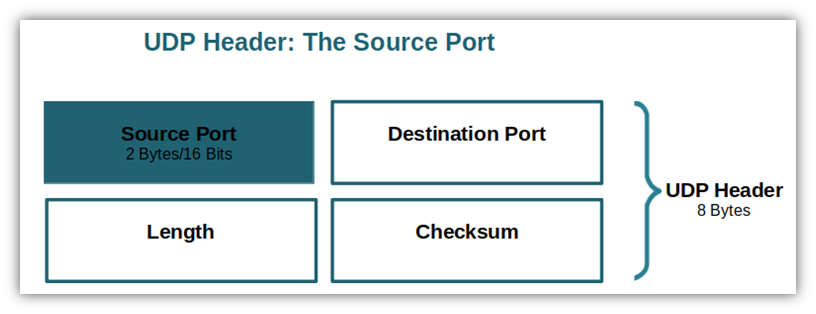
The source port is the first bit of the header and it represents the port number of the sending device. If not used (it’s an optional field, remember?) — for example, because no reply is required — it should be set to zero by the sender. Each device has several ports, each used for specific network traffic.
How UDP Works: A Look at the UDP Header Destination Port
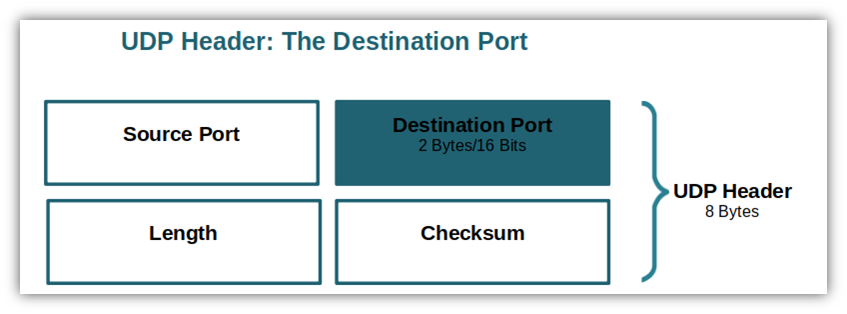
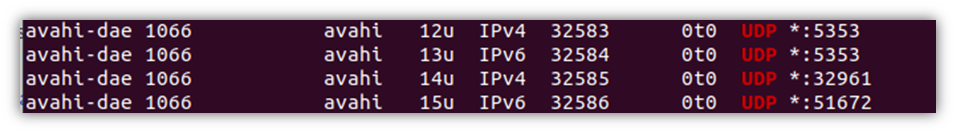
The destination port indicates the port number of the receiving device. To ensure that the packets are delivered to the correct destination, it’s considered a mandatory field. Below is an extract of a device’s listening ports showing the name of the process and, at the end of the row, the protocol and port number.
How UDP Works: A Look at the UDP Header Segment Length
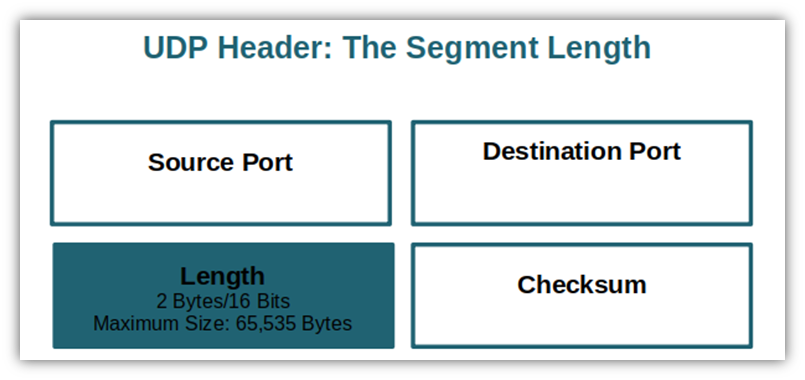
It’s a 16-bit field that specifies in bytes the total length of the datagram (UDP header plus the data). Its maximum field size is 65,535 bytes (216−1). In IPv6, it’s possible to have a greater size thanks to “jumbograms” (i.e., internet packets with a transmission unit bigger than 65,535 bytes). In this case, the length field must be set to zero as specified by RFC 2675.
How UDP Works: A Look at the UDP Header Checksum
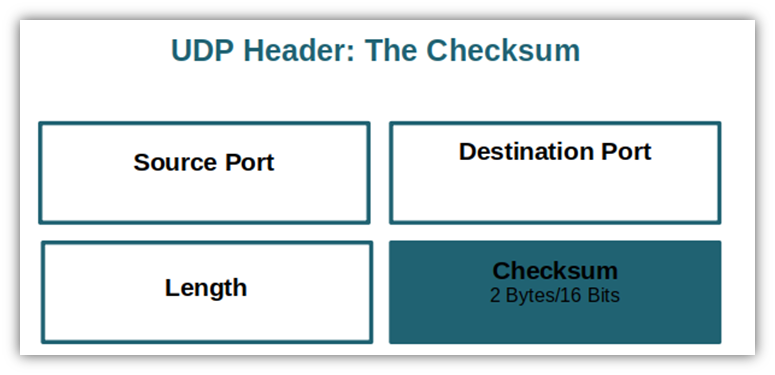
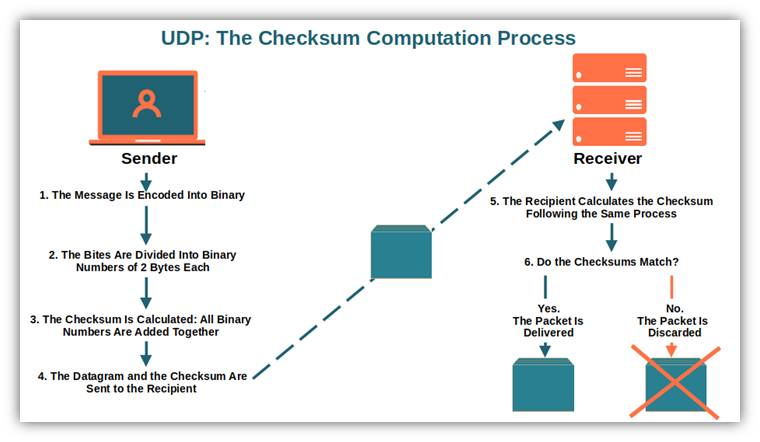
A checksum is a unique value generated by a cryptographic algorithm that works like a digital fingerprint. Usually represented by a short string of letters and numbers, it’s used for error detection and it’s mandatory in the UPD header over IPv6. (It’s optional for UPD over IPv4.) Basically, it enables the sender and the receiver to verify the transmitted data’s integrity and identify any manipulation or corruption. How?
- The sender encodes the data into binary.
- The bytes are divided into 2-byte binary numbers.
- All 2-byte binary numbers are added together to compute the checksum.
- The datagram is sent to the recipient together with the checksum.
- The recipient receives the data and calculates the checksum following the same process.
- The recipient compares the two checksums. If they match, everything is good; if they don’t, then “something is rotten in the state of Denmark” like Shakespeare once wrote. In other words, the data have been modified (voluntarily or involuntarily) during transmission and are discarded.
With such a minimalist structure and a basic transmission method, UDP cannot guarantee that the data sent will reach its destination making it unreliable. Datagrams may do any of the following without warning:
- Get delivered out of order,
- Not be delivered at all, or
- Disappear or have duplicates.
While this may be a real issue with some applications, its low overhead, latency, and high speed make it invaluable for those applications that don’t require a reliable transmission service. Which ones? This is what we’re going to see next.
Applications of UDP in Computer Networking
Despite the above-mentioned downsides, several key internet applications use UDP:
Simple Request-Response Communications
Domain name system (DNS) queries are a typical example of where you’ll find UDP in use. Every time you visit a website, a DNS query is generated. Your device queries the DNS server for the IP address of the site, sends the response back and, voila, you can now see the web page. This happens in a matter of milliseconds, thanks to the UDP protocol.
Other tiny request-reply transactions where UDP is used include:
- Dynamic host configuration protocol (DHCP) — A network management protocol mechanism used in TCP/IP networks to dynamically and automatically assign IP addresses within a network.
- Simple network management protocol (SNMP) — One of the most used protocols for managing and monitoring network connected devices.
- Routine information protocol (RIP) — A dynamic routing protocol (also defined as distant-vector protocol) that determines the best route for data packets calculating the distance between the sender and the recipient’s network.
- Trivial file transfer protocol (TFTP) — A simple protocol used for basic file transfer (e.g., sending a file from a server to a client) without the need of user’s authentication. Similar to the file transfer protocol (FTP), it’s based on the same technology.
- Network news transfer protocol (NNTP) — An application protocol of UseNet, specifically designed to transfer news and articles from one network to another.
- Quote of the day protocol —A basic protocol used to deliver daily quotes. The protocol is very short (216 words, nearly like a Twitter message) and it’s not very much in use today.
Real-Time Applications That Don’t Tolerate Uneven Delays
The human eye is thought to register an average of 36-60 frames per second (i.e., 30-60 hertz [Hz]). Movies are recorded at an average of 24 hertz, but there’s talk about increasing it to 60/120 frames per second. The more frames per second, the smoother and more seamless the display will appear. (Many games use 30-120 frames per second depending on the type of game with 60 FPS being the preferred frame rate.)
All of this means that when you’re watching a live video streaming, for example, you might not notice minor errors and occasional hiccups depending on the display rate something is presented at. Yes, in some cases you may experience a video or audio degradation quality due to packet losses; however, it’s better than experiencing huge delays and buffering issues.
The same applies to online games. Being extremely time-sensitive, retransmission of lost packets is out of the question while bandwidth and speed are essential. Additional real-time applications using UDP are:
- VoIP (e.g., Skype)
- Multiplayer games
- Media streaming
Multicast Applications
Multicast applications (one-to-many applications) can send packets to any number of recipients simultaneously without the needing point-to-point connections. Basically, the application sends a single copy of each datagram to a single multicast address, which is then distributed to all recipients. Multicasting is mostly used for:
- Video and audio data transmission
- Event notifications
- Status monitoring
- Distance learning
Some Virtual Private Networks (VPN)
Even if most VPNs utilize TCP by default, some others like OpenVPN also offer UDP as an option. Why? Because when streaming high-definition (HD) videos or movies over a VPN, you may care more about speed than reliability. Or, if costs due to TCP’s latency and additional overhead are a concern, you may want to opt for UDP.
Google’s Quick UDP Internet Connection (QUIC)
In May 2021, Google’s QUIC, a UDP-based encrypted transport protocol optimized for HTTPS, was officially added to the Internet Engineering Task Force’s (IETF) internet standard. With QUIC, you get the best of two worlds as it combines the best features of both TCP and UDP by enabling low latency, lighter data streams, with fewer errors. So, even if this new transport protocol doesn’t rely solely on UDP, it’s worth mentioning it.
Final Thoughts on How UDP Works: A Look at the User Datagram Protocol in Computer Networks
The internet is evolving and UDP is contributing to this evolution in a big way, joining the quest for more responsive applications in computer networks. At the end of the day, we’re all expecting a smooth internet experience, above all when using real-time applications. With different protocols available, understanding the technology and processes behind one of the most important ones is a step forward toward identifying the protocol that best suits your network’s needs.
Now that you know how UDP works from a technical perspective, you’ll better understand why glitches, blurriness, or other issues occur when you’re attending a work video conference or playing your favorite online game.
And that’s not all! Our journey into the world of standard network protocols continues. In a couple of our upcoming articles, we’ll tell you everything you need to know about TCP and will make the ultimate comparison between TCP and UDP. Don’t miss them!