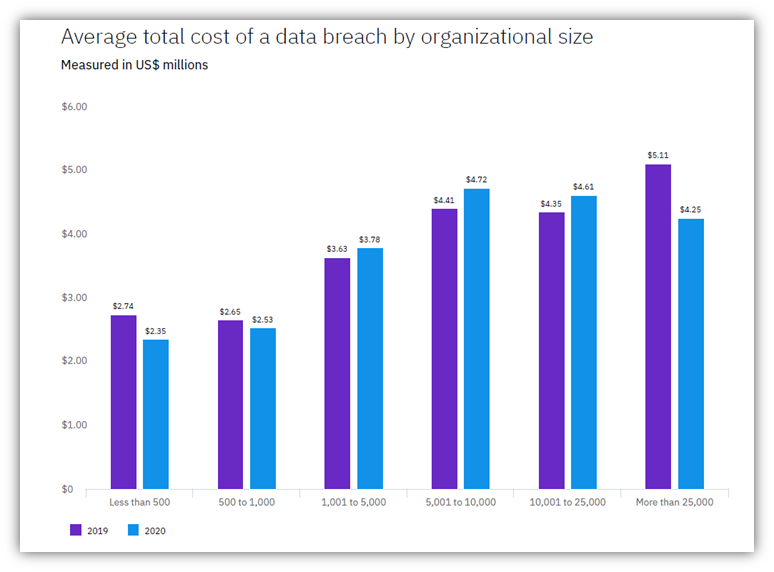
IBM’s 2020 Cost of Data Breach Report states that the average cost of a data breach for small organizations was $2.35 million (<500 employees) and $2.53 million (for small businesses with 500-1,000 employees). So, if you think cybersecurity is not your top priority, think again. We’ll give you eight critical reasons why small business cybersecurity matters
Owning or operating small or medium-sized business (SMB) is easier said than done. It takes a lot of time, hard work, and dedication in terms of resources. Protecting your small business from cybercriminals is much the same. Unfortunately, when it comes to small business cyber security, some owners choose to skip a step here and there and wind up falling prey to cybercrime.
Data from Verizon’s 2020 Data Breach Investigations Report (DBIR) indicates that small businesses represent 28% of the data breach victims reported in 2019. Again, that’s just the registered number that Verizon knows about and studied. There are likely many other SMB-related data breaches that are unknown or have gone unreported. Considering that the U.S. Small Business Administration’s (SBA) Office of Advocacy reports that 99.9% of all businesses in the United States are small businesses (having fewer than 500 employees), this means that there are a lot of companies that are likely to get hit.
Sectigo’s 2021 Sectigo State of Website Security and Threat Report indicates that 48% of SMBs say they’re “too small” for cybercriminals to target. This is particularly troubling considering that Keeper Security and the Ponemon Institute report that fewer than half of their survey respondents believe their organizations’ risk and attack mitigation efforts are practical. Since the start of the COVID-19 pandemic in early 2020, the percentage of confident employees dropped 27%, from 71% to 44%.
If we look at this data in the context that more than one-in-four victims of cyber attacks are SMBs, it’s clear to see why small business cyber security should be among your top priorities.
Why Small Business Cyber Security Matters to You & Your Customers
In a nutshell, cybersecurity for small businesses helps you keep your data — which includes everything from your employees’ and customers’ personal information to your sensitive intellectual property — secure. This isn’t just crucial from a data security standpoint; it’s also a compliance requirement. If you don’t protect your data, you become non-compliant and may face fines and penalties. Furthermore, you’ll lose the trust of your key stakeholders… and this may be something that your organization’s reputation may never recover from.
But just how bad can a cyber attack be for organizations? Let’s consider the following example to illustrate the damage and confusion cyber attacks can cause:
Bristol schools in the United Kingdom announced they were the target of a highly sophisticated ransomware attack on March 16, 2021. The Castle School Education Trust (CSET), which oversees seven of the 23 schools that have recently come under attack (including those in Bristol), says that the attack aimed to cause live classes to cancel. BristolLive reports that more than 1,000 devices have been infected and are being rebuilt, along with 16 servers that are responsible for core functions, including access management.
Although the South Gloucestershire Council says the March 16 attack didn’t appear to affect personal data, BristolLive reports that it caused many other issues for the school:
- Staff are unable to access key IT systems, databases, and files,
- Remote learning lessons have been lost, and
- Teachers are unable to access integrated teaching technologies.
Okay, so this ransomware attack targeted schools. What does that have to do with small business cyber security? Data from the Sophos State of Ransomware Report 2021 shows that 37% of their survey respondents indicate that their mid-size organizations had been hit by at least one ransomware attack. The average ransom paid by a mid-sized organization was $170,404. And even in cases where companies paid the ransom demands, only companies report an average of 65% of the data was restored.
As a small business owner, that’s a lot of money to gamble with no guarantee that you’ll regain access to your data or control of your IT systems. And considering that ransomware attacks are only one type of cyber attack targeting small businesses, it should be pretty clear why small business cyber security matters. However, if you need a few more reasons, we’ve got them for you…
1. Small Businesses Have Lots of Data to Protect
Where start-ups and small businesses often lack value in terms of money, they often make up for in rich data. Many attackers recognize the value of data (particularly intellectual property and personal information) and view it as a valuable resource to steal, use, barter, or sell.
The most recent data from Verizon’s 2020 DBIR reveals that 86% of the breaches in 2019 were financially motivated, and 10% were motivated by espionage. More than 50% of the actors (cybercriminals) have ties to organized crime, and around 10% are affiliated with foreign nations.
While some small businesses lack money, they might be a rich source of data. Cybercriminals often use the stolen data in many ways, including:
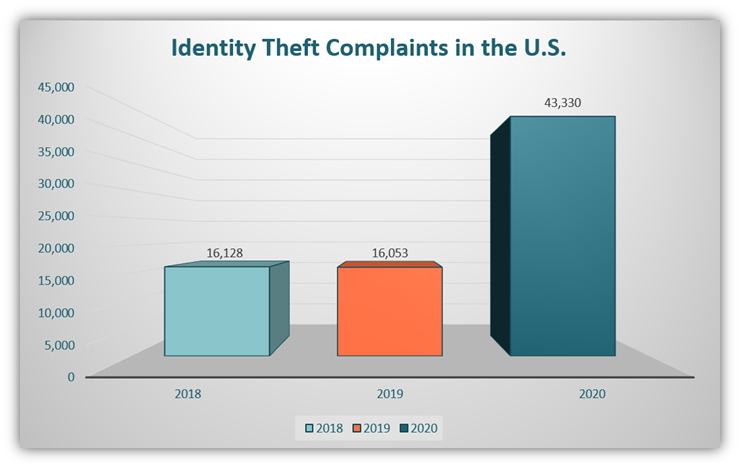
- Using personally identifiable information (PII) to carry out identity fraud. The FBI IC3 report observed a substantial rise in identity theft in 2020. The figure below shows the identity theft data for the last three years:
- Carry out phishing attacks against your customers or users while impersonating your company. The IC3 report also states that phishing scams have increased from 114,702 in 2019 to 241,342 in 2020, an increase of 110.41% (more than double!!).
- Selling or trading the personal or financial data they steal on the dark web to other cybercriminals and crime syndicates. A parallel market has developed for stolen data on the dark web to sell IDs and credit card info. Privacy Affairs reports that the price of a cloned Mastercard with PIN rose from $15 last year to $25 this year. Also, cards stolen from US users were cheapest at $17 apiece, whereas card data from Israeli cardholders sells for $65 per card.
- Using or selling your trade secrets or intellectual property to your competitors. Verizon’s 2020 DBIR also states that 30% of the data breaches involve internal actors. The actors can use a disgruntled employee to gain access to the company’s data. This data might be sold to a competitor by the criminals for a price. General Electric faced a similar situation where an employee of the company established an enterprise manufacturing competitive goods by using the stolen data.
An example of the last bullet point can be seen with Jean Patrice Delia, a former General Electric employee. Delia, along with a former GE IT employee named Miguel Sernas, downloaded thousands of proprietary files from the company, including valuable data on advanced computer models for calibrating turbines the company manufactured. Delia started his own company and competed (and won) for tenders against GE for quite some time before GE realized the breach that included Sernas and Delia. After a lengthy court battle, both former employees were imprisoned, and GE received $1.4 million in restitution.
2. Cybercriminals May Target You as a Way to Attack “Bigger Fish”
Cybercriminals sometimes attack small businesses as a way to get to the larger companies and organizations they’re affiliated with. Essentially, you’re not their true target — rather, you’re merely a stepping-stone or their means to an end. Ouch. Yeah, we know that stings.
Don’t think this is possible? Here are a few examples of small business cyber security attacks where threat actors used other companies as an attack vector to gain access to other or bigger targets:
- Target data breach. Hackers broke into the systems of HVAC, refrigeration, heating, and air-conditioning subcontractor to attack a bigger company, Target, in 2013. This single breach was responsible for the stolen data of 40 million customers. Later in 2017, Target agreed to pay $18.5 million to settle claims by 47 states and the District of Columbia to resolve a multi-state investigation for the breach.
- U.S. utilities. In 2018, hundreds of contractors and sub-contractors of the U.S. power grid were targeted to form the base from which a foreign government planned to attack the nation’s electric grid. The Russian campaign to take down the power stopped in its tracks when the FBI and Homeland Security took stern actions. They notified the unsuspecting contractors that their systems had been breached.
- Acer. Although Acer hasn’t openly admitted to it, BleepingComputer reports that the threat actor group REvil hit the tech giant with a ransomware attack in March 2021. With a $50 million ransomware demand, BleepingComputer reports Acer faces the largest ransomware demand known to date. The article also states that the attack may have resulted from exploiting a vulnerability in an Acer domain Microsoft Exchange server.
3. Small Businesses Have Fewer Resources to Dedicate to Cyber Security
Next up on our list of why small business cyber security matters… Data from Sectigo’s 2021 State of Website Security and Threat report shows that 60% of small businesses spend $500 or less on cybersecurity per month. With the rising cyber threats that SMBs expect to face in 2021, 49% of companies indicate that they’re planning to spend more on cybersecurity.
Small businesses will have less stringent security and the cybercriminals are aware of this vulnerability. This is often because of entrepreneurs’ limited resources. To set up their businesses, entrepreneurs often take on many responsibilities to conserve labor and financial resources. This can be dangerous as many entrepreneurs aren’t IT security or small business cybersecurity experts.
A significant proportion of the labor new businesses employ often focuses on starting the business efficiently, generating new ideas to take over the market, setting up processes and people at various levels, and other tasks for the business setup. Moreover, due to a lack of capital, increasing staffing beyond a certain level may seem impossible. As a result, cybersecurity is often deprioritized. Even if they invest in anti-virus and anti-malware tools, they often can’t spare enough people to keep tabs on everything.
4. SMBs Must Follow and Adhere to Applicable Industry and Government Regulations
Small businesses must comply with rules and regulations set up by governing authorities. Some of these compliance standards are mentioned below:
- If you accept payment from your online customers, you are obligated to follow the PCI DSS requirements. The Payment Card Industry Data Security Standards, or PCI DSS, are the standards mandated by all the major credit card companies to ensure the safety of the data. These standards define businesses’ operational and technical requirements to accept and process online payments. If you fail to comply with the requirements of PCI/DSS, you might have to pay heavy penalties.
- Federal agencies and government contractors must follow specific rules and regulations outlined by NIST and FIPS. For example, the United States government contractors must follow the National Institute of Standards and Technology’s (NIST) SP 800-171 cybersecurity standards. Covered organizations must comply with these 14 standards, which are pre-defined for the different areas of an organization.
- In addition to NIST, US defense contractors must also be DFARS compliant. As defined in DFARS § 252.204-7012, there are 110 security requirements that covered organizations must fulfill. Also, the cloud service used should be FedRAMP compliant.
- U.S. healthcare organizations must be HIPPA (Health Insurance Portability and Accountability Act) compliant. The Herjavec Group’s 2020 Healthcare Cybersecurity Report concludes that more than 93% of healthcare organizations have experienced a data breach over the past three years, and 57% have had more than five data breaches during the same timeframe. IBM reported that the average data breach cost of the healthcare industry was the highest amounting to $7.13 million.
- Organizations globally that handle the personal data of people located in the European Union must abide by General Data Protection Regulation (GDPR). All entities that collect, store, or process PKII of people located in the EU must follow these guidelines regardless of their organizations’ sizes and locations. This means that international organizations also fall under the purview of GDPR when they handle said data. Non-compliance can cost companies upwards of 4% of their annual gross revenue or €20 million (whichever is greater) in fines.
- CCPA (California Consumer Privacy Act) is a state statute that protects the data privacy and rights of California consumers. The CCPA, which went into effect on Jan. 1, 2020, is a security regulation that applies to organizations doing business in California. Covered organizations that this regulation applies to collect California consumers’ personal data and meet one or more specified thresholds relating to revenues or the amounts of personal data they buy, use, or sell.
CCPA violators must pay up to $2,500 or $7,500 for unintentional and intentional violations, respectively. Companies that experience data breaches or data theft also may have to pay statutory damages of $100-750 (or the actual damage, whichever is higher) per incident to California residents.
5. Your Business’s Brand and Reputation Are at Stake
If cybercriminals attack your organization’s IT devices, infrastructure or website and successfully steal data, your customers may think twice before doing business with you again. You become a liability in their eyes, and they’ll likely turn to your competitors in the future than risk their data being involved in another of your small business cybersecurity attacks or data breaches.
Sectigo’s 2021 Website Security and Threats study observed that 28% of breached SMBs suffered “severe” to “very severe” consequences as the result of website breaches:
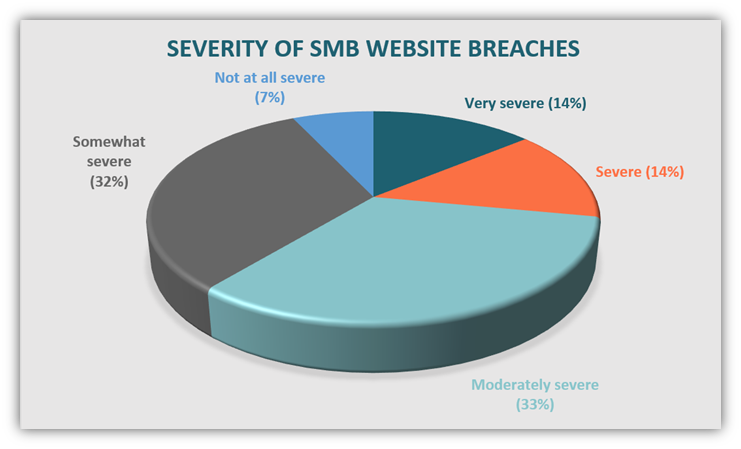
These consequences include everything from loss of intellectual property and customers to reputational loss and website downtime.
One way to help secure your data on websites is to use an SSL/TLS certificate to ensure you’re serving your website via a secure, encrypted HTTPS protocol. Our April 2020 survey data shows that just slightly more than half (52%) of small websites use HTTPS.
6. Data Breaches Aren’t Only Caused by Outside Threats
While external threat actors are bad, they’re not the only people you have to worry about for small business cyber security. Verizon’s 2020 DBIR points out that 30% of the 2019 data breaches they studied involved internal actors — both intentional and unintentional users. Some employees make mistakes (human error) while others choose to do bad things intentionally. Both types of employees, those who know the full consequences of their actions and those who are oblivious to them, pose serious threats to your organization.
This is why access controls are critical to small business cybersecurity. (Of course, it’s critical to ALL organizations’ cyber defenses, but we’re just focusing on SMBs for this article.) This approach limits access to sensitive IT systems and data to only select employees who require it to do their jobs. This process involves setting up strict access controls, including the use of secure authentication tools and setting user permissions for privileged users.
Access controls are a must for companies across all industries, and the financial services industry is no exception. Varonis’ research suggests that all financial services employees have access to an average of 11 million files from the first day they walk in. Nearly two-thirds of the financial service companies have more than 1,000 sensitive files open to all of their employees. This poses a serious security risk because it means that if even just one of those employees’ credentials becomes compromised, the cybercriminal who uses them gains access to all of those files, IT systems and data.
Needless to say, controlling access to your sensitive data is a must. Taking these steps might help prevent your small business from becoming the focus of the next cybercrime-related headline.
7. Moving Your Business to the Cloud Requires Planning
Cloud technologies are incredible resources for small businesses — but they don’t come without risks. And if you try to do this without having the appropriate cybersecurity measures and IT support in place, you might as well just hand your data over to cybercriminals directly. According to IBM’s 2020 Cost of Data Breach Report, cloud misconfiguration was a root cause of 19% of the malicious data breaches they studied. Also, cloud misconfigurations increased the average cost of a data breach by14%.
Following are some of the noteworthy cloud-based data breaches:
- Bonobos: BleepingComputer reports a 70 GB database owned by the clothing retailer Bonobos was leaked by a cybercriminal group known as ShinyHunters. Million of records — including the personal data of Bonobos’ customers, their partial payment information, transactions, and password histories — were published online in a single SQL file. The threat actors were able to access and download the database through the company’s cloud backup.
- VIPGames: WizCase reports a whopping 30 GB of data — including 23 million records and data relating to 66,000 VIPGames users — were exposed due to cloud misconfiguration. Thankfully, the leak was discovered by WizCase white hackers who were researching open servers. Had it been discovered by cybercriminals instead, the results could have been devastating.
- Elasticsearch: vpnMentor reports an anonymous hacker informed them of a massive 882.1 GB data leak affecting hundreds of thousands of users globally and 70+ dating and e-commerce sites. All the impacted websites were using Mailfire marketing software, and Mailfire claimed responsibility for the security incident since they owned the exposed Elasticsearch server.
8. Adopting Remote Work Capabilities Requires Greater Cyber Security
The onslaught of the COVID-19 global pandemic has led to a substantial increase in the remote workforce for more than a year. Some companies are like Google are adopting a hybrid approach to work. As you can imagine, this approach requires a greater focus on small business cybersecurity — and having security-focused processes and policies in place before making that change is critical.
However, it seems that not all businesses have received that memo, as the saying goes. Data from Alliant Cybersecurity shows that 22% of small businesses allow employees to work remotely without first developing a clear cybersecurity prevention policy. Not having those prevention measures in place can lead to potentially substantial consequences. IBM’S 2020 Cost of Data Breach Report data indicates that remote work increased the average cost of a data breach by $137,000.
Final Thoughts on Small Business Cyber Security
Inadequate cybersecurity measures affect everything for small businesses. From your ability to protect your intellectual property and customer data to your compliance with industry regulations, it’s easy to see why small business cybersecurity matters.
Considering that IBM’s 2020 data reports $7.68 million as the average costs to small businesses (those with 500 or fewer employees), it’s easy to see why small business cyber security needs to become a top priority. The truth is that cybercriminals aren’t going anywhere, and industry leaders expect cyber-related breaches and attacks to occur with greater frequency in the years to come. Every small business needs to take the time now to build strong cyber defenses before they find themselves in a threat actor’s sights.